The following release notes cover the most recent changes over the last 60 days. For a comprehensive list of product-specific release notes, see the individual product release note pages.
You can also see and filter all release notes in the Google Cloud console or you can programmatically access release notes in BigQuery.
To get the latest product updates delivered to you, add the URL of this page to your feed reader, or add the feed URL directly.
November 20, 2025
AlloyDB for PostgreSQLAlloyDB now supports horizontal autoscaling for read pool instances. This feature is available in Preview.
Support for Node.js 24 runtime is in General Availability.
You can now use the BigQuery Agent Analytics plugin within the Agent Development Kit to export agent interaction data directly into BigQuery. This plugin captures comprehensive logs of your agent's prompts, tool usage, and responses, enabling you to analyze and visualize agent performance metrics. The plugin leverages the BigQuery Storage Write API for efficient high-throughput streaming. For more information on how to leverage this plugin in your agent, see the Announcing BigQuery Agent Analytics for the Google ADK.
Support for Node.js 24 runtime is in General Availability.
PostgreSQL version 18 is now generally available for Cloud SQL for PostgreSQL.
You can now use Database Migration Service with Cloud SQL for PostgreSQL when using PostgreSQL version 18.
To upgrade your instance to PostgreSQL 18, see Upgrade the database major version in-place.
The following extensions are also now available for PostgreSQL 18:
pg_hint_planpgroutinganonymizerpg_wait_samplingtds_fdwplpgsql_check
For more information about these extensions, see Configure PostgreSQL extensions.
Vertex AI Search: Updated file size restrictions for unstructured data
The file size restrictions for unstructured data import have been unified. For unstructured data, you can import files up to 200 MB regardless of the parser type.
For more information, see Unstructured data.
November 19, 2025
AlloyDB for PostgreSQLThe upper limit of the query plans captured per minute is enhanced to 200. For more information, see Improve query performance using advanced query insights features for AlloyDB.
You can now perform self-service maintenance if you need to apply the latest AlloyDB updates to your clusters as soon as possible. Updating to the latest version can unlock AlloyDB features, apply patches, and let you set deny periods.
Added Change Block Tracking (CBT) support for RHEL 8.8 SAP kernels.
- Resolved an issue with SAP HANA datafile validation on scale-out clusters.
- Fixed a bug causing SAP HANA log backups to fail when the log mode is not 'normal'.
- Addressed failures in Db2 dump full backups in some environments.
- Corrected an issue where Db2 restore jobs with the roll-forward option were not applying logs completely.
Resolved a decryption failure that occurred when accessing KMS keys.
You can now use Gemini in BigQuery to fix and explain errors in your SQL queries. This feature is in Preview.
You can use the
JSON_FLATTEN function
to extract all non-array values that are either directly in the input JSON
value or children of one or more consecutively nested arrays in the input
JSON value. This function is available in
Preview.
You can deploy source artifacts directly to Cloud Run, bypassing the Cloud Build step. (Preview)
The rollout of the following minor version and extension upgrades is complete:
Minor versions
- 13.22 is upgraded to 13.23.
- 14.19 is upgraded to 14.20.
- 15.14 is upgraded to 15.15.
- 16.10 is upgraded to 16.11.
- 17.6 is upgraded to 17.7.
- 18 is upgraded to 18.1.
Extensions
Pgvectoris upgraded from 0.8.0 to 0.8.1.
To use these versions of the extensions and plugins, update your instance to
[PostgreSQL version].R20251004.01_19.
If you use a maintenance window, then the updates to the minor, extension, and plugin versions happen according to the timeframe that you set in the window. Otherwise, the updates occur within the next few weeks.
For more information on checking your maintenance version, see Self-service maintenance. To find your maintenance window or to manage maintenance updates, see Find and set maintenance windows.
Cloud SQL for PostgreSQL now supports Vector assist (Preview).
Vector assist is a Cloud SQL for PostgreSQL extension that simplifies the deployment and management of your Cloud SQL vector workloads. It helps you set up production-ready vector search capabilities, such as embedding generation, query optimization, and index creation.
For more information about vector assist, how it works, and its limitations, see Vector assist overview.
Gemini Enterprise: Enhanced Agent Designer with visual flow builder [Preview]
Agent Designer in Gemini Enterprise is now enhanced with a new visual flow builder, offering a more intuitive and powerful way to create and manage complex, multi-step agents.
This enhancement is available for all new agents. Existing no-code agents will continue to use the familiar editor to ensure backward compatibility.
For more information, see Agent Designer overview.
Sensitive data redaction
You can now automatically identify and redact sensitive data from chat conversations, both in real time and in transcripts. This helps to prevent unauthorized people from accessing sensitive information and can help you comply with security standards. You can configure redaction for incoming messages from end-users, outgoing messages from agents, and session notes. You can also let agents temporarily view redacted messages during a session. This capability is available for the web SDK.
Administrators: You can find the settings for configuring automatic redaction in the following locations:
To add a redaction platform: Settings > Developer Settings > Redaction Platform
To configure automatic redaction at the global level: Settings > Chat > Automatic Redaction
To configure automatic redaction at the queue level: Settings > Queue > Web > Edit / View > SELECT_QUEUE > Automatic Redaction
For more information, see Sensitive data redaction.
New standalone queue settings page
Google Cloud CCaaS now includes a standalone Queue Menu Settings page for each queue in your instance. These pages are separate from (but identical to) the Queue Menu Settings pages at Settings > Queue > Edit / View > YOUR_QUEUE. The standalone pages load faster and you can quickly access them in the following ways:
From the Queues page (access this by clicking the Queues menu). Links to the standalone Queue Menu Settings pages are in the Queue Name column.
From the Phone Number Management pane at Settings > Call > Phone Numbers > Phone number management. Links to the Queue Menu Settings pages are in the Assigned Queues / Agents column.
Using a URL that identifies the queue. Example:
https://YOUR_CCAAS_HOST/queues/QUEUE_ID/LANGUAGE_CODE
Links to standalone Queue Menu Settings pages are active only for users with permissions to view queue settings. For more information, see Access queue menu settings.
Virtual task assistant support in the chat platform API
The chat platform API now provides improved support for virtual task assistants. When an agent transfers a chat to a virtual task assistant, your application can send and receive messages from the virtual task assistant. Enhanced webhooks provide the virtual task assistant's message content instantly, streamlining private, automated workflows like collecting sensitive information.
Documentation is coming soon.
We addressed the following issues in this release:
Fixed an issue where Agent Assist generated incomplete or inaccurate chat summaries.
Fixed inaccurate reporting for chats escalated by a virtual agent to a human agent.
Fixed incorrect labeling and routing of French voicemails to the English-language queue in the agent adapter.
Fixed the missed response timer, which added an extra 30 minutes to the calculated time.
Fixed a significant slowdown in background job processing.
Fixed an issue where the global default voicemail greeting failed to save when applied to an individual user's settings.
Fixed an issue that caused agents to be assigned a call and a chat at the same time, even when this was disabled in the settings.
Fixed an issue that prevented users from testing Android push notifications.
Fixed an issue where editing a phone number's settings on the Phone Number Management page removed it from queues where it was assigned for outbound calls.
Fixed an issue that caused a Custom roles permissions is invalid error when attempting to save a change to the Audit Dashboard permission in a custom role.
Fixed an issue that caused the handle time for queued chats to display an incorrect value, particularly after a session transfer.
Fixed an issue where the call ID was missing in the Activity Timeline report.
Fixed an issue where the Auto answered label on a chat tab in the chat adapter persisted even after an agent opened the chat.
Fixed an issue where the agent directory in the call adapter appeared empty when an agent attempted to transfer a call.
Fixed an issue that prevented an agent from adding another agent to a call using their extension number.
Fixed an agent desktop issue where unsigned data appeared before signed data in the Session Data Feed panel. This was inconsistent with the display order in the agent adapter.
Fixed an issue at Settings > Developer Settings > CRM > Custom CRM > CRM lookup method > Custom Link. In the Custom link CRM lookup section, we replaced the incorrect
{Custom UID}variable name with{CUID}in the UI text.Fixed a web SDK issue where the Select an option channel selection screen appeared unnecessarily when a chat started, when the Direct Action Parameter was enabled.
Improved web SDK page loading speed.
Fixed a web SDK issue where external deflection links weren't working correctly.
Restrict the transfer of email sessions to a queue
You can now configure queues to prevent them from receiving email session transfers.
Administrators: A new Allow incoming Email Transfers toggle appears in the settings pane at Settings > Queue > Email > Edit / View > YOUR_QUEUE.
For more information, see Transfer email sessions to a queue.
Alvaria Advanced List Management integration with outbound dialer
You can now integrate Alvaria Advanced List Management (ALM) with the outbound dialer. This lets you combine Alvaria's list and campaign management capabilities with the dialing capability of Google Cloud CCaaS. This integration exchanges contact and result files through a shared Cloud Storage bucket.
Capabilities:
Multi-tenancy support: helps ensure that each tenant's data remains separate and secure
Flexible delimiter support: supports files using comma, pipe, tab, or semicolon delimiters
For more information, see Alvaria Advanced List Management integration.
Chat check-in
Users of the web SDK can use chat check-in to help ensure that end-users are present and ready to engage before connecting them to a human agent. This helps to reduce the time lost when agents wait for end-users who have abandoned a chat.
When an end-user reaches the front of the chat queue, the system asks if they're still available. If there's no response after the amount of time you configure, the system removes the end-user from the queue. If the end-user rejoins the queue, you can configure whether they rejoin at the front or the back of the queue.
Documentation is coming soon.
Email signatures
You can now define standardized signatures for all outgoing emails sent from a specific queue.
Administrators: A new Email Signatures section appears in the settings pane at Settings > Queue > Email > Edit / View > YOUR_QUEUE.
For more information, see Email signatures.
Virtual agent aliases
You can assign a public-facing alias to each of your virtual agents. When all of your virtual agents have the same alias, they each appear to have the same name to end-users. This gives the impression that a single virtual agent is handling a session even if the session is transferred between virtual agents. You can assign virtual agent aliases to both support agents and virtual task assistants. Virtual agent aliases are used in the web SDK, the mobile SDKs, in system messages, and in transcripts.
Administrators: A new Virtual Agent Alias checkbox appears in the following dialogs:
The Add a Customer Support Agent dialog at Settings > Virtual Agent > Virtual Agents > Add virtual agent > Customer Support
The Add a Virtual Task Assistant dialog at Settings > Virtual Agent > Virtual Agents > Add virtual agent > Task Assistant
For more information, see Virtual agent aliases.
New chat platform API endpoint for getting media files
You can use the new chat platform API endpoint to get the media file that an agent sends to an end-user during a chat session. Your custom chat application can then make the media file available to the end-user during the session.
New endpoint: /apps/api/v1/chats/CHAT_ID/media/MEDIA_ID
For more information, see Agent file attachments with the chat platform API.
Dial pad improvements
The dial pad in the agent adapter now includes the following:
Country code selector
Outbound number, Language, and Queue selectors
If you use a CRM with flexible outbound dialing turned on, the Outbound number and Language selectors appear in the Outbound call details screen.
Documentation is coming soon.
Google Cloud CCaaS 3.42
We've released version 3.42 of Google Cloud CCaaS.
The timing of the update to your instance depends on the deployment schedule that you have chosen. For more information, see Deployment schedules.
Google Threat Intelligence: Version 6.0
The following new action has been added:
- Get Related Associations
Splunk: Version 59.0
Refactored the following integration items to use the new API endpoints:
Ping
Get Host Events
Splunk Notable Events Connector
Sync Splunk ES Closed Events
Sync Splunk ES Comments
Cofense Triage: Version 14.0
Added the ability to filter based on category to the following connector:
- Cofense Triage - Reports Connector
Google Chronicle: Version 68.0
Improved error handling in the following jobs:
Google Chronicle Sync Job
Google Chronicle Alerts Creator Job
Okta: Version 11.0
Updated the pagination processing mechanism in the following actions:
List Users
Add Group
Get Group
List Providers
SentinelOneV2: Version 44.0
Updated the mechanism for fetching agent information in the following actions:
Disconnect Agent From Network
Enrich Endpoint
Get Agent Status
Get Application List For Endpoint
Get Events For Endpoint Hours Back
Initiate Full Scan
Move Agents
Reconnect Agent To The Network
Google Threat Intelligence: Version 6.0
The following new action has been added:
- Get Related Associations
Splunk: Version 59.0
Refactored the following integration items to use the new API endpoints:
Ping
Get Host Events
Splunk Notable Events Connector
Sync Splunk ES Closed Events
Sync Splunk ES Comments
Cofense Triage: Version 14.0
Added the ability to filter based on category to the following connector:
- Cofense Triage - Reports Connector
Google Chronicle: Version 68.0
Improved error handling in the following jobs:
Google Chronicle Sync Job
Google Chronicle Alerts Creator Job
Okta: Version 11.0
Updated the pagination processing mechanism in the following actions:
List Users
Add Group
Get Group
List Providers
SentinelOneV2: Version 44.0
Updated the mechanism for fetching agent information in the following actions:
Disconnect Agent From Network
Enrich Endpoint
Get Agent Status
Get Application List For Endpoint
Get Events For Endpoint Hours Back
Initiate Full Scan
Move Agents
Reconnect Agent To The Network
Google Threat Intelligence: Version 6.0
The following new action has been added:
- Get Related Associations
Splunk: Version 59.0
Refactored the following integration items to use the new API endpoints:
Ping
Get Host Events
Splunk Notable Events Connector
Sync Splunk ES Closed Events
Sync Splunk ES Comments
Cofense Triage: Version 14.0
Added the ability to filter based on category to the following connector:
- Cofense Triage - Reports Connector
Google Chronicle: Version 68.0
Improved error handling in the following jobs:
Google Chronicle Sync Job
Google Chronicle Alerts Creator Job
Okta: Version 11.0
Updated the pagination processing mechanism in the following actions:
List Users
Add Group
Get Group
List Providers
SentinelOneV2: Version 44.0
Updated the mechanism for fetching agent information in the following actions:
Disconnect Agent From Network
Enrich Endpoint
Get Agent Status
Get Application List For Endpoint
Get Events For Endpoint Hours Back
Initiate Full Scan
Move Agents
Reconnect Agent To The Network
November 18, 2025
Apigee API hubNew API deployments view
API deployment information is now available as a separate tab in the API details page. You can view your API deployment details, create new deployments, and manage existing deployments using the API deployments tab.
For more information, see Manage deployments.
The issue relating to API hub provisioning failures in data residency enabled Apigee organizations is now resolved. You can now provision API hub within an Apigee organization that has data residency enabled.
For information about provisioning API hub, see Provision API hub in the Cloud console.
New tutorial: Ingest Microsoft Azure API data into API hub
A new tutorial is available for ingesting Microsoft Azure API data into API hub.
This tutorial shows you how to ingest API metadata from Azure API Management (APIM) into Apigee API hub. It uses a pre-built Application Integration template and a set of custom scripts on GitHub to perform a manual, on-demand ingestion of your API data.
For more information, see Ingest Microsoft Azure API data into API hub.
Dataform now lets you automate the creation of BigLake tables for Apache Iceberg in BigQuery. This feature is generally available (GA).
BigQuery ML now supports the following generative AI functions:
AI.GENERATE: generate free text to accomplish a wide range of tasks, such as translation, summarization, and classification, on any unstructured data, including images, audio, video, and documents. It can also perform entity extraction and generate structured output. This function is generally available (GA).AI.EMBED: turn text, image, audio, video, or documents into embeddings. This function is in Preview.AI.SIMILARITY: compute the semantic similarity between pairs of text, pairs of images, or across text and images. This function is in Preview.- You can use the
AI.GENERATE_BOOL,AI.GENERATE_DOUBLE, andAI.GENERATE_INTfunctions to generate scalar values, which are convenient for filtering, scoring, and counting purposes. - Each of these functions supports authentication with end-user credentials (EUC) to set up the necessary Vertex AI permissions.
BigQuery ML now supports the following table-valued generative AI functions:
AI.GENERATE_TABLE: generate a table of structured output from unstructured data including text, images, audio, and video.AI.GENERATE_TEXTis the new, preferred version ofML.GENERATE_TEXT, which has the same functionality but with simplified column output names.AI.GENERATE_EMBEDDINGis the new, preferred version ofML.GENERATE_EMBEDDING, which has the same functionality but with simplified column output names.- These functions are all generally available (GA).
You can now use Gemini 3.0
when you call generative AI functions in BigQuery,
such as AI.GENERATE.
You must use the full global endpoint argument:
https://aiplatform.googleapis.com/v1/projects/PROJECT_ID/locations/global/publishers/google/models/gemini-3-pro-preview.
You can now publish data insights, including query recommendations and auto-generated table and column descriptions, to the Dataplex Universal Catalog. This feature is in Preview.
Database Migration Service now supports the one-time migration type for all heterogeneous migration scenarios. For more information, see the following pages:
Database Migration Service for homogeneous PostgreSQL migrations to Cloud SQL for PostgreSQL now supports PostgreSQL version 18. For more information, see Supported source and destination databases.
Cloud SQL for MySQL 8.4.6 is upgraded to MySQL 8.4.7. For more information, see the MySQL 8.4.7 Release Notes.
The following rollouts have completed for managed Cloud Service Mesh:
- 1.21.6-asm.4 has rolled out to the rapid release channel.
- 1.20.8-asm.56 has rolled out to the regular release channel.
- 1.19.10-asm.52 has rolled out to the stable release channel.
- CNI and MDPC version 1.20.8-asm.56 has rolled out to all release channels.
While the managed data plane automatically updates Envoy Proxies by restarting workloads, you must manually restart any StatefulSets and Jobs.
Preview: The general purpose C4 machine series now supports the following machine types on Intel's Xeon 6 processor (Granite Rapids):
c4-standard-288-lssd-metalc4-highmem-288-lssd-metal
To learn more, see the C4 machine series.
For more information, see Machine types that automatically attach Local SSD disks and Bare metal instances on Compute Engine.
You can autoscale a regional managed instance group
(MIG) that has the target distribution shape set to ANY or ANY_SINGLE_ZONE.
These shapes are particularly beneficial for batch workloads.
For more information about target distribution shapes, see
Regional MIG target distribution shape.
Dataform now lets you automate the creation of BigLake tables for Apache Iceberg in BigQuery. This feature is generally available (GA).
Gemini Enterprise: Use Gemini 3
You can now use Gemini 3 in preview with Gemini Enterprise. To make Gemini 3 available to users in your Gemini Enterprise app, a Gemini Enterprise admin must enable the Gemini 3 Pro (Preview) toggle in the Model availability feature control. For more information on feature controls, see Manage features on the web app.
Gemini Enterprise: Sources from model
In the Sources panel of an answer, Gemini Enterprise shows other sources used by the Gemini models.
Gemini Enterprise: Microsoft OneDrive @mentions
You can use the @ symbol within your chats to mention and reference files in the connected Microsoft OneDrive data sources.
Gemini Enterprise: View generated images and videos
You can view chats and download your generated images and videos using the Library. For more information, see View and download generated images and videos.
Oracle Database@Google Cloud adds the following regions and zones for its services:
Exadata Database Service
australia-southeast1-b-r1(Sydney, Australia)northamerica-northeast2-a-r2(Toronto, Canada)
Exadata Database Service on Exascale infrastructure
us-central1-a-r1(Iowa, North America)us-west3-a-r1(Salt Lake City, North America)
Autonomous Database Service
northamerica-northeast2(Toronto, Canada)
For a full list of supported locations, see Supported regions and zones.
November 17, 2025
Apigee AnalyticsOn November 17, 2025 we released an updated version of Apigee Analytics.
Support for aggregate data in Error Code Analysis, Cache Performance, and Target Performance charts
Announcing support for viewing aggregate data in the Error Code Analysis, Cache Performance, and Target Performance Analytics dashboards.
For information on the Analytics dashboards, see Use the Analytics dashboards.
| Bug ID | Description |
|---|---|
| 446973091 |
Proxy editor endpoint view is now disabled if there are over 200 flows configured in proxy endpoints. When opening the proxy editor endpoint view with a proxy that has over 200 flows, the proxy graph is no longer rendered, and instead you are presented with a message informing you that there are too many flows to render. This action addresses a performance issue that made the proxy editor unusable when there were over 200 flows configured. |
On November 17, 2025, we released an updated version of the Apigee UI.
On November 17, 2025 we released an updated version of Apigee Analytics.
Support for aggregate data in Error Code Analysis, Cache Performance, and Target Performance charts
Announcing support for viewing aggregate data in the Error Code Analysis, Cache Performance, and Target Performance Analytics dashboards.
For information on the Analytics dashboards, see Use the Analytics dashboards.
On November 17, 2025, we released an updated version of Apigee (1-16-0-apigee-5).
Secure and validate documents using WS-Security with X.509 certificates
You can now secure and validate SOAP documents using WS-Security with X.509 certificates using crypto object methods. See Secure SOAP documents using WS-Security with X.509 certificates and Validate SOAP documents using WS-Security with X.509 certificates.
| Bug ID | Description |
|---|---|
| N/A | Updates to security, infrastructure, and libraries. |
| Bug ID | Description |
|---|---|
| 454672970 | Added strict input validation to the SetIntegrationRequest policy |
App Hub now supports new metadata properties to provide deeper context and governance for your services and workloads:
- Functional type: Services and workloads now include the
FunctionalTypeproperty, which is an output-only field that identifies the known function of a resource. The initial supported value isAGENT, which indicates that a workload is an AI agent. - Extended metadata: Services and workloads now include the
ExtendedMetadataproperty to provide rich, structured, and schema-driven information about the resource, such as theapphub.googleapis.com/AgentPropertiesschema for AI agents. - Registration type: Services now have the
RegistrationTypeproperty. This output-only field indicates whether a service is exclusive (can be registered to only one application) or shared (can be registered to multiple applications). To view the registration type of your services, see View details of services and workloads. - Identity: Services and workloads now include the
Identityproperty, which is an output-only field that contains the service account or managed workload identity name for a service or workload.
In the query execution graph, you can now use the query text heatmap to identify which query text contributes to stages that consume more slot time, and to see query plan details for those stages. This feature is in Preview.
You can use folders to organize and control access to single file code assets, such as notebooks, saved queries, data canvases, and data preparation files. This feature is in Preview.
You can now share SQL stored procedures in BigQuery sharing listings and enable role-based authorization for stored procedures. These features are in preview.
New Airflow builds are available in Cloud Composer 3:
Airflow 3 is available in Preview in Cloud Composer 3.
All Cloud Composer environment's GKE clusters are set up with maintenance exclusions from December 16, 2025 to January 2, 2025. For more information, see Maintenance exclusions.
You can create a Remote Direct Memory Access (RDMA) over converged ethernet (RoCE) Virtual Private Cloud (VPC) network and configure firewall rules that apply to the network. For more information, see Cloud NGFW for RoCE VPC networks. This feature is available in General Availability.
Cloud Run and Cloud Run functions source deployments support pyproject.toml
file for managing dependencies. If you use a pyproject.toml file, source deployments
use one of the following to find and install dependencies:
pipuvpoetry
For more information, see Deploy Python applications with a pyproject.toml
file (Preview).
Cloud SQL now offers a free trial instance for both existing and new Google Cloud customers. A free trial instance lets you test advanced Cloud SQL capabilities and features for up to 30 days without any financial commitment.
For information about a free trial instance, and its inclusions and conditions, see Free trial instance overview.
Cloud SQL now offers a free trial instance for both existing and new Google Cloud customers. A free trial instance lets you test advanced Cloud SQL capabilities and features for up to 30 days without any financial commitment.
For information about a free trial instance, and its inclusions and conditions, see Free trial instance overview.
cos-dev-129-19386-0-0
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.57 | v27.5.1 | v2.1.4 | See List |
Updated app-containers/runc to v1.3.3.
Added support for the Lustre 2.14.0_p224 drivers.
Updated the Google OS Config Agent package to version 20250522.00.
Updated the OS Login package to version 20251022.00.
Runtime sysctl changes:
- Changed: fs.file-max: 811473 -> 811420
Backported various TCPDirect networking fixes.
cos-121-18867-294-25
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.113 | v27.5.1 | v2.0.6 | See List |
Updated app-containers/runc to v1.2.8.
Added support for the Lustre 2.14.0_p224 drivers.
Backported an upstream commit to fix high CPU usage when trying to find suitable blocks in ext4 fs.
Runtime sysctl changes:
- Changed: fs.file-max: 811813 -> 811764
cos-117-18613-439-28
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.111 | v24.0.9 | v1.7.28 | See List |
Updated app-containers/runc to v1.2.8.
Added support for the Lustre 2.14.0_p224 drivers.
Backported an upstream commit to fix high CPU usage when trying to find suitable blocks in ext4 fs.
Runtime sysctl changes:
- Changed: fs.file-max: 811751 -> 811818
cos-113-18244-521-23
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.1.155 | v24.0.9 | v1.7.27 | See List |
Updated app-containers/runc to v1.2.8.
Fixed CVE-2025-40040 in the Linux kernel.
Fixed CVE-2025-40109 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 812054 -> 812007
cos-125-19216-104-25
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.55 | v27.5.1 | v2.1.4 | See List |
Runtime sysctl changes:
- Changed: fs.file-max: 811458 -> 811512
Backported various TCPDirect networking fixes.
Previously, data profile scan results were published only to the Google Cloud console. You can now publish the results of a data profile scan as Dataplex Universal Catalog metadata. The latest results are saved to the entry that represents the source table. You can view the results in the Google Cloud console.
If you want to enable catalog publishing for an existing data profile scan, you must edit the scan and re-enable the publishing option.
For more information, see Use data profiling.
This feature is generally available (GA).
Datastream now supports partitioning and clustering for BigQuery destinations. For more information, see the documentation.
Gemini Enterprise: Register ADK and A2A agents
You can register your ADK agents that are hosted on the Vertex AI Agent Engine and your agents that were built using the Agent-to-Agent (A2A) protocol with Gemini Enterprise. This makes the agents available to your users on the Gemini Enterprise web app.
For more information, see:
Gemini Enterprise: Authorize assistant actions from the chat box
If actions are enabled for a data source, the user sees an Enable Actions button next to the data source listing in the assistant chat box. The user must click this button and complete authorization before they can use the assistant actions associated with the data source.
Veo video generation
Veo 3.1 is Generally Available, and introduces the following models:
For more information, see the following:
Advanced reporting dashboards version 3.41
We've released version 3.41 of the advanced reporting dashboards.
We addressed the following issues in this release:
- Fixed an issue where the Chat Agent Metrics (Historical) explore and the Agent Metrics (Historical) explore returned different data for chats handled. This resulted in inconsistent chat handling metrics in dashboards.
- Fixed an issue where ambiguous metrics names appeared in the Call Queue Metrics (Historical) explore.
- Fixed an issue where the average active concurrency metric appeared as a total instead of a percentage.
- Fixed an issue where the CSAT values on the CSAT and Agent Performance dashboards were not consistent with each other.
- Changed the Caller ANI table heading to Consumer phone number in all of the tables it appeared in.
- Fixed an issue where Call ID on the Calls Transfer dashboard was not correctly formatted.
- Fixed an issue where the column headings in the Agent Productivity table of the Agent Performance dashboard were ordered incorrectly.
- Fixed an issue on the Dispositions - Chat dashboard where the Disposition Codes filter wasn't working correctly.
- Fixed an issue on the Dispositions - Chat dashboard where the Disposition Code filter was unable to find existing disposition codes.
- Fixed an issue on the Dispositions - Chat dashboard where the Direction filter didn't display the available values.
- Fixed an issue on the Dispositions - Chat dashboard where the Agent Name filter wasn't working correctly.
- Fixed an issue on the Dispositions - Chat dashboard where the Disposition Distribution tile displayed the disposition codes in the wrong order.
- Fixed an issue on the Dispositions - Calls dashboard where the Disposition Code filter didn't find existing disposition lists.
- Fixed an issue on the Dispositions - Calls dashboard where agents didn't appear in the Dispositions by Agent table when filtering by Agent ID.
- Fixed an issue where dismissed chat time was being included with current chat time metrics on the Agent Monitoring dashboard.
Campaigns dashboard
We've added a new Campaigns dashboard that displays real-time and historical performance metrics for call campaigns, including call outcomes, campaign volumes, and agent metrics. Managers can use this information to monitor call campaigns and make data-driven decisions to improve campaign performance. For more information, see Campaigns dashboard.
All Interactions dashboards: updates to tables
On the All Interactions - Calls dashboard, we did the following:
- Renamed the All Call Interactions (Historical) table to Call Metrics Detail.
- Updated the formatting of the column headings in the Virtual Agent Interactions table.
On the All Interactions - Chats dashboard, we renamed the All Chat Interactions (Historical) table to Chat Metric Detail.
For more information, see All interactions dashboards.
Real-time dashboard optimization
We've optimized real-time dashboards to provide faster loading and refresh times.
NVIDIA recommends that Kubernetes clusters enable Coherent Driver-Based Memory Management (CDMM) to resolve memory over-reporting. CDMM is enabled by default on A4X nodes running the R580 GPU driver in GKE clusters with the following versions:
- 1.33 or later: 1.33.4-gke.1036000 or later
- 1.32: 1.32.8-gke.1108000 or later
CDMM allows GPU memory to be managed through the driver instead of the operating system (OS), avoiding OS onlining of GPU memory, and exposing the GPU memory as a Non-Uniform Memory Access (NUMA) node to the OS.
For more information about CDMM, see Hardware and Software Support. To create GKE clusters with A4X, see the following documents:
The /node/server/healthy
metric is Generally Available.
You can now use Hyperdisk Storage Pools with migrating VMs if you need large-scale storage. Hyperdisk Storage Pools help you manage large-scale storage and can optimize costs and performance.
The following AI Protection features are available:
- AI Security dashboard: The dashboard has an updated AI Inventory section, which includes an overview of AI agents.
- Assets page: You can filter for AI resources, including AI agents that are deployed to Vertex AI Agent Engine.
AI Protection is available in Preview to the Security Command Center Enterprise tier.
Agent Engine Threat Detection, a built-in service of Security Command Center, is available in Preview to the Security Command Center Enterprise and Premium tiers. This service helps you detect and investigate potential attacks on AI agents that are deployed to Vertex AI Agent Engine Runtime.
For authorization extensions, in addition to the ext_proc Envoy gRPC API, the ext_authz gRPC API is also supported. This capability allows seamless integration with the broader authorization ecosystem. This feature is in Preview.
M135 release
The M135 release of Vertex AI Workbench instances includes the following:
- Patched an issue where user-triggered OS shutdowns aren't reported to the Notebooks API.
November 16, 2025
Google SecOps SIEMRelease 6.3.68 is being rolled out to the first phase of regions as listed here.
This release contains the following changes:
Change views per alert
The Alert Overview page now includes a new option to select a specific view for each alert. If several playbooks have run on an alert, and those playbooks have customized views, you can now select and display any of those customized views for that alert.
Release 6.3.68 is being rolled out to the first phase of regions as listed here.
This release contains the following changes:
Change views per alert
The Alert Overview page now includes a new option to select a specific view for each alert. If several playbooks have run on an alert, and those playbooks have customized views, you can now select and display any of those customized views for that alert.
November 15, 2025
Google SecOps SIEMRelease 6.3.67 is now available for all regions.
Release 6.3.67 is now available for all regions.
November 14, 2025
App HubApp Hub has expanded its support for Google Cloud resources. You can now register services and workloads from a wide range of products to your applications, including new resources from Access Approval, Certificate Authority Service, Cloud Run, Firebase, Gemini for Google Cloud, GKE Multi-Cloud, and more. Many of these supported resources are available in Preview. For a complete list, see App Hub supported resources.
Management projects are now Generally Available (GA) to enable application management in folders. This setup model is recommended for all new App Hub implementations and provides a centralized and scalable way to organize, deploy, and govern your applications.
Key features of this release include:
- App-enabled folders: You can now enable application management on a standard Google Cloud folder, which then becomes an app-enabled folder. This folder acts as the application management boundary for your App Hub applications.
- Management projects: A dedicated management project is automatically created within your app-enabled folder to store application metadata and configurations, and to centralize operations.
- Simplified API management: Required APIs for core App Hub features are automatically enabled on the management project. You can also enable recommended APIs to access the full application lifecycle experience.
- Flexible billing: Linking a billing account is now optional. You can use App Hub's core features for organizing and observing your applications at no cost. A billing account is required only for other application-centric features.
For more information on how to get started, see Set up App Hub with app-enabled folders.
Cloud Run and Cloud Run functions source deployments support pyproject.toml
file for managing dependencies. If you use a pyproject.toml file, source deployments
use one of the following to find and install dependencies:
pipuvpoetry
For more information, see Deploy Python applications with a pyproject.toml
file (Preview).
You can now start Gemini Cloud Assist investigations for failed Airflow tasks.
You can now view Active Assist cost optimization recommendations in Cloud Hub is now in Preview.
Cloud SQL for MySQL now supports read pool autoscaling (GA), which helps you more easily manage your application's workload needs.
This feature automates read pool scale in and scale out operations based on one or both of the following conditions:
- Allowed CPU usage of the read pool
- Allowed number of client connections to the read pool
Cloud SQL for PostgreSQL now supports read pool autoscaling (GA), which helps you more easily manage your application's workload needs.
This feature automates read pool scale in and scale out operations based on one or both of the following conditions:
- Allowed CPU usage of the read pool
- Allowed number of client connections to the read pool
You can now use the Google Cloud console to relocate buckets. Using bucket relocation, you can move an existing bucket from one location to another without changing the bucket's name or requiring manual transfer of data within the bucket.
Config Connector version 1.138.0 is now available.
New Beta Resources (Direct Reconciler):
BackupDRBackupVaultOrgPolicyCustomConstraint
Bug Fixes:
- Fixed format validation issue in the
DataflowFlexTemplateJobdirect controller when thespec.subnetworkRef.externalfield contains full URL. - Updated
status.observedGenerationinConfigConnectorobject.
New Alpha Resources (Direct Reconciler):
FirestoreBackupScheduleFirestoreDocument
Reconciliation Improvements:
- Improved Normalization logic for
OrgPolicy,RunJob,TagsTagBinding, andVertexAIIndexresources.
cos-125-19216-104-23
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.55 | v27.5.1 | v2.1.4 | See List |
Updated app-containers/runc to v1.3.3.
Fixed a bug where setting MTU above 9000 on ARM systems with a 64k page size would cause IDPF networking to fail.
Runtime sysctl changes:
- Changed: fs.file-max: 811489 -> 811458
VMware Engine ve2 nodes are now available in the Tokyo, Japan region (asia-northeast1-a).
(2025-R47) Security updates
This release includes new GKE versions that use updated Container-Optimized OS images. These updated images are cumulative, incorporating security fixes from all Container-Optimized OS versions released since the previous GKE release.
To identify the specific vulnerabilities that were resolved in each updated Container-Optimized OS image, see the Security release notes for that image. The following table includes links to the release notes for each updated Container-Optimized OS image:
| GKE version | Container-Optimized OS version | Details |
|---|---|---|
| 1.34.1-gke.2037002 | cos-125-19216-0-94 | cos-125-19216-0-94 release notes |
| 1.34.1-gke.2909000 | cos-125-19216-0-115 | cos-125-19216-0-115 release notes |
(2025-R47) Version updates
GKE cluster versions have been updated.
New versions available for upgrades and new clusters.
The following versions are now available for new GKE clusters, and for manual control plane upgrades and node upgrades for existing clusters. For more information about versioning and upgrades, see GKE versioning and support and About GKE cluster upgrades.
Rapid channel
- The following versions are now available in the Rapid channel:
- Version 1.34.1-gke.1829001 is no longer available in the Rapid channel.
Regular channel
- The following versions are now available in the Regular channel:
Stable channel
There are no new releases in the Stable channel.
Extended channel
- The following versions are now available in the Extended channel:
No channel
- The following versions are now available:
- The following node versions are now available:
(2025-R47) Version updates
- The following versions are now available in the Extended channel:
(2025-R47) Version updates
- The following versions are now available:
- The following node versions are now available:
(2025-R47) Version updates
- The following versions are now available in the Rapid channel:
- Version 1.34.1-gke.1829001 is no longer available in the Rapid channel.
(2025-R47) Version updates
- The following versions are now available in the Regular channel:
(2025-R47) Version updates
There are no new releases in the Stable channel.
The Vertex AI Search for commerce Merchandising console introduces self-serve and agentic explainability for issue diagnosis. Streamlined governance is supported with distinct Creator and Approver roles. New features enhance preview and provide real-time control application feedback.
For more information, see Serving controls in the Merchandising console.
Data Security Posture Management (DSPM) supports the Security Command Center Premium tier at the organization level.
Vertex AI Search: Gemini layout parser (Public Preview)
For data stores with unstructured documents, you can use Gemini to get layout analysis and content extraction on PDF files. Layout parsing with Gemini provides high quality table recognition, improved reading order and more accurate text recognition.
This feature is in Public Preview. For more information, see Parse and chunk documents.
Dynamic Private Service Connect interfaces are available in General Availability. Private Service Connect interfaces let service producers initiate connections to service consumers. You can update a VM instance to add or remove dynamic Private Service Connect interfaces without needing to restart or recreate the instance.
For more information, see Private Service Connect interface types.
November 13, 2025
AlloyDB for PostgreSQLAlloyDB AI native vector search accelerator is now generally available (GA). It includes the following features and improvements:
- The
google_columnar_engineextension is updated to automatically recommend data for searches, so you don't need to manually add vector columns to the table. For more information, see Perform a vector search. - The
alloydb_scannextension is updated with new metrics for vector index creation. You can now use the pg_stat_ann_index_creation view to see the number of rows present in a table at the time of index creation.
Cloud CDN lets you add custom code to the request processing path of global external Application Load Balancers by using Service Extensions edge extensions (pre-cache) and traffic extensions (post-cache). These extensions help you manipulate request headers early in the processing lifecycle to influence caching and routing decisions. This feature is in General Availability.
The Cloud KMS Encryption metrics dashboard is available in Preview. The dashboard shows the following metrics for the selected project to help you understand your CMEK usage:
- Resources in this project by protection type
- Alignment to key usage recommended practices
- Resource protection type by service
To learn more about the Encryption metrics dashboard, including its limitations, see View encryption metrics.
You can create a firewall endpoint that supports jumbo frames up to 8,500 bytes in size. For more information, see Supported packet size. This feature is available in General Availability.
You can deploy services to Cloud Run using a Compose file (Preview).
Cloud SQL for MySQL now lets you have more control over the number of results
that are returned when you perform an ANN vector search with filters.
You can use iterative filtering when the selective filters of the
WHERE clause in your ANN search query produce fewer results
than the number of results specified in your LIMIT clause.
To enable iterative filtering for your ANN search query, set the
cloudsql_vector_iterative_filtering flag to ON.
You can set the flag at a session or global level.
To enable and use iterative filtering for your ANN search query, you must have
[MYSQL_$VERSION].R20251004.01_07
or later installed on your MySQL instance.
For more information, see Search approximate nearest neighbors (ANN).
Version 20251107.01 of the guest agent
is now available.
Version 20251107.01 includes a fix for the
Startup script runner component
that prevented it from writing status logs and script output to Cloud Logging.
Preview: Future reservation requests in calendar mode support reserving
capacity for a3-megagpu-8g and a3-highgpu-8g machine types. Use future
reservation requests in calendar mode to obtain resources for running model
pre-training, model fine-tuning, simulation, and inference workloads. For more
information, see
About future reservation requests in calendar mode.
You can use custom constraints with Organization Policy to provide more
granular control over specific fields for the CompilationResult,
ReleaseConfig, WorkflowConfig, WorkflowInvocation, and Workspace
resources. For more information, see
Create custom organization policy constraints.
This feature is
generally available
(GA).
New Serverless for Apache Spark runtime versions:
- 1.2.62
- 2.2.62
- 2.3.15
Serverless for Apache Spark: Added the
dataproc.artifacts.remove property,
which lets users remove default artifacts, such as spark-bigquery-connector,
iceberg, and delta-lake from a Serverless for Apache Spark runtime.
Known issue in VS Code 2.57 and later
The Gemini Code Assist 2.57 and later releases for VS Code have a known issue that prevents the extension from connecting to the server if you are using a gnc c runtime version that's earlier than 2.36.
You can permanently fix this issue by upgrading your gnu c runtime version to 2.36 or higher.
Alternatively, you can downgrade the Gemini Code Assist VS Code extension to version 2.56 until a fix is released.
VS Code server connection issue fixed as of version 2.58.1
The server connection issue affecting Gemini Code Assist 2.57 and 2.58 releases is fixed as of version 2.58.1
Known issue in VS Code 2.57 and later
The Gemini Code Assist 2.57 and later releases for VS Code have a known issue that prevents the extension from connecting to the server if you are using a gnc c runtime version that's earlier than 2.36.
You can permanently fix this issue by upgrading your gnu c runtime version to 2.36 or higher.
Alternatively, you can downgrade the Gemini Code Assist VS Code extension to version 2.56 until a fix is released.
VS Code server connection issue fixed as of version 2.58.1
The server connection issue affecting Gemini Code Assist 2.57 and 2.58 releases is fixed as of version 2.58.1
Updated Prompt Caching for Anthropic Claude Models
Prompt caching for Anthropic Claude models now supports a one-hour Time To Live (TTL).
For more information, see Prompt caching.
Kimi K2 Thinking is available in Model Garden. This model is a thinking model that excels at complex problem-solving and deep reasoning. Kimi K2 Thinking is available as a managed API in Model Garden. To learn more, see Kimi K2 Thinking.
Raw log search enhancements
Google SecOps now includes enhancements to raw log search to boost usability, performance, and data analysis:
New filtering options: Filter raw log results by their parsing status or by one or more log sources.
Optimized results view: Expand or collapse the Trend over time graph, providing more space for results.
Download raw log results: Download raw log results to a CSV file. By default, the Timestamp, Event Type, and Raw log columns are included. You can select additional columns through Column Manager.
Enhanced search visibility: The search query and applied filters are now displayed on the Search page.
New API for raw log search: Use the legacySearchRawLogsV2 API to search for raw logs within a specified Google SecOps instance.
For more details, see the following topics:
Raw log search enhancements
Google SecOps now includes enhancements to raw log search to boost usability, performance, and data analysis:
New filtering options: Filter raw log results by their parsing status or by one or more log sources.
Optimized results view: Expand or collapse the Trend over time graph, providing more space for results.
Download raw log results: Download raw log results to a CSV file. By default, the Timestamp, Event Type, and Raw log columns are included. You can select additional columns through Column Manager.
Enhanced search visibility: The search query and applied filters are now displayed on the Search page.
New API for raw log search: Use the legacySearchRawLogsV2 API to search for raw logs within a specified Google SecOps instance.
For more details, see the following topics:
Raw log search enhancements
Google SecOps now includes enhancements to raw log search to boost usability, performance, and data analysis:
New filtering options: Filter raw log results by their parsing status or by one or more log sources.
Optimized results view: Expand or collapse the Trend over time graph, providing more space for results.
Download raw log results: Download raw log results to a CSV file. By default, the Timestamp, Event Type, and Raw log columns are included. You can select additional columns through Column Manager.
Enhanced search visibility: The search query and applied filters are now displayed on the Search page.
New API for raw log search: Use the legacySearchRawLogsV2 API to search for raw logs within a specified Google SecOps instance.
For more details, see the following topics:
Version 20251107.01 of the guest agent
is now available.
Version 20251107.01 includes a fix for the
Startup script runner component
that prevented it from writing status logs and script output to Cloud Logging.
Filter control default values now accept parameters
You can now use parameters as default values in filter controls.
Modernized timeline chart
Timeline charts have a new modernized look by default and give you new options for customizing bar corner radius, axes, and grid.
New shapes
The Shapes menu has been enhanced and expanded to include new shape types for report editors. See Add text, images, lines, and shapes to your report to learn more.
For Exadata Database Service, Oracle Database@Google Cloud supports region asia-south1 (Mumbai, India).
For a full list of supported locations, see Regional availability.
You can use custom constraints with Organization Policy to provide more granular control over specific fields for some Dataform resources. For more information, see Create custom organization policy constraints. This feature is generally available (GA).
Edge extensions help you manipulate request headers early in the processing lifecycle of global external Application Load Balancers to influence caching and routing decisions. This feature is in General Availability.
Regional external and internal Application Load Balancers support route and traffic extensions using plugins. This feature is in Preview.
Speech-to-Text has just launched chirp_3 in public preview for the regions asia-south1, europe-west2, europe-west3 and northamerica-northeast1.
For more information about the Chirp 3 model, see Chirp 3 Transcription: Enhanced multilingual accuracy.
November 12, 2025
API GatewayOn November 12, 2025, we released a new version of API Gateway.
API Gateway now supports OpenAPI version 3.0.
With this release, API Gateway now supports OpenAPI version 3.0, including all patch versions (3.0.x).
Key Benefits:
- Simplified Deployment: Directly upload and deploy OpenAPI version 3.0.x specifications without prior conversion to 2.0.
- Enhanced Compatibility: Seamlessly integrate your OpenAPI version 3.0.x definitions with API Gateway.
For more detail, see OpenAPI overview.
On November 12, 2025, we released an updated version of the Apigee UI.
| Bug ID | Description |
|---|---|
| 455584175 |
Fixed a performance issue with Debug session UI Fixed an issue where performance of the Debug session was severely degraded when loading a Debug session with a moderate number of transactions. |
Support for Python 3.14 runtime is in Preview.
Support for Python 3.14 runtime is in Preview.
Cloud Endpoints now supports OpenAPI version 3.0.
With this release, Cloud Endpoints now supports OpenAPI version 3.0, including all patch versions (3.0.x).
Key Benefits:
- Simplified Deployment: Directly upload and deploy OpenAPI version 3.0.x specifications without prior conversion to 2.0.
- Enhanced Compatibility: Seamlessly integrate your OpenAPI version 3.0.x definitions with Cloud Endpoints.
For more detail, see OpenAPI overview.
Cloud Run source deployment supports Ubuntu 24
LTS base images (Preview). This builder is available under
gcr.io/buildpacks/builder:google-24. For more information, see
Builders.
Support for Python 3.14 runtime is in Preview. Starting from Python version 3.14 and later, the Python buildpack uses the uv package manager as the
default installer for the dependencies you specify in your requirements.txt file. You can also use pip as the default installer for these versions by setting the GOOGLE_PYTHON_PACKAGE_MANAGER environment variable to pip. For more information, see Specify dependencies in Python.
Support for Python 3.14 runtime is in Preview. Starting from Python version 3.14 and later, the Python Buildpack uses the UV package manager as the
default installer for the dependencies you specify in your requirements.txt file. You can also use pip as the default installer for these versions by setting the GOOGLE_PYTHON_PACKAGE_MANAGER environment variable to pip. For more information, see Specify dependencies in Python.
Cloud SQL for MySQL now supports minor version 8.0.44. To upgrade your existing instance to the new version, see Upgrade the database minor version.
Automated schema extraction for custom extractor processors is in Preview.
This feature allows you to automatically extract a document schema from a test document you supply. Then, you can approve or decline the schema and edit it manually. This saves time and effort when defining the document schema for your custom processor and allows you to focus on refining the schema.
When creating a custom extractor processor, find the Generate from document option in the Get started tab of the Google Cloud console.
Chat performance metrics
Gain deeper insights into Gemini for Google Cloud's chat performance with metrics for chat acceptance rate and lines of chat accepted, including interactions in Agent mode and non-agentic chat. Combine these metrics with existing code metrics to calculate total acceptance and total lines of code accepted, providing a complete picture of Gemini's performance. For more information, see View Gemini for Google Cloud logs.
Code customization available in agent mode and Gemini CLI (Preview)
Code customization is now supported when using Gemini CLI and agent mode in Gemini Code Assist.
Chat performance metrics
Gain deeper insights into Gemini for Google Cloud's chat performance with metrics for chat acceptance rate and lines of chat accepted, including interactions in Agent mode and non-agentic chat. Combine these metrics with existing code metrics to calculate total acceptance and total lines of code accepted, providing a complete picture of Gemini's performance. For more information, see View Gemini for Google Cloud logs.
Code customization available in agent mode and Gemini CLI (Preview)
Code customization is now supported when using Gemini CLI and agent mode in Gemini Code Assist.
Inline diff is generally available (GA) for IntelliJ
Inline diff is generally available for IntelliJ Gemini Code Assist. With the inline diff view, chat generated code suggestions are visually highlighted directly in your editor. This feature can boost productivity by offering immediate visibility on modifications, streamlining reviews and enabling precise control over integrating new code, all without leaving your current view.
If preferred, you can also change the diff view settings to have a side-by-side diff window instead of the inline diff.
Inline diff is generally available (GA) for IntelliJ
Inline diff is generally available for IntelliJ Gemini Code Assist. With the inline diff view, chat generated code suggestions are visually highlighted directly in your editor. This feature can boost productivity by offering immediate visibility on modifications, streamlining reviews and enabling precise control over integrating new code, all without leaving your current view.
If preferred, you can also change the diff view settings to have a side-by-side diff window instead of the inline diff.
Google Distributed Cloud (software only) for VMware 1.31.1100-gke.40 is available for download. To upgrade, see Upgrade a cluster. Distributed Cloud 1.31.1100-gke.40 runs on Kubernetes v1.31.12-gke.600.
If you are using a third-party storage vendor, check the GDC Ready storage partners document to make sure the storage vendor has already passed the qualification for this release.
After a release, it takes approximately 7 to 14 days for the version to become available for use with GKE On-Prem API clients: the Google Cloud console, the gcloud CLI, and Terraform.
The following issues were fixed in 1.33.200-gke.70:
Fixed an issue that
gkectl updateblocks updating a non-HA non-advanced cluster to HA advanced clusterFixed vulnerabilities listed in Vulnerability fixes.
The following issues were fixed in 1.31.1100-gke.40:
- Fixed vulnerabilities listed in Vulnerability fixes.
Google Distributed Cloud (software only) for VMware 1.33.200-gke.70 is available for download. To upgrade, see Upgrade a cluster. Distributed Cloud 1.33.200-gke.70 runs on Kubernetes v1.33.5-gke.600.
If you are using a third-party storage vendor, check the GDC Ready storage partners document to make sure the storage vendor has already passed the qualification for this release.
After a release, it takes approximately 7 to 14 days for the version to become available for use with GKE On-Prem API clients: the Google Cloud console, the gcloud CLI, and Terraform.
The following issues were fixed in 1.33.200-gke.70:
Fixed a timeout issue for the
kubeadmAPI server health check that runs during bootstrap cluster creation. The timeout issue blocked some cluster operations, such as restoring a cluster.This patch release doesn't include new fixes for specific, externally-cited vulnerabilities.
Google Distributed Cloud for bare metal 1.33.200-gke.70 is now available for download. To upgrade, see Upgrade clusters. Distributed Cloud for bare metal 1.33.200-gke.70 runs on Kubernetes v1.33.4-gke.900.
After a release, it takes approximately 7 to 14 days for the version to become available for installations or upgrades with the GKE On-Prem API clients: the Google Cloud console, the gcloud CLI, and Terraform.
If you use a third-party storage vendor, check the Ready storage partners document to make sure the storage vendor has already passed the qualification for this release of Distributed Cloud for bare metal.
For information about the latest known issues, see Google Distributed Cloud for bare metal known issues in the Troubleshooting section.
For information about the latest known issues, see Google Distributed Cloud for bare metal known issues in the Troubleshooting section.
Google Distributed Cloud for bare metal 1.31.1100-gke.40 is now available for download. To upgrade, see Upgrade clusters. Distributed Cloud for bare metal 1.31.1100-gke.40 runs on Kubernetes v1.31.12-gke.600.
After a release, it takes approximately 7 to 14 days for the version to become available for installations or upgrades with the GKE On-Prem API clients: the Google Cloud console, the gcloud CLI, and Terraform.
If you use a third-party storage vendor, check the Ready storage partners document to make sure the storage vendor has already passed the qualification for this release of Distributed Cloud for bare metal.
New parser documentation now available
New parser documentation is available to help you ingest and normalize logs from the following sources:
- Collect Absolute Secure Endpoint logs
- Collect AIDE (Advanced Intrusion Detection Environment) logs
- Collect Akamai Enterprise Application Access logs
- Collect Apache Hadoop logs
- Collect Armis Vulnerabilities logs
- Collect Array Networks SSL VPN logs
- Collect Aruba IPS logs
- Collect Atlassian Confluence logs
- Collect Cisco AMP for Endpoints logs
- Collect Cisco APIC logs
- Collect Cisco Application Centric Infrastructure (ACI) logs
- Collect Cisco CallManager logs
- Collect Cisco CloudLock CASB logs
- Collect Cisco DNA Center Platform logs
- Collect Cisco eStreamer logs
- Collect Cribl Stream logs
- Collect CrowdStrike FileVantage logs
- Collect CrowdStrike IDP Services logs
- Collect Cynet 360 AutoXDR logs
- Collect Digital Shadows SearchLight logs
- Collect Duo Telephony logs
- Collect Edgio WAF logs
- Collect Elastic Auditbeat logs
- Collect Elastic Packet Beats logs
- Collect Elasticsearch logs
- Collect Entrust nShield HSM audit logs
- Collect Imperva Advanced Bot Protection logs
- Collect Imperva Attack Analytics logs
- Collect Imperva Audit Trail logs
- Collect Imperva CEF logs
- Collect Imperva Data Risk Analytics (DRA) logs
- Collect Imperva Database logs
- Collect Imperva FlexProtect logs
- Collect Imperva SecureSphere Management logs
- Collect Kiteworks (formally Accellion) logs
- Collect Proofpoint Emerging Threats Pro IOC logs
- Collect ServiceNow audit logs
- Collect Team Cymru Scout Threat Intelligence data
- Collect URLScan IO logs
- Collect Uptycs EDR logs
- Collect VanDyke VShell SFTP logs
- Collect Zendesk CRM logs
- Collect ZeroFox Platform logs
Enhance threat visibility and detection with Emerging Threats
The new Emerging Threats page provides AI-powered threat intelligence to help you understand how current threat campaigns might affect your organization. Powered by Google Threat Intelligence (GTI) and Gemini models, this page offers a curated view of critical global threats relevant to your environment.
Emerging Threats continuously aligns intelligence from GTI with your organization's telemetry to highlight detection coverage and identify gaps. When it finds a gap, it uses Gemini to automatically draft new detection rules to accelerate your response.
For more details, see Emerging Threats overview, Emerging Threats feed,and Emerging Threats detailed view.
Use the Triage Agent to investigate alerts
You can now use Triage Agent, an AI-powered investigation assistant, to analyze alerts in Google SecOps. Triage Agent determines if an alert is a true or false positive, provides a summarized explanation for its conclusion, and suggests next steps for further investigation.
You can trigger investigations manually or have them run automatically on supported alert types. Each investigation produces a detailed report that includes the agent's disposition, a summary of its findings, and a timeline of the analysis.
For more details, see Use Triage Agent to investigate alerts.
New Azure Monitor integration
Siemplify: Version 95.0
The following new action has been added:
- Get Case Alerts
CrowdStrike Falcon: Version 69.0
Refactored the pagination and filtering mechanism in the following actions:
List Uploaded IOCs
List Hosts
Added support for wildcards to
File Paths to Scanin the following action:- On-Demand Scan
Cybereason: Version 21.0
- Integration: Added ability to provide a CA Certificate file as part of the configuration.
Google Chronicle: Version 67.0
Updated curated detections processing logic in the following action:
- Get Detection Details
The following integrations are now GUS recommended:
CrowdStrike Falcon: Version 69.0
Wiz: Version .0
Fortigate: Version 16.0
Updated the dependency files in the following integrations:
Microsoft Graph Mail: Version 33.0
Microsoft Graph Mail Delegated: Version 10.0
Updated action definitions to meet the new requirements of IDE in the following integrations:
Updated Integrations (45)
Google Security Command Center: Version 14.0
Added the ability to ingest Toxic Combinations and Chokepoints in the following connector:
- Google Security Command Center - Findings Connector
New Azure Monitor integration
Siemplify: Version 95.0
The following new action has been added:
- Get Case Alerts
CrowdStrike Falcon: Version 69.0
Refactored the pagination and filtering mechanism in the following actions:
List Uploaded IOCs
List Hosts
Added support for wildcards to
File Paths to Scanin the following action:- On-Demand Scan
Cybereason: Version 21.0
- Integration: Added ability to provide a CA Certificate file as part of the configuration.
Google Chronicle: Version 67.0
Updated curated detections processing logic in the following action:
- Get Detection Details
The following integrations are now GUS recommended:
CrowdStrike Falcon: Version 69.0
Wiz: Version .0
Fortigate: Version 16.0
Updated the dependency files in the following integrations:
Microsoft Graph Mail: Version 33.0
Microsoft Graph Mail Delegated: Version 10.0
Updated action definitions to meet the new requirements of IDE in the following integrations:
Updated Integrations (45)
Google Security Command Center: Version 14.0
Added the ability to ingest Toxic Combinations and Chokepoints in the following connector:
- Google Security Command Center - Findings Connector
New parser documentation now available
New parser documentation is available to help you ingest and normalize logs from the following sources:
- Collect Absolute Secure Endpoint logs
- Collect AIDE (Advanced Intrusion Detection Environment) logs
- Collect Akamai Enterprise Application Access logs
- Collect Apache Hadoop logs
- Collect Armis Vulnerabilities logs
- Collect Array Networks SSL VPN logs
- Collect Aruba IPS logs
- Collect Atlassian Confluence logs
- Collect Cisco AMP for Endpoints logs
- Collect Cisco APIC logs
- Collect Cisco Application Centric Infrastructure (ACI) logs
- Collect Cisco CallManager logs
- Collect Cisco CloudLock CASB logs
- Collect Cisco DNA Center Platform logs
- Collect Cisco eStreamer logs
- Collect Cribl Stream logs
- Collect CrowdStrike FileVantage logs
- Collect CrowdStrike IDP Services logs
- Collect Cynet 360 AutoXDR logs
- Collect Digital Shadows SearchLight logs
- Collect Duo Telephony logs
- Collect Edgio WAF logs
- Collect Elastic Auditbeat logs
- Collect Elastic Packet Beats logs
- Collect Elasticsearch logs
- Collect Entrust nShield HSM audit logs
- Collect Imperva Advanced Bot Protection logs
- Collect Imperva Attack Analytics logs
- Collect Imperva Audit Trail logs
- Collect Imperva CEF logs
- Collect Imperva Data Risk Analytics (DRA) logs
- Collect Imperva Database logs
- Collect Imperva FlexProtect logs
- Collect Imperva SecureSphere Management logs
- Collect Kiteworks (formally Accellion) logs
- Collect Proofpoint Emerging Threats Pro IOC logs
- Collect ServiceNow audit logs
- Collect Team Cymru Scout Threat Intelligence data
- Collect URLScan IO logs
- Collect Uptycs EDR logs
- Collect VanDyke VShell SFTP logs
- Collect Zendesk CRM logs
- Collect ZeroFox Platform logs
Enhance threat visibility and detection with Emerging Threats
The new Emerging Threats page provides AI-powered threat intelligence to help you understand how current threat campaigns might affect your organization. Powered by Google Threat Intelligence (GTI) and Gemini models, this page offers a curated view of critical global threats relevant to your environment.
Emerging Threats continuously aligns intelligence from GTI with your organization's telemetry to highlight detection coverage and identify gaps. When it finds a gap, it uses Gemini to automatically draft new detection rules to accelerate your response.
For more details, see Emerging Threats overview, Emerging Threats feed,and Emerging Threats detailed view.
Use the Triage Agent to investigate alerts
You can now use Triage Agent, an AI-powered investigation assistant, to analyze alerts in Google SecOps. Triage Agent determines if an alert is a true or false positive, provides a summarized explanation for its conclusion, and suggests next steps for further investigation.
You can trigger investigations manually or have them run automatically on supported alert types. Each investigation produces a detailed report that includes the agent's disposition, a summary of its findings, and a timeline of the analysis.
For more details, see Use Triage Agent to investigate alerts.
New parser documentation now available
New parser documentation is available to help you ingest and normalize logs from the following sources:
- Collect Absolute Secure Endpoint logs
- Collect AIDE (Advanced Intrusion Detection Environment) logs
- Collect Akamai Enterprise Application Access logs
- Collect Apache Hadoop logs
- Collect Armis Vulnerabilities logs
- Collect Array Networks SSL VPN logs
- Collect Aruba IPS logs
- Collect Atlassian Confluence logs
- Collect Cisco AMP for Endpoints logs
- Collect Cisco APIC logs
- Collect Cisco Application Centric Infrastructure (ACI) logs
- Collect Cisco CallManager logs
- Collect Cisco CloudLock CASB logs
- Collect Cisco DNA Center Platform logs
- Collect Cisco eStreamer logs
- Collect Cribl Stream logs
- Collect CrowdStrike FileVantage logs
- Collect CrowdStrike IDP Services logs
- Collect Cynet 360 AutoXDR logs
- Collect Digital Shadows SearchLight logs
- Collect Duo Telephony logs
- Collect Edgio WAF logs
- Collect Elastic Auditbeat logs
- Collect Elastic Packet Beats logs
- Collect Elasticsearch logs
- Collect Entrust nShield HSM audit logs
- Collect Imperva Advanced Bot Protection logs
- Collect Imperva Attack Analytics logs
- Collect Imperva Audit Trail logs
- Collect Imperva CEF logs
- Collect Imperva Data Risk Analytics (DRA) logs
- Collect Imperva Database logs
- Collect Imperva FlexProtect logs
- Collect Imperva SecureSphere Management logs
- Collect Kiteworks (formally Accellion) logs
- Collect Proofpoint Emerging Threats Pro IOC logs
- Collect ServiceNow audit logs
- Collect Team Cymru Scout Threat Intelligence data
- Collect URLScan IO logs
- Collect Uptycs EDR logs
- Collect VanDyke VShell SFTP logs
- Collect Zendesk CRM logs
- Collect ZeroFox Platform logs
Enhance threat visibility and detection with Emerging Threats
The new Emerging Threats page provides AI-powered threat intelligence to help you understand how current threat campaigns might affect your organization. Powered by Google Threat Intelligence (GTI) and Gemini models, this page offers a curated view of critical global threats relevant to your environment.
Emerging Threats continuously aligns intelligence from GTI with your organization's telemetry to highlight detection coverage and identify gaps. When it finds a gap, it uses Gemini to automatically draft new detection rules to accelerate your response.
For more details, see Emerging Threats overview, Emerging Threats feed,and Emerging Threats detailed view.
Use the Triage Agent to investigate alerts
You can now use Triage Agent, an AI-powered investigation assistant, to analyze alerts in Google SecOps. Triage Agent determines if an alert is a true or false positive, provides a summarized explanation for its conclusion, and suggests next steps for further investigation.
You can trigger investigations manually or have them run automatically on supported alert types. Each investigation produces a detailed report that includes the agent's disposition, a summary of its findings, and a timeline of the analysis.
For more details, see Use Triage Agent to investigate alerts.
New Azure Monitor integration
Siemplify: Version 95.0
The following new action has been added:
- Get Case Alerts
CrowdStrike Falcon: Version 69.0
Refactored the pagination and filtering mechanism in the following actions:
List Uploaded IOCs
List Hosts
Added support for wildcards to
File Paths to Scanin the following action:- On-Demand Scan
Cybereason: Version 21.0
- Integration: Added ability to provide a CA Certificate file as part of the configuration.
Google Chronicle: Version 67.0
Updated curated detections processing logic in the following action:
- Get Detection Details
The following integrations are now GUS recommended:
CrowdStrike Falcon: Version 69.0
Wiz: Version .0
Fortigate: Version 16.0
Updated the dependency files in the following integrations:
Microsoft Graph Mail: Version 33.0
Microsoft Graph Mail Delegated: Version 10.0
Updated action definitions to meet the new requirements of IDE in the following integrations:
Updated Integrations (45)
Google Security Command Center: Version 14.0
Added the ability to ingest Toxic Combinations and Chokepoints in the following connector:
- Google Security Command Center - Findings Connector
Conversational Analytics is now generally available for Looker instances that are on Looker 25.18 or later. Use of Conversational Analytics in your Looker instance is now available without a Looker admin having to enable the Trusted Testers settings. Enablement of the Gemini in Looker setting is still required. Enablement of the Trusted Tester Features setting is still required when using the Code Interpreter with Conversational Analytics in Looker.
For Looker (Google Cloud core) instances, this launch includes support for Conversational Analytics in instances that are within a VPC perimeter.
See the Looker pricing page for pricing information.
(This release note was updated on November 13, 2025 to add pricing information.)
November 11, 2025
AlloyDB for PostgreSQLYou can now use Dataplex Universal Catalog to discover, search, and manage your AlloyDB resources, including clusters, databases, and tables. This integration (in Preview) provides a unified view of your metadata, enabling better data governance and easier analysis. For more information, see Manage your AlloyDB resources using Dataplex Universal Catalog.
Improve query performance for partitioned tables and complex queries using
parallel execution for the SELECT portion of an INSERT INTO ... SELECT
query. For more information,
see Improve select insert performance with parallel select.
The BigQuery Overview page is now your hub for discovering tutorials, features, and resources to help you get the most out of BigQuery. It provides guided paths for users of all skill levels. This feature is in Preview.
You can now use the interactive SQL translator, the translation API, and the batch SQL translator to translate the following SQL dialects into GoogleSQL:
- Apache Impala SQL
- GoogleSQL (BigQuery)
Impala SQL translation can be used to migrate Cloudera and Apache Hadoop SQL workloads that use Impala as a query engine.
GoogleSQL (BigQuery) translation can be used to verify and iteratively customize your translated SQL queries after an initial translation from an external dialect. For example, you can apply systematic query rewrites using YAML configurations to customize and optimize your GoogleSQL queries before deploying it.
These features are in Preview.
You can now use custom constraints with an Organization Policy to provide more granular control over specific fields for BigQuery dataset resources. This feature is generally available (GA).
You can set a task timeout up to 168 hours (7 days) for Cloud Run jobs. (GA)
You can now enable Autoclass for buckets with hierarchical namespace enabled.
cos-dev-129-19370-0-0
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.57 | v27.5.1 | v2.1.4 | See List |
Updated app-admin/sosreport to v4.10.1. Enabled containerd stack dump by default.
Updated app-containers/containerd to v2.1.4.
Updated app-containers/runc to v1.3.2.
Updated the Linux kernel to v6.12.57.
Updated the Linux kernel to v6.12.56.
Enabled HTCP TCP congestion control algorithm as a module.
Added support for SCSI logging.
Made CX-8 NIC naming order deterministic.
Upgraded sys-apps/makedumpfile to v1.7.8.
Upgraded sys-auth/pambase to v20251104.
Updated app-containers/cri-tools to 1.32.0.
Updated net-misc/chrony to v4.8.
Upgraded app-emulation/cloud-init to v25.1.4.
Upgraded chromeos-base/google-breakpad to v2025.10.31.183851-r257.
Upgraded sys-process/audit to 4.0.2-r1.
Upgraded dev-libs/nss to 3.117 and dev-libs/nspr to 4.37.
Upgraded sys-libs/libcap to v2.77.
Upgraded net-libs/gnutls to v3.8.10 and dev-libs/nettle to 3.10.2.
Upgraded dev-python/coverage to v7.10.7.
Enabled multiport support for CX-8 devices.
Fixed a bug where setting MTU above 9000 on ARM systems with a 64k page size would cause IDPF networking to fail.
Fixed bcache latency spikes.
Fixed CVE-2025-31133, CVE-2025-52565, and CVE-2025-52881 in app-containers/runc.
Runtime sysctl changes:
- Changed: fs.file-max: 811384 -> 811473
cos-125-19216-104-17
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.55 | v27.5.1 | v2.1.4 | See List |
Updated app-containers/containerd to v2.1.4.
Added support for the Lustre 2.14.0_p224 drivers.
Enabled HTCP TCP congestion control algorithm as a module.
Added support for SCSI logging.
Upgraded sys-apps/makedumpfile to v1.7.8.
Made CX-8 NIC naming order deterministic.
Enabled multiport support for CX-8 devices.
Fixed a race condition where unmounting file systems monitored by inotify or fanotify could result in kernel crash.
Fixed CVE-2025-21833 in the Linux kernel.
Fixed CVE-2025-40083 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811455 -> 811489
- Changed: net.ipv4.udp_mem: 188034 250714 376068 -> 188034 250715 376068
cos-113-18244-521-16
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.1.155 | v24.0.9 | v1.7.27 | See List |
Upgraded sys-apps/makedumpfile to v1.7.8.
Fixed CVE-2025-40078 in the Linux kernel.
Fixed CVE-2025-40099 in the Linux kernel.
Fixed CVE-2025-40103 in the Linux kernel.
Fixed CVE-2025-40105 in the Linux kernel.
Fixed CVE-2025-40070 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 812016 -> 812054
cos-121-18867-294-17
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.113 | v27.5.1 | v2.0.6 | See List |
Upgraded sys-apps/makedumpfile to v1.7.8.
Upgraded sys-apps/pv to v1.9.44.
Fixed a race condition where unmounting file systems monitored by inotify or fanotify could result in kernel crash.
Fixed CVE-2025-40083 in the Linux kernel.
Fixed CVE-2025-40078 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811792 -> 811813
cos-117-18613-439-22
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.111 | v24.0.9 | v1.7.28 | See List |
Fixed a race condition where unmounting file systems monitored by inotify or fanotify could result in kernel crash.
Fixed CVE-2025-40083 in the Linux kernel.
Fixed CVE-2025-40042 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811733 -> 811751
Eventarc Advanced support for using access policies to control access when publishing event messages to an Eventarc Advanced bus is available in Preview.
Anthropic's Claude 3.7 Sonnet
Anthropic's Claude 3.7 Sonnet is deprecated as of November 11, 2025 and will be shut down on May 11, 2026. For more information, see Partner model deprecations.
The N4D machine family is now Generally Available (GA) for Standard and Autopilot mode. N4D instances are powered by the fifth generation AMD EPYC SP5 processors (Turin). The N4D machine series is available as follows:
- Cluster autoscaler, node pool auto-creation, and Autopilot mode: GKE version 1.34.1-gke.2037000 and later.
- Manually created node pools in Standard mode: all available GKE versions.
For more information, see N4D machine series.
You can now schedule a daily, zero-downtime export for Looker (Google Cloud core) instances. For more information, see the Create a scheduled export job for a Looker (Google Cloud core) instance documentation page. This feature is being rolled out and will appear in all instances within a few weeks.
The list of Organization Policy Service constraints that are enforced when an organization
resource is created has changed. The following Google Cloud security baseline
constraints are enforced for all organizations created on or after May 3, 2024:
* constraints/iam.managed.disableServiceAccountKeyCreation
* constraints/iam.managed.disableServiceAccountKeyUpload
* constraints/iam.automaticIamGrantsForDefaultServiceAccounts
* constraints/iam.allowedPolicyMemberDomains
* constraints/essentialcontacts.managed.allowedContactDomains
* constraints/compute.managed.restrictProtocolForwardingCreationForTypes
* constraints/storage.uniformBucketLevelAccess
For more information, see Google Cloud security baseline constraints.
Several features and updates have been made available to Security Command Center in a federated identity environment:
- Exporting findings to a CSV file.
- Exporting findings to Cloud Storage.
The following features aren't supported by identity federation but are being moved to other sections in the documentation:
- Sending feedback in Security Command Center
- Managing Google SecOps settings.
Service Usage support for hierarchical service activation is available in Preview. This feature lets you enable and disable services across your organization's resource hierarchy.
Spanner Studio now supports several new export options for your query results. You can export to a CSV or JSON file, Google Sheets, or copy the results to a clipboard. For more information, see Create, modify, and query your data.
November 10, 2025
AlloyDB for PostgreSQLAlloyDB AI introduces auto embedding generation in Preview. You can now generate large-scale embeddings to leverage in semantic search and Retrieval Augmented Generation (RAG) on text content.
AlloyDB now supports PostgreSQL 17 for migrating from Cloud SQL for PostgreSQL to AlloyDB for PostgreSQL using your Cloud SQL for PostgreSQL backup. The size limit for these operations is now 15TB. For more information, see Migrate from Cloud SQL for PostgreSQL to AlloyDB.
On November 10, 2025 we released an updated version of Apigee.
Support for new Apigee Analytics regions
This release introduces Apigee Analytics support for these new regions:
Hong Kong (asia-east2) and São Paulo (southamerica-east1).
NOTE: Apigee Advanced API Security does not support these new regions at this time.
For a list of all of the supported Analytics regions, see Available Apigee API Analytics regions.
On November 10, 2025 we released an updated version of Apigee.
Support for new Apigee Analytics regions
This release introduces Apigee Analytics support for these new regions:
Hong Kong (asia-east2) and São Paulo (southamerica-east1).
NOTE: Apigee Advanced API Security does not support these new regions at this time.
For a list of all of the supported Analytics regions, see Available Apigee API Analytics regions.
You can aggregate and deduplicate table data with Gemini assistance in your BigQuery data preparations. These features are generally available (GA).
BigQuery ML now offers the
AI.DETECT_ANOMALIES function.
Use the AI.DETECT_ANOMALIES function with a TimesFM model to
detect anomalies
in time series data, using historical data as a baseline.
This feature is in
Preview.
BigQuery ML now supports the TimesFM 2.5
time series foundational model.
You can use the TimesFM 2.5 model in the
AI.FORECAST,
AI.EVALUATE,
and
AI.DETECT_ANOMALIES
functions to achieve better forecasting accuracy and lower latency.
Partitioning is now available for BigLake tables for Apache Iceberg in BigQuery. This feature is in Preview.
Cloud SQL now provides brute-force detection and protection for your Cloud SQL instances. This helps protect your instances from brute-force access attempts by identifying the source and mitigating the risk caused by these attempts. For more information, see Use brute-force protection.
The default latest Python version is now 3.12. See Python versions.
The Windows guest agent identifies administrator accounts and groups using
string matching. Therefore, credential management features only function
correctly when you use English language names for user accounts and groups,
for example, Administrators. If you use non-English language names, credential
management features such as generating or resetting passwords might not function
as expected. For more information about managing Windows user accounts, see
Manage accounts and credentials on Windows VMs and
Known issues for Windows VM instances.
Generally available: Two new features that provide better observability for Compute Engine reservations and deeper insights into their capacity usage and costs:
- A new
consumedReservationfield in the VM instance details showing the full resource name of the consumed reservation, providing reservation consumption status on VMs and better visibility for resource management and troubleshooting. - Two new system labels in the BigQuery billing export for instances
consuming a reservation and the unused portion of a reservation, providing
more detailed cost analysis:
compute.googleapis.com/reservation_name: the short name of the Compute Engine reservation.compute.googleapis.com/reservation_project_id: the Project ID owning the Compute Engine reservation.
For more information, see the following:
Persistent memory for Gemini Code Assist on GitHub (Preview)
Gemini Code Assist on GitHub now supports persistent memory, which stores your previous interactions with Gemini Code Assist on GitHub so that it has context during your future interactions.
For users of the enterprise version, persistent memory is enabled from the connection settings within the Google Cloud console. For users of the consumer version, persistent memory is enabled from the Gemini Code Assist site. For more information, see manage configuration files across multiple repositories.
Persistent memory for Gemini Code Assist on GitHub (Preview)
Gemini Code Assist on GitHub now supports persistent memory, which stores your previous interactions with Gemini Code Assist on GitHub so that it has context during your future interactions.
For users of the enterprise version, persistent memory is enabled from the connection settings within the Google Cloud console. For users of the consumer version, persistent memory is enabled from the Gemini Code Assist site. For more information, see manage configuration files across multiple repositories.
Nested if
You can now use if statements in both the outcome and events sections and
also within the then else clauses of another if statement. This capability
lets you introduce more complicated logic to your query and is supported in
Rules, Search, and Dashboards.
For more information, see Use nested if statements for more complex logic.
Nested if
You can now use if statements in both the outcome and events sections and
also within the then else clauses of another if statement. This capability
lets you introduce more complicated logic to your query and is supported in
Rules, Search, and Dashboards.
For more information, see Use nested if statements for more complex logic.
Nested if
You can now use if statements in both the outcome and events sections and
also within the then else clauses of another if statement. This capability
lets you introduce more complicated logic to your query and is supported in
Rules, Search, and Dashboards.
For more information, see Use nested if statements for more complex logic.
The following insight types and subtypes are available in Network Analyzer:
- Recommender insight subtypes:
ROUTE_NEXT_HOP_FORWARDING_RULE_IP_MISMATCHROUTE_NEXT_HOP_FORWARDING_RULE_TYPE_INVALIDROUTE_NEXT_HOP_ILB_VIP_NOT_ASSIGNEDROUTE_NEXT_HOP_IP_NOT_ASSIGNEDROUTE_NEXT_HOP_VM_NON_PRIMARY_IPROUTE_NEXT_HOP_VM_WRONG_NETWORKROUTE_NEXT_HOP_VPN_TUNNEL_NOT_ESTABLISHEDNCC_DYNAMIC_ROUTE_FULLY_SHADOWED
- Cloud Logging insight types:
ROUTE_INVALID_NEXT_HOP_FORWARDING_RULE_IP_MISMATCHROUTE_INVALID_NEXT_HOP_FORWARDING_RULE_TYPE_INVALIDROUTE_INVALID_NEXT_HOP_ILB_VIP_NOT_ASSIGNEDROUTE_INVALID_NEXT_HOP_IP_NOT_ASSIGNEDROUTE_INVALID_NEXT_HOP_VM_NON_PRIMARY_IPROUTE_INVALID_NEXT_HOP_VM_WRONG_NETWORKROUTE_INVALID_NEXT_HOP_VPN_TUNNEL_NOT_ESTABLISHEDDYNAMIC_ROUTE_SHADOWED_FULLY_SHADOWED_BY_NCC_SUBNET_ROUTENCC_DYNAMIC_ROUTE_SHADOWED_FULLY_SHADOWED_BY_PEERING_SUBNET_ROUTENCC_DYNAMIC_ROUTE_SHADOWED_FULLY_SHADOWED_BY_STATIC_ROUTENCC_DYNAMIC_ROUTE_SHADOWED_FULLY_SHADOWED_BY_SUBNET_ROUTE
For more information, see Routes with an invalid next hop and Shadowed dynamic routes.
Network Analyzer no longer generates the following insight types and subtypes:
- Recommender insight subtypes:
ROUTE_NEXT_HOP_ILB_BACKEND_IP_FORWARDING_DISABLEDDYNAMIC_ROUTE_PARTIALLY_SHADOWEDPEERING_DYNAMIC_ROUTE_PARTIALLY_SHADOWED
- Cloud Logging insight types:
ROUTE_INVALID_NEXT_HOP_ILB_BACKEND_IP_FORWARDING_DISABLEDDYNAMIC_ROUTE_SHADOWED_PARTIALLY_SHADOWED_BY_SUBNET_ROUTEDYNAMIC_ROUTE_SHADOWED_PARTIALLY_SHADOWED_BY_PEERING_SUBNET_ROUTEDYNAMIC_ROUTE_SHADOWED_PARTIALLY_SHADOWED_BY_STATIC_ROUTEDYNAMIC_ROUTE_SHADOWED_PARTIALLY_SHADOWED_BY_PEERING_STATIC_ROUTE
For Autonomous Databases, you can perform a failover in the event of a disaster in which your primary database becomes inaccessible. This feature is Generally Available (GA).
Data Security Posture Management (DSPM) has been released to General Availability for the Security Command Center Enterprise tier.
Model Armor is available in the following regions:
europe-west1(Belgium)europe-west2(London)europe-west3(Frankfurt)asia-south1(Mumbai)
For more information, see Locations for the Model Armor API.
Spanner now automatically provides recommendations to apply schema design best practices to your databases. You can view these schema issue recommendations on the Spanner Studio page for your database. For more information, see View schema design best practice recommendations. This feature is in Preview.
Chirp 3: HD voices now support speech synthesis in the following languages: bg-BG, cs-CZ, et-EE, el-GR, he-IL, hr-HR, hu-HU, lt-LT, lv-LV, ro-RO, sk-SK, sl-SI, and sr-RS. For more information, see Chirp 3: Language Availability.
Service producers can accept or reject connections from individual Private Service Connect endpoints. This feature is available in Preview.
November 09, 2025
Google SecOps SIEMRelease 6.3.67 is being rolled out to the first phase of regions as listed here.
This release contains internal and customer bug fixes.
Release 6.3.67 is being rolled out to the first phase of regions as listed here.
This release contains internal and customer bug fixes.
November 08, 2025
Google SecOps SIEMRelease 6.3.66 is now available for all regions.
Release 6.3.66 is now available for all regions.
November 07, 2025
Backup and DRAnnouncing the public preview launch of Database Center support for resources protected with Backup and DR Service. Database Center is an AI-assisted dashboard that highlights fleet-wide data points.The integration is designed to provide Database Center users with a single, unified, and accurate view of the data protection posture for all databases protected by Backup and DR Service.This capability is available today, at no additional cost, for all Cloud SQL customers who have protected their databases through Backup and DR Service enhanced protection.
Generally available: N4D VMs are powered by the fifth generation AMD EPYC Turin processor and Titanium I/O offload processing. N4D machine types have up to 96 vCPUs and up to 768 GB of DDR5 memory, and a max-boost frequency of 4.1 GHz. They are offered in predefined and custom machine types and are available in select regions and zones.
N4D VM instances support standard networking with up to 50 Gbps of networking bandwidth and Hyperdisk storage. For more information, see General-purpose machine types.
Serverless for Apache Spark: Apache Spark upgrade to version 3.5.3 for the 1.2 and 2.2 Serverless for Apache Spark runtime versions announced on October 13, 2025 has been rolled back.
Gemini layout parser is in
Preview.
The Gemini layout parser gives better layout quality on table recognition,
reading order and text recognition on PDF files. You can enable the feature by
default by selecting layout parser processor version
pretrained-layout-parser-v1.4-2024-08-25, pretrained-layout-parser-v1.5-2025-08-25
or pretrained-layout-parser-v1.5-pro-2025-08-25 for your processor.
Bug fixes in VS Code
Various bug fixes and minor product enhancements.
Vertex AI Agent Engine
The following features are now available in Preview:
Configure, manage, and view observability features such as sessions, traces, logs, and events for your agent in the Google Cloud console.
Use the playground to test and interact with your agent in the Google Cloud console.
Evaluate your agents using the Gen AI evaluation service's GenAI Client in Vertex AI SDK.
Create and manage memory revisions for Memory Bank.
Use Identity Access Management (IAM) to create an agent identity to manage access and authentication when using agents on Vertex AI Agent Engine Runtime.
The following features are now available in GA:
Express mode support for Vertex AI Agent Engine Runtime.
Use the new free tier with Vertex AI Agent Engine Runtime. For more information, see Pricing.
In version 1.34.1-gke.1829001 and later, GKE can auto-create multiple node pools concurrently to improve the speed with which multiple new node pools become ready.
In GKE version 1.34.1-gke.2037001 and later, the GKE logging agent in your clusters can process logs up to two times faster per node than in version 1.33 and earlier. The logging agent also uses less node resources, which improves efficiency especially if you use high-throughput logging. These improvements to the logging agent are automatically enabled in version 1.34.1-gke.2037001 and later.
In GKE version 1.35 and later, GKE rejects
anonymous requests to cluster endpoints (except for the livez, /healthz, and
/readyz health check endpoints) by default for all new Autopilot or
Standard clusters. Existing clusters aren't affected by this change. To
allow anonymous requests to cluster endpoints, explicitly specify a value of
ENABLED in the --anonymous-authentication-config flag or the
AnonymousAuthenticationConfig.mode API field. For more information, see
Restrict anonymous access to cluster endpoints.
(2025-R46) Version updates
GKE cluster versions have been updated.
New versions available for upgrades and new clusters.
The following versions are now available for new GKE clusters, and for manual control plane upgrades and node upgrades for existing clusters. For more information about versioning and upgrades, see GKE versioning and support and About GKE cluster upgrades.
Rapid channel
- Version 1.34.1-gke.2037001 is now the default version for cluster creation in the Rapid channel.
- The following versions are now available in the Rapid channel:
- The following versions are no longer available in the Rapid channel:
- 1.31.13-gke.1123000
- 1.32.9-gke.1207000
- 1.33.5-gke.1308000
- 1.34.1-gke.2037000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1139000
- 1.31 to 1.32.9-gke.1239000
- 1.32 to 1.33.5-gke.1350000
- 1.33 to 1.34.1-gke.2037001
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1139000
- 1.32 to 1.32.9-gke.1239000
- 1.33 to 1.33.5-gke.1350000
- 1.34 to 1.34.1-gke.2037001
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Regular channel
- Version 1.33.5-gke.1201000 is now the default version for cluster creation in the Regular channel.
- The following versions are now available in the Regular channel:
- The following versions are no longer available in the Regular channel:
- 1.31.13-gke.1023000
- 1.32.9-gke.1108000
- 1.33.5-gke.1162000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1040000
- 1.31 to 1.32.9-gke.1130000
- 1.32 to 1.33.5-gke.1201000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1040000
- 1.32 to 1.32.9-gke.1130000
- 1.33 to 1.33.5-gke.1201000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Stable channel
- Version 1.33.5-gke.1125000 is now the default version for cluster creation in the Stable channel.
- The following versions are now available in the Stable channel:
- The following versions are no longer available in the Stable channel:
- 1.31.12-gke.1265000
- 1.32.9-gke.1072000
- 1.33.5-gke.1080000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1008000
- 1.31 to 1.32.9-gke.1092000
- 1.32 to 1.33.5-gke.1125000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1008000
- 1.32 to 1.32.9-gke.1092000
- 1.33 to 1.33.5-gke.1125000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Extended channel
- Version 1.33.5-gke.1201000 is now the default version for cluster creation in the Extended channel.
- The following versions are now available in the Extended channel:
- The following versions are no longer available in the Extended channel:
- 1.28.15-gke.2751000
- 1.28.15-gke.2857000
- 1.29.15-gke.1989000
- 1.29.15-gke.2109000
- 1.30.14-gke.1336000
- 1.30.14-gke.1426000
- 1.31.13-gke.1023000
- 1.32.9-gke.1108000
- 1.33.5-gke.1162000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.27 to 1.28.15-gke.2767000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.28 to 1.28.15-gke.2767000
- 1.29 to 1.29.15-gke.2002000
- 1.30 to 1.30.14-gke.1349000
- 1.31 to 1.31.13-gke.1040000
- 1.32 to 1.32.9-gke.1130000
- 1.33 to 1.33.5-gke.1201000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
No channel
- Version 1.33.5-gke.1201000 is now the default version for cluster creation.
- The following versions are now available:
- The following node versions are now available:
- The following versions are no longer available:
- 1.31.12-gke.1265000
- 1.32.9-gke.1072000
- 1.33.4-gke.1350000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1040000
- 1.31 to 1.32.9-gke.1130000
- 1.32 to 1.33.5-gke.1125000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1040000
- 1.32 to 1.32.9-gke.1130000
- 1.33 to 1.33.5-gke.1125000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R46) Security updates
This release includes new GKE versions that use updated Container-Optimized OS images. These updated images are cumulative, incorporating security fixes from all Container-Optimized OS versions released since the previous GKE release.
To identify the specific vulnerabilities that were resolved in each updated Container-Optimized OS image, see the Security release notes for that image. The following table includes links to the release notes for each updated Container-Optimized OS image:
| GKE version | Container-Optimized OS version | Details |
|---|---|---|
| 1.28.15-gke.2966000 | cos-113-18244-521-7 | cos-113-18244-521-7 release notes |
| 1.29.15-gke.2236000 | cos-113-18244-448-79 | cos-113-18244-448-79 release notes |
| 1.30.14-gke.1525000 | cos-113-18244-521-7 | cos-113-18244-521-7 release notes |
| 1.31.13-gke.1231000 | cos-117-18613-439-9 | cos-117-18613-439-9 release notes |
| 1.32.9-gke.1330000 | cos-117-18613-439-9 | cos-117-18613-439-9 release notes |
| 1.33.5-gke.1521000 | cos-121-18867-294-2 | cos-121-18867-294-2 release notes |
| 1.34.1-gke.2037001 | cos-125-19216-0-94 | cos-125-19216-0-94 release notes |
| 1.34.1-gke.2541000 | cos-125-19216-0-115 | cos-125-19216-0-115 release notes |
(2025-R46) Version updates
- Version 1.33.5-gke.1201000 is now the default version for cluster creation in the Extended channel.
- The following versions are now available in the Extended channel:
- The following versions are no longer available in the Extended channel:
- 1.28.15-gke.2751000
- 1.28.15-gke.2857000
- 1.29.15-gke.1989000
- 1.29.15-gke.2109000
- 1.30.14-gke.1336000
- 1.30.14-gke.1426000
- 1.31.13-gke.1023000
- 1.32.9-gke.1108000
- 1.33.5-gke.1162000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.27 to 1.28.15-gke.2767000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.28 to 1.28.15-gke.2767000
- 1.29 to 1.29.15-gke.2002000
- 1.30 to 1.30.14-gke.1349000
- 1.31 to 1.31.13-gke.1040000
- 1.32 to 1.32.9-gke.1130000
- 1.33 to 1.33.5-gke.1201000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R46) Version updates
- Version 1.33.5-gke.1201000 is now the default version for cluster creation.
- The following versions are now available:
- The following node versions are now available:
- The following versions are no longer available:
- 1.31.12-gke.1265000
- 1.32.9-gke.1072000
- 1.33.4-gke.1350000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1040000
- 1.31 to 1.32.9-gke.1130000
- 1.32 to 1.33.5-gke.1125000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1040000
- 1.32 to 1.32.9-gke.1130000
- 1.33 to 1.33.5-gke.1125000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R46) Version updates
- Version 1.34.1-gke.2037001 is now the default version for cluster creation in the Rapid channel.
- The following versions are now available in the Rapid channel:
- The following versions are no longer available in the Rapid channel:
- 1.31.13-gke.1123000
- 1.32.9-gke.1207000
- 1.33.5-gke.1308000
- 1.34.1-gke.2037000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1139000
- 1.31 to 1.32.9-gke.1239000
- 1.32 to 1.33.5-gke.1350000
- 1.33 to 1.34.1-gke.2037001
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1139000
- 1.32 to 1.32.9-gke.1239000
- 1.33 to 1.33.5-gke.1350000
- 1.34 to 1.34.1-gke.2037001
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R46) Version updates
- Version 1.33.5-gke.1201000 is now the default version for cluster creation in the Regular channel.
- The following versions are now available in the Regular channel:
- The following versions are no longer available in the Regular channel:
- 1.31.13-gke.1023000
- 1.32.9-gke.1108000
- 1.33.5-gke.1162000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1040000
- 1.31 to 1.32.9-gke.1130000
- 1.32 to 1.33.5-gke.1201000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1040000
- 1.32 to 1.32.9-gke.1130000
- 1.33 to 1.33.5-gke.1201000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R46) Version updates
- Version 1.33.5-gke.1125000 is now the default version for cluster creation in the Stable channel.
- The following versions are now available in the Stable channel:
- The following versions are no longer available in the Stable channel:
- 1.31.12-gke.1265000
- 1.32.9-gke.1072000
- 1.33.5-gke.1080000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1008000
- 1.31 to 1.32.9-gke.1092000
- 1.32 to 1.33.5-gke.1125000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1008000
- 1.32 to 1.32.9-gke.1092000
- 1.33 to 1.33.5-gke.1125000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
MITRE ATT&CK coverage dashboard is now available
The new MITRE ATT&CK coverage dashboard lets you measure your security posture against the MITRE ATT&CK framework, helping you:
- Assess threat coverage
- Identify gaps
- Prioritize security efforts
MITRE ATT&CK coverage dashboard is now available
The new MITRE ATT&CK coverage dashboard lets you measure your security posture against the MITRE ATT&CK framework, helping you:
- Assess threat coverage
- Identify gaps
- Prioritize security efforts
MITRE ATT&CK coverage dashboard is now available
The new MITRE ATT&CK coverage dashboard lets you measure your security posture against the MITRE ATT&CK framework, helping you:
- Assess threat coverage
- Identify gaps
- Prioritize security efforts
You can use customer-managed encryption keys (CMEK) organization policies with Security Command Center. For more information see Use CMEK organization policies with Security Command Center.
The monitoring and auditing capabilities for Compliance Manager have been released to General Availability.
The following infoType detectors are available in global and the europe and
us multi-regions:
DOCUMENT_TYPE/CONTEXT/FINANCEDOCUMENT_TYPE/CONTEXT/HEALTHDOCUMENT_TYPE/CONTEXT/LEGALDOCUMENT_TYPE/CONTEXT/OBSCENEDOCUMENT_TYPE/CONTEXT/OFFENSIVEDOCUMENT_TYPE/CONTEXT/POLITICSDOCUMENT_TYPE/CONTEXT/RELIGIONDOCUMENT_TYPE/CONTEXT/SEXUAL
For more information about all infoTypes, see InfoType detector reference.
Gemini TTS now supports synthesis for streaming requests. For more information, see the Gemini TTS page.
Gemini TTS now supports relaxing safety filters for accounts with monthly invoiced billing. For more information, see the Gemini TTS page.
Vertex AI Agent Engine
The following features are now available in Preview:
Configure, manage, and view observability features such as sessions, traces, logs, and events for your agent in the Google Cloud console.
Use the playground to test and interact with your agent in the Google Cloud console.
Evaluate your agents using the Gen AI evaluation service's GenAI Client in Vertex AI SDK.
Create and manage memory revisions for Memory Bank.
Use Identity Access Management (IAM) to create an agent identity to manage access and authentication when using agents on Vertex AI Agent Engine Runtime.
The following features are now available in GA:
Express mode support for Vertex AI Agent Engine Runtime.
Use the new free tier with Vertex AI Agent Engine Runtime. For more information, see Pricing.
November 06, 2025
Anthos Attached ClustersYou can now launch clusters with the following Kubernetes versions. Click on the following links to see the release notes associated with these patches:
You can now launch clusters with the following Kubernetes versions. Click on the following links to see the release notes associated with these patches:
You can now launch clusters with the following Kubernetes versions. Click on the following links to see the release notes associated with these patches:
The research paper ARIMA_PLUS: Large-scale, Accurate, Automatic and
Interpretable In-Database Time Series Forecasting and Anomaly Detection in
Google BigQuery is now publicly available.
This paper describes the algorithms behind the
ARIMA_PLUS
and
ARIMA_PLUS_XREG
models for time series forecasting and anomaly detection, and demonstrates the
high performance, scalability, explainability, and customizability of the
models.
Use dual-stack subnets with IPv6 to let your Cloud Run resources send IPv4 and internal IPv6 traffic to a VPC network with Direct VPC egress, and send external IPv6 traffic to the public internet. (GA)
You can now collect, view, and analyze prompts and responses from your agentic applications when they are built with the Agent Development Kit (ADK). This feature is in Public Preview.
Collect and view multimodal prompts and responses describes how to do the following:
- Configure your project and ADK to collect multimodal data.
- View a conversation and the multimodal data by using the Trace Explorer.
- Find log entries that contain references to multimodal data.
- Query your prompts and responses by using BigQuery.
- Evaluate your prompts and responses by using the Vertex AI SDK for Python.
Preview: N4A VMs are powered by Google's next-generation Axion processor, which is built on the Arm Neoverse N3 platform. N4A includes machine types with up to 64 vCPUs and 512 GB of DDR5 memory. N4A is available as standard, high-mem, high-cpu, and custom machine types with extended memory and up to 50 Gbps of standard networking. These machine types are available in limited regions and zones. For more information, see N4A machine series.
To access these VMs, complete this access request form, or speak to your account team.
Conversational Agents (Dialogflow CX):You can now specify custom voice in the Conversation profiles menu in the console.
You can now offer Terraform Kubernetes apps through Google Cloud Marketplace with usage-based pricing, in which customers pay for your app based on measurements that you choose, called metrics, such as the number of containers or storage time. For more information, see Pricing models for Terraform Kubernetes apps.
You can now offer Terraform Kubernetes apps through Google Cloud Marketplace with usage-based pricing, in which customers pay for your app based on measurements that you choose, called metrics, such as the number of containers or storage time. For more information, see Pricing models for Terraform Kubernetes apps.
Pro feature: Cloud Audit Logs
Looker Studio Pro logs are now available in the Logs Explorer within the Google Cloud console.
Looker connector enhancements
The Looker connector now supports query results of up to 75,000 rows. The Looker connector also supports exports of up to 75,000 rows of data.
More data from Google Ads
You can visualize the following metrics using the Google Ads connector:
- Conversions (Platform comparable)
- Conv. value (Platform comparable)
- Conv. value / cost (Platform comparable)
- Cost / conv. (Platform comparable)
Conditional formatting for bars in bar charts
You can now use conditional formatting on bar charts that use modern charts.
Partner connection launch update
The following partner connectors have been added to the Looker Studio Connector Gallery:
- Google Ads with AI By Picometrics. Sources: Google Adwords
- DataTrue v2 By DataTrue. Sources: DataTrue
- Lazada Ads By Supermetrics. Sources: Lazada
- OmniWallet By Dataslayer. Sources: OmniWallet
- TikTok Shop By Catchr. Sources: Tiktok
- Local Viking By Local Viking. Sources: Local Viking
- Sprout Social By Windsor.ai. Sources: SproutSocial
- TikTok Shop By Windsor.ai. Sources: Tiktok Shop
- Hurma By Hurma. Sources: Custom JSON
- Google Sheets By Supermetrics. Sources: Google Drive
Google Cloud NetApp Volumes supports the block storage feature with iSCSI protocol in allow-listed General Availability (GA) for the Flex service level of the Unified type. For more information, see Block storage.
Guidance for RISE with SAP on Google Cloud
Guidance is available to help you plan for running SAP solutions on Google Cloud that are managed by SAP under the RISE with SAP program. This guidance includes the following topics:
- An overview about the architecture and involved components.
- Establishing network connectivity to RISE with SAP on Google Cloud from on-premises systems and Google Cloud projects.
- Building extensions for RISE with SAP on Google Cloud by using the ABAP SDK for Google Cloud.
For more information, see Overview of RISE with SAP on Google Cloud.
Use of Oracle Automatic Storage Management with Oracle Database
To run Oracle Database with SAP NetWeaver based applications on Google Cloud, SAP and Oracle have validated the use of Oracle Automatic Storage Management (ASM).
For more information, see the following:
Security Command Center Risk Engine supports Cloud Run attack paths for the following high-value resources:
run.googleapis.com/Jobrun.googleapis.com/Service
November 05, 2025
BigQueryYou can now generate data insights when you
create a
DataScan
using the Dataplex API. This feature is
generally available
(GA).
You can now generate table and column descriptions in all supported Gemini languages when you generate data insights. This feature is generally available (GA).
The BigQuery Data Transfer Service for Google Ads now supports Google Ads API v21.
You can use the
MATCH_RECOGNIZE clause
in your SQL queries to filter and aggregate matches across rows in a table.
This feature is
generally available
(GA).
New Airflow builds are available in Cloud Composer 3:
Fixed the CVE-2025-49844 vulnerability. The updated version of the environment component that hosts a Redis-based task queue is available:
- To apply the fix in Cloud Composer 3, upgrade the Airflow build of your environment to airflow-2.10.5-build.19 or airflow-2.9.3-build.39, or later.
- To apply the fix in Cloud Composer 2, upgrade your environment to Cloud Composer version 2.15.3, or later.
New images are available in Cloud Composer 2:
Resolved an issue in the Kubernetes Pod Operator (KPO) where the Kubernetes client experienced unreliable connections, leading to occasional failures. The fix enhances connection stability through the addition of retry logic for underlying connectivity problems.
We strongly recommend to use highly resilient environments for production use cases. Highly resilient environments provide high availability and use built-in redundancy and failover mechanisms to reduce the environment's susceptibility to zonal failures and single point of failure outages.
Database Migration Service for homogeneous MySQL migrations to Cloud SQL for MySQL now supports MySQL version 8.0.43. For more information, see Supported source and destination databases.
The rollout of the following extension versions, plugin versions, and extension support is underway:
Extensions and plugins
plpgsql_checkis upgraded from 2.8.1 to 2.8.3 for PostgreSQL versions 14 and later.pg_wait_samplingis upgraded from 1.1.6 to 1.1.9 for PostgreSQL versions 13 and later.tds_fdwis upgraded from 2.0.4 to 2.0.5.
The following extensions are available for PostgreSQL 18:
anonpg_hint_planpg_wait_samplingplpgsql_checktds_fdw
To use these versions of the extensions and plugins, update your instance to
[PostgreSQL version].R20251004.01_14.
If you use a maintenance window, then the updates to the minor, extension, and plugin versions happen according to the timeframe that you set in the window. Otherwise, the updates occur within the next few weeks.
For more information on checking your maintenance version, see Self-service maintenance. To find your maintenance window or to manage maintenance updates, see Find and set maintenance windows.
cos-117-18613-439-16
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.111 | v24.0.9 | v1.7.28 | See List |
Fixed bcache latency spikes.
Fixed CVE-2025-31133, CVE-2025-52565, and CVE-2025-52881 in app-containers/runc. There are known reliability issues in these fixes that will be addressed in subsequent releases.
Fixed CVE-2025-40103 in the Linux kernel.
Fixed CVE-2025-40105 in the Linux kernel.
Fixed CVE-2025-40099 in the Linux kernel.
Fixed CVE-2025-40052 in the Linux kernel.
Fixed CVE-2025-40040 in the Linux kernel.
Fixed CVE-2025-40035 in the Linux kernel.
Fixed CVE-2025-40044 in the Linux kernel.
Fixed CVE-2025-40049 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811728 -> 811733
cos-113-18244-521-11
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.1.155 | v24.0.9 | v1.7.27 | See List |
Fixed CVE-2025-31133, CVE-2025-52565, and CVE-2025-52881 in app-containers/runc. There are known reliability issues in these fixes that will be addressed in subsequent releases.
Fixed CVE-2025-40042 in the Linux kernel.
Fixed CVE-2025-40049 in the Linux kernel.
Fixed CVE-2025-40044 in the Linux kernel.
Fixed CVE-2025-40027 in the Linux kernel.
Fixed CVE-2025-40035 in the Linux kernel.
Fixed CVE-2025-40026 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 812007 -> 812016
cos-121-18867-294-12
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.113 | v27.5.1 | v2.0.6 | See List |
Fixed bcache latency spikes.
Fixed CVE-2025-31133, CVE-2025-52565, and CVE-2025-52881 in app-containers/runc. There are known reliability issues in these fixes that will be addressed in subsequent releases.
Fixed CVE-2025-40103 in the Linux kernel.
Fixed CVE-2025-40105 in the Linux kernel.
Fixed CVE-2025-40099 in the Linux kernel.
Fixed CVE-2025-40040 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811785 -> 811792
cos-125-19216-104-5
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.55 | v27.5.1 | v2.1.3 | See List |
Fixed bcache latency spikes.
Fixed CVE-2025-31133, CVE-2025-52565, and CVE-2025-52881 in app-containers/runc. There are known reliability issues in these fixes that will be addressed in subsequent releases.
Runtime sysctl changes:
- Changed: fs.file-max: 811499 -> 811455
Gemini Enterprise: Layout parser support for DOCX, PPTX, and XLSX (GA)
With the layout parser, support for parsing DOCX, PPTX, and XLSX file formats is Generally Available (GA). Both the layout and digital parsers can parse PDF, HTML, DOCX, PPTX, and XLSX files. For more information about the parsers, see Parse and chunk documents.
SentinelOneV2: Version 43.0
The following new action has been added:
- Get Site Agents
FortiAnalyzer: Version 8.0
Updated search processing logic in the following action:
- Search Logs
Freshworks Freshservice: Version 15.0
Added the ability to provide a department in the integration configuration for the following action:
- Create Ticket
Microsoft Teams: Version 31.0
- Integration: Updated the integration's action definitions to meet the new requirements of the IDE.
Palo Alto XDR: Version 20.0
The following new action has been added:
- Scan Endpoint
AWS Identity and Access Management: Version 7.0
Refactored the following actions:
Create User
Create Group
Create Policy
List Users
List Groups
List Policies
SentinelOneV2: Version 43.0
The following new action has been added:
- Get Site Agents
FortiAnalyzer: Version 8.0
Updated search processing logic in the following action:
- Search Logs
Freshworks Freshservice: Version 15.0
Added the ability to provide a department in the integration configuration for the following action:
- Create Ticket
Microsoft Teams: Version 31.0
- Integration: Updated the integration's action definitions to meet the new requirements of the IDE.
Palo Alto XDR: Version 20.0
The following new action has been added:
- Scan Endpoint
AWS Identity and Access Management: Version 7.0
Refactored the following actions:
Create User
Create Group
Create Policy
List Users
List Groups
List Policies
SentinelOneV2: Version 43.0
The following new action has been added:
- Get Site Agents
FortiAnalyzer: Version 8.0
Updated search processing logic in the following action:
- Search Logs
Freshworks Freshservice: Version 15.0
Added the ability to provide a department in the integration configuration for the following action:
- Create Ticket
Microsoft Teams: Version 31.0
- Integration: Updated the integration's action definitions to meet the new requirements of the IDE.
Palo Alto XDR: Version 20.0
The following new action has been added:
- Scan Endpoint
AWS Identity and Access Management: Version 7.0
Refactored the following actions:
Create User
Create Group
Create Policy
List Users
List Groups
List Policies
Looker 25.20 contains the following accessibility improvements:
- The character count for the custom message field of a schedule is now accessible to screen readers.
- The text for errors on custom filters is now accessible to screen readers.
- The list of visualization types in the Visualization section of an Explore is now accessible to screen readers.
- The reload button and corresponding "last refreshed" timestamp on a dashboard are now accessible to screen readers.
- The timezone selector on an Explore is now accessible to screen readers.
- The sort indicators in an Explore are now accessible to screen readers.
- The text formatting options in the Series tab of an Explore are now accessible to screen readers.
- Contrast is improved for elements that are selected when you set up dashboard filters.
- Contrast is improved for fields that are selected when Looker suggests a field name in the table calculations editor.
- Contrast is improved for tabs that are selected on the Schedule Delivery dialog.
- Contrast is improved for radio buttons that are selected on dialogs such as the download dialog.
- Dashboard filter options are no longer incorrectly classified as dialogs.
- The drill links in a single value visualization are now classified as buttons and can be accessed using the keyboard.
- The destination of an alert is now a required field.
Looker now recognizes results from the YEAR function as a number and not a date in MySQL 8.4. This change replicates the behavior of MySQL 8.0 and earlier.
To undo this change for a MySQL connection, add the following parameter to the Additional JDBC parameters section: yearIsDateType=true
The Max Number of PDT Builder Connections limit has been increased from 10 to 100.
When you use Elite System Activity, the System Activity fields sql_query.sql and sql_text.text are limited to a length of 1.9 MB. Any data beyond the 1.9 MB limit will be truncated. (This release note was updated on November 10, 2025 to specify Elite System Activity.)
Looker 25.20 is expected to include the following changes, features, and fixes:
- Expected Looker (original) deployment start: Thursday, November 6, 2025
- Expected Looker (original) final deployment and download available: Thursday, November 13, 2025
- Expected Looker (Google Cloud core) deployment start: Thursday, November 6, 2025
- Expected Looker (Google Cloud core) final deployment: Tuesday, November 18, 2025
An issue has been fixed where SQL Runner could return a NoMethodError when trying to query a LookML model that doesn't exist in the user's development mode. This feature now performs as expected.
An issue has been fixed where a measure of type: period_over_period could be referenced in the sql parameter for a measure of type: number. Attempting to do so now correctly displays an error in the LookML validator. This feature now performs as expected.
An issue has been fixed where the Clear field keep filter button on an Explore could incorrectly become disabled when a user used the field search bar in the field picker. This feature now performs as expected.
The Visual Drilling feature is now out of Labs and generally available on the Admin > General Settings page.
A new Labs feature, Internal Dashboard Theming, lets users apply predefined themes to a Looker dashboard. These themes, which are distinct from the themes that are used for embedded dashboards, can be managed by users with the manage_internal_themes permission.
An issue has been fixed where disabling the Favoriting LookML Dashboards Labs feature prevented users from moving LookML dashboards in folders. This feature now performs as expected.
The Visual Drilling feature is now generally available on the Admin > General Settings page.
You can use custom constraints with Organization Policy to provide more granular control over specific fields for some BigQuery resources. For more information, see Manage BigQuery resources using custom constraints. This feature is generally available (GA).
Cloud Load Balancing callouts have full duplex streaming support.
Vertex AI Search: Layout parser support for DOCX, PPTX, and XLSX (GA)
With the layout parser, support for parsing DOCX, PPTX, and XLSX file formats is Generally Available (GA). Both the layout and digital parsers can parse PDF, HTML, DOCX, PPTX, and XLSX files. For more information about the parsers, see Parse and chunk documents.
November 04, 2025
Apigee API hubFilter APIs by user-defined attributes
You can now filter APIs using your custom, user-defined attributes from the APIs page in the Google Cloud console.
For more information, see Filter resources based on attributes.
Artifact Registry support for managing Ruby gems with Artifact Registry repositories is in Preview. For more information, see the following topics:
You can now use custom organization policies with the BigQuery migration service to allow or deny specific operations during a BigQuery migration to meet your organization's compliance and security requirements. This includes an option to disable AI suggestions during a migration. This feature is in Preview.
GRPC_WITH_TLS health checks are used for health checking gRPC backends
with TLS enabled. For more information, see the following:
This feature is in General availability.
You can now view the topology for applications that you register with App Hub. The topology map provides a graphical view of the relationships between the services and workloads in your App Hub application. The topology map also displays alerts and traffic latency, which can help you understand how your application is performing and diagnose issues. This feature is in Public Preview.
To learn more, see the following:
Cloud SQL now supports the
automatic minor version upgrade
for Cloud SQL for MySQL 8.0.35 or later instances.
If your Cloud SQL for MySQL instance is running MySQL 8.0.35 or later, but
you didn't select a specific minor version when you created the instance (databaseVersion=MYSQL_8_0),
then your MySQL instance is upgraded automatically to the default minor version
of Cloud SQL for MySQL 8.0 during its regular scheduled maintenance update.
All eligible Cloud SQL for MySQL instances receive the first automatic
minor version upgrade during the rollout of MYSQL_8_0_[N].R20251004.01_07.
Generally available: You can verify which reservation a VM consumes and view a list of VMs that consume a reservation. For more information, see View reservation consumption.
Public preview: You can configure a regional managed instance group (MIG) to repair a VM in an alternate zone when the MIG can't repair the VM in its original zone. Repairing a VM in an alternate zone can improve your application's resiliency and resource obtainability. For more information, see Repair a VM in an alternate zone.
Layout parser support for DOCX, PPTX, XLSX, and XLSM file types in Document AI is in General Availability (GA). It makes content like paragraphs, tables, lists, and structural elements like headings, page headers, and footers easily accessible. It also creates context-aware chunks that facilitate information retrieval in a range of generative AI and discovery applications.
For more information, see Process documents with Layout Parser.
MiniMax M2 is available in Model Garden. This model is is built for end-to-end development workflows and has strong capabilities in planning and executing complex tool-calling tasks. The model is optimized to provide a balance of performance, cost, and inference speed. MiniMax M2 is available as a managed API in Model Garden. To learn more, see MiniMax M2.
VMware Engine ve2 nodes are now available in the London, England, Europe (europe-west2-b) zone in the London, England, Europe region (europe-west2).
You can use Policy Troubleshooter to troubleshoot policies that include bindings for service account principal sets. This feature is available in GA.
Google Cloud's Agent for SAP version 3.10
Version 3.10 of Google Cloud's Agent for SAP is generally available (GA). This version introduces enhancements for SAP workload evaluations, and disk snapshot based backup and recovery for SAP HANA.
For more information, see What's new with Google Cloud's Agent for SAP.
November 03, 2025
Apigee API hubAPI hub provisioning fails in data residency enabled Apigee organizations
Currently, API hub can't be provisioned within an Apigee organization that has data residency enabled. Attempts to provision API hub in a data residency-enabled Apigee organization will result in a timeout error.
Workaround: There is no workaround available at this time. If your existing Apigee organization has data residency enabled, you will not be able to provision API hub until this limitation is resolved in a future release.
You can use protocol buffer (protobuf) schemas to query individual fields within protobuf messages stored as bytes in Bigtable. First, create and manage your protobuf schemas. Then, query your protobuf data using GoogleSQL for Bigtable or BigQuery external tables. This feature is in Preview.
VersionedStorageSizeBytes was added to the output of
GetFhirStoreMetrics.
Cluster Toolkit version v1.71.0 is available. This release includes a
fix for a munge mount on login failure due to slow controller Slurm v6 setup, and
adds Managed Lustre support in the gke-a4x blueprint. For more information about
this release, see the Release announcement on
GitHub.
cos-125-19216-104-3
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.55 | v27.5.1 | v2.1.3 | See List |
This is an LTS refresh release.
Fixed a bug in cos-extensions which would cause GB200 and GB300 devices not to be detected in one code path, which would result in Imex channels not being created by default.
Upgraded dev-lang/go to v1.23.12.
Fixed a TCPX bug which would sometimes incorrectly report devices as being missing when route cache entries were missing or invalidated.
Fixed CVE-2025-40006 in the Linux kernel.
Fixed CVE-2025-40009 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811500 -> 811499
- Changed: net.ipv4.udp_mem: 188034 250715 376068 -> 188034 250714 376068
cos-117-18613-439-12
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.111 | v24.0.9 | v1.7.28 | See List |
Fixed CVE-2025-40070 in the Linux kernel.
Fixed CVE-2025-40038 in the Linux kernel.
Fixed CVE-2025-40078 in the Linux kernel.
Fixed CVE-2025-38073 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811785 -> 811728
cos-dev-129-19350-0-0
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.55 | v27.5.1 | v2.1.3 | See List |
Updated the Linux kernel to v6.12.55.
Fixed a bug in cos-extensions which would cause GB200 and GB300 devices not to be detected in one code path, which would result in Imex channels not being created by default.
Fixed a TCPX bug which would sometimes incorrectly report devices as being missing when route cache entries were missing or invalidated.
Runtime sysctl changes:
- Changed: fs.file-max: 811495 -> 811384
cos-121-18867-294-8
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.113 | v27.5.1 | v2.0.6 | See List |
Added support for NVIDIA driver v535.274.02 and v570.195.03.
Fixed CVE-2025-11413,11414 in binutils-libs.
Fixed CVE-2025-38073 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811835 -> 811785
cos-113-18244-521-8
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.1.155 | v24.0.9 | v1.7.27 | See List |
Runtime sysctl changes:
- Changed: fs.file-max: 812040 -> 812007
Google Cloud CCaaS 3.41
We've released version 3.41 of Google Cloud CCaaS.
The timing of the update to your instance depends on the deployment schedule that you have chosen. For more information, see Deployment schedules.
Nested disposition lists
You can now organize your disposition lists by grouping them into nested folders, making it easier for agents to find the disposition codes they need. This is available in the agent adapter and the agent desktop.
Administrators: The Disposition Codes dialog at Settings > Operation Management > Wrap-up > Manage Disposition Codes has a new Tree tab.
User experience change: If you've configured nested disposition lists, the Disposition screen in the agent adapter displays links to the nested disposition lists.
For more information, see Configure nested disposition lists.
Virtual agent to virtual agent direct chat transfers
You can configure Dialogflow payloads to transfer chat sessions from one virtual agent directly to another virtual agent, using the destination virtual agent's agent ID.
For more information, see Virtual agent to virtual agent direct transfer .
Extensions for support numbers
You can assign a phone number extension to an agent that an end-user can use to directly call the agent. You can also set up an extension directory that end-users can use to find the extension for an agent that they want to call.
Administrators:
The Agent Extensions pane on the Call page at Settings > Call contains a new Consumer to Agent Calls section.
The Add new menu dialog at Settings > Queue > IVR (Interactive Voice Response) > Menu Structure contains a new Extension Directory toggle.
For more information, see Turn on and configure agent extensions.
Skip language selection and IVR menu readout
You can configure your call flow to skip language selection and the IVR menu readout. Instead, callers get the default language and are routed to the default queue. This creates a faster call connection experience for end-users.
Administrators:
In the Settings > Languages & Messages > Languages pane, there's a new Skip language selection option.
In the Settings > Queue > IVR (Interactive Voice Response) > IVR Queue Menu Readout section, there's a new Skip IVR Menu readout option.
For more information, see Configure IVR messages.
Transfer an email session to a queue
Agents can now transfer an email session to a queue. This resolves the problem of multiple email sessions being created when an agent forwards an email directly to an agent to transfer it.
Administrators: The General pane on the Email page at Settings > Email contains a new Enable Email Transfer Between Queues checkbox.
User experience change: In the email adapter, a new Transfer button appears when an agent views an assigned email.
For more information, see Let agents transfer email sessions to a queue.
We addressed the following issues in this release:
- Fixed an issue where hyperlinks in the after-hours message of the web SDK were broken.
- Fixed an issue where the language selector mistakenly appeared in the chat UI.
- Fixed an issue where an authentication request with an invalid or expired authentication token caused an agent's browser to become unresponsive and crash.
- Fixed an issue where an end-user using the iOS mobile SDK couldn't play a video that they had sent to an agent during a web chat session.
- Fixed an issue for Android mobile SDK users where the Send icon in the end-user's chat input field didn't appear correctly.
- Fixed an issue where an instance using an Agent Assist profile with Conversation Summarization disabled incorrectly returned errors.
- Fixed an issue that caused inaccurate virtual agent chat analytics. Affected metrics included
response_count,response_time_total,response_time_avg, andresponse_time_max. - Fixed an issue for Microsoft Windows users where the scroll down button in the web chat pane wasn't working correctly.
- Fixed an issue that occurred after an administrator deactivated the chat channel or the email channel. Instead of sending a single notification email for this change, the system was sending multiple notification emails.
- Fixed a reporting discrepancy between the Agent Metrics (Historical) explore and the Chat Agent Metrics (Historical) explore in the advanced reporting dashboards.
- Fixed an issue in the Operation Management > Virtual Agent settings pane. After configuring the virtual agent to assign records to a specific user, subsequent changes to other settings couldn't be saved.
- Fixed an issue where the
sub_statusproperty was missing from the session metadata file. - Fixed an issue for HubSpot users where the inbound phone number in the call adapter displayed as null null.
- Fixed an issue for Kustomer users that caused calls to be disconnected and the agent to be moved to
Unavailablestatus. - Fixed an issue where the target response time timer in the chat adapter was resetting when the end-user sent a message instead of when the agent sent a message.
- Fixed an issue that occurred when agents used the chat adapter to send email addresses containing underscores. The email addresses resolved incorrectly in the end-user's chat pane, breaking the links.
- Fixed an issue that caused inaccurate chat analytics. Affected metrics included
response_time_total,response_time_avg, andchat_duration. - Fixed an issue where the queue-level overcapacity callback limit was ignored, and the global setting was enforced instead.
- Fixed an issue for Kustomer users where the ticket for an outbound call incorrectly showed the recipient's number in the From field and left the To field blank.
- Fixed an issue where the agent adapter froze when an agent making an outbound call changed the outbound call number using their favorites list.
- Fixed an issue that prevented a new chat from appearing in the agent desktop. This occurred when an agent had both the agent desktop and the standard chat adapter open in separate browser tabs.
- Fixed an issue that caused a significant delay in displaying contact detail information in the call adapter for campaign calls.
- Fixed an issue where users with read-only roles were able to change settings on the developer settings page.
Media CDN supports flexible shielding. You can specify a single geographic region for origin shielding. This way, cache fills route through this configured region, offering a more efficient configuration for centralized origins than the default user-location-based approach. This feature is Generally Available.
For more information, see flexible shielding.
A weekly digest of client library updates from across the Cloud SDK.
Compliance Manager supports the Security Command Center Premium tier at the organization level.
The OBJECT_TYPE/PERSON/PASSPORT and OBJECT_TYPE/PERSON/PHOTO_ID_CARD infoType detectors are available in global and the asia, europe, and us multi-regions. For more information about all infoTypes, see InfoType detector reference.
VPC Network Peering supports peering connections in consensus mode. This feature is available in General Availability. For more information, see Connection mode.
November 02, 2025
Apigee UIOn November 2, 2025, we released an updated version of the Apigee UI.
The Apigee Classic UI shutdown is complete. The shutdown was finalized on November 2, 2025, completing the migration of Apigee to the Google Cloud console. All Apigee functionality is now available in the Apigee UI in the Google Cloud console.
See the Apigee Classic UI shutdown page for more details.
If you need to synchronize time with high accuracy and monitor its accuracy for
your Compute Engine instances, you can sync your VM clock with its host
server clock using chrony and ptp_kvm. This configuration provides accuracy
within 1 ms for supported setups. For more information, see
Configure accurate time for Compute Engine VMs.
Release 6.3.66 is being rolled out to the first phase of regions as listed here.
This release contains internal and customer bug fixes.
Release 6.3.66 is being rolled out to the first phase of regions as listed here.
This release contains internal and customer bug fixes.
November 01, 2025
Google SecOps SIEMRelease 6.3.65 is now available for all regions.
Release 6.3.65 is now available for all regions.
October 31, 2025
Access ApprovalCloud Scheduler is generally available (GA).
Vertex AI model tuning is generally available (GA).
Cloud Scheduler is generally available (GA).
Vertex AI model tuning is generally available (GA).
The alloydb_scann extension version 0.1.3 is updated to include the following vector search improvements, which are now Generally Available (GA):
- The columnar engine now automatically includes vector columns in searches, so you don't need to add them to the table manually. For more information, see Perform a vector search.
- You can use the
pg_stat_ann_index_creationview for metrics about the number of rows at index creation. For more information, see Vector index metrics.
On October 31, 2025, we released an updated version of Apigee (1-16-0-apigee-4).
| Bug ID | Description |
|---|---|
| 452621774, 452381632, 441266643, 448498138 | Security fix for Apigee infrastructure. This addresses the following vulnerabilities:
|
| Bug ID | Description |
|---|---|
| 448647917 | Fixed a issue where non-SSL connections through a forward proxy could be improperly shared. |
| N/A | Updates to security, infrastructure, and libraries. |
Support for Java 25 runtime is in Preview.
Support for Java 25 runtime is in Preview.
To improve email security and ensure reliable, high-volume email delivery, migrate from the legacy Mail API to an SMTP-based email service, such as SendGrid, Mailgun, or Mailjet (Preview).
To improve email security and ensure reliable, high-volume email delivery, migrate from the legacy Mail API to an SMTP-based email service, such as SendGrid, Mailgun, or Mailjet (Preview).
Troubleshoot failed execution logs using AI
You can now use AI-powered troubleshooting with Google Gemini to analyze failed execution logs, identify root causes, and receive precise, actionable steps to resolve errors. To use this feature, you must enable AI capabilities in your Google Cloud region. For more information, see Troubleshoot failed execution logs using AI.
We have increased the row capacity for pivot tables backed by BigQuery in Connected Sheets from 100,000 to 200,000 rows.
The global and classic external Application Load Balancers implemented on Google Front-Ends (GFEs) now reject TLS connections when the client and the load balancer support ALPN (Application-Layer Protocol Negotiation), but don't share common ALPN protocols.
Previously, if a client proposed a list of application protocols during the TLS
handshake using the ALPN extension and none were supported by the load balancer,
ALPN would be deactivated and the connection would default to using HTTP/1 as
the default application protocol. After this update, the GFE instead returns
an SSL_TLSEXT_ERR_ALERT_FATAL response which causes the load balancer to
terminate the TLS handshake, and the connection to close. This change ensures
that an application-layer protocol is always explicitly negotiated between the
clients and the load balancers that support ALPN.
Support for Java 25 runtime is in Preview.
Support for Java 25 runtime is in Preview.
Version 20251030.02 includes fixes for the plugin-based architecture that is used by guest agent. For more information about the plugin-based architecture, see Guest agent.
- The Clock Skew module no longer causes time inconsistencies on VMs. The agent no longer attempts to synchronize the hardware clock (
hwclock) when the VM's Real-time Clock (RTC) isn't set to Coordinated Universal Time 0(UTC). For more information about how the guest agent handles clock synchronization, see Clock Synchronization. - The
vlan_setup_enabledoption now correctly sets up Dynamic Network Interfaces (NICs). Dynamic NICs now initialize reliably. - The agent now prevents a race condition in network interface and route setup. Previously, routes were temporarily flushed if they were added before a DHCP lease was acquired. The agent now ensures routes persist correctly, preventing a brief period of missing routes. These routes were previously auto-corrected after approximately one minute.
Custom splitter model
pretrained-splitter-v1.5-2025-07-14 with zero-shot splitting, classification
and confidence scores is available as Release Candidate
(Preview).
Gemini Enterprise: Hidden model thinking details
When generating an answer, the details of a model's thinking are always hidden to protect sensitive information.
Google Cloud CCaaS 3.40
We've released version 3.40 of Google Cloud CCaaS, including the web SDK.
The timing of the update to your instance depends on the deployment schedule that you have chosen. For more information, see Deployment schedules.
Web SDK: Support for hiding the Start a new conversation button
You can now configure the web SDK to hide the Start a new conversation button on the end-user's chat screen after the session ends. For more information, see Hide the button to download a transcript at the end of a session.
Search in email channel by email address and name
Agents can now search for email sessions by email address and name in the email adapter.
User experience change: The search pane in the email adapter includes two new fields: Email Address and Name.
For more information, see Search for emails.
The europe-west4 and europe-west6 regions are available for Agent Assist conversation profiles
The europe-west4 and europe-west6 regions are now available when you create an Agent Assist conversation profile for a Dialogflow CX virtual agent. For more information, see Create conversation profile for Dialogflow CX virtual agents.
Customize the color of the Start Screen Share button
You can now control the color of the Start Screen Share button to match the color palette of your brand. For more information, see Customize the Start Screen Share button.
New variables for custom lookup URLs
We've added the following five variables for custom lookup URLs:
- CUSTOMER_PHONE_NUMBER: the end-user's phone number
- SUPPORT_PHONE_NUMBER: your call center's phone number that an end-user calls in on
- OUTBOUND_NUMBER: the phone number an agent uses when making an outbound call
- SESSION_ID: the session ID
- CUSTOM_AGENT_ID: an optional agent ID
For more information, see Custom lookup URL configuration.
Web SDK: Support for hiding the download transcript option
You can now configure the web SDK to do the following on the end-user's chat screen:
Agent desktop maintains state after refresh
While you're using the agent desktop, if you refresh your browser, the agent desktop now maintains its state. This means that active conversations, finished tabs, and recently closed sessions remain as they were before the refresh.
The following issues were addressed in this release:
Fixed an issue that prevented administrators from configuring virtual agents on the top level for IVR queues.
Fixed an issue where attempting to configure automatic redirection settings for the top level of an IVR queue returned an error.
Fixed in issue that caused incorrect agent monitoring and reporting data when a virtual agent escalated a call to a queue in a different language.
Fixed issue for HubSpot users where the call adapter got stuck on a non-functional reconnect page after a session expired.
Fixed an issue for HubSpot users where the Delay call record creation until the call is connected to agent checkbox didn't appear in the CRM Record Creation Details pane.
Fixed an issue that prevented agents from ending direct SMS chat sessions.
Fixed an issue for Microsoft Windows 11 users that prevented agents from entering Japanese characters in the chat screen during chat sessions and into the notes during wrap-up.
Fixed an issue where SDK custom data that was passed using the web SDK didn't appear in the agent adapter.
Fixed an issue that prevented custom links entered in the chat adapter from being converted into clickable links.
Fixed an issue in the chat screen of the chat adapter where the Missed target response time message was partially obscured by the formatting toolbar.
Fixed an issue where agents couldn't initiate a callback to a missed agent-to-agent call from the History tab of the agent adapter.
Fixed an issue where predictive outbound calling campaigns stalled and incorrectly moved contacts to the Redialed list before retrying them. This prevented the campaigns from completing successfully.
Fixed an issue in the Call Details pane where the Recording Message Sequence settings were incorrectly inactive when the Play Call Recording Messages checkboxes were cleared.
Administrators: In the Call Details pane, we changed Recording Message Sequence to Recording Message Sequence for Outbound Calls for clarity.
Fixed an issue where the customized greeting for an automatic redirection rule didn't play for calls that entered the queue using a Direct Access Phone (DAP) number.
Fixed an issue that occurred when a call was made from the global contact list. On the Details tab of the call adapter, the destination name didn't display. Instead, the destination phone number displayed.
Fixed an agent desktop issue where an agent status that was configured with a role restriction mistakenly appeared in the status list for a user assigned to that restricted role.
Fixed an issue where searching for an inbound-only queue on the Phone Number Management page failed to return a result.
Fixed an issue that caused queue duration and wait duration to be reported as
0. This occurred when the Call Service Level Target on a queue settings page was set to a number that exceeded the maximum allowed limit.Fixed an issue where a team assigned to a preference profile added only 1 user to the profile's users count, instead of adding the total number of users on the team.
Fixed an issue where agents were timed out for inactivity while composing an email in the email adapter.
Fixed an issue where users with a custom role were unable to save changes in the Chat Settings pane, even when their role had View and Edit permissions.
Fixed an issue that occurred after an agent configured their own hours of operation settings in the agent adapter. Those settings didn't appear for administrators in the agent's user profile on the Settings > Users & Team > Manage Users & Teams page. This prevented the administrator from making other edits to the agent's profile without overwriting the agent's hours of operation settings.
Fixed an issue where CRM tickets weren't created for some calls.
Fixed an issue where outbound SIP calls incorrectly appended data parameters, causing calls to fail.
Fixed a Web SDK security vulnerability associated with DOMPurify.
Fixed an issue where chat metadata wasn't saved to external storage. This occurred when an end-user ended a chat after escalating from a virtual agent but before being connected to a human agent.
VMware Engine ve1 nodes are now available in the Mumbai, India (asia-south1-b) zone in the Mumbai region (asia-south1).
The Multi-Cluster Services (MCS) feature has been updated with a finalizer to more effectively prevent potential resource leaks and ensure a full cleanup during the feature's disablement process. As a result of this improvement, the disablement procedure has been updated. For more details on how to disable MCS, see Disabling MCS.
Custom log type rename
From now on, all custom log types will be renamed with the custom suffix to prevent confusion with prebuilt log types. The following custom log types already reflect the new naming convention:
- HUAWEI_SECMASTER_CUSTOM
- GTI_THREAT_FEED_CUSTOM
- GTI_IOC_STREAM_CUSTOM
- ABSOLUTE_SECURE_ENDPOINT_CUSTOM
- GTI_IOC_CUSTOM
- IBM_ILO_CUSTOM
- GCP_THREATINTEL_CUSTOM
- SAP_ETD_CUSTOM
Search usability enhancements
Google SecOps has introduced the following capabilities to improve usability, performance, and customization in search results:
Improved performance for large result sets: For broad queries, Google SecOps now provides paginated search results. You can select the number of rows to display per page. This pagination applies to the 10,000 results displayed in the table.
Optimized results view: The search editor now automatically collapses after a query runs, providing more space for results. You can also hide or show the Charts and Aggregations panels with the View Options list.
Customizable column views: You can now create, save, and share custom sets of columns in the Events table for consistent analysis across teams.
For more details, see Search for events and alerts.
Custom log type rename
From now on, all custom log types will be renamed with the custom suffix to prevent confusion with prebuilt log types. The following custom log types already reflect the new naming convention:
- HUAWEI_SECMASTER_CUSTOM
- GTI_THREAT_FEED_CUSTOM
- GTI_IOC_STREAM_CUSTOM
- ABSOLUTE_SECURE_ENDPOINT_CUSTOM
- GTI_IOC_CUSTOM
- IBM_ILO_CUSTOM
- GCP_THREATINTEL_CUSTOM
- SAP_ETD_CUSTOM
Search usability enhancements
Google SecOps has introduced the following capabilities to improve usability, performance, and customization in search results:
Improved performance for large result sets: For broad queries, Google SecOps now provides paginated search results. You can select the number of rows to display per page. This pagination applies to the 10,000 results displayed in the table.
Optimized results view: The search editor now automatically collapses after a query runs, providing more space for results. You can also hide or show the Charts and Aggregations panels with the View Options list.
Customizable column views: You can now create, save, and share custom sets of columns in the Events table for consistent analysis across teams.
All-time search: A new All Time option lets you run a search over the entire data retention period.
For more details, see Search for events and alerts.
Custom log type rename
From now on, all custom log types will be renamed with the custom suffix to prevent confusion with prebuilt log types. The following custom log types already reflect the new naming convention:
- HUAWEI_SECMASTER_CUSTOM
- GTI_THREAT_FEED_CUSTOM
- GTI_IOC_STREAM_CUSTOM
- ABSOLUTE_SECURE_ENDPOINT_CUSTOM
- GTI_IOC_CUSTOM
- IBM_ILO_CUSTOM
- GCP_THREATINTEL_CUSTOM
- SAP_ETD_CUSTOM
Search usability enhancements
Google SecOps has introduced the following capabilities to improve usability, performance, and customization in search results:
Improved performance for large result sets: For broad queries, Google SecOps now provides paginated search results. You can select the number of rows to display per page. This pagination applies to the 10,000 results displayed in the table.
Optimized results view: The search editor now automatically collapses after a query runs, providing more space for results. You can also hide or show the Charts and Aggregations panels with the View Options list.
Customizable column views: You can now create, save, and share custom sets of columns in the Events table for consistent analysis across teams.
For more details, see Search for events and alerts.
Version 20251030.02 includes fixes for the plugin-based architecture that is used by guest agent. For more information about the plugin-based architecture, see Guest agent.
- The Clock Skew module no longer causes time inconsistencies on VMs. The agent no longer attempts to synchronize the hardware clock (
hwclock) when the VM's Real-time Clock (RTC) isn't set to Coordinated Universal Time 0(UTC). For more information about how the guest agent handles clock synchronization, see Clock Synchronization. - The
vlan_setup_enabledoption now correctly sets up Dynamic Network Interfaces (NICs). Dynamic NICs now initialize reliably. - The agent now prevents a race condition in network interface and route setup. Previously, routes were temporarily flushed if they were added before a DHCP lease was acquired. The agent now ensures routes persist correctly, preventing a brief period of missing routes. These routes were previously auto-corrected after approximately one minute.
Looker (Google Cloud core) instances that use Private Service Connect now offer a simplified method for configuring outbound connections to external domains or the Looker Marketplace. For more information, see the Configure outbound connections documentation.
A monthly digest of client library updates from across the Cloud SDK.
Java
Changes for google-cloud-spanner
6.102.1 (2025-10-23)
Bug Fixes
- deps: Update the Java code generator (gapic-generator-java) to 2.63.0 (c1a8238)
- Do a quick check if the application runs on Google Cloud (#4163) (b9d7daf)
- Migrate away from GoogleCredentials.fromStream() usages (#4151) (94d0474)
Dependencies
- Update actions/checkout action to v5 (#4158) (b32ebcf)
- Update actions/checkout action to v5 (#4161) (02a17c6)
- Update dependency com.google.cloud:sdk-platform-java-config to v3.53.0 (#4178) (24fe194)
- Update dependency net.bytebuddy:byte-buddy to v1.17.8 (#4154) (c911381)
- Update dependency net.bytebuddy:byte-buddy-agent to v1.17.8 (#4155) (3075df7)
- Update googleapis/sdk-platform-java action to v2.63.0 (#4179) (5f48191)
Documentation
6.102.0 (2025-10-08)
Features
- Add connection property for gRPC interceptor provider (#4149) (deb8dff)
- Support statement_timeout in connection url (#4103) (542c6aa)
Bug Fixes
- Automatically set default_sequence_kind for CREATE SEQUENCE (#4105) (3beea6a)
- deps: Update the Java code generator (gapic-generator-java) to 2.62.3 (7047a3a)
Dependencies
- Update actions/checkout action to v5 (#4069) (4c88eb9)
- Update actions/checkout action to v5 (#4106) (14ebdb3)
- Update actions/setup-java action to v5 (#4071) (e23134a)
- Update all dependencies (#4099) (b262edc)
- Update dependency com.google.api.grpc:grpc-google-cloud-monitoring-v3 to v3.77.0 (#4117) (2451ca2)
- Update dependency com.google.api.grpc:proto-google-cloud-monitoring-v3 to v3.77.0 (#4143) (6c9dc26)
- Update dependency com.google.api.grpc:proto-google-cloud-trace-v1 to v2.76.0 (#4144) (d566a42)
- Update dependency com.google.cloud:google-cloud-monitoring to v3.77.0 (#4145) (8917c05)
- Update dependency com.google.cloud:google-cloud-monitoring to v3.77.0 (#4146) (4ebea1a)
- Update dependency com.google.cloud:google-cloud-trace to v2.76.0 (#4147) (4b1d4af)
- Update dependency com.google.cloud:google-cloud-trace to v2.76.0 (#4148) (8f91a89)
- Update dependency com.google.cloud:sdk-platform-java-config to v3.52.3 (#4107) (8a8a042)
- Update dependency org.json:json to v20250517 (#3881) (5658c83)
- Update googleapis/sdk-platform-java action to v2.62.3 (#4108) (65913ec)
Node.js
Changes for @google-cloud/spanner
8.2.2 (2025-10-07)
Bug Fixes
Python
Changes for google-cloud-spanner
3.59.0 (2025-10-18)
Features
Bug Fixes
Documentation
October 30, 2025
Access ApprovalIAM System for Cross-domain Identity Management (SCIM) Service is generally available (GA).
IAM System for Cross-domain Identity Management (SCIM) Service is generally available (GA).
AlloyDB offers enhanced backups (Preview) that integrate a cluster's backup operations with the Google Cloud Backup and DR Service. This integration provides vaulted backups data with retention lock enforcement, and it uses the Backup and DR Service control plane for centralized policy management and advanced scheduling for AlloyDB clusters. For more information, see Manage enhanced backups.
On October 30, 2025, we released an updated version of the Apigee UI.
| Bug ID | Description |
|---|---|
| 443120120 |
Fixed an issue where an incorrect target URL or cURL command was displayed in the proxy debug properties window. New generated debug sessions now contain information in a flow info event that describes the values used by the proxy to call the target endpoint. The debug UI displays these values and uses them to generate the target URL and curl command displayed in the debug properties window when the target request event is selected. If some of the header fields are masked in the debug session, a warning appears next to the Copy cURL button. If the headers are truncated due to system limitations, Copy cURL is disabled. Older debug sessions that do not have the new target endpoint information no longer attempt to display the target URL or generate a cURL command as they were unreliable. A dialog is displayed warning you of this when attempting to open older debug sessions. |
A new backup vault setting, Prevent deletion for duration specified in backup rule, is now available. When enabled, this feature locks backups for the exact retention period defined in the associated backup plan, overriding the vault's local minimum retention and preventing manual deletion.
Announcing the Public Preview launch of AlloyDB for PostgreSQL enhanced backups with Backup and DR Service. This enables advanced data protection capabilities offered by Backup and DR Service including backup vault support, granular scheduling through backup plans, and centralized management.
Documentation has been updated to clarify the machine types that jobs can use.
Dynamic Workload Scheduler for Batch (Preview) has been replaced with the following consumption options:
Flex-start VMs (Preview): We recommend Flex-start VMs if your job can withstand best-effort availability in exchange for discounted pricing and up to 7 days to finish running.
Calendar-mode reservations (Preview): We recommend calendar-mode reservations if your job needs a very high level of assurance of resource availability for at least 1 day and up to 90 days.
Both consumption options use Dynamic Workload Scheduler pricing, which offers discounts of up to 53% off of on-demand pricing. For more information, see Create and run a job that uses GPUs.
The Apache Iceberg REST catalog in BigLake metastore is now generally available (GA) with several new features, including BigQuery catalog federation, credential vending, and catalog management in the Google Cloud console.
Anomaly Detection is generally available
View and manage cost spikes that deviate from your typical spend patterns using the Anomalies dashboard, which is generally available. Each anomaly includes a detailed root cause analysis that identifies the top services, regions, and SKUs that contributed to the spike.
With this launch, we've added the following features to Anomaly Detection:
- Auto-generated anomaly thresholds that update daily based on your usage patterns.
- Deviation percentage as a new threshold for you to configure for your anomalies.
- Email alerts automatically set up for Billing administrators to help you proactively manage your costs.
All Cloud Composer environment's GKE clusters will receive maintenance exclusions from November 8, 2025 to December 2, 2025. For more information, see Maintenance exclusions.
New Airflow builds are available in Cloud Composer 3:
The following Cloud Composer versions and builds have reached their end of support period: composer-3-airflow-2.7.3-build.21 and composer-2.9.9-*.
New images are available in Cloud Composer 2:
(Cloud Composer 3) Airflow workers are restarted when they exceed their storage limit.
Fixed an error where Airflow components failed to start up when multiple
objects with the same name were present in the /dags or /plugins folder in
the environment's bucket.
Database Migration Service now supports Private Service Connect interfaces for source network connectivity in all heterogeneous migration scenarios.
For more information, see the following pages:
For Cloud Run source deployed services and functions with GPU enabled, Cloud Run defaults to using Cloud Build's e2-highcpu-8 machine type for
the build process when using the gcloud CLI or the Google Cloud console. This
change allows for higher CPU support and faster build times, and also leads to a
moderate increase in the overall cost of your service (GA).
Generally available: Dynamic NICs let you add or remove network interfaces to or from an instance without restarting or recreating the instance.
You can also use Dynamic NICs when you need more network interfaces. The maximum number of vNICs for most machine types in Google Cloud is 10; however, you can configure up to 16 total interfaces by using Dynamic NICs.
For more information, see the following:
Bug fixes in VS Code
Various bug fixes and minor product enhancements.
Advanced reporting dashboards version 3.40
We've released version 3.40 of the advanced reporting dashboards.
New Audit Log dashboard
We've added a new Audit log dashboard to help you track changes to the configuration of your instance. The dashboard tracks changes to the settings on the Developer Settings page, and displays information such as the type of change, who made the change, and when. This dashboard is similar in format to the advanced reporting dashboards, but you can't save it as a new dashboard. You access the Audit Log dashboard from the Settings menu. For more information, see Audit log dashboard.
New Agent Preference table in the Agent Availability dashboard
We've added a new Agent Preference table to the Agent Availability dashboard. This table can help you ensure that queues have properly skilled agents assigned to them. It can also help identify agents who improperly change their availability filters. For more information, see Agent availability dashboard.
We addressed the following issues in this release:
Fixed an issue where the queue groups dashboard failed to display data for users with a custom role assigned to a queue or queue group.
Fixed an issue that caused the Agent Activity Timeline dashboard to display inaccurate or incomplete data.
Fixed an issue on the Virtual Agent - Calls dashboard where the Virtual Agent Name and Queue filters didn't display available values.
Fixed an issue on the Dispositions - Chats dashboard that prevented the Agent Email, Agent ID, and Location filters from displaying available values.
Fixed an issue on the Virtual Agent - Chats dashboard that prevented the Virtual Agent Name filter from displaying available values.
Fixed an issue on the Virtual Agent - Chats dashboard where the Date filter was incorrectly labeled Time Range.
Fixed an issue on the Abandons - Calls dashboard where Customer ANI values weren't appearing in the Queue Abandon Details and IVR Abandon Details tables despite the customer signing the waiver.
Fixed an issue on the Agent Activity Timeline dashboard where the Agent Name filter wasn't working properly.
Upgraded Chronicle API ingestion methods from alpha to beta
We've upgraded the Chronicle API ingestion methods from alpha to beta. This upgrade signals API stability and functional completeness, unblocking customer and partner adoption for production integrations.
For more information, see Ingestion methods.
YARA-L functions
The following new YARA-L functions are now generally available:
strings.ends_with: Takes two strings (value, suffix) and returns true if the suffix is non-empty and at end-of-value.
strings.split: Splits string value using a delimiter argument (by default, a comma).
window.range: Returns the range of the values input values found.
Upgraded Chronicle API ingestion methods from alpha to beta
We've upgraded the Chronicle API ingestion methods from alpha to beta. This upgrade signals API stability and functional completeness, unblocking customer and partner adoption for production integrations.
For more information, see Ingestion methods.
YARA-L functions
The following new YARA-L functions are now generally available:
strings.ends_with: Takes two strings (value, suffix) and returns true if the suffix is non-empty and at end-of-value.
strings.split: Splits string value using a delimiter argument (by default, a comma).
window.range: Returns the range of the values input values found.
Upgraded Chronicle API ingestion methods from alpha to beta
We've upgraded the Chronicle API ingestion methods from alpha to beta. This upgrade signals API stability and functional completeness, unblocking customer and partner adoption for production integrations.
For more information, see Ingestion methods.
YARA-L functions
The following new YARA-L functions are now generally available:
strings.ends_with: Takes two strings (value, suffix) and returns true if the suffix is non-empty and at end-of-value.
strings.split: Splits string value using a delimiter argument (by default, a comma).
window.range: Returns the range of the values input values found.
Partner connection launch update
The following partner connectors have been added to the Looker Studio Connector Gallery:
- Spotify Ads by Dataslayer. Sources: Spotify Ads Studio
- Amazon Ads by Dataslayer. Sources: Amazon Ads
- Zoho by Dataslayer. Sources: Zoho CRM
- Lazada Commerce by Supermetrics. Sources: Supermetrics
- Google Sheets by Porter Metrics. Sources: Google Drive
- OWOX Data Marts by OWOX. Sources: Owox Data Mart
- Close CRM by Supermetrics. Sources: Close
- Centra by Supermetrics. Sources: Centra
- BMS Monitoring by BMS. Sources: BMS
- Vibe by Supermetrics. Sources: Vibe
- Power My Analytics by Power My Analytics. Sources: Constant Contact
- Zen AI - Meta Ads by Zen AI. Sources: Facebook Ads
Pro feature: CSV connector enhancement
Introducing new user experience enhancements for the CSV connector.
You can use custom constraints with Organization Policy to provide more granular control over specific fields for some CA Service resources. For more information, see Manage CA Service resources using custom constraints. This feature is generally available (GA).
You can use custom constraints with Organization Policy to provide more granular control over specific fields for some BigQuery sharing resources. For more information, see Manage Sharing data exchanges and listings using custom constraints. This feature is in preview.
You can use custom constraints with Organization Policy to provide more granular control over specific fields for managed workload identities. For more information, see Use custom organization policies for Managed workload identities. This feature is generally available (GA).
You can use custom constraints with Organization Policy to provide more granular control over specific fields for some Datastream resources. For more information, see Create custom organization policy constraints. This feature is generally available (GA).
In addition to the Enterprise service tier, Issues are available on the Security Command Center Premium service tier at the organization level. This update includes capabilities such as Toxic Combinations, Chokepoints, and Graph Search (Preview). The console navigation has been updated to reflect an Issues page for Premium tier users.
Dynamic Network Interfaces (NICs) are available in General Availability.
Dynamic NICs let you update an instance to add or remove network interfaces without having to restart or recreate the instance.
You can also use Dynamic NICs when you need more network interfaces. The maximum number of vNICs for most machine types in Google Cloud is 10; however, you can configure up to 16 total interfaces by using Dynamic NICs.
For more information, see the following:
October 29, 2025
Access ApprovalText-to-Speech is generally available (GA).
Agent Assist offers summarization with custom sections 5.0 in GA. 5.0 is available in all Agent Assist regions.
Enhanced Validation for API products
Heightened validation logic for creating and updating API products is now available. Apigee now explicitly verifies proxy and environment resources against your organization when creating and updating API products.
Please ensure that all referenced resources exist and are correctly associated with your organization to avoid validation errors.
Support for API-product scoped quotas
You can now set quotas at the API product level to limit the number of requests all API proxies in the API product can process within a specified time frame. See Configuring the quota policy to use API product quota settings for information and instructions.
NOTE: API product-scoped quotas are not supported in Apigee hybrid at this time.
On October 29, 2025, we released an updated version of Apigee.
You can now group reservations together to prioritize idle slot sharing within the group. Reservations within a reservation group share idle slots with each other before making them available to other reservations in the project, giving you more control over slot allocation for high-priority workloads. This feature is in Preview.
You can specify a custom ephemeral /96 IPv6 address range when creating a
regional IPv6 forwarding rule. For more information, see the following:
- Internal passthrough Network Load Balancer overview
- Backend service-based external passthrough Network Load Balancer overview
- Protocol forwarding overview
This feature is in General availability.
You can integrate Cloud SQL for SQL Server with customer-managed Active Directory (CMAD).
CMAD provides capabilities such as authentication and authorization. Joining an instance to a CMAD domain lets you sign in using Windows Authentication with an AD-based identity.
Customer-managed Active Directory (CMAD) is generally available (GA).
Dataproc on Compute Engine subminor image version
2.3.16, announced on
October 20, 2025
has been blocklisted and cannot be used when creating a new cluster.
Google Distributed Cloud (software only) for VMware 1.32.600-gke.53 is available for download. To upgrade, see Upgrade a cluster. Distributed Cloud 1.32.600-gke.53 runs on Kubernetes v1.32.9-gke.200.
If you are using a third-party storage vendor, check the GDC Ready storage partners document to make sure the storage vendor has already passed the qualification for this release.
After a release, it takes approximately 7 to 14 days for the version to become available for use with GKE On-Prem API clients: the Google Cloud console, the gcloud CLI, and Terraform.
The following issues were fixed in 1.32.600-gke.53:
- Fixed vulnerabilities listed in Vulnerability fixes.
The following issues were fixed in 1.32.600-gke.53:
Fixed the
etcd-cleanupjob timeout issue caused by the use of incorrect certificates.Fixed vulnerabilities listed in Vulnerability fixes.
For information about the latest known issues, see Google Distributed Cloud for bare metal known issues in the Troubleshooting section.
Google Distributed Cloud for bare metal 1.32.600-gke.53 is now available for download. To upgrade, see Upgrade clusters. Google Distributed Cloud for bare metal 1.32.600-gke.53 runs on Kubernetes v1.32.9-gke.200.
After a release, it takes approximately 7 to 14 days for the version to become available for installations or upgrades with the GKE On-Prem API clients: the Google Cloud console, the gcloud CLI, and Terraform.
If you use a third-party storage vendor, check the Ready storage partners document to make sure the storage vendor has already passed the qualification for this release of Google Distributed Cloud for bare metal.
(2025-R45) Version updates
GKE cluster versions have been updated.
New versions available for upgrades and new clusters.
The following versions are now available for new GKE clusters, and for manual control plane upgrades and node upgrades for existing clusters. For more information about versioning and upgrades, see GKE versioning and support and About GKE cluster upgrades.
Rapid channel
- Version 1.34.1-gke.1829001 is now the default version for cluster creation in the Rapid channel.
- The following versions are now available in the Rapid channel:
- The following versions are no longer available in the Rapid channel:
- 1.31.13-gke.1040000
- 1.32.9-gke.1130000
- 1.33.5-gke.1201000
- 1.34.0-gke.2201000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1123000
- 1.31 to 1.32.9-gke.1207000
- 1.32 to 1.33.5-gke.1308000
- 1.33 to 1.34.1-gke.1829001
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1123000
- 1.32 to 1.32.9-gke.1207000
- 1.33 to 1.33.5-gke.1308000
- 1.34 to 1.34.1-gke.1829001
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Regular channel
- Version 1.33.5-gke.1162000 is now the default version for cluster creation in the Regular channel.
- The following versions are now available in the Regular channel:
- The following versions are no longer available in the Regular channel:
- 1.31.13-gke.1008000
- 1.32.9-gke.1092000
- 1.33.5-gke.1125000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1023000
- 1.31 to 1.32.9-gke.1108000
- 1.32 to 1.33.5-gke.1162000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1023000
- 1.32 to 1.32.9-gke.1108000
- 1.33 to 1.33.5-gke.1162000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Stable channel
- Version 1.33.5-gke.1080000 is now the default version for cluster creation in the Stable channel.
- The following versions are now available in the Stable channel:
- The following versions are no longer available in the Stable channel:
- 1.31.12-gke.1220000
- 1.32.9-gke.1010000
- 1.33.4-gke.1350000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.12-gke.1265000
- 1.31 to 1.32.9-gke.1072000
- 1.32 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.12-gke.1265000
- 1.32 to 1.32.9-gke.1072000
- 1.33 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Extended channel
- Version 1.33.5-gke.1162000 is now the default version for cluster creation in the Extended channel.
- The following versions are now available in the Extended channel:
- The following versions are no longer available in the Extended channel:
- 1.28.15-gke.2740000
- 1.28.15-gke.2793000
- 1.29.15-gke.1979000
- 1.29.15-gke.2085000
- 1.30.14-gke.1267000
- 1.30.14-gke.1408000
- 1.31.13-gke.1008000
- 1.32.9-gke.1092000
- 1.33.5-gke.1125000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.27 to 1.28.15-gke.2751000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.28 to 1.28.15-gke.2751000
- 1.29 to 1.29.15-gke.1989000
- 1.30 to 1.30.14-gke.1336000
- 1.31 to 1.31.13-gke.1023000
- 1.32 to 1.32.9-gke.1108000
- 1.33 to 1.33.5-gke.1162000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
No channel
- Version 1.33.5-gke.1162000 is now the default version for cluster creation.
- The following versions are now available:
- The following node versions are now available:
- The following versions are no longer available:
- 1.31.12-gke.1220000
- 1.32.9-gke.1010000
- 1.33.4-gke.1245000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1023000
- 1.31 to 1.32.9-gke.1108000
- 1.32 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1023000
- 1.32 to 1.32.9-gke.1108000
- 1.33 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R45) Security updates
This release includes new GKE versions that use updated Container-Optimized OS images. These updated images are cumulative, incorporating security fixes from all Container-Optimized OS versions released since the previous GKE release.
To identify the specific vulnerabilities that were resolved in each updated Container-Optimized OS image, see the Security release notes for that image. The following table includes links to the release notes for each updated Container-Optimized OS image:
| GKE version | Container-Optimized OS version | Details |
|---|---|---|
| 1.33.5-gke.1350000 | cos-121-18867-199-105 | cos-121-18867-199-105 release notes |
| 1.34.1-gke.2037000 | cos-125-19216-0-94 | cos-125-19216-0-94 release notes |
(2025-R45) Version updates
- Version 1.33.5-gke.1162000 is now the default version for cluster creation in the Extended channel.
- The following versions are now available in the Extended channel:
- The following versions are no longer available in the Extended channel:
- 1.28.15-gke.2740000
- 1.28.15-gke.2793000
- 1.29.15-gke.1979000
- 1.29.15-gke.2085000
- 1.30.14-gke.1267000
- 1.30.14-gke.1408000
- 1.31.13-gke.1008000
- 1.32.9-gke.1092000
- 1.33.5-gke.1125000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.27 to 1.28.15-gke.2751000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.28 to 1.28.15-gke.2751000
- 1.29 to 1.29.15-gke.1989000
- 1.30 to 1.30.14-gke.1336000
- 1.31 to 1.31.13-gke.1023000
- 1.32 to 1.32.9-gke.1108000
- 1.33 to 1.33.5-gke.1162000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R45) Version updates
- Version 1.33.5-gke.1162000 is now the default version for cluster creation.
- The following versions are now available:
- The following node versions are now available:
- The following versions are no longer available:
- 1.31.12-gke.1220000
- 1.32.9-gke.1010000
- 1.33.4-gke.1245000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1023000
- 1.31 to 1.32.9-gke.1108000
- 1.32 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1023000
- 1.32 to 1.32.9-gke.1108000
- 1.33 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R45) Version updates
- Version 1.34.1-gke.1829001 is now the default version for cluster creation in the Rapid channel.
- The following versions are now available in the Rapid channel:
- The following versions are no longer available in the Rapid channel:
- 1.31.13-gke.1040000
- 1.32.9-gke.1130000
- 1.33.5-gke.1201000
- 1.34.0-gke.2201000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1123000
- 1.31 to 1.32.9-gke.1207000
- 1.32 to 1.33.5-gke.1308000
- 1.33 to 1.34.1-gke.1829001
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1123000
- 1.32 to 1.32.9-gke.1207000
- 1.33 to 1.33.5-gke.1308000
- 1.34 to 1.34.1-gke.1829001
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R45) Version updates
- Version 1.33.5-gke.1162000 is now the default version for cluster creation in the Regular channel.
- The following versions are now available in the Regular channel:
- The following versions are no longer available in the Regular channel:
- 1.31.13-gke.1008000
- 1.32.9-gke.1092000
- 1.33.5-gke.1125000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1023000
- 1.31 to 1.32.9-gke.1108000
- 1.32 to 1.33.5-gke.1162000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1023000
- 1.32 to 1.32.9-gke.1108000
- 1.33 to 1.33.5-gke.1162000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R45) Version updates
- Version 1.33.5-gke.1080000 is now the default version for cluster creation in the Stable channel.
- The following versions are now available in the Stable channel:
- The following versions are no longer available in the Stable channel:
- 1.31.12-gke.1220000
- 1.32.9-gke.1010000
- 1.33.4-gke.1350000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.12-gke.1265000
- 1.31 to 1.32.9-gke.1072000
- 1.32 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.12-gke.1265000
- 1.32 to 1.32.9-gke.1072000
- 1.33 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Improved Support for Chrome Enterprise Premium
This feature is currently in Preview.
An improved integration for Chrome Enterprise Premium is now available that includes:
- Streamlined connection to Google SecOps, using recommended security defaults
- Enhanced log events with Google Safe Browsing context
- Updated parser and integration documentation: Collect Google Chrome logs
- Curated dashboards for Chrome Enterprise Premium
- Google Workspace SOAR actions to manage Chrome extension blocklist policies (Block Extension and Delete Extension)
Palo Alto Cortex XDR: Version 19.0
Updated incident processing logic in the following action:
- Get Incident Details
Added new filtering options, the ability to create a SecOps alert for every Palo Alto XDR alert, and the ability to track updates to an incident in the following connector:
- Palo Alto Cortex XDR Connector
Tanium: Version 15.0
(REGRESSIVE) Updated JSON result to return data for multiple columns in the following action:
- Get Question Results
ZScaler: Version 10.0
Added support for domain entity type in the following actions:
Add to Whitelist
Lookup Entity
Microsoft Graph Mail Delegated: Version 9.0
Updated the file management logic in the following action:
- Download Attachments from Email
CSV: Version 35.0
Updated file path processing logic in the following connector:
- CSV Connector
Exchange: Version 115.0
Updated the file management logic in the following action:
- Download Attachments
Microsoft Graph Mail: Version 32.0
Updated the file management logic in the following action:
- Download Attachments from Email
CrowdStrike Falcon: Version 68.0
Update the following action to check if there is an existing identical running scan for a provided hostname before creating a new one:
- On-Demand Scan
Palo Alto Cortex XDR: Version 19.0
Updated incident processing logic in the following action:
- Get Incident Details
Added new filtering options, the ability to create a SecOps alert for every Palo Alto XDR alert, and the ability to track updates to an incident in the following connector:
- Palo Alto Cortex XDR Connector
Tanium: Version 15.0
(REGRESSIVE) Updated JSON result to return data for multiple columns in the following action:
- Get Question Results
ZScaler: Version 10.0
Added support for domain entity type in the following actions:
Add to Whitelist
Lookup Entity
Microsoft Graph Mail Delegated: Version 9.0
Updated the file management logic in the following action:
- Download Attachments from Email
CSV: Version 35.0
Updated file path processing logic in the following connector:
- CSV Connector
Exchange: Version 115.0
Updated the file management logic in the following action:
- Download Attachments
Microsoft Graph Mail: Version 32.0
Updated the file management logic in the following action:
- Download Attachments from Email
CrowdStrike Falcon: Version 68.0
Update the following action to check if there is an existing identical running scan for a provided hostname before creating a new one:
- On-Demand Scan
Improved support for Chrome Enterprise Premium
This feature is currently in Preview.
An improved integration for Chrome Enterprise Premium is now available that includes:
- Streamlined connection to Google SecOps, using recommended security defaults
- Enhanced log events with Google Safe Browsing context
- Updated parser and integration documentation: Collect Google Chrome logs
- Curated dashboards for Chrome Enterprise Premium
- Google Workspace SOAR actions to manage Chrome extension blocklist policies (Block Extension and Delete Extension)
Improved Support for Chrome Enterprise Premium
This feature is currently in Preview.
An improved integration for Chrome Enterprise Premium is now available that includes:
- Streamlined connection to Google SecOps, using recommended security defaults
- Enhanced log events with Google Safe Browsing context
- Updated parser and integration documentation: Collect Google Chrome logs
- Curated dashboards for Chrome Enterprise Premium
- Google Workspace SOAR actions to manage Chrome extension blocklist policies (Block Extension and Delete Extension)
Palo Alto Cortex XDR: Version 19.0
Updated incident processing logic in the following action:
- Get Incident Details
Added new filtering options, the ability to create a SecOps alert for every Palo Alto XDR alert, and the ability to track updates to an incident in the following connector:
- Palo Alto Cortex XDR Connector
Tanium: Version 15.0
(REGRESSIVE) Updated JSON result to return data for multiple columns in the following action:
- Get Question Results
ZScaler: Version 10.0
Added support for domain entity type in the following actions:
Add to Whitelist
Lookup Entity
Microsoft Graph Mail Delegated: Version 9.0
Updated the file management logic in the following action:
- Download Attachments from Email
CSV: Version 35.0
Updated file path processing logic in the following connector:
- CSV Connector
Exchange: Version 115.0
Updated the file management logic in the following action:
- Download Attachments
Microsoft Graph Mail: Version 32.0
Updated the file management logic in the following action:
- Download Attachments from Email
CrowdStrike Falcon: Version 68.0
Update the following action to check if there is an existing identical running scan for a provided hostname before creating a new one:
- On-Demand Scan
Named schemas are supported in Spanner Graph. For more information, see Spanner Graph schema overview.
You can specify a /96 IPv6 address range when reserving static regional IPv6
addresses. For more information, see the following:
This feature is available in General Availability.
October 28, 2025
Apigee API hubAPI insights in API hub
API insights is now available in API hub, providing a unified view of your API traffic and performance across all connected gateways. With API insights, you can gain a holistic understanding of your API ecosystem's health and quickly identify areas for optimization.
Currently, API insights supports data sources from Apigee, Apigee hybrid, Apigee Edge Public Cloud, and Apigee Edge Private Cloud (OPDK).
For more information, see API insights overview.
Detailed API resource insights
A new Insights tab is now available on the API details page, providing API-centric analytics to help you understand usage patterns and performance for each of your APIs.
You can now analyze key metrics such as total traffic, average TPS, request/response latencies, and more, directly from the API details page.
For more information, see View API resource insights.
Subscriber email logging lets you log the principal identifiers of users
who execute jobs and queries against linked datasets. You can enable
logging at the
listing level
and the
data exchange level.
The logged data is available in the job_principal_subject field of the
INFORMATION_SCHEMA.SHARED_DATASET_USAGE view.
This feature is
generally available.
The BigQuery Data Transfer Service can now transfer data from the following data sources:
Transfers from these data sources are now generally available (GA).
You can use Cloud KMS Autokey in the Google Cloud console to automate the creation and use of customer-managed encryption keys (CMEK) in Bigtable clusters.
Application Load Balancers support authorization policies that let you establish access control checks for incoming traffic.
For details, see Authorization policy overview.
This feature is in General availability.
Both internal passthrough Network Load Balancers and external passthrough Network Load Balancers support load balancing to managed instance groups (MIGs) comprised of IPv6-only VM instances.
For more details, see the following pages:
- Set up an external passthrough Network Load Balancer with a backend service
- Set up an internal passthrough Network Load Balancer with VM instance group backends
This feature is in General availability.
Cloud SQL has enhanced the optimized writes feature, which includes an improved crash recovery algorithm to reduce crash recovery time and utilizes unused disk I/O throughput adaptively to accelerate buffer pool warm-up. The optimized writes feature provides a set of write performance improvements that adjust MySQL configurations dynamically based on workload demand and underlying infrastructure.
By default these improvements are enabled for all new Cloud SQL Enterprise Plus edition instances that you create or that you upgrade to from Cloud SQL Enterprise edition.
For more information about optimized writes, see Configure database flags.
1.25.5-asm.9 is now available for in-cluster Cloud Service Mesh.
This patch release contains fixes for the security vulnerabilities listed in GCP-2025-064. For details on upgrading Cloud Service Mesh, refer to Upgrade Cloud Service Mesh. Cloud Service Mesh v1.25.5-asm.9 uses Envoy v1.33.12.
1.26.5-asm.1 is now available for in-cluster Cloud Service Mesh.
This patch release contains fixes for the security vulnerabilities listed in GCP-2025-064. For details on upgrading Cloud Service Mesh, refer to Upgrade Cloud Service Mesh. Cloud Service Mesh v1.26.5-asm.1 uses Envoy v1.34.10.
1.27.2-asm.1 is now available for in-cluster Cloud Service Mesh.
This patch release contains fixes for the security vulnerabilities listed in GCP-2025-064. For details on upgrading Cloud Service Mesh, refer to Upgrade Cloud Service Mesh. Cloud Service Mesh v1.27.2-asm.1 uses Envoy v1.35.6.
Generally available: You can create managed instance groups (MIGs) that consist of IPv6-only VM instances.
For more information, see Basic scenarios for creating managed instance groups (MIGs).
Fixed a Jupyter Kernel Gateway bug that caused failures while restarting kernels.
New Dataproc on Compute Engine subminor image versions:
- 2.0.153-debian10, 2.0.153-ubuntu18, 2.0.153-rocky8
- 2.1.102-debian11, 2.1.102-ubuntu20, 2.1.102-ubuntu20-arm, 2.1.102-rocky8
- 2.2.70-debian12, 2.2.70-ubuntu22, 2.2.70-ubuntu22-arm, 2.2.70-rocky9
- 2.3.17-debian12, 2.3.17-ubuntu22, 2.3.17-ubuntu22-arm, 2.3.17-ml-ubuntu22, 2.3.17-rocky9
You can use the G4 VM, powered by NVIDIA's RTX PRO 6000 GPUs, with GKE Autopilot in version 1.34.1-gke.1829001 or later. To get started, see Deploy GPU workloads in Autopilot.
Autoscaled blue-green upgrades are a type of node upgrade strategy that maximizes the amount of time before disruption-intolerant workloads are evicted, while minimizing cost. This feature is available in Preview for GKE Standard node pools. For more information, see Autoscaled blue-green upgrades.
Risk-based alerting with entity-only rules
With the new ENTITY_RISK_CHANGE UDM event type, you can now write YARA-L
detection rules that trigger independently of ingested events. This capability
lets you focus specifically on changes in an entity's risk score, significantly
decreasing the time required for Google Security Operations to detect and alert
on shifting entity risk levels.
For more information, see Risk-based alerting with entity-only rules.
Risk-based alerting with entity-only rules
With the new ENTITY_RISK_CHANGE UDM event type, you can now write YARA-L
detection rules that trigger independently of ingested events. This capability
lets you focus specifically on changes in an entity's risk score, significantly
decreasing the time required for Google Security Operations to detect and alert
on shifting entity risk levels.
For more information, see Risk-based alerting with entity-only rules.
Risk-based alerting with entity-only rules
With the new ENTITY_RISK_CHANGE UDM event type, you can now write YARA-L
detection rules that trigger independently of ingested events. This capability
lets you focus specifically on changes in an entity's risk score, significantly
decreasing the time required for Google Security Operations to detect and alert
on shifting entity risk levels.
For more information, see Risk-based alerting with entity-only rules.
The ability to use a path wildcard in the aud (audience) field when using a
service account JWT to authenticate with an IAP-secured resource
is generally available.
For more information, see Authenticate with a service account JWT.
Authorization extensions help you configure Cloud Load Balancing authorization policies to use custom authorization engines. This feature is in General Availability.
reCAPTCHA policy-based challenge keys are available in GA. With policy-based challenge keys, you can configure reCAPTCHA to deterministically trigger CAPTCHA challenges based on a score threshold and challenge difficulty. For more information about the policy-based challenge keys, see reCAPTCHA keys overview.
October 27, 2025
AlloyDB for PostgreSQLAlloyDB supports configuring Authorized Networks for Public IP without any CIDR-range restrictions. Use custom organization policies to limit the size and number of Authorized Networks. See Supported custom constraints and operations for examples.
Introduction of the target.evaluated.url flow variable
This release includes a new flow variable, target.evaluated.url,
which should be used instead of the target.url flow variable in
cases when the URL is dynamically constructed based on user input.
For more information, see the target flow variables documentation.
On October 27, 2025, we released an updated version of Apigee.
You can now use the Data Engineering Agent to use Gemini in BigQuery to build and modify data pipelines to ingest data into BigQuery. This feature is in preview.
The administrative jobs explorer now includes a job details page to help you diagnose and troubleshoot queries. The Performance tab compiles query information including the execution graph, SQL text, execution history, performance variance, and system load during execution. You can also compare two jobs to identify discrepancies and potential areas to improve query performance.
This feature is in Preview.
BigQuery now offers the following managed AI functions that use Gemini to help you filter, join, rank, and classify your data:
AI.IF: Filter and join text or multimodal data based on a condition described in natural language.AI.SCORE: Rate text or multimodal input to rank your data by quality, similarity, or other criteria.AI.CLASSIFY: Classify text into user-defined categories.
These functions are in Preview.
You can now use the Apache Arrow format to stream data to BigQuery with the Storage Write API. This feature is generally available (GA).
Bigtable provides vector and key-value store integrations for LangChain, an LLM orchestration framework. For more information, see Build LLM-powered applications using LangChain and Perform Maximal Marginal Relevance search with LangChain on Bigtable.
A weekly digest of client library updates from across the Cloud SDK.
Java
Changes for google-cloud-bigtable
2.68.0 (2025-10-22)
Features
- Add Type API updates needed to support structured keys in materialized views (469290e)
Bug Fixes
- Add ReadRows/SampleRowKeys bindings for materialized views (469290e)
- deps: Update the Java code generator (gapic-generator-java) to 2.62.3 (469290e)
- deps: Update the Java code generator (gapic-generator-java) to 2.63.0 (ed6c03f)
- Don't use String.format in Preconditions messages (#2691) (62a1812)
- Fixed the bigtableadmin API name for snippet region tags and possibly other GAPIC attributes (469290e)
Dependencies
Python
Changes for google-cloud-bigtable
2.34.0 (2025-10-16)
Features
New images are available in Cloud Composer 2:
(Cloud Composer 2) Configuration of firewall rules for Private IP environments now requires allowing egress traffic on port 19090.
All scheduled and started maintenance activities are now listed together on the Maintenance page. You can use the Settings menu for scheduled activities that you can modify.
The rollout of the following extension versions and plugin versions is underway:
Extensions and plugins
pg_squeezeis upgraded from 1.8 to 1.9 for PostgreSQL version 13 and later.pg_cronis upgraded from 1.6.4 to 1.6.7 for PostgreSQL version 10 and later.postgisis upgraded from 3.5.2 to 3.6.0 for PostgreSQL version 13 and later.rdkitis upgraded from 4.6.1 to 4.7.0.
To use these versions of the extensions and plugins, update your instance to
[PostgreSQL version].R20251004.01_07.
If you use a maintenance window, then the updates to the minor, extension, and plugin versions happen according to the timeframe that you set in the window. Otherwise, the updates occur within the next few weeks.
For more information on checking your maintenance version, see Self-service maintenance. To find your maintenance window or to manage maintenance updates, see Find and set maintenance windows.
The following images are now rolling out for managed Cloud Service Mesh:
- 1.21.6-asm.4 is rolling out to the rapid release channel.
- 1.20.8-asm.56 is rolling out to the regular release channel.
- 1.19.10-asm.52 is rolling out to the stable release channel.
CNI/managed data plane controller version 1.20.8-asm.56 is rolling out to all release channels.
These patches contain fixes for the following CVEs:
1.21.6-asm.4
| Name | Envoy Proxy | Envoy Proxy Distroless | Control plane |
|---|---|---|---|
| CVE-2025-4802 | - | Yes | - |
| CVE-2025-8058 | - | Yes | - |
| CVE-2023-4039 | Yes | - | - |
| CVE-2024-10041 | Yes | - | - |
| CVE-2025-32988 | Yes | - | - |
| CVE-2025-6395 | Yes | - | - |
| CVE-2025-48964 | Yes | - | - |
| CVE-2025-32989 | Yes | - | - |
| CVE-2025-47268 | Yes | - | - |
| CVE-2025-40909 | Yes | - | - |
| CVE-2025-32990 | Yes | - | - |
1.20.8-asm.55
| Name | Envoy Proxy | Envoy Proxy Distroless | Control plane |
|---|---|---|---|
| CVE-2023-4813 | - | Yes | - |
| CVE-2025-8058 | - | Yes | - |
| CVE-2023-4806 | - | Yes | - |
| CVE-2025-32989 | Yes | - | - |
| CVE-2025-32988 | Yes | - | - |
| CVE-2025-48964 | Yes | - | - |
| CVE-2024-10041 | Yes | - | - |
| CVE-2025-40909 | Yes | - | - |
| CVE-2025-32990 | Yes | - | - |
| CVE-2025-47268 | Yes | - | - |
| CVE-2025-6395 | Yes | - | - |
| CVE-2023-4039 | Yes | - | - |
1.19.10-asm.52
| Name | Envoy Proxy | Envoy Proxy Distroless | Control plane |
|---|---|---|---|
| CVE-2023-4813 | - | Yes | - |
| CVE-2025-8058 | - | Yes | - |
| CVE-2023-4806 | - | Yes | - |
| CVE-2025-32989 | Yes | - | - |
| CVE-2025-48964 | Yes | - | - |
| CVE-2024-10041 | Yes | - | - |
| CVE-2025-32988 | Yes | - | - |
| CVE-2025-40909 | Yes | - | - |
| CVE-2025-32990 | Yes | - | - |
| CVE-2025-47268 | Yes | - | - |
| CVE-2025-6395 | Yes | - | - |
| CVE-2023-4039 | Yes | - | - |
CNI & MDPC
| Name | CNI | MDPC |
|---|---|---|
| CVE-2024-56406 | Yes | Yes |
| CVE-2025-1372 | Yes | Yes |
| CVE-2025-46836 | Yes | Yes |
| CVE-2025-30258 | Yes | Yes |
| CVE-2023-4039 | Yes | Yes |
| CVE-2025-4802 | Yes | Yes |
| CVE-2025-1377 | Yes | Yes |
| CVE-2025-4598 | Yes | Yes |
| CVE-2025-3576 | Yes | Yes |
A weekly digest of client library updates from across the Cloud SDK.
Java
Changes for google-cloud-storage
2.59.0 (2025-10-21)
Features
Bug Fixes
- Add case insensitive check for X-Goog-Content-SHA256 in SignatureInfo (#3337) (54bc2c1)
- Migrate away from GoogleCredentials.fromStream() usages (#3339) (7e42c2f)
- Update BlobReadSession channels to not implicitly close once EOF is observed (#3344) (9f0a93e)
- Update grpc single-shot uploads to attach the callers stracktrace as suppressed exception if an error happens in the background (#3330) (64e2b2e)
- Update retry logic for grpc start resumable upload to properly handle client side deadline_exceeded (#3354) (6eb3331)
Dependencies
Following a firmware update, Confidential VM instances with AMD SEV-SNP generate v4 attestation reports. Attestation report parsers that are designed for v3 attestation reports might break.
Customers using go-sev-guest to
parse attestation reports can resolve attestation failures by updating to
go-sev-guest v0.14.0 or above.
If you're writing your own parser, the attestation report format is defined by the SEV Secure Nested Paging Firmware ABI Specification.
cos-121-18867-294-2
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.113 | v27.5.1 | v2.0.6 | See List |
This is an LTS Refresh release.
Updated app-containers/runc to v1.2.7.
Reduced gcr_wait_online retry gap.
Upgraded sys-auth/pambase to v20250906.
Upgraded app-admin/google-guest-configs to v20250805.00.
Upgraded dev-lang/go to v1.23.12.
Upgraded sys-apps/hwdata to v0.400.
Upgraded sys-apps/pv to v1.9.42.
Upgraded sys-apps/less to v685.
Upgraded dev-libs/expat to v2.7.3.
Upgraded app-admin/sudo to v1.9.17_p2.
Upgraded dev-db/sqlite to v3.50.3.
Fixed CVE-2025-11494 in binutils-libs.
Fixed CVE-2025-11495 in binutils-libs.
Fixed CVE-2025-11412 in binutils-libs.
cos-113-18244-521-7
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.1.155 | v24.0.9 | v1.7.27 | See List |
This is an LTS Refresh release.
Updated app-containers/runc to v1.2.7.
Added support for NVIDIA driver v535.274.02 and v570.195.03. Updated default driver version to v535.274.02 for devices using 535 as the default driver. Updated the default driver version to v570.195.03 for NVIDIA_H200.
Upgraded app-admin/google-guest-configs to v20250805.00.
Upgraded net-nds/rpcbind to v1.2.8.
Upgraded sys-apps/less to v685.
Upgraded sys-apps/hwdata to v0.400.
Upgraded dev-db/sqlite to v3.50.3.
Upgraded app-admin/sudo to v1.9.17_p2.
Fixed CVE-2025-11413 and CVE-2025-11414 in binutils-libs.
Fixed CVE-2025-11494 in binutils-libs.
Fixed CVE-2025-11495 in binutils-libs.
Fixed CVE-2025-11412 in binutils-libs.
Fixed CVE-2025-39998 in the Linux kernel.
Fixed CVE-2025-39996 in the Linux kernel.
cos-dev-129-19340-0-0
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.54 | v27.5.1 | v2.1.3 | See List |
Updated cos-gpu-installer to v2.5.9. This adds support for installing drivers for GB 300 devices.
Updated the Linux kernel to v6.12.54.
Added GB300 support to cos-extensions.
Added support for NVIDIA driver v535.274.02 and v570.195.03.
Upgraded chromeos-base/google-breakpad to v2025.10.16.221019-r255.
Upgraded sys-apps/less to v685.
Upgraded sys-apps/pv to v1.9.44.
Fixed CVE-2025-11413 and CVE-2025-11414 in binutils-libs.
cos-117-18613-439-9
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.111 | v24.0.9 | v1.7.28 | See List |
Updated app-containers/runc to v1.2.7.
Added support for NVIDIA driver v535.274.02 and v570.195.03.
Upgraded sys-apps/hwdata to v0.400.
Upgraded sys-apps/less to v685.
Fixed CVE-2025-11413 and CVE-2025-11414 in binutils-libs.
Fixed CVE-2025-11494 in binutils-libs.
Fixed CVE-2025-11495 in binutils-libs.
Fixed CVE-2025-11412 in binutils-libs.
cos-125-19216-0-115
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.46 | v27.5.1 | v2.1.3 | See List |
Updated cos-gpu-installer to v2.5.9. This adds support for installing drivers for GB 300 devices.
Added GB300 support to cos-extensions.
Added support for NVIDIA driver v535.274.02 and v570.195.03.
Upgraded sys-apps/pv to v1.9.44.
Fixed CVE-2025-11413, CVE-2025-11414 in binutils-libs.
The database clone feature is now supported at the General Availability (GA) level.
The database clone feature is now supported at the General Availability (GA) level.
A weekly digest of client library updates from across the Cloud SDK.
Java
Changes for google-cloud-datastore
2.32.3 (2025-10-20)
Bug Fixes
- deps: Update the Java code generator (gapic-generator-java) to 2.63.0 (b9b95cb)
Dependencies
New rules for Chrome Enterprise Premium
Curated Detections has been enhanced with additional Chrome Enterprise Premium Browser Threat detections. The following rules have been added to the rulepack:
- Archive Exfiltration Event to Non-Google Websites
- Google Chrome Navigation Event to Shortened URLs
- Suspicious Download from Filehosting or Chat Platform in Chrome Management
- Chrome Suspicious Download Event from Newly Observed Domain in Environment
New rules for Chrome Enterprise Premium
Curated Detections has been enhanced with additional Chrome Enterprise Premium Browser Threat detections. The following rules have been added to the rulepack:
- Archive Exfiltration Event to Non-Google Websites
- Google Chrome Navigation Event to Shortened URLs
- Suspicious Download from Filehosting or Chat Platform in Chrome Management
- Chrome Suspicious Download Event from Newly Observed Domain in Environment
New rules for Chrome Enterprise Premium
Curated Detections has been enhanced with additional Chrome Enterprise Premium Browser Threat detections. The following rules have been added to the rulepack:
- Archive Exfiltration Event to Non-Google Websites
- Google Chrome Navigation Event to Shortened URLs
- Suspicious Download from Filehosting or Chat Platform in Chrome Management
- Chrome Suspicious Download Event from Newly Observed Domain in Environment
A weekly digest of client library updates from across the Cloud SDK.
Java
Changes for google-cloud-pubsub
1.143.0 (2025-10-20)
Features
- Annotate some resource fields with their corresponding API types (ab60afa)
- Implement SubscriberShutdownSettings (#2569) (8195f6f)
Bug Fixes
- deps: Update the Java code generator (gapic-generator-java) to 2.63.0 (ab60afa)
- Update .OwlBot-hermetic.yaml to preserve SubscriberShutdownSettings files (#2583) (f3cf5e7)
Dependencies
- Update actions/checkout action to v5 (#2576) (1375f6d)
- Update actions/checkout action to v5 (#2584) (25059ce)
- Update dependency com.google.cloud:google-cloud-bigquery to v2.55.2 (#2582) (d0f9673)
- Update dependency com.google.cloud:google-cloud-storage to v2.58.1 (#2580) (d156cdb)
- Update dependency com.google.cloud:sdk-platform-java-config to v3.53.0 (#2589) (ce7cb09)
The NEW_ZEALAND_DRIVERS_LICENSE_NUMBER infoType detector is available in all regions. For more information about all built-in infoTypes, see the InfoType detector reference.
October 26, 2025
Google SecOpsDelete high-load SOAR environments
You can now easily delete environments with heavy loads directly from the platform.
Delete high-load SOAR environments
You can now easily delete environments with heavy loads directly from the platform.
Delete high-load environments
You can now easily delete environments with heavy loads directly from the platform.
Release 6.3.65 is being rolled out to the first phase of regions as listed here.
This release contains the following changes:
Delete high-load environments
You can now easily delete environments with heavy loads directly from the platform.
Release 6.3.65 is being rolled out to the first phase of regions as listed here.
This release contains the following changes:
October 25, 2025
Cloud Healthcare API- The Cloud Healthcare API is now available in the
me-central1(Qatar) andme-central2(KSA) regions.
Release 6.3.64 is now available for all regions.
Release 6.3.64 is now available for all regions.
October 24, 2025
Cluster ToolkitCluster Toolkit version v1.70.0 is available. This release adds
automated TPU support and Cloud Storage FUSE mounts in the TPU v6 blueprint and refactors
the H4D blueprint. This version also includes breaking changes, such as removing
support for the maintenance_interval field for reservations created by Technical Account Managers (TAMs) and
migrating Jobset from static manifests to a Helm chart. For a complete list of
changes, see the Release announcement on
GitHub.
Config Controller now uses the following versions of its included products:
- Config Connector v1.134.1, release notes
cos-125-19216-0-110
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.46 | v27.5.1 | v2.1.3 | See List |
Updated cos-gpu-installer to v2.5.8.
Added support for A4X-Max NICs.
Updated app-containers/runc to v1.2.7.
Added support for NVIDIA GB300 devices.
Reduced gcr_wait_online retry gap.
Upgraded sys-apps/less to v685.
Upgraded sys-apps/pv to v1.9.42.
Upgraded sys-apps/hwdata to v0.400.
Fixed CVE-2025-11494 in binutils-libs.
Fixed CVE-2025-11495 in binutils-libs.
Fixed CVE-2025-11412 in binutils-libs.
Runtime sysctl changes:
- Changed: net.ipv4.udp_mem: 188034 250714 376068 -> 188034 250715 376068
cos-dev-129-19334-0-0
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.53 | v27.5.1 | v2.1.3 | See List |
Updated cos-gpu-installer to v2.5.8.
Added support for A4X-Max NICs.
Updated app-containers/runc to v1.2.7.
Added support for NVIDIA GB300 devices.
Upgraded sys-auth/pambase to v20251013.
Upgraded app-admin/google-guest-configs to v20251014.00.
Upgraded sys-apps/hwdata to v0.400.
Upgraded sys-apps/pv to v1.9.42.
Fixed CVE-2025-11494 in binutils-libs.
Fixed CVE-2025-11495 in binutils-libs.
Fixed CVE-2025-11412 in binutils-libs.
Bug fixes in IntelliJ
Various bug fixes and minor product enhancements.
You can view IP address utilization when you list or describe subnets. IP address utilization displays the number of free and allocated IP addresses in a subnet. This feature is available in General Availability.
October 23, 2025
AlloyDB for PostgreSQLYou can now perform time-series forecasting in AlloyDB to predict future trends based on your historical data. This feature supports various forecasting models, including TimesFM, and is available in Preview.
BigQuery is now offering early access to conversational analytics. Conversational analytics accelerates data analysis by enabling quick insights through natural language. Users can chat with their BigQuery data, create custom agents, and access those agents even outside of BigQuery. To enroll in conversational analytics early access, fill out the request form.
- A new application has been added to the Cloud Console under "Healthcare", called "DICOM Studio"
- This new application provides a web interface for exploring DICOM Stores
in the Cloud Healthcare API similar to "FHIR Viewer".
- Search and find studies, series, and instances in any DICOM Store using our DICOM Web API
- View studies, series and instance metadata
- Edit studies, series and instance metadata
- Perform CRUD operations (Delete) on studies, series and instances
- View studies, series and instance images via a transcoded image preview
You can now use the Google Cloud CLI and the Cloud Monitoring API to list incidents and get incident details. This feature is in Public Preview. For more information, see the following pages:
Cloud SQL now proactively detects and works to cancel high memory usage connections to prevent out-of-memory (OOM) failures. For more information, see Cancelled queries due to high memory usage.
You can now use Storage batch operations to create and manage retention configurations for objects in bulk using the PutMetadata transformation.
Conversational Agents (Dialogflow CX): The Entity Types console menu now allows you to set a page size for entity entries and excluded phrases. Pagination options are automatically displayed if there are more than 10 items listed.
Conversational Agents (Dialogflow CX):The Block none safety feature in agent settings is no longer restricted access.
Conversational Agents (Dialogflow CX): New fields temperature, input_token_limit and output_token_limit are now available for LlmModelSettings in the v3beta1 API. This allows you to adjust the model per playbook.
Conversational Agents (Dialogflow CX): You can now configure service account authorization for both tools and webhooks. See the reference documentation for details.
Bug fixes in VS Code
Various bug fixes and minor product enhancements.
The following models are available through Model Garden:
Conversational Analytics in Looker
The following features are available in Preview for use with Conversational Analytics in Looker instances that are running Looker 25.18 or later:
- Event and event attribute information is now available in System Activity Explores.
- A Conversational Analytics System Activity dashboard is now available to surface usage data for Conversational Analytics features in Looker, including the most popular data agents, the most popular Explores that are used in conversations, and the most active users.
Looker now supports cloning a public Git repository using an https:// URL. Looker does not support cloning Git repositories using git:// URLs.
October 22, 2025
BigQueryYou can now use custom constraints with Organization Policy to provide more granular control over specific fields for some BigQuery sharing resources. For more information, see Manage Sharing data exchanges and listings using custom constraints. This feature is in preview.
Support for table parameters in table-value functions (TVFs) has been temporarily disabled. We are working to restore this feature as soon as possible.
BigQuery ML now offers a built-in TimesFM univariate time series forecasting model that implements Google Research's open source TimesFM model. You can use BigQuery ML's built-in TimesFM model with the following functions:
- Use
AI.FORECASTto perform forecasting. This function now supports a larger context window. - Use
AI.EVALUATEto evaluate forecasted data against a reference time series based on historical data.
To try using a TimesFM model with the AI.FORECAST function, see
Forecast a time series with a TimesFM univariate model.
This feature is generally available (GA).
The default value of the
NO_PROXY
environment variable now includes the IP address of the environment's cluster
Compute Engine metadata server.
(Airflow 2.10.5) The apache-airflow-providers-cncf-kubernetes package was
upgraded to version 10.8.2.
For changes in other packages, see the
preinstalled packages changelog.
New Airflow builds are available in Cloud Composer 3:
The following Cloud Composer versions and builds have reached their end of support period: composer-3-airflow-2.7.3-build.20, composer-3-airflow-2.7.3-build.19, composer-2.9.8-*, composer-2.9.7-*.
New images are available in Cloud Composer 2:
(Airflow 2.10.5) The apache-airflow-providers-google package was upgraded to version 18.0.0 in Cloud Composer 2 images and Cloud Composer 3 builds.
For more information about changes, see the apache-airflow-providers-google changelog from version 17.2.0 to version 18.0.0.
Announcing the General Availability (GA) of Lightning Engine for Google Cloud Serverless for Apache Spark. Lightning Engine is a high-performance query accelerator that delivers up to 4.3x faster performance for Spark workloads compared to open-source Spark, as measured on TPC-H-like benchmarks.
For more details on enabling Lightning Engine and its advanced features like Native Query Execution (NQE), see the official documentation.
Serverless for Apache Spark: With the Lightning Engine GA release, the property to enable Native Query Execution (NQE) feature has been updated.
In order to use Lightning Engine, submit your jobs in the Premium tier. Under Lightning Engine, if you would like to use the NQE feature, set the new flag: spark.dataproc.lightningEngine.runtime=native. Users are encouraged to try this feature to explore the full potential of Lightning Engine.
For backward compatibility, the legacy property that was used to enable NQE spark.dataproc.runtimeEngine=native will continue to be honored in the existing runtimes 1.2, 2.2 and 2.3, but it's not supported in future releases (3.0+ runtimes).
(2025-R44) Version updates
GKE cluster versions have been updated.
New versions available for upgrades and new clusters.
The following versions are now available for new GKE clusters, and for manual control plane upgrades and node upgrades for existing clusters. For more information about versioning and upgrades, see GKE versioning and support and About GKE cluster upgrades.
Rapid channel
- Version 1.34.0-gke.2201000 is now the default version for cluster creation in the Rapid channel.
- The following versions are now available in the Rapid channel:
- The following versions are no longer available in the Rapid channel:
- 1.31.13-gke.1023000
- 1.32.9-gke.1108000
- 1.33.5-gke.1162000
- 1.34.1-gke.1293000
- 1.34.1-gke.1431000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1040000
- 1.31 to 1.32.9-gke.1130000
- 1.32 to 1.33.5-gke.1201000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1040000
- 1.32 to 1.32.9-gke.1130000
- 1.33 to 1.33.5-gke.1201000
- 1.34 to 1.34.0-gke.2201000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Regular channel
- Version 1.33.5-gke.1125000 is now the default version for cluster creation in the Regular channel.
- The following versions are now available in the Regular channel:
- The following versions are no longer available in the Regular channel:
- 1.31.12-gke.1265000
- 1.32.9-gke.1072000
- 1.33.5-gke.1080000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1008000
- 1.31 to 1.32.9-gke.1092000
- 1.32 to 1.33.5-gke.1125000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1008000
- 1.32 to 1.32.9-gke.1092000
- 1.33 to 1.33.5-gke.1125000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Stable channel
- Version 1.33.4-gke.1350000 is now the default version for cluster creation in the Stable channel.
- The following versions are now available in the Stable channel:
- The following versions are no longer available in the Stable channel:
- 1.31.11-gke.1036000
- 1.32.8-gke.1170000
- 1.33.4-gke.1245000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.12-gke.1220000
- 1.31 to 1.32.9-gke.1010000
- 1.32 to 1.33.4-gke.1350000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.12-gke.1220000
- 1.32 to 1.32.9-gke.1010000
- 1.33 to 1.33.4-gke.1350000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Extended channel
- Version 1.33.5-gke.1125000 is now the default version for cluster creation in the Extended channel.
- The following versions are now available in the Extended channel:
- The following versions are no longer available in the Extended channel:
- 1.28.15-gke.2730000
- 1.28.15-gke.2767000
- 1.29.15-gke.1971000
- 1.29.15-gke.2002000
- 1.30.14-gke.1150000
- 1.30.14-gke.1349000
- 1.31.12-gke.1265000
- 1.32.9-gke.1072000
- 1.33.5-gke.1080000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.27 to 1.28.15-gke.2740000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.28 to 1.28.15-gke.2740000
- 1.29 to 1.29.15-gke.1979000
- 1.30 to 1.30.14-gke.1267000
- 1.31 to 1.31.13-gke.1008000
- 1.32 to 1.32.9-gke.1092000
- 1.33 to 1.33.5-gke.1125000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
No channel
- Version 1.33.5-gke.1125000 is now the default version for cluster creation.
- The following versions are now available:
- The following node versions are now available:
- The following versions are no longer available:
- 1.31.11-gke.1036000
- 1.32.8-gke.1170000
- 1.33.4-gke.1172000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1008000
- 1.31 to 1.32.9-gke.1092000
- 1.32 to 1.33.4-gke.1350000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1008000
- 1.32 to 1.32.9-gke.1092000
- 1.33 to 1.33.4-gke.1350000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R44) Security updates
This release includes new GKE versions that use updated Container-Optimized OS images. These updated images are cumulative, incorporating security fixes from all Container-Optimized OS versions released since the previous GKE release.
To identify the specific vulnerabilities that were resolved in each updated Container-Optimized OS image, see the Security release notes for that image. The following table includes links to the release notes for each updated Container-Optimized OS image:
| GKE version | Container-Optimized OS version | Details |
|---|---|---|
| 1.28.15-gke.2793000 | cos-113-18244-448-63 | cos-113-18244-448-63 release notes |
| 1.29.15-gke.2085000 | cos-113-18244-448-63 | cos-113-18244-448-63 release notes |
| 1.30.14-gke.1408000 | cos-113-18244-448-63 | cos-113-18244-448-63 release notes |
| 1.31.13-gke.1123000 | cos-117-18613-339-84 | cos-117-18613-339-84 release notes |
| 1.32.9-gke.1207000 | cos-117-18613-339-84 | cos-117-18613-339-84 release notes |
| 1.33.5-gke.1308000 | cos-121-18867-199-88 | cos-121-18867-199-88 release notes |
| 1.34.0-gke.2201000 | cos-121-18867-199-28 | cos-121-18867-199-28 release notes |
| 1.34.1-gke.1829001 | cos-125-19216-0-94 | cos-125-19216-0-94 release notes |
(2025-R44) Version updates
- Version 1.33.5-gke.1125000 is now the default version for cluster creation in the Extended channel.
- The following versions are now available in the Extended channel:
- The following versions are no longer available in the Extended channel:
- 1.28.15-gke.2730000
- 1.28.15-gke.2767000
- 1.29.15-gke.1971000
- 1.29.15-gke.2002000
- 1.30.14-gke.1150000
- 1.30.14-gke.1349000
- 1.31.12-gke.1265000
- 1.32.9-gke.1072000
- 1.33.5-gke.1080000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.27 to 1.28.15-gke.2740000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.28 to 1.28.15-gke.2740000
- 1.29 to 1.29.15-gke.1979000
- 1.30 to 1.30.14-gke.1267000
- 1.31 to 1.31.13-gke.1008000
- 1.32 to 1.32.9-gke.1092000
- 1.33 to 1.33.5-gke.1125000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R44) Version updates
- Version 1.33.5-gke.1125000 is now the default version for cluster creation.
- The following versions are now available:
- The following node versions are now available:
- The following versions are no longer available:
- 1.31.11-gke.1036000
- 1.32.8-gke.1170000
- 1.33.4-gke.1172000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1008000
- 1.31 to 1.32.9-gke.1092000
- 1.32 to 1.33.4-gke.1350000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1008000
- 1.32 to 1.32.9-gke.1092000
- 1.33 to 1.33.4-gke.1350000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R44) Version updates
- Version 1.34.0-gke.2201000 is now the default version for cluster creation in the Rapid channel.
- The following versions are now available in the Rapid channel:
- The following versions are no longer available in the Rapid channel:
- 1.31.13-gke.1023000
- 1.32.9-gke.1108000
- 1.33.5-gke.1162000
- 1.34.1-gke.1293000
- 1.34.1-gke.1431000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1040000
- 1.31 to 1.32.9-gke.1130000
- 1.32 to 1.33.5-gke.1201000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1040000
- 1.32 to 1.32.9-gke.1130000
- 1.33 to 1.33.5-gke.1201000
- 1.34 to 1.34.0-gke.2201000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R44) Version updates
- Version 1.33.5-gke.1125000 is now the default version for cluster creation in the Regular channel.
- The following versions are now available in the Regular channel:
- The following versions are no longer available in the Regular channel:
- 1.31.12-gke.1265000
- 1.32.9-gke.1072000
- 1.33.5-gke.1080000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1008000
- 1.31 to 1.32.9-gke.1092000
- 1.32 to 1.33.5-gke.1125000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1008000
- 1.32 to 1.32.9-gke.1092000
- 1.33 to 1.33.5-gke.1125000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R44) Version updates
- Version 1.33.4-gke.1350000 is now the default version for cluster creation in the Stable channel.
- The following versions are now available in the Stable channel:
- The following versions are no longer available in the Stable channel:
- 1.31.11-gke.1036000
- 1.32.8-gke.1170000
- 1.33.4-gke.1245000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.12-gke.1220000
- 1.31 to 1.32.9-gke.1010000
- 1.32 to 1.33.4-gke.1350000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.12-gke.1220000
- 1.32 to 1.32.9-gke.1010000
- 1.33 to 1.33.4-gke.1350000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
CrowdStrike Falcon: Version 67.0
Fixed a bug where the Contains filter would fail to find hosts when the
Max Hosts To Returnlimit was applied in the following action:- List Host
SentinelOneV2: Version 42.0
The following new actions have been added:
Create Device Control Rule
Delete Device Control Rule
Update Device Control Rule
CSV: Version 34.0
Fixed a bug that caused inconsistent column order for the same JSON input by stabilizing the order based on the keys of the first object in the list in the following action:
- Save Json to CSV
DomainTools: Version 8.0
Extended capabilities in the following action:
- Get Domain Risk
Added support for the domain entity type in the following actions:
Get Domain Profile
Get Domain Risk
Reverse Domain
Integration of GTI score in Applied Threat Intelligence (ATI)
Google SecOps now uses Google Threat Intelligence (GTI) score for prioritization in Applied Threat Intelligence (ATI) instead of the IC-score. The GTI score delivers a unified verdict for potential Indicators of Compromise (IoCs) and aggregates a wealth of threat intelligence data.
For details, see Applied Threat Intelligence priority overview and Google Threat Intelligence (GTI) score overview.
CrowdStrike Falcon: Version 67.0
Fixed a bug where the Contains filter would fail to find hosts when the
Max Hosts To Returnlimit was applied in the following action:- List Host
SentinelOneV2: Version 42.0
The following new actions have been added:
Create Device Control Rule
Delete Device Control Rule
Update Device Control Rule
CSV: Version 34.0
Fixed a bug that caused inconsistent column order for the same JSON input by stabilizing the order based on the keys of the first object in the list in the following action:
- Save Json to CSV
DomainTools: Version 8.0
Extended capabilities in the following action:
- Get Domain Risk
Added support for the domain entity type in the following actions:
Get Domain Profile
Get Domain Risk
Reverse Domain
CrowdStrike Falcon: Version 67.0
Fixed a bug where the Contains filter would fail to find hosts when the
Max Hosts To Returnlimit was applied in the following action:- List Host
SentinelOneV2: Version 42.0
The following new actions have been added:
Create Device Control Rule
Delete Device Control Rule
Update Device Control Rule
CSV: Version 34.0
Fixed a bug that caused inconsistent column order for the same JSON input by stabilizing the order based on the keys of the first object in the list in the following action:
- Save Json to CSV
DomainTools: Version 8.0
Extended capabilities in the following action:
- Get Domain Risk
Added support for the domain entity type in the following actions:
Get Domain Profile
Get Domain Risk
Reverse Domain
We have implemented a security fix for CVE-2025-49844.
We have implemented a security fix for CVE-2025-49844.
The issue that caused IAM recommender role recommendations to be inaccurate and out of date is fixed.
reCAPTCHA Mobile SDK v18.8.1 is available for iOS. This version fixes an issue with iOS 26 screen time showing use from recaptcha.net
October 21, 2025
AI HypercomputerGenerally available: You can use future reservations in AI Hypercomputer to request to reserve capacity starting on a specific date up to one year in the future. For more information, see Reserve capacity.
- Change Block Tracking (CBT) support has been added for latest kernel versions in RHEL 8.10, 9.2, 9.4 and 9.6.
- Improved alerting for long-running jobs by adding application type and name to the alerts.
The following CVEs have been addressed in this release: CVE-2022-1471, CVE-2025-31651, CVE-2025-31650, CVE-2022-42003, CVE-2025-25193, CVE-2024-6763, CVE-2025-52999, CVE-2025-24970, CVE-2025-49125, CVE-2025-48734, CVE-2024-52317, CVE-2025-48988, CVE-2025-46701
- Resolved a problem with timestamp conversions during recovery range calculations in SAP HANA
- Fixed a bug that prevented the identification of persistent disk names in some SAP HANA environments
- Fixed DB2 restore issue wrt pre-flight checks and instances with a large number of archive logs
- Fixed a logging issue during Postgres upgrades where an incorrect version was displayed after a rollback
- Resolved a restore failure when using a combination of full and incremental backups for SAP ASE
- Fixed a connection leak and an issue with executor service shutdown in the VMware hypervisor integration, improving reliability.
BigQuery now supports TransUnion for entity resolution. This feature is generally available (GA).
Private NAT supports Cloud Run in General Availability. For more information, see Supported resources.
Support for configuring GPU for your Cloud Run job is in General Availability (GA).
Direct VPC egress now supports Private NAT (GA).
Cluster Toolkit version v1.69.0 is available. This release adds
NUMA-aware scheduling in GKE clusters for G4 machines and adds a new module that
provides mount scripts for WEKA filesystems. This version also includes PSA
updates and adds a GKE sample for running the nvidia-bug-report shell script. For details, see
the Release announcement on
GitHub.
Version 20251009.01 of the guest agent, announced in the October 20, 2025 release notes, has been rolled back. This version introduced the plugin-based architecture to Windows but contained a bug in the WSFC module.
To resolve this issue, guest agent version 20251011.00 is now available for Windows, which excludes the new plugin-based architecture.
As part of the consolidation of CIQ's kernel trees, the kernel dist-tag that supports the Rocky Linux Optimized and Accelerator images on Compute Engine is changing from elX_ycld_next to elX_y_ciq. There are no changes to Secure Boot or GPG signing keys.
For example, 6.12.0-55.32.1.el10_0cld_next.2.1 changes to 6.12.0-55.39.1.el10_0_ciq.2.1, where ciq replaces the cld_next tag.
This change affects the Rocky Linux 8, 9, and 10 optimized and accelerator images in an upcoming kernel update over the next month. The major version 8 and 9 kernels now include FIPS 140-3 patches as part of CIQ's ongoing FIPS 140-3 validation efforts for Rocky Linux. These patches have no effect if FIPS mode is not enabled. There are no code changes to the major version 10 kernel.
You can find the kernel source tree in the CIQ kernel-src-tree GitHub repository.
Generally available: Future reservations let you reserve capacity for a specific date up to one year in advance. For more information, see About future reservation requests.
Gemini Enterprise: Select individual connector instance
Select or deselect specific connector instances, such as Jira or Confluence, using the database icon located in the chat box.
On September 23, 2025, we discovered a technical issue in the Vertex AI API that resulted in a limited amount of responses being misrouted between recipients for certain third-party models when using streaming requests. This issue is now resolved. Google models, e.g. Gemini, were not impacted.
Some internal proxies did not properly handle HTTP requests that
have an Expect: 100-continue header, resulting in
a desynchronization in a streaming response connection, where
a response intended for one request was instead delivered as
the response for a subsequent request.
For more information, see Security bulletins.
The G4 VM, powered by NVIDIA's RTX PRO 6000 Blackwell Server Edition GPUs with the AMD EPYC Turin CPU platform, is generally available on GKE. G4 instances have up to 384 vCPUs, 1,440 GB of memory, 12 TiB of Titanium SSD disks attached, and up to 400 Gbps of standard network performance. The G4 VM offers a leap in performance with up to 9 times the throughput of G2 instances for workloads such as AI development, and graphics rendering. G4 VMs are currently available with 1, 2, 4, or 8 GPUs.
- For GKE Standard, use GKE version 1.34.0-gke.1662000 or later. To get started, see Run GPUs in GKE Standard node pools.
Premium Fortinet Firewall parser now available as Release Candidate
This enhanced parser is available as a Release Candidate for the next 2 months. To opt in and begin testing it, go to SIEM Settings > Parsers. We encourage you to try it out and evaluate the improvements before it becomes the default.
Premium Fortinet Firewall parser now available as Release Candidate
This enhanced parser is available as a Release Candidate for the next 2 months. To opt in and begin testing it, go to SIEM Settings > Parsers. We encourage you to try it out and evaluate the improvements before it becomes the default.
Version 20251009.01 of the guest agent, announced in the October 20, 2025 release notes, has been rolled back. This version introduced the plugin-based architecture to Windows but contained a bug in the WSFC module.
To resolve this issue, guest agent version 20251011.00 is now available for Windows, which excludes the new plugin-based architecture.
The new Looker Status Dashboard provides real-time updates about service availability or disruptions for Looker-hosted instances. For more information, see the Monitor Looker status documentation page.
You can now use self-service maintenance to update your instance to a newer version. This feature is Generally Available.
The release note for Security Command Center and attack path simulations, published on October 16, 2025, was updated to clarify that attack path simulations use Compute Engine and Google Kubernetes Engine OS and software vulnerability findings to detect toxic combinations and chokepoints.
Schema object drop protection is now generally available. This feature protects schema objects such as tables, indexes, and columns from accidental deletion.
Chirp 3: instant custom voice now supports voice cloning key generation in the eu and us regions. For more information, see the Chirp 3: instant custom voice page.
October 20, 2025
Agent AssistAgent Assist offers summarization automatic evaluation in GA. This feature assesses the quality of AI-generated summaries based on accuracy, completeness, and adherence. Summarization autoevaluation is available in the following regions:
- us-central1
- us-west1
- global
Support for TLS version 1.2 and later, along with a corresponding secure set of cipher suites, is in General Availability (GA).
Support for TLS version 1.2 and later, along with a corresponding secure set of cipher suites, is in General Availability (GA).
You can now use visualization cells to automatically generate a visualization of any DataFrame in your notebook. You can customize the columns, chart type, aggregations, colors , labels, and title.
This feature is in Preview.
In BigQuery ML, you can now fully manage open models as Vertex AI endpoints. BigQuery-managed open models offer the following benefits:
- Manage Vertex AI resource by using SQL queries
- Automatic or immediate open model undeployment to save costs
- Customize model deployment machine types or reserve open model resources by using Compute Engine reservations
This feature is in Preview.
You can save queries and then view and manage the saved queries in Bigtable Studio. This feature is in Preview.
Direct VPC egress now supports VPC Flow Logs (Preview).
Visualization cells
Preview: You can use visualization cells to generate interactive and editable visualizations from within a Colab Enterprise notebook. You can configure the chart type, aggregation, colors, labels, and other aspects of the visualization to help you explore data and discover insights. For more information, see Use visualization cells.
Version 20251009.01 of the guest agent, which introduces the plugin-based
architecture to Windows, is now available.
For more information about the plugin-based architecture, see Guest agent.
A vulnerability affecting AMD Zen 5 processors (Turin) is being addressed. For more information, see the GCP-2025-058 security bulletin.
Generally Available: The G4 accelerator-optimized machine series is designed for graphics-intensive workloads such as NVIDIA Omniverse simulations, video transcoding, and virtual desktops. The G4 machine series also provides a cost-effective solution for single-host inference and model tuning. The G4 machine series is available in the following regions and zones:
- APAC
- Jurong West, Singapore:
asia-southeast1-b
- Jurong West, Singapore:
- Europe
- Eemshaven, Netherlands:
europe-west4-a
- Eemshaven, Netherlands:
- North America
- Council Bluffs, Iowa:
us-central1-b - Ashburn, Virginia:
us-east4-c - Columbus, Ohio:
us-east5-c
- Council Bluffs, Iowa:
To get started with G4 machine types, see Create a G2 or G4 instance.
A vulnerability affecting AMD Zen 5 processors (Turin) was discovered and is being addressed. For more information, see the GCP-2025-058 security bulletin.
cos-117-18613-439-2
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.111 | v24.0.9 | v1.7.28 | See List |
This is an LTS Refresh release.
Reduced gcr_wait_online retry gap.
Added task information collection to sosreports.
Updated golang.org/x/crypto, golang.org/x/net, and golang.org/x/oauth2 in kubelet and kubectl.
Upgraded app-admin/google-guest-configs to v20250805.00.
Upgraded dev-lang/go to v1.23.12.
Upgraded sys-apps/gentoo-functions to v1.7.4.
Upgraded net-nds/rpcbind to v1.2.8.
Upgraded dev-libs/expat to v2.7.3.
Upgraded app-admin/sudo to v1.9.17_p2.
Upgraded dev-db/sqlite to v3.50.3.
Fixed CVE-2025-41244 in app-emulation/open-vm-tools.
Fixed KCTF-6bb73db in the Linux Kernel.
Fixed KCTF-cd8ae32 in the Linux kernel.
Fixed CVE-2025-39961 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811830 -> 811764
cos-121-18867-199-105
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.105 | v27.5.1 | v2.0.6 | See List |
Added task information collection to sosreports.
Updated golang.org/x/crypto, golang.org/x/net, and golang.org/x/oauth2 in kubelet and kubectl.
Fixed CVE-2025-39970 in the Linux kernel.
Fixed CVE-2025-39975 in the Linux kernel.
Fixed CVE-2025-39968 in the Linux kernel.
Fixed CVE-2025-39998 in the Linux kernel.
Fixed CVE-2025-39971 in the Linux kernel.
Fixed CVE-2025-39972 in the Linux kernel.
Fixed CVE-2025-39969 in the Linux kernel.
Fixed CVE-2025-39980 in the Linux kernel.
Fixed CVE-2025-39977 in the Linux kernel.
Fixed KCTF-6bb73db in the Linux Kernel.
Fixed CVE-2025-39961 in the Linux kernel.
Fixed KCTF-cd8ae32 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811792 -> 811798
cos-125-19216-0-100
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.46 | v27.5.1 | v2.1.3 | See List |
Fixed CVE-2025-39992 in the Linux kernel.
Fixed CVE-2025-39990 in the Linux kernel.
Fixed CVE-2025-39998 in the Linux kernel.
Fixed CVE-2025-38322 in the Linux kernel.
Fixed CVE-2025-39977 in the Linux kernel.
Fixed CVE-2025-39973 in the Linux kernel.
Fixed CVE-2025-39969 in the Linux kernel.
Fixed CVE-2025-39940 in the Linux kernel.
Fixed CVE-2025-39971 in the Linux kernel.
Fixed CVE-2025-39972 in the Linux kernel.
Fixed CVE-2025-39975 in the Linux kernel.
Fixed CVE-2025-39980 in the Linux kernel.
Fixed CVE-2025-39984 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811534 -> 811421
- Changed: net.ipv4.udp_mem: 188034 250715 376068 -> 188034 250714 376068
cos-dev-129-19326-0-0
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.53 | v27.5.1 | v2.1.3 | See List |
Updated the Linux kernel to v6.12.53.
Reduced gcr_wait_online retry gap.
Updated the dump capture kernel to v6.12.52.
Updated golang.org/x/crypto, golang.org/x/net, and golang.org/x/oauth2 in kubelet and kubectl.
Fixed KCTF-6bb73db in the Linux Kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811438 -> 811426
cos-113-18244-448-79
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.1.151 | v24.0.9 | v1.7.27 | See List |
Reduced gcr_wait_online retry gap.
Added task information collection to sosreports.
Fixed CVE-2025-41244 in app-emulation/open-vm-tools.
Fixed CVE-2025-39977 in the Linux kernel.
Fixed CVE-2025-39980 in the Linux kernel.
Fixed KCTF-6bb73db in the Linux Kernel.
New Dataproc on Compute Engine subminor image versions:
- 2.0.152-debian10, 2.0.152-ubuntu18, 2.0.152-rocky8
- 2.1.101-debian11, 2.1.101-ubuntu20, 2.1.101-ubuntu20-arm, 2.1.101-rocky8
- 2.2.69-debian12, 2.2.69-ubuntu22, 2.2.69-ubuntu22-arm, 2.2.69-rocky9
- 2.3.16-debian12, 2.3.16-ubuntu22, 2.3.16-ubuntu22-arm, 2.3.16-ml-ubuntu22, 2.3.16-rocky9
You can now create regional Filestore instances starting at 100 GiB and scale them in 1 GiB units. The small instances feature is available under Restricted GA in us-central1 and us-east4 regions.
For more information, see Small capacity Filestore instances.
Version 20251009.01 of the guest agent, which introduces the plugin-based
architecture to Windows, is now available.
For more information about the plugin-based architecture, see Guest agent.
Container image vulnerability findings has been released to General Availability.
You can now use the GoogleSQL ML.PREDICT function to convert your natural language query text into an embedding and perform approximate nearest neighbors (ANN) vector search.
VPC Flow Logs supports logging for Cloud Run resources that are configured with Direct VPC egress. This feature is available in General Availability.
For more information, see Serverless flows and ServerlessDetails field format.
October 19, 2025
Google SecOps SIEMRelease 6.3.64 is being rolled out to the first phase of regions as listed here.
This release contains internal and customer bug fixes.
Release 6.3.64 is being rolled out to the first phase of regions as listed here.
This release contains internal and customer bug fixes.
October 18, 2025
Compute EngineGenerally Available: You can use the Compute Engine alpha API at the project level through a self-service process. By enabling the alpha API, you can use the Google Cloud console, Google Cloud CLI, API, and Terraform to view and manage preview features. For more information, see Use the Compute Engine alpha API.
Release 6.3.63 is now available for all regions.
Release 6.3.63 is now available for all regions.
October 17, 2025
Cloud SQL for MySQLCloud SQL Enterprise edition now supports a new machine series called the N4 machine series. This machine series provides balanced price-to-performance and uses the Hyperdisk Balanced storage. You can create custom machine types for the N4 machine series with up to 80 vCPUs and up to 640 GB memory. The N4 machine series is generally available (GA).
For more information about the N4 machine series and its availability, see Machine series overview.
The C4A machine series is now generally available (GA).
The C4A machine series is supported for Cloud SQL Enterprise Plus edition instances, and provides optimized price-performance and delivers predictable high performance for high demand Cloud SQL workloads. It uses the Hyperdisk Balanced storage.
For more information about the C4A machine series and its availability, see Machine series overview.
Cloud SQL Enterprise edition now supports a new machine series called the N4 machine series. This machine series provides balanced price-to-performance and uses the Hyperdisk Balanced storage. You can create custom machine types for the N4 machine series with up to 80 vCPUs and up to 640 GB memory. The N4 machine series is generally available (GA).
For more information about the N4 machine series and its availability, see Machine series overview.
The C4A machine series is now generally available (GA).
The C4A machine series is supported for Cloud SQL Enterprise Plus edition instances, and provides optimized price-performance and delivers predictable high performance for high demand Cloud SQL workloads. It uses the Hyperdisk Balanced storage.
For more information about the C4A machine series and its availability, see Machine series overview.
Cloud SQL Enterprise edition now supports a new machine series called the N4 machine series. This machine series provides balanced price-to-performance and uses the Hyperdisk Balanced storage. You can create custom machine types for the N4 machine series with up to 80 vCPUs and up to 640 GB memory. The N4 machine series is generally available (GA).
For more information about the N4 machine series and its availability, see Machine series overview.
Generally Available: You can use the Compute Engine alpha API at the project level through a self-service process. By enabling the alpha API, you can use the Google Cloud console, Google Cloud CLI, API, and Terraform to view and manage preview features. For more information, see Use the Compute Engine alpha API.
cos-125-19216-0-94
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.46 | v27.5.1 | v2.1.3 | See List |
Updated the dump capture kernel to v6.12.52.
Added task information collection to sosreports.
Updated golang.org/x/crypto, golang.org/x/net, and golang.org/x/oauth2 in kubelet and kubectl.
Fixed CVE-2025-41244 in app-emulation/open-vm-tools.
Fixed KCTF-6bb73db in the Linux Kernel.
Fixed CVE-2025-39963 in the Linux kernel.
Fixed CVE-2025-39965 in the Linux kernel.
Fixed CVE-2025-39961 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811514 -> 811534
- Changed: net.ipv4.udp_mem: 188034 250714 376068 -> 188034 250715 376068
Layout parser lets you parse images and tables as annotations in Preview.
Layout parser can identify if there are images or tables in parsed documents. When found, images and tables are annotated as a descriptive block of text with the information depicted in the image and table.
Bug fixes in IntelliJ
Various bug fixes and minor product enhancements.
Don't use GKE version 1.34.1-gke.1431000 or later when creating
or upgrading node pools with the
a3-highgpu-8g machine
type. GKE nodes with these versions include COS Milestone 125,
which has an updated Linux kernel version that is incompatible with
GPUDirect-TCPX.
You can now create an instance in Memorystore for Valkey, even if a zone of the region where you want the instance to be created is unavailable. If this occurs, then Memorystore for Valkey creates the instance in the available zones of the region. This feature is Generally Available.
Customers with an organization-level activation of Security Command Center Premium have an organization-level discovery subscription at no charge from Sensitive Data Protection. For more information, see Sensitive data discovery in Security Command Center Premium.
Customers with an organization-level activation of Security Command Center Premium have an organization-level discovery subscription at no charge from Sensitive Data Protection. For more information, see Sensitive data discovery in Security Command Center Premium.
Chirp 3 HD now supports speech synthesis using SSML input. Supported SSML tags are: <phoneme>, <p>, <s>, <sub>, and <say-as>. For more information, see Chirp 3 HD: SSML support.
October 16, 2025
Apigee API hubCreate and manage API operations in the UI
You can now create and manage API operations for your API versions from the API details page in the Google Cloud console.
For more information, see Manage operations.
| Bug ID | Description |
|---|---|
| 440419558, 433759657 | Security fix for Apigee infrastructure. This addresses the following vulnerabilities: |
On October 16, 2025, we released an updated version of Apigee (1-16-0-apigee-3).
| Bug ID | Description |
|---|---|
| 442501403 | Fixed an issue that caused incorrect target latency metrics in Apigee Analytics when a TargetEndpoint is configured with a <LoadBalancer>. |
| 437999897 | Reduced the log level for failed geo IP lookups to address excessive log messages for private IP addresses. |
| 436323210 | Fixed ingress cert keys to allow both tls.key/key and tls.crt/cert. |
| 438192028 | Updated the geolocation database to mitigate stale IP-to-location mappings. |
| N/A | Updates to security infrastructure and libraries. |
The following features are now generally available (GA) in BigQuery Studio:
To streamline resource discovery and access, the left Explorer pane has been reorganized into three sections: Explorer, Classic Explorer, and Git repository. You can still use the Classic Explorer, which provides the complete resources tree.
In the Explorer pane, you can use the search feature to find BigQuery resources in your organization. The results appear in a new tab in the details pane. You can use filters to narrow your search.
You can access job histories by clicking Job history in the Explorer pane. A new tab opens that displays a list of job histories. BigQuery Studio no longer has a bottom pane for job history.
To reduce tab proliferation, clicking a resource opens it within the same tab. To open the resource in a separate tab, press Ctrl (or Command on macOS) and click the resource. To prevent the current tab from getting its content replaced, double-click the tab. The name changes from italicized to regular font. If you still lose your resource, you can click tab_recent Recent tabs in the details pane to find the resource.
You can use breadcrumbs to navigate through different tabs and resources in the details pane.
In the Home tab, the What's new section contains a list of new capabilities and changes to the BigQuery Studio.
The notebook action bar is consolidated by default to give you more screen space for writing code.
You can now access repositories by clicking Repositories in the Explorer pane. A new tab opens that displays a list of repositories. The Explorer pane no longer has a bottom pane for repositories. When you open a workspace in a repository, it opens in the Git repository pane in the left pane. These features are available in BigQuery Studio in preview.
The promotion of 1.21 to the Rapid release channel included upstream breaking changes to ExternalName and auto-sni when using the ISTIOD implementation. After considering the impact on customers, we have decided to restore the previous behavior from 1.20 and earlier for managed Cloud Service Mesh clusters using the ISTIOD implementation to match Rapid clusters using the TRAFFIC_DIRECTOR implementation. These changes are rolling out to the Rapid release channel in version 1.21.5-asm.55 or later.
If you are using an
ExternalNameservice in the Rapid channel without a port description, theExternalNameservice will not be translated intoClusterin the Envoy configuration. If theExternalNameservice is a destination ofVirtualServiceorExternalNameservice is used withREGISTRY_ONLYmode, you must specify the port in the service like in 1.20 and earlier.If you have an external service multiplexing traffic based on SNI but the corresponding
DestinationRuledoesn't have an explicit SNI, you must set SNI properly.
Starting with SUSE Linux Enterprise Server (SLES) 16, including variants for SAP, the default file system for the root partition (/) is Btrfs, which replaces the previous default of XFS. For more information, see File systems in SLES in the SUSE documentation.
Config Connector version 1.137.0 is now available.
New Fields:
BigtableMaterializedView: Addedspec.sourceTableRefandspec.definition.BackupDRBackupPlan: Addedspec.backupConfig.retentionPeriodDaysandspec.backupConfig.backupWindow.MemorystoreInstance: Added support forMEMCACHEandREDISinstance types.
Reconciliation Improvements:
- Enabled opt-in for IAM partial policy management.
- Enabled server-side apply for KMS resources.
- Improved reconciliation for
BigtableLogicalViewby using deep reflection. - Improved reconciliation for
FirestoreDatabasewith identity pattern and export support. - Improved reconciliation for
RunJobwith export support. - Unified
ComputeTargetTCPProxydirect API and controller.
Bug Fixes:
- Fixed an issue where
ComputeBackendServicebackends were not sorted. - Fixed an issue where
CloudFunctionsFunctionruntime was not a supported value. - Fixed an issue with labels for
BackupDRBackupPlan. - Fixed an issue with labels for
RunJob. - Fixed a fuzzing issue for
FirestoreField. - Fixed an issue with
KMSCryptoKeyimport. - Fixed a flakiness issue in the
MonitoringDashboardfuzzer. - Fixed a flakiness issue in tests.
- Fixed an issue with bad labels in tests.
- Fixed an issue with
etagin direct reconciliation.
New Alpha Resources (Direct Reconciler):
BigtableMaterializedView
New Beta Resources (Direct Reconciler):
DocumentAIProcessorVersionEssentialContactsContactBigQueryBigLakeTableBackupDRBackupPlan
New Serverless for Apache Spark runtime versions:
- 3.0.0-RC6
Dataproc on Compute Engine: The default image version of premium tier clusters is now 2.3.
Dialogflow CX (Conversational Agents): The Dialogflow CX console will be deprecated on October 31, 2025. After that date all users will be automatically routed to the Conversational Agents console.
Dialogflow CX (Conversational Agents): The default models for data stores and playbooks have been upgraded as follows:
Data stores
- Default voice mode summarization from
gemini-2.0-flash-lite-001togemini-2.5-flash-lite. - Default text mode summarization from
gemini-2.0-flash-001togemini-2.5-flash. - Default text mode rewriter from
gemini-2.0-flash-lite-001togemini-2.5-flash-lite.
- Default voice mode summarization from
Playbooks:
- All newly-created playbooks use default model
gemini-2.5-flash.
- All newly-created playbooks use default model
Bug fixes in VS Code
Various bug fixes and minor product enhancements.
vLLM TPU
vLLM TPU, a highly-efficient serving framework for large language models (LLM) that's optimized for Cloud TPU hardware, is available through Model Garden.
Mistral's Codestral 2
You can use Mistral's Codestral 2 in Model Garden.
Pro feature: Share and schedule reports with Slack
You can now send Looker Studio reports to Slack channels and Slack users on your Slack workspaces. This feature is only available to Looker Studio Pro users, and is available in Preview.
Vertical stacking in responsive reports
Responsive reports now support vertical stacking. You can add multiple components to a column within a section. Learn more about creating responsive reports.
Migrate to Virtual Machines now supports all available versions of AlmaLinux EL 8 and 9.
You can use Policy Troubleshooter to remediate access issues. This feature is available in Preview.
Security Command Center and attack path simulations use Compute Engine and Google Kubernetes Engine operating system and software vulnerabilities to detect toxic combinations and chokepoints.
UPDATE: Attack path simulations analyze OS and software vulnerability findings for Compute Engine and Google Kubernetes Engine resources to detect toxic combinations and chokepoints.
October 15, 2025
Backup and DRBackup and DR Service 11.0.16.253 is now available to update your backup/recovery appliances. Refer to these instructions to update your appliance.
- Guardrails have been defined for each backup/recovery appliance to specify the number of supported job slots, ensuring smooth parallel backup and mount jobs.
Introducing notifications and alerts for the following critical events:
- Processes not running on a backup/recovery appliance
- Expired certificates
- No jobs running on a backup/recovery appliance
- CPU and memory usage exceeding threshold values
- Backup/recovery appliance appliance version out of support
- Backup/recovery appliance updates available
You can subscribe to these events and configure email alerts.
You can visualize your geospatial query results on an interactive map in BigQuery Studio. This feature is generally available (GA).
You can use the dbt-bigquery adapter to run Python code that's defined in
BigQuery DataFrames. For more information, see
Use BigQuery DataFrames in dbt.
This feature is
generally available
(GA).
1.26.4-asm.7 is now available for in-cluster Cloud Service Mesh.
You can now download 1.26.4-asm.7 for in-cluster Cloud Service Mesh. It includes the features of Istio 1.26.4 subject to the list of supported features.
For details on upgrading Cloud Service Mesh, see Upgrade Cloud Service Mesh. Cloud Service Mesh version 1.26.4-asm.7 uses Envoy v1.34.8-dev.
1.26.4-asm.7 includes the fixes for the following CVEs:
| CVE | Proxy | Control Plane | CNI | Distroless |
|---|---|---|---|---|
| CVE-2024-10963 | Yes | Yes | Yes | - |
| CVE-2025-8058 | Yes | Yes | Yes | Yes |
| CVE-2025-4802 | - | - | - | Yes |
1.25.5-asm.7 includes the fixes for the following CVEs:
| CVE | Proxy | Control Plane | CNI | Distroless |
|---|---|---|---|---|
| CVE-2025-6297 | Yes | Yes | Yes | - |
| CVE-2024-10963 | Yes | Yes | Yes | - |
| CVE-2025-4802 | - | - | - | Yes |
| CVE-2025-8058 | Yes | Yes | Yes | Yes |
1.25.5-asm.7 is now available for in-cluster Cloud Service Mesh.
You can now download 1.25.5-asm.7 for in-cluster Cloud Service Mesh. It includes the features of Istio 1.25.5 subject to the list of supported features. Cloud Service Mesh version 1.25.5-asm.7 uses envoy v1.33.10-dev.
For details on upgrading Cloud Service Mesh, see Upgrade Cloud Service Mesh.
1.27.1-asm.5 includes the fixes for the following CVEs:
| CVE | Proxy | Control Plane | CNI | Distroless |
|---|---|---|---|---|
| CVE-2025-6297 | Yes | Yes | Yes | - |
| CVE-2024-10963 | Yes | Yes | Yes | - |
| CVE-2025-9230 | Yes | Yes | Yes | - |
| CVE-2025-8058 | Yes | Yes | Yes | Yes |
| CVE-2025-4802 | - | - | - | Yes |
1.27.1-asm.5 is now available for in-cluster Cloud Service Mesh.
You can now download 1.27.1-asm.5 for in-cluster Cloud Service Mesh. It includes the features of Istio 1.27.1 subject to the list of supported features.
For details on upgrading Cloud Service Mesh, see Upgrade Cloud Service Mesh. Cloud Service Mesh version 1.27.1-asm.5 uses Envoy v1.35.4-dev.
In-cluster Cloud Service Mesh 1.24 is no longer supported. For more information and to view the earliest end-of-life dates for other versions, see Supported versions.
Anthropic's Claude Haiku 4.5
You can use Anthropic's Claude Haiku 4.5 in Model Garden.
Veo video generation
Veo 2 supports adding and removing objects from videos in Preview.
For more information about Veo 2, see Veo 2 Preview
For more information about adding and removing objects, see the following:
Veo video generation
Veo 3.1 is available in Preview, and introduces the following models:
For more information, see the following:
Cloud Armor's Hierarchical security policies that facilitate centralized control, enhanced consistency, operational efficiency, and effective delegation of security policy management is Generally Available.
Mobile SDK patch 2.14.1 is released
This patch adds the didHandleUjetError function to the iOS SDK. The didHandleUjetError function can listen for and handle the following errors:
networkErrorauthenticationErrorauthenticationJwtErrorvoipConnectionErrorvoipLibraryNotFoundchatLibraryNotFound
For more information, see Fallback.
Google Distributed Cloud (software only) for VMware 1.31.1000-gke.44 is available for download. To upgrade, see Upgrade a cluster. Distributed Cloud 1.31.1000-gke.44 runs on Kubernetes v1.31.12-gke.600.
If you are using a third-party storage vendor, check the GDC Ready storage partners document to make sure the storage vendor has already passed the qualification for this release.
After a release, it takes approximately 7 to 14 days for the version to become available for use with GKE On-Prem API clients: the Google Cloud console, the gcloud CLI, and Terraform.
The following issues were fixed in 1.31.1000-gke.44:
- Fixed vulnerabilities listed in Vulnerability fixes.
For information about the latest known issues, see Google Distributed Cloud for bare metal known issues in the Troubleshooting section.
Google Distributed Cloud for bare metal 1.31.1000-gke.44 is now available for download. To upgrade, see Upgrade clusters. Distributed Cloud for bare metal 1.31.1000-gke.44 runs on Kubernetes v1.31.12-gke.600.
After a release, it takes approximately 7 to 14 days for the version to become available for installations or upgrades with the GKE On-Prem API clients: the Google Cloud console, the gcloud CLI, and Terraform.
If you use a third-party storage vendor, check the Ready storage partners document to make sure the storage vendor has already passed the qualification for this release of Distributed Cloud for bare metal.
The following issues were fixed in 1.31.1000-gke.44:
Fixed an issue where the cluster restore process leaves the Kubelet certificate files as regular files instead of symbolic links, preventing certificate rotation.
Fixed the
etcd-cleanupjob timeout issue caused by the use of incorrect certificates.Fixed vulnerabilities listed in Vulnerability fixes.
(2025-R43) Version updates
GKE cluster versions have been updated.
New versions available for upgrades and new clusters.
The following versions are now available for new GKE clusters, and for manual control plane upgrades and node upgrades for existing clusters. For more information about versioning and upgrades, see GKE versioning and support and About GKE cluster upgrades.
Rapid channel
- Version 1.34.1-gke.1293000 is now the default version for cluster creation in the Rapid channel.
- The following versions are now available in the Rapid channel:
- The following versions are no longer available in the Rapid channel:
- 1.31.12-gke.1265000
- 1.31.13-gke.1008000
- 1.32.9-gke.1072000
- 1.32.9-gke.1092000
- 1.33.5-gke.1080000
- 1.33.5-gke.1125000
- 1.34.0-gke.2201000
- 1.34.1-gke.1127000
- 1.34.1-gke.1279000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1023000
- 1.31 to 1.32.9-gke.1108000
- 1.32 to 1.33.5-gke.1162000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1023000
- 1.32 to 1.32.9-gke.1108000
- 1.33 to 1.33.5-gke.1162000
- 1.34 to 1.34.1-gke.1293000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Regular channel
- Version 1.33.5-gke.1080000 is now the default version for cluster creation in the Regular channel.
- The following versions are now available in the Regular channel:
- The following versions are no longer available in the Regular channel:
- 1.31.12-gke.1220000
- 1.32.9-gke.1010000
- 1.33.4-gke.1350000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.12-gke.1265000
- 1.31 to 1.32.9-gke.1072000
- 1.32 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.12-gke.1265000
- 1.32 to 1.32.9-gke.1072000
- 1.33 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Stable channel
- Version 1.33.4-gke.1245000 is now the default version for cluster creation in the Stable channel.
- The following versions are now available in the Stable channel:
- The following versions are no longer available in the Stable channel:
- 1.32.8-gke.1134000
- 1.33.4-gke.1172000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.31 to 1.32.8-gke.1170000
- 1.32 to 1.33.4-gke.1245000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.32 to 1.32.8-gke.1170000
- 1.33 to 1.33.4-gke.1245000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Extended channel
- Version 1.33.5-gke.1080000 is now the default version for cluster creation in the Extended channel.
- The following versions are now available in the Extended channel:
- The following versions are no longer available in the Extended channel:
- 1.28.15-gke.2697000
- 1.28.15-gke.2751000
- 1.29.15-gke.1936000
- 1.29.15-gke.1989000
- 1.30.14-gke.1336000
- 1.31.12-gke.1220000
- 1.32.9-gke.1010000
- 1.33.4-gke.1350000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.27 to 1.28.15-gke.2730000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.28 to 1.28.15-gke.2730000
- 1.29 to 1.29.15-gke.1971000
- 1.31 to 1.31.12-gke.1265000
- 1.32 to 1.32.9-gke.1072000
- 1.33 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
No channel
- Version 1.33.5-gke.1080000 is now the default version for cluster creation.
- The following versions are now available:
- The following node versions are now available:
- The following versions are no longer available:
- 1.32.8-gke.1134000
- 1.33.4-gke.1134000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.12-gke.1265000
- 1.31 to 1.32.9-gke.1072000
- 1.32 to 1.33.4-gke.1245000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.12-gke.1265000
- 1.32 to 1.32.9-gke.1072000
- 1.33 to 1.33.4-gke.1245000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R43) Security updates
This release includes new GKE versions that use updated Container-Optimized OS images. These updated images are cumulative, incorporating security fixes from all Container-Optimized OS versions released since the previous GKE release.
To identify the specific vulnerabilities that were resolved in each updated Container-Optimized OS image, see the Security release notes for that image. The following table includes links to the release notes for each updated Container-Optimized OS image:
| GKE version | Container-Optimized OS version | Details |
|---|---|---|
| 1.34.1-gke.1431000 | cos-beta-125-19216-0-76 | cos-beta-125-19216-0-76 release notes |
(2025-R43) Version updates
- Version 1.33.5-gke.1080000 is now the default version for cluster creation in the Extended channel.
- The following versions are now available in the Extended channel:
- The following versions are no longer available in the Extended channel:
- 1.28.15-gke.2697000
- 1.28.15-gke.2751000
- 1.29.15-gke.1936000
- 1.29.15-gke.1989000
- 1.30.14-gke.1336000
- 1.31.12-gke.1220000
- 1.32.9-gke.1010000
- 1.33.4-gke.1350000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.27 to 1.28.15-gke.2730000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.28 to 1.28.15-gke.2730000
- 1.29 to 1.29.15-gke.1971000
- 1.31 to 1.31.12-gke.1265000
- 1.32 to 1.32.9-gke.1072000
- 1.33 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R43) Version updates
- Version 1.33.5-gke.1080000 is now the default version for cluster creation.
- The following versions are now available:
- The following node versions are now available:
- The following versions are no longer available:
- 1.32.8-gke.1134000
- 1.33.4-gke.1134000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.12-gke.1265000
- 1.31 to 1.32.9-gke.1072000
- 1.32 to 1.33.4-gke.1245000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.12-gke.1265000
- 1.32 to 1.32.9-gke.1072000
- 1.33 to 1.33.4-gke.1245000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R43) Version updates
- Version 1.34.1-gke.1293000 is now the default version for cluster creation in the Rapid channel.
- The following versions are now available in the Rapid channel:
- The following versions are no longer available in the Rapid channel:
- 1.31.12-gke.1265000
- 1.31.13-gke.1008000
- 1.32.9-gke.1072000
- 1.32.9-gke.1092000
- 1.33.5-gke.1080000
- 1.33.5-gke.1125000
- 1.34.0-gke.2201000
- 1.34.1-gke.1127000
- 1.34.1-gke.1279000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.13-gke.1023000
- 1.31 to 1.32.9-gke.1108000
- 1.32 to 1.33.5-gke.1162000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.13-gke.1023000
- 1.32 to 1.32.9-gke.1108000
- 1.33 to 1.33.5-gke.1162000
- 1.34 to 1.34.1-gke.1293000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R43) Version updates
- Version 1.33.5-gke.1080000 is now the default version for cluster creation in the Regular channel.
- The following versions are now available in the Regular channel:
- The following versions are no longer available in the Regular channel:
- 1.31.12-gke.1220000
- 1.32.9-gke.1010000
- 1.33.4-gke.1350000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.12-gke.1265000
- 1.31 to 1.32.9-gke.1072000
- 1.32 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.12-gke.1265000
- 1.32 to 1.32.9-gke.1072000
- 1.33 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R43) Version updates
- Version 1.33.4-gke.1245000 is now the default version for cluster creation in the Stable channel.
- The following versions are now available in the Stable channel:
- The following versions are no longer available in the Stable channel:
- 1.32.8-gke.1134000
- 1.33.4-gke.1172000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.31 to 1.32.8-gke.1170000
- 1.32 to 1.33.4-gke.1245000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.32 to 1.32.8-gke.1170000
- 1.33 to 1.33.4-gke.1245000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
The Netskope v1 API feed has been deprecated by Netskope. If you are using the Netskope REST API v1 with Google SecOps, you must switch to the Netskope REST API v2.
Microsoft Teams: Version 30.0
- Integration: Fixed an issue with the special characters in the query parameters.
Okta: Version 10.0
Updated the pagination processing mechanism in the following actions:
List Users
Add Group
Get Group
List Providers
CrowdStrike Falcon: Version 66.0
Updated entity processing logic in the following actions:
Contain Endpoint
Download File
Execute Command
Get Host Information
Lift Contained Endpoint
List Host Vulnerabilities
On-Demand Scan
Run Script
Azure Active Directory: Version 19.0
Improved performance by implementing a direct API filter query for group name searches, which avoids fetching all groups and significantly reduces execution time in large-group environments, in the following action:
- List Members in Group
Updated dependencies in the following integrations:
Microsoft Teams: Version 30.0
Microsoft Graph Mail Delegated: Version 8.0
Exchange: Version 114.0
Case Federation: Version 5.0
Azure Security Center: Version 12.0
UrlScan.io: Version 26.0
Added ability to scan domains and IPs in the following action:
- URL Check
ThreatQ: Version 15.0
Updated the API request payload to align with a change in the ThreatQ API in the following actions:
Enrich IP
Enrich URL
Enrich Email
Enrich Hash
Enrich CVE
CrowdStrike Falcon: Version 66.0
The following new action has been added:
- Get Alert Details
Microsoft Teams: Version 30.0
- Integration: Fixed an issue with the special characters in the query parameters.
Okta: Version 10.0
Updated the pagination processing mechanism in the following actions:
List Users
Add Group
Get Group
List Providers
CrowdStrike Falcon: Version 66.0
Updated entity processing logic in the following actions:
Contain Endpoint
Download File
Execute Command
Get Host Information
Lift Contained Endpoint
List Host Vulnerabilities
On-Demand Scan
Run Script
Azure Active Directory: Version 19.0
Improved performance by implementing a direct API filter query for group name searches, which avoids fetching all groups and significantly reduces execution time in large-group environments, in the following action:
- List Members in Group
Updated dependencies in the following integrations:
Microsoft Teams: Version 30.0
Microsoft Graph Mail Delegated: Version 8.0
Exchange: Version 114.0
Case Federation: Version 5.0
Azure Security Center: Version 12.0
UrlScan.io: Version 26.0
Added ability to scan domains and IPs in the following action:
- URL Check
ThreatQ: Version 15.0
Updated the API request payload to align with a change in the ThreatQ API in the following actions:
Enrich IP
Enrich URL
Enrich Email
Enrich Hash
Enrich CVE
CrowdStrike Falcon: Version 66.0
The following new action has been added:
- Get Alert Details
The Netskope v1 API feed has been deprecated by Netskope. If you are using the Netskope REST API v1 with Google SecOps, you must switch to the Netskope REST API v2.
The Netskope v1 API feed has been deprecated by Netskope. If you are using the Netskope REST API v1 with Google SecOps, you must switch to the Netskope REST API v2.
Microsoft Teams: Version 30.0
- Integration: Fixed an issue with the special characters in the query parameters.
Okta: Version 10.0
Updated the pagination processing mechanism in the following actions:
List Users
Add Group
Get Group
List Providers
CrowdStrike Falcon: Version 66.0
Updated entity processing logic in the following actions:
Contain Endpoint
Download File
Execute Command
Get Host Information
Lift Contained Endpoint
List Host Vulnerabilities
On-Demand Scan
Run Script
Azure Active Directory: Version 19.0
Improved performance by implementing a direct API filter query for group name searches, which avoids fetching all groups and significantly reduces execution time in large-group environments, in the following action:
- List Members in Group
Updated dependencies in the following integrations:
Microsoft Teams: Version 30.0
Microsoft Graph Mail Delegated: Version 8.0
Exchange: Version 114.0
Case Federation: Version 5.0
Azure Security Center: Version 12.0
UrlScan.io: Version 26.0
Added ability to scan domains and IPs in the following action:
- URL Check
ThreatQ: Version 15.0
Updated the API request payload to align with a change in the ThreatQ API in the following actions:
Enrich IP
Enrich URL
Enrich Email
Enrich Hash
Enrich CVE
CrowdStrike Falcon: Version 66.0
The following new action has been added:
- Get Alert Details
The following features in Compliance Manager are available in General Availability:
- Applying and updating built-in frameworks and cloud controls
- Creating, applying, and editing custom frameworks and cloud controls
- Support for VPC Service Control perimeters
- Audit logging
- Client libraries
- REST APIs
Private Service Connect health is available in Preview.
Private Service Connect health lets service producers define health states to support automatic cross-region failover for consumers that use Private Service Connect backends. For more information, see About Private Service Connect health for automatic cross-region failover.
October 14, 2025
Access ApprovalGoogle Cloud Managed Service for Apache Kafka is generally available (GA).
Google Cloud Managed Service for Apache Kafka is generally available (GA).
New MCP API style system attribute
The system-defined API style attribute now includes a new value: MCP. This lets you classify and govern APIs based on the latest Model Context Protocol (MCP) standards.
For more information, see System attributes.
Removal of deprecated Gemini Code Assist @Apigee tool.
The Gemini Code Assist @Apigee tool is shut down as of October 14, 2025.
See Gemini Code Assist @Apigee tool deprecation for information.
You can now set up backup vault specific workload quotas for critical resources like data sources, backups, backup plans, and backup plan associations. Until now these quotas were set up only at the project level, not at the workload level.
You can now embed natural language as comments in existing SQL to refine and transform your code. This feature is preview.
The BigQuery Data Transfer API (bigquerydatatransfer.googleapis.com) is now enabled by default for every new Google Cloud project. This feature is generally available (GA).
You can now use SQL cells to write, edit, and run SQL queries on your BigQuery data directly from your notebooks. This feature is in Preview.
SQL cells
Preview: You can use SQL cells to write, edit, and run SQL queries directly from your Colab Enterprise notebooks. For more information, see Use SQL cells.
New Dataproc on Compute Engine subminor image versions:
- 2.0.151-debian10, 2.0.151-ubuntu18, 2.0.151-rocky8
- 2.1.100-debian11, 2.1.100-ubuntu20, 2.1.100-ubuntu20-arm, 2.1.100-rocky8
- 2.2.68-debian12, 2.2.68-ubuntu22, 2.2.68-ubuntu22-arm, 2.2.68-rocky9
- 2.3.15-debian12, 2.3.15-ubuntu22, 2.3.15-ubuntu22-arm, 2.3.15-ml-ubuntu22, 2.3.15-rocky9
Fixed startup race condition in multi-tenant clusters using the dataproc:pip.packages property that could cause authentication failures while starting Jupyter notebook kernels.
Gemini Code Assist tools are no longer available and are replaced by agent mode (Preview)
Effective October 14, 2025, Gemini Code Assist tools are no longer available. This completes the deprecation process that was announced on October 2, 2025.
Using the @ symbol followed by the name of a tool no longer connects to
Gemini Code Assist tools.
To connect to external services, use Model Context Protocol (MCP) servers in Gemini Code Assist agent mode.
For more information, see:
Gemini Code Assist tools are no longer available and are replaced by agent mode (Preview)
Effective October 14, 2025, Gemini Code Assist tools are no longer available. This completes the deprecation process that was announced on October 2, 2025.
Using the @ symbol followed by the name of a tool no longer connects to
Gemini Code Assist tools.
To connect to external services, use Model Context Protocol (MCP) servers in Gemini Code Assist agent mode.
For more information, see:
Imagen 4 preview models
The following Imagen 4 preview models will be removed on
November 30, 2025 :
imagen-4.0-generate-preview-06-06,
imagen-4.0-ultra-generate-preview-06-06, and
imagen-4.0-fast-generate-preview-06-06. To avoid service
disruption, migrate all workflows that use Imagen 4 preview models before
November 30, 2025 , 2025, to the following Imagen 4 Generally
Available models: imagen-4.0-generate-001,
imagen-4.0-ultra-generate-001,
imagen-4.0-fast-generate-001.
Imagen subject and style fine-tuning
Imagen subject model and style model tuning will be removed on December 31, 2025. We recommend that you use Gemini 2.5 Flash Image, which supports most use cases that require fine-tuning. For more information, see Edit images with Gemini.
In GKE versions 1.32.4-gke.1029000 and later, MountVolume calls
for network file system (NFS) volumes might fail with the following error:
mount.nfs:rpc.statd is not running but is required for remote locking.
This failure can occur if a Pod mounting an NFS volume runs on the same node as
an NFS server Pod, and the NFS server Pod starts before the client Pod attempts
to mount the volume. This scenario causes a conflict over the rpcbind service,
which prevents the service from starting correctly on the node for the client
Pod, leading to the mount failure.
As a workaround, deploy this DaemonSet on all nodes where you mount the NFS volumes. The DaemonSet ensures that the required services start correctly.
You can use custom constraints with Organization Policy to provide more granular control over specific fields for some Datastream resources. For more information, see Create custom organization policy constraints. This feature is generally available (GA).
October 13, 2025
Access ApprovalIAM System for Cross-domain Identity Management (SCIM) Service is available in Preview.
IAM System for Cross-domain Identity Management (SCIM) Service is available in Preview.
A weekly digest of client library updates from across the Cloud SDK.
Java
Changes for google-cloud-bigtable
2.67.1 (2025-10-08)
Dependencies
Python
Changes for google-cloud-bigtable
2.33.0 (2025-10-06)
Features
- Add support for Proto and Enum types (#1202) (34ceb86)
- Expose universe_domain for tpc (#1150) (451fd97)
Bug Fixes
A weekly digest of client library updates from across the Cloud SDK.
Node.js
Changes for @google-cloud/storage
7.17.2 (2025-10-06)
Bug Fixes
Java
Changes for google-cloud-storage
2.58.1 (2025-10-06)
Bug Fixes
- deps: Update the Java code generator (gapic-generator-java) to 2.62.3 (ba84793)
- Update BlobReadSession ScatteringByteChannel projection to use less CPU (#3324) (678fecc)
- Update DefaultRetryContext to trap and forward RejectedExceptionException to onFailure (#3327) (1be31bd)
- Update PCU request building logic to properly clear crc32c and md5 (#3323) (4da9f31)
Dependencies
Python
Changes for google-cloud-storage
3.4.1 (2025-10-08)
Bug Fixes
cos-dev-129-19319-0-0
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.50 | v27.5.1 | v2.1.3 | See List |
Updated the Linux kernel to v6.12.50.
Added support for NVIDIA driver v580.95.05. Updated all latest driver version and default driver versions for NVIDIA_GB200 and NVIDIA_B200 to v580.95.05.
Upgraded app-containers/docker-credential-helpers to v0.9.4.
Updated toolbox container image tag to v20251002.
Upgraded chromeos-base/google-breakpad to v2025.10.06.205107-r254.
Upgraded dev-libs/expat to v2.7.3.
Upgraded sys-apps/hwdata to v0.399.
Upgraded net-libs/libtirpc to v1.3.7.
Partially fixed an issue where excessive contention among writeback kworkers when switching a large number of inodes between cgroups could lead to system unresponsiveness.
Upgraded open-vm-tools to 13.0.5. This fixes CVE-2025-41244 in anthos variant.
Fixed CVE-2025-11081, CVE-2025-11082 and CVE-2025-11083 in sys-libs/binutils-libs.
Updated dev-python/urllib3 to v2.5.0. This resolves CVE-2025-50181.
Updated sys-apps/coreutils to v9.5. This resolves CVE-2024-0684.
Fixed KCTF-134121b in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811493 -> 811438
- Changed: net.ipv4.udp_mem: 188034 250714 376068 -> 188034 250715 376068
cos-121-18867-199-98
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.105 | v27.5.1 | v2.0.6 | See List |
Added support for NVIDIA driver v580.95.05. Updated all latest driver version and default driver versions for NVIDIA_GB200 and NVIDIA_B200 to v580.95.05.
Upgraded app-admin/node-problem-detector to v0.8.22.
Updated toolbox container image tag to v20251002.
Upgraded sys-apps/hwdata to v0.399.
Partially fixed an issue where excessive contention among writeback kworkers when switching a large number of inodes between cgroups could lead to system unresponsiveness.
Fixed CVE-2025-41244 in app-emulation/open-vm-tools in anthos variant.
Fixed CVE-2025-11081, CVE-2025-11082 and CVE-2025-11083 in sys-libs/binutils-libs.
Fixed CVE-2025-23143 in the Linux kernel.
Fixed CVE-2025-39947 in the Linux kernel.
Fixed KCTF-134121b in the Linux kernel.
Fixed CVE-2025-39931 in the Linux kernel.
Fixed CVE-2025-39953 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811724 -> 811792
cos-125-19216-0-87
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.46 | v27.5.1 | v2.1.3 | See List |
Added support for NVIDIA driver v580.95.05. Updated all latest driver version and default driver versions for NVIDIA_GB200 and NVIDIA_B200 to v580.95.05.
Upgraded app-admin/node-problem-detector to v0.8.22.
Upgraded sys-apps/hwdata to v0.399.
Partially fixed an issue where excessive contention among writeback kworkers when switching a large number of inodes between cgroups could lead to system unresponsiveness.
Fixed CVE-2025-11081, CVE-2025-11082 and CVE-2025-11083 in sys-libs/binutils-libs.
Fixed CVE-2025-39931 in the Linux kernel.
Fixed CVE-2025-39953 in the Linux kernel.
Fixed CVE-2025-39947 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811500 -> 811514
cos-113-18244-448-73
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.1.151 | v24.0.9 | v1.7.27 | See List |
Updated toolbox container image tag to v20251002.
Upgraded sys-apps/hwdata to v0.399.
Fixed CVE-2025-11081, CVE-2025-11082 and CVE-2025-11083 in sys-libs/binutils-libs.
Fixed CVE-2025-23143 in the Linux kernel.
Fixed KCTF-134121b in the Linux kernel.
Fixed CVE-2025-39931 in the Linux kernel.
Fixed CVE-2025-39953 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811950 -> 812035
cos-117-18613-339-97
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.105 | v24.0.9 | v1.7.28 | See List |
Added support for NVIDIA driver v580.95.05. Updated all latest driver version and default driver versions for NVIDIA_GB200 and NVIDIA_B200 to v580.95.05.
Upgraded app-admin/node-problem-detector to v0.8.22.
Fixed CVE-2025-11081, CVE-2025-11082 and CVE-2025-11083 in sys-libs/binutils-libs.
Fixed CVE-2025-23143 in the Linux kernel.
Fixed CVE-2025-39947 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811755 -> 811830
Serverless for Apache Spark: Runtimes rollout with Apache Spark upgrade to version 3.5.3 in the latest 1.2 and 2.2 Serverless for Apache Spark runtime versions has started and is expected to finish by October 16th.
Enterprise version of Gemini Code Assist on GitHub (Preview)
Gemini Code Assist on GitHub provides Gemini-powered reviews of pull requests in your GitHub repositories.
The enterprise version enables consolidated control of Gemini Code Assist reviews across multiple repositories, provides increased quotas, supports GitHub Enterprise Cloud and GitHub Enterprise Server, and operates under the Google Cloud Terms of Service.
Enterprise version of Gemini Code Assist on GitHub (Preview)
Gemini Code Assist on GitHub provides Gemini-powered reviews of pull requests in your GitHub repositories.
The enterprise version enables consolidated control of Gemini Code Assist reviews across multiple repositories, provides increased quotas, supports GitHub Enterprise Cloud and GitHub Enterprise Server, and operates under the Google Cloud Terms of Service.
Google Cloud Managed Lustre now fully supports data transfers to and from Cloud Storage buckets that have Object Lifecycle Management (OLM) or Autoclass enabled.
Due to an ongoing issue, IAM recommender role recommendations might be out of date and inaccurate. Removing roles or permissions can break existing processes. Therefore, please validate usage before applying any changes.
A weekly digest of client library updates from across the Cloud SDK.
Java
Changes for google-cloud-pubsub
1.142.0 (2025-10-07)
Features
- Support the protocol version in StreamingPullRequest (af40810)
Bug Fixes
- deps: Update the Java code generator (gapic-generator-java) to 2.62.3 (af40810)
Dependencies
- Update actions/checkout action to v5 (#2562) (b7fa499)
- Update actions/checkout action to v5 (#2573) (4153dba)
- Update dependency com.google.cloud:google-cloud-bigquery to v2.55.1 (#2566) (66c9ec4)
- Update dependency com.google.cloud:google-cloud-core to v2.60.2 (#2557) (460bcd9)
- Update dependency com.google.cloud:google-cloud-core to v2.60.3 (#2571) (ac2c85a)
- Update dependency com.google.cloud:google-cloud-storage to v2.58.0 (#2561) (0189388)
- Update dependency com.google.cloud:sdk-platform-java-config to v3.52.3 (#2572) (0785ee4)
- Update dependency org.assertj:assertj-core to v3.27.6 (#2560) (c82766a)
For more information, see Synchronize secrets to Kubernetes Secrets.
Speech-to-Text is excited to announce the General Availability (GA) of the Chirp 3: Transcription, the latest generation of Google's multilingual Automatic Speech Recognition (ASR)-specific generative model, delivering state-of-the-art ASR accuracy and multilingual capabilities. Available exclusively in the Speech-to-Text API V2, Chirp 3 delivers significant enhancements in transcription accuracy and speed over previous versions.
Under the new chirp_3 model identifier, you can now leverage powerful new capabilities, including speaker diarization to identify different speakers and automatic language detection for multilingual audio. The model supports all major recognition methods —StreamingRecognize, Recognize, and BatchRecognize- making it suitable for both real-time and batch processing. Chirp 3 also offers advanced features such as speech adaptation for custom vocabularies and a built-in denoiser to improve results from noisy audio.
To explore the new Chirp 3: Transcription model's capabilities and learn how to leverage its full potential, please visit our updated documentation page.
October 12, 2025
Apigee hybridRecurring, top-up, and setup fees for Apigee hybrid monetization
Apigee hybrid now supports recurring, top-up, and setup fees for monetization. For information see Enabling monetization for Apigee hybrid.
hybrid v1.15.1
On October 10, 2025 we released an updated version of the Apigee hybrid software, 1.15.1.
- For information on upgrading, see Upgrading Apigee hybrid to version 1.15.
- For information on new installations, see The big picture.
Apigee policies for LLM/GenAI workloads
Apigee hybrid now supports the following Apigee policies with support for LLM/GenAI workloads.
The Apigee semantic caching policies enable intelligent response reuse based on semantic similarity. Using these policies in your Apigee API proxies can minimize redundant backend API calls, reduce latency, and lower operational costs. With this release, the semantic caching policies support URL templating, enabling the use of variables for AI model endpoint values.
The Model Armor policies protect your AI applications by sanitizing user prompts to and responses from large language models (LLMs). Using these policies in your Apigee API proxies can mitigate the risks associated with LLM usage by leveraging Model Armor to detect prompt injection, prevent jailbreak attacks, apply responsible AI filters, filter malicious URLs, and protect sensitive data.
For more information on using these policies in your Apigee API proxies, see:
| Bug ID | Description |
|---|---|
| 451841788 | Apigee hybrid required the mintTaskScheduler.serviceAccountPath property even when Monetization was not enabled. |
| 451375397 | The apigee-pull-push.sh script could return a "No such image error" message. |
| 445912919 | Unused files and folders have been removed from the Apigee hybrid Helm charts to prevent potential security exposure and streamline the product installation and upgrade process. |
| 442501403 | Fixed an issue that caused incorrect target latency metrics in Apigee Analytics when a TargetEndpoint is configured with a <LoadBalancer>. |
| 437999897 | Reduced the log level for failed geo IP lookups to address excessive log messages for private IP addresses. |
| 431930277, 395272878 | When the configuration property envs.managementCallsSkipProxy is set to true via helm for environment-level forward proxy, trace and analytics (which use googleapis.com) will skip forward proxy. |
| 423597917 | Post of an AppGroupAppKey scopes should result in insert operation instead of update. |
| 420675540 | Fixed Cassandra based replication for runtime contracts in synchronizer. |
| 419578402 | Mint-Mart forward proxy compatible. |
| 416634326 | Presence of istio.io Custom Resource Definitions (CRDs) in an Apigee hybrid cluster could cause failure in apigee-ingressgateway-manager pods. |
| 412740465 | Fixed issue where zipkin headers were not generated by Apigee Ingress Gateway. |
| 409048431 | Fixes a vulnerability which could allow a SAML signature verification to be bypassed. |
| 378686709 | The use of wildcards (*) in Apigee proxy basepaths would conflict with other explicit basepaths, resulting in a 404 error. To apply this fix, follow the procedure in Known issue 378686709. |
| 367815792 | Two new Flow Variables: app_group_app and app_group_name have been added to VerifyApiKey and Access Token policy. |
| Bug ID | Description |
|---|---|
| 448498138 | Security fixes for apigee-runtime. This addresses the following vulnerability: |
| 447367372 | Security fixes for apigee-runtime. This addresses the following vulnerability: |
| 418557195 | Security fixes for apigee-fluent-bit. This addresses the following vulnerabilities: |
| N/A | Security fixes for apigee-fluent-bit. This addresses the following vulnerabilities: |
| N/A | Security fixes for apigee-hybrid-cassandra. This addresses the following vulnerability: |
| N/A | Security fixes for apigee-mart-server. This addresses the following vulnerabilities: |
| N/A | Security fixes for apigee-stackdriver-logging-agent. This addresses the following vulnerabilities:
|
Documentation change
The following documents have been changed or introduced to align the Apigee hybrid installation guides with the supported methods for service account authentication:
- Service account authentication methods in Apigee hybrid - A new overview topic for service account authentication.
- Storing service account keys in Kubernetes secrets - A new topic.
- Step 4: Create service accounts - Rewritten to accommodate all supported methods of service account authentication.
- Step 5: Set up service account authentication - A new topic on configuring authentication after creating service accounts.
- Step 7: Create the overrides and Step 11: Install Apigee hybrid Using Helm - Topics revised to provide templates, examples, and procedures for each supported type of service account authentication.
- Step 11(Optional): Configure Workload Identity - Topic removed. The procedures are included in Step 11: Install Apigee hybrid Using Helm: WIF for GKE
October 10, 2025
Application IntegrationManage Application Integration resources using custom constraints
You can now use custom constraints with Organization Policy to provide more granular control over specific fields for some Application Integration resources. For more information, see Manage Application Integration resources using custom constraints. This feature is now available in Preview.
The following Cloud Composer versions and builds have reached their end of support period: composer-2.9.6-*, composer-3-airflow-2.7.3-build.17, composer-3-airflow-2.7.3-build.18, composer-3-airflow-2.9.1-build.8, and composer-3-airflow-2.9.1-build.9.
New images are available in Cloud Composer 2:
New Airflow builds are available in Cloud Composer 3:
(Cloud Composer 2 versions from 2.12.0 to 2.12.3) Fixed a problem where Airflow components in the environment's cluster were running out of ephemeral storage. This change rolls out gradually over several releases to all regions supported by Cloud Composer 2.
Cluster Toolkit version v1.68.0 is available. This release lets you
download the NVIDIA Collective Communications Library (NCCL) software packages
libnccl2 and libnccl-dev for A3U and A4H machine types. For more information
about this release, see the Release announcement on
GitHub.
This release supports the generally available, open-source IBM Spectrum Symphony HostFactory connectors for Google Compute Engine and Google Kubernetes Engine, which you can deploy through Cluster Toolkit to extend your on-premises cluster or run entirely within Google Cloud. For information, see Run IBM Spectrum Symphony workloads.
You can monitor the inventory, metrics, and alerts for Oracle Database@Google Cloud databases using Database Center. For more information, see Metrics and alerting policy filters. Oracle Database@Google Cloud support in Database Center is in Preview. During Preview, you can't monitor health issues for Oracle Database@Google Cloud databases.
Bug fixes in IntelliJ
Various bug fixes and minor product enhancements.
Conversational Analytics in Looker
The following features are available in Preview for use with Conversational Analytics in Looker instances that are running Looker 25.18.9 or later:
- New model-specific Looker permissions are available to manage and use the Conversational Analytics data agents that are created to chat with Looker Explores. You can grant these permissions to users as part of a custom role, or use one of two new default roles, Conversational Analytics Agent Manager and Conversational Analytics User, to manage and use agents, respectively.
- You can now select up to five Looker Explores as data sources for a data agent in Looker.
- Users with the
admin_agentspermission can now share data agents to let other users chat with your agent and its Explores. Starting in Looker 25.18.10, users with either thesave_agentsor theadmin_agentspermission can share data agents with other users.
(This release note was updated on October 10, 2025 to correct the Looker version for this release. This release note was updated on October 23, 2025 to correct the Looker version for data agent sharing permissions.)
Media CDN supports multipart range requests, which enable users to request multiple non-contiguous segments of a file in a single HTTP request. This feature is in Preview.
For more information, see Multipart range requests.
Memorystore for Valkey now supports maintenance changelogs. Maintenance changelogs provide information about updates available in new maintenance versions, such as patches for security vulnerabilities.
For links to current maintenance changelogs for each major version of Memorystore for Valkey, see Memorystore for Valkey maintenance changelogs. This feature is Generally Available.
You can use custom constraints with Organization Policy to provide more granular control over specific fields for some Application Integration resources. For more information, see Manage Application Integration resources using custom constraints. This feature is available in Preview.
Correlated Threats is available in Preview. This feature combines related threat findings together by using the security graph, helping you to prioritize and respond to active threats.
The BRAZIL_RG_NUMBER infoType detector is available in all regions. For more information about all built-in infoTypes, see the InfoType detector reference.
October 09, 2025
Agent AssistOpenAPI and Integration Connectors tools are generally available in Agent Assist. Google Cloud enables the use of this external API and data source to improve Agent Assist integrations.
Agent Assist offers the following functions in addition to generative knowledge assist features:
- Apply document and safety filters.
- Configure Pub/Sub notifications for empty suggestions.
- Troubleshoot knowledge assist features.
Agent Assist offers AI coach in GA. AI coach automatically suggests responses to an agent during a customer service conversation. AI coach is available in all Google Cloud languages and regions.
Addressed multiple Common Vulnerabilities and Exposures (CVEs) by updating dependencies.
Deprecation of the Gemini Code Assist @Apigee tool.
The Gemini Code Assist @Apigee tool is deprecated and will be shut down as of October 14, 2025.
See Gemini Code Assist @Apigee tool deprecation for information.
Security, privacy, and compliance for Gemini in BigQuery details how customer data is protected and processed by Gemini in BigQuery.
An updated version of the ODBC driver for BigQuery is now available.
You can allocate idle slots fairly across reservations within a single admin project. This ensures each reservation receives an approximately equal share of available capacity. This feature is now generally available (GA).
You can set a maximum slot limit for a reservation. You can configure the maximum reservation size when creating or updating a reservation. This feature is now generally available (GA).
The Service Account User role has been removed from the Cloud Build Permissions page in the Google Cloud Console. Instead, when you enable certain roles on your Cloud Build service account, you can configure your Cloud Build Service account to impersonate the service account of the managed services related to those roles. This configuration lets you deploy builds using managed services while maintaining minimal permissions. For more information, see Configure Cloud Build service account impersonation for managed services.
In addition, the Cloud Build Permissions page in the Google Cloud Console will only show the legacy Cloud Build service account if your organization's policy allows it.
Upgrade checks are now generally available (GA) in Cloud Composer 3 and Cloud Composer 2.
The query builder in the Log Analytics page is generally available (GA). For more information, see Build, edit, and run a query.
cos-117-18613-339-89
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.105 | v24.0.9 | v1.7.28 | See List |
Updated toolbox container image tag to v20251002.
Upgraded sys-apps/hwdata to v0.399.
Partially fixed the system not responding caused by excessive contention among writeback kworkers when switching a large number of inodes between cgroups.
Fixed KCTF-134121b in the Linux kernel.
Fixed CVE-2025-39953 in the Linux kernel.
Fixed CVE-2025-39931 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811788 -> 811755
cos-125-19216-0-80
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.46 | v27.5.1 | v2.1.3 | See List |
Promoted Milestone 125 to stable.
Fixed KCTF-134121b in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811450 -> 811500
- Changed: net.ipv4.udp_mem: 188034 250715 376068 -> 188034 250714 376068
Updated toolbox container image tag to v20251002.
Bug fixes in VS Code
Various bug fixes and minor product enhancements.
Security, privacy, and compliance for Gemini in BigQuery
Security, privacy, and compliance for Gemini in BigQuery details how customer data is protected and processed by Gemini in BigQuery.
Gemini Enterprise: Google Agentspace is now part of Gemini Enterprise
The Google Agentspace experience in the Google Cloud console and the default application is now referred to as Gemini Enterprise. This includes all associated resources and documentation.
Imagen
Imagen's virtual try-on model, virtual-try-on-preview-08-04
was updated on September 30, 2025, to more accurately preserve the person's
body shape and preserve the garment's identity.
Version 3.39 is released
All release notes published on this date are part of version 3.39.
The timing of the update to your instance depends on the deployment schedule that you have chosen. For more information, see Deployment schedules.
New advanced reporting dashboards
The following new advanced reporting dashboard is available:
Deflections. Get deflection information by queue and for your entire contact center. For more information, see Deflections dashboards.
Agent activity timeline. See the historical activity for an agent. For more information, see Agent activity timeline dashboard.
Mid-session authentication is supported by all CRM types
Mid-session authentication is supported by all CRM types, not just custom CRMs. For more information, see Mid-Session authentication by API.
Cancel scheduled calls with the callback calls API
You can now use the callback calls API to cancel a single scheduled callback call or a list of calls. For more information, see Callback call API.
Advanced reporting dashboard updates
We've made the following updates to the advanced reporting dashboards:
Queue Group Dashboards All dashboard: The tiles and tables on this dashboard have been replaced with the following tables:
Queue Group Performance Calls: displays detailed performance information for calls by queue group.
Queue Group Performance Chats: displays detailed performance information for chats by queue group.
For more information, see Queue Group Dashboards All.
Queue interval dashboards: The Queue Interval - Calls and Queue Interval - Chats dashboards have a new Total Queue Entries column in the table tile. This is the sum of all inbound interactions that have entered a queue, excluding transfers.
For more information, see Queue interval dashboards.
Virtual agent dashboards: On both the Virtual Agent Dashboard Calls and Virtual Agent Dashboard Chats dashboards, the virtual agent metrics table contains a new Interaction Outcome column.
For more information, see Virtual agent dashboards.
All Interactions - Chat dashboard: In the All Chat Interactions (Historical) table, if you configure chat transcript storage for your CRM, the values in the Chat ID column become links to the chat transcripts.
For more information, see All interactions dashboards.
New metrics in the Call Queue Metrics (Historical) Explore: We've added the following two metrics to the Call Queue Metrics (Historical) Explore:
CSL %: Custom Service Level. This is calculated as follows: The number of queued interactions within SLA / The number of queued interactions answered.
Total Queued Answered: The number of queued interactions answered by a human agent.
For information about metrics in an Explore, see Create a new metrics tile in a dashboard.
Additional dashboards with advanced capabilities: the following dashboards now appear on the Advanced Reporting Landing Page. This means you can use them to create new custom dashboards or create Looks to link to custom dashboards.
Performance
Dispositions / Calls
Dispositions / Chats
Deflections / Calls
Deflections / Chats
CSAT / Calls
CSAT / Chats
Co-browse / Calls
Co-browse / Chats
Failed / Calls
Failed / Chats
Missed / Calls
Missed / Chats
Agent Reporting
- Agent Activity Timeline
Monitoring Dashboards
Calls Connected
Chats Connected
Calls Queued
Chats Queued
For more information, see Advanced capabilities.
Improved controls over the ordering of key-value pairs in the agent adapter and CRM records
Google Cloud CCaaS has improved controls over the ordering of the key-value pairs that appear in the agent adapter and in CRM records. Here's how the ordering controls work:
Virtual agents: When you configure session variables, you can use the new
display_order_in_adapterproperty to specify the order that the session variables appear in the agent adapter and in CRM records. For more information, see Capture from intent response.Web SDK: Web SDK custom data is displayed in the agent adapter and CRM records in the order that the key-value pairs appear in the JSON custom data file. For more information about JSON custom data files, see Chat unsigned custom data.
Virtual agents for the SMS channel
Virtual agents are now available for the SMS channel. This lets you create virtual agents and assign them to SMS queues, offering virtual agent support to end-users in SMS chat sessions. For more information, see Virtual agents for SMS.
Destination queue name and session history is available in the agent adapter
The agent adapter now displays the destination queue during transfers and deflections for IVR calls. The agent adapter also displays transfer history in the Call details and Chat details tabs.
User experience changes:
- The Call details and Chat details tabs in the agent adapter have a new Transfer History section.
- The chat pane in the chat adapter has a new Transfers button that opens the Transfer History pane.
Administrators: There's a new checkbox at Settings > Operation Management > Transfer history for turning on transfer history in the agent adapter.
For more information, see Transfer history and queue information in the agent adapter.
Search in the email channel
Agents can now search for emails in the agent adapter by keyword, session ID, or subject. For more information, see Search for emails.
The following issues were addressed in this release:
Fixed an issue where incoming chats took precedence over the in-progress chat.
User experience change: When a new chat appears in the agent adapter, it no longer takes focus away from the in-progress chat. The in-progress retains focus.
Fixed a web SDK issue where sensitive data sent by an end-user was redacted for both the end-user and the agent, instead of just for the agent.
Fixed an issue where the contact list in the agent adapter wouldn't load the full list of contacts.
Fixed an issue where an agent clicking an email in the agent adapter returned an Email Not Found error.
Fixed an issue where managers assigned to multiple teams were unable to view agent statistics for every team they were assigned to.
Fixed an issue for ServiceNow users where
call_durationwas using the earliestconnected_attime instead of the latestconnected_attime, causing call durations to appear longer than they actually were.Fixed an issue in the Settings > Developer Settings > External Storage pane where language checkboxes were associated with the Co-browse Recordings checkbox instead of the Session Data Feed checkbox.
Administrators: In the Settings > Developer Settings > External Storage pane, the languages checkboxes have moved from the Co-browse Recordings checkbox to the Session Data Feed checkbox.
Fixed an issue where agent-initiated outbound calls were using the default number for the selected queue instead of the number chosen by the agent.
Fixed an issue where the downloaded session chat data report contained an extra quotation mark.
Fixed an issue where users received an email telling them to create a password after Single Sign-On (SSO) was turned on.
Fixed an issue where SSO configuration settings in the user's instance were deleted after they turned off SSO.
Fixed an issue where an administrator couldn't configure agent status restrictions without exposing them to agents.
Fixed an issue where custom contact lists could only be replaced, and not removed, after they were assigned to a team.
Fixed an issue where the inheritance indicator and Reset to parent button was missing from the queue level Contact List Management pane.
Fixed an issue where the SMS and Web chat availability preferences in the agent adapter were the reverse of how they were configured.
Fixed an issue where queue transfer restrictions were not saved after being configured.
Fixed an issue that occurred when a user attempted to name a new queue. The name field abruptly lost focus after the first character, forcing the user to enter the queue name again.
Fixed an issue where creating an instance would time out and fail.
Fixed an issue that prevented reports from being downloaded.
Fixed an issue where the chat history for blended SMS sessions failed to save.
Fixed an issue where the Transfer failed message didn't appear. This occurred when an agent failed to pick up a transferred call before the transferred call expiration time expired.
Fixed an issue where IVR call recordings failed to save or were corrupted. This resulted in recordings that were only one second long, were saved in the wrong format, or weren't saved at all.
Fixed an issue where completed chat sessions appeared in the chats waiting area of agent desktop.
Fixed an issue for CRM users with voicemails that are attached directly to tickets. An incorrect "External Storage must be configured" warning appeared when configuring voicemail options for IVR queues.
Fixed an issue where transfer restrictions that were configured and saved for a web queue did not appear correctly the next time the Transfer Restrictions pane for that queue was viewed.
Fixed an issue where the unread message count in the chat pane was inconsistent when viewing it from multiple browser tabs.
Fixed an issue in virtual assistant reporting where the
finish_reasonproperty was incorrectly assigned to theundefinedvalue. Now thefinish_reasonproperty is assigned to descriptive values that describe the reason for the conclusion of the chat session.Fixed an issue where PDF transcripts of chat sessions contained malformed links.
Fixed an issue in historical reports where the fields in the Failed Reason Description column were blank.
Fixed an issue where CSAT scores were missing from some advanced reporting dashboards.
Fixed an issue for HubSpot users that caused long delays in case creation for inbound calls.
Fixed an issue where the photo and video files that the agent provided in pre-session Smart Actions didn't appear in the CRM.
Fixed an issue where agents in
Unavailablestatus couldn't see waiting web chats.Fixed an issue where HTML was not rendering properly in virtual agent messages in the agent adapter
Fixed an issue where agents were not switching into
Wrap-up Exceededstatus after a breakthrough call.Fixed an agent desktop issue where administrators were unable to assign announcements to some teams or agents.
Fixed an agent desktop issue where agents couldn't copy text to the clipboard from an agent desktop custom panel.
Fixed an agent desktop issue where the term "Anonymous User" wasn't being translated into French.
Fixed an issue where the
UJET_IDandANIvariables weren't passed correctly for SIP calls.Fixed an issue where the chat adapter froze when agents switched between chats.
Fixed an issue on the Agents page of the Google Cloud CCaaS portal where administrators couldn't switch between session types.
Fixed an issue where a newly added Agent Assist platform displayed as
Invalideven though it was valid.Fixed an issue for Salesforce users where the call button didn't work when an agent attempted to call a number that was attached to a record for a previous call.
Fixed an issue where audio files with accented characters in their file names failed to play back when using a storage proxy.
Fixed an agent desktop issue where the
UJET_IDvariable in the custom URL for a custom panel wasn't being passed correctly.Fixed an issue where calls originating from a native campaign generated two CRM tickets for the same interaction.
Fixed latency issues with web SDK Telnyx calls.
Fixed an issue where outbound Bring Your Own Carrier (BYOC) calls used a number other than the one agents selected in the agent adapter.
Fixed a Telnyx chatbot worker failure issue where background jobs related to call processing and chatbot escalations were failing and consuming excessive system resources.
Fixed an issue where calls to the bulk user upload endpoint returned a success status even when the uploads failed.
Fixed an issue in the chat waiting field of the agent desktop when multiple chats were in wrap-up. Instead of displaying Wrap-up in progress for all sessions in wrap-up, some sessions displayed Auto answered.
Fixed an issue in the queue group dashboard where the Callbacks waiting tile incorrectly included callbacks that were completed, abandoned, or failed.
Fixed an issue that caused inbound calls to disconnect if they were routed to an agent with a disabled microphone.
Fixed an issue for HubSpot users where logging the "call started" event (
create_activity) in the ticket was delayed.Fixed an issue that prevented transferred calls from being routed to available agents.
Fixed an issue in the agent adapter for French (Canada) where words weren't translated or were translated incorrectly.
Fixed an issue in call queue reporting where the Failed Reason Description for voice-scheduled mobile calls was not appearing.
Fixed an issue that prevented external chat transcripts from being passed into new chat sessions.
Fixed an advanced reporting issue where CSAT ratings were not appearing correctly when creating custom dashboards.
Fixed an advanced reporting issue where callbacks waiting metrics didn't match in the following dashboards: Queue Groups Dashboard Calls and Queued Calls Status Dashboard.
For AI models deployed on a GKE cluster, you can view details about these deployments in the Google Cloud console. The pages include deployment details, logs, and observability dashboards.
The following networking features are available:
In GKE version 1.33.4-gke.1055000 or later, you can control how external traffic reaches your Services on GKE clusters by using Network Service Tiers. You can configure the network tier to use either Standard Tier or Premium Tier when you create or update clusters or when you update LoadBalancer Services. For more information, see Configure external traffic with Network Service Tiers.
Starting with GKE versions 1.33 and later, you can enable automatic IP address management (auto IPAM) on GKE clusters. Auto IPAM dynamically adds or removes additional IP address ranges for nodes and Pods as the cluster scales up or down. This feature eliminates the need for large, potentially wasteful, upfront IP reservations and manual intervention during cluster scaling. For more information, see Use auto IP address management.
In GKE version 1.30.3-gke.1211000 and later, you can assign additional subnets to a VPC-native cluster. Additional subnets assigned to a cluster let you create new node pools where IPv4 addresses for both nodes and Pods come from the additional subnet ranges. This enhancement removes single-subnet limitations, increases scalability, and enhances the flexibility of your GKE clusters. For more information, see Add subnets to clusters.
Google Workspace: Version 22.0
Updated the action description to reflect that the action deletes the extension from the blocklist rather than deleting the extension from the organizational unit in the following action:
- Delete Extension
Google Threat Intelligence: Version 5.0
Added ability to filter by issue name in the following connector:
- Google Threat Intelligence - ASM Issues Connector
Added ability to filter events in the following connector:
- Google Threat Intelligence - DTM Alerts Connector
Google Chronicle: Version 66.0
Updated processing of reference list rows in the following action:
- Get Reference Lists
Microsoft Teams: Version 29.0
Refactored action logic in the following actions:
Get Authorization
Generate Token
Google Workspace: Version 22.0
Updated the action description to reflect that the action deletes the extension from the blocklist rather than deleting the extension from the organizational unit in the following action:
- Delete Extension
Google Threat Intelligence: Version 5.0
Added ability to filter by issue name in the following connector:
- Google Threat Intelligence - ASM Issues Connector
Added ability to filter events in the following connector:
- Google Threat Intelligence - DTM Alerts Connector
Google Chronicle: Version 66.0
Updated processing of reference list rows in the following action:
- Get Reference Lists
Microsoft Teams: Version 29.0
Refactored action logic in the following actions:
Get Authorization
Generate Token
Google Workspace: Version 22.0
Updated the action description to reflect that the action deletes the extension from the blocklist rather than deleting the extension from the organizational unit in the following action:
- Delete Extension
Google Threat Intelligence: Version 5.0
Added ability to filter by issue name in the following connector:
- Google Threat Intelligence - ASM Issues Connector
Added ability to filter events in the following connector:
- Google Threat Intelligence - DTM Alerts Connector
Google Chronicle: Version 66.0
Updated processing of reference list rows in the following action:
- Get Reference Lists
Microsoft Teams: Version 29.0
Refactored action logic in the following actions:
Get Authorization
Generate Token
Oracle Database@Google Cloud adds the following regions and zones for its services:
Exadata Database Service
europe-west2-a-r1(London, Europe)europe-west3-a-r2(Frankfurt, Europe)
Exadata Database Service on Exascale infrastructure
asia-northeast1-a-r1(Tokyo, Asia Pacific)europe-west3-b-r1(Frankfurt, Europe)
Base Database Service
asia-northeast1-a-r1(Tokyo, Asia Pacific)europe-west3-b-r1(Frankfurt, Europe)
Autonomous Database Service
australia-southeast2(Melbourne, Asia Pacific)us-central1(Iowa, North America)
For a full list of supported locations, see Supported regions and zones.
Data Security Posture Management (available in Preview) lets you deploy frameworks with advanced data security cloud controls to app-enabled folders. For more information, see Deploy advanced data security cloud controls.
M134 release
The M134 release of Vertex AI Workbench instances includes the following:
- Patched a regression with custom notebook metrics reporting (for example,
jupyterlab_kernelsanddocker_status metrics). - Updated the Dataproc JupyterLab plugin (
dataproc-jupyter-plugin) to version 0.1.92. - When using Google Cloud CLI commands, the
projectandregionproperties are preset.
October 08, 2025
Access ApprovalCloud Domains is available in Preview.
NCC Gateway is generally available (GA).
Cloud Domains is available in Preview.
NCC Gateway is generally available (GA).
The default limit of QueryUsagePerDay for
on-demand pricing has changed. The default limit of all new projects is now 200
TiB. For existing projects, the default limit has been set based on your
project's usage over the last 30 days. Projects that have custom cost
controls configured or that use
reservations aren't affected.
If the new limit might affect your workload, create a custom cost
control based on your workload needs.
You can set labels on reservations. These labels can be used to organize your reservations and for billing analysis. This feature is generally available (GA).
You can specify which reservation a query uses at runtime, and set IAM policies directly on reservations. This provides more flexibility and fine-grained control over resource management. This feature is generally available (GA).
Chat code suggestion preview in IntelliJ
Chat code suggestions are displayed in a preview block by default with IntelliJ Gemini Code Assist, improving the readability of generated chat responses.
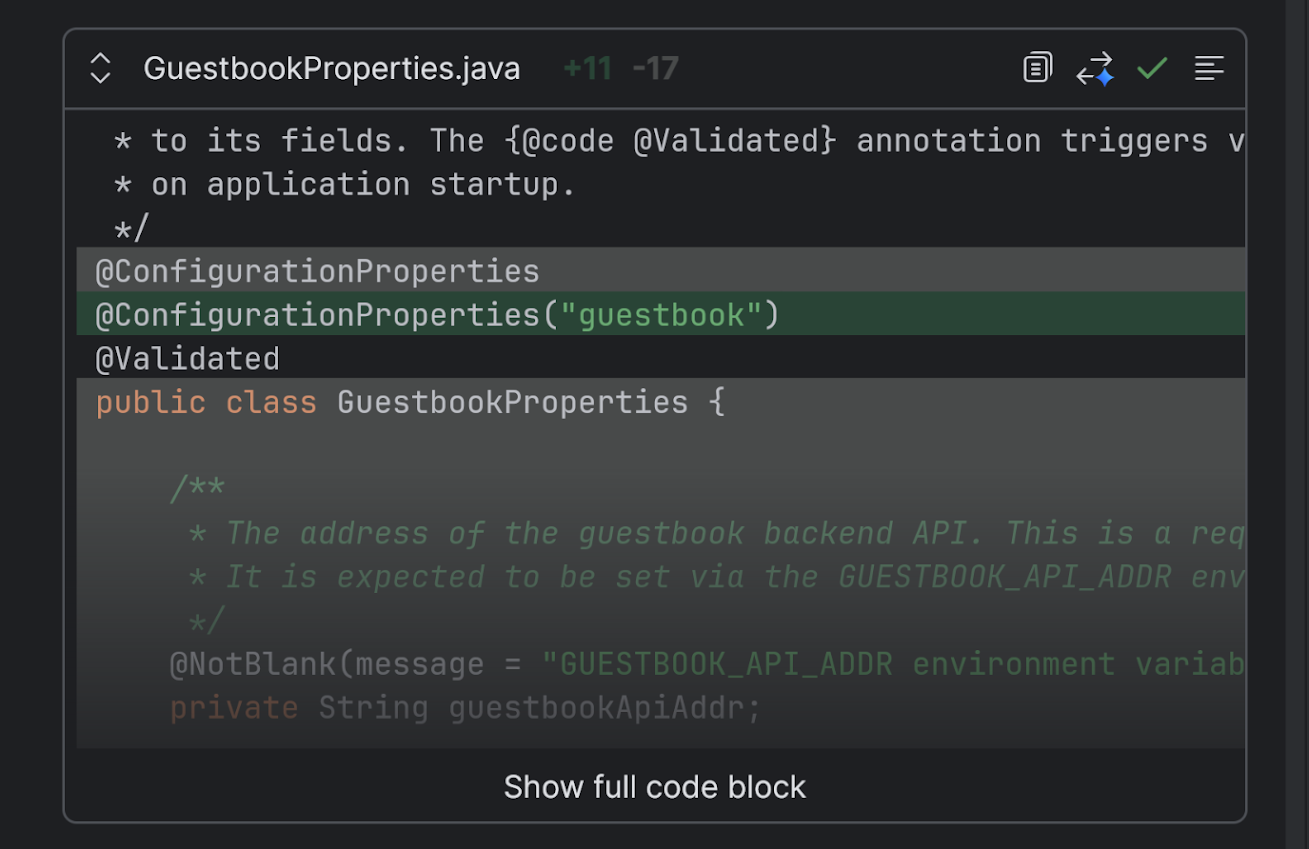
Next Edit Predictions in IntelliJ (Preview)
Next Edit Predictions, which predicts the next code suggestions throughout the code file that you're currently in, are now available in IntelliJ Gemini Code Assist, in Preview.
You can cycle through multiple suggestions, dismiss suggestions, or ignore them and continue coding.
Enable Next Edit Predictions in your IDE to get started.
Chat code suggestion preview in IntelliJ
Chat code suggestions are displayed in a preview block by default with IntelliJ Gemini Code Assist, improving the readability of generated chat responses.
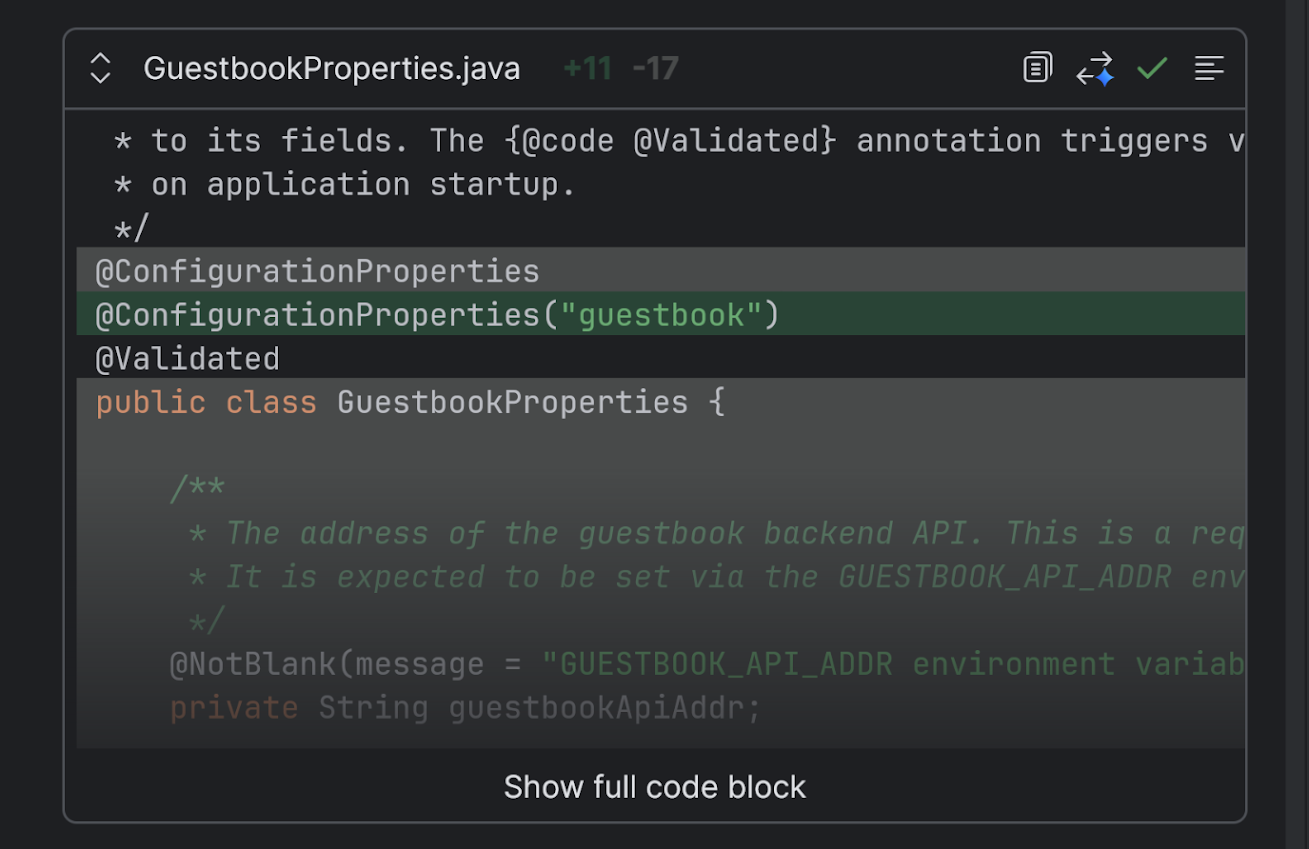
Next Edit Predictions in IntelliJ (Preview)
Next Edit Predictions, which predicts the next code suggestions throughout the code file that you're currently in, are now available in IntelliJ Gemini Code Assist, in Preview.
You can cycle through multiple suggestions, dismiss suggestions, or ignore them and continue coding.
Enable Next Edit Predictions in your IDE to get started.
(2025-R42) Version updates
GKE cluster versions have been updated.
New versions available for upgrades and new clusters.
The following versions are now available for new GKE clusters, and for manual control plane upgrades and node upgrades for existing clusters. For more information about versioning and upgrades, see GKE versioning and support and About GKE cluster upgrades.
Rapid channel
- The following versions are now available in the Rapid channel:
- The following versions are no longer available in the Rapid channel:
- 1.30.14-gke.1267000
- 1.30.14-gke.1316000
- 1.30.14-gke.1325000
- 1.31.12-gke.1220000
- 1.32.9-gke.1010000
- 1.33.4-gke.1350000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.12-gke.1265000
- 1.31 to 1.32.9-gke.1072000
- 1.32 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.12-gke.1265000
- 1.32 to 1.32.9-gke.1072000
- 1.33 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Regular channel
- Version 1.33.4-gke.1350000 is now the default version for cluster creation in the Regular channel.
- The following versions are now available in the Regular channel:
- The following versions are no longer available in the Regular channel:
- 1.30.14-gke.1150000
- 1.30.14-gke.1267000
- 1.31.11-gke.1036000
- 1.32.8-gke.1170000
- 1.33.4-gke.1245000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.12-gke.1220000
- 1.31 to 1.32.9-gke.1010000
- 1.32 to 1.33.4-gke.1350000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.12-gke.1220000
- 1.32 to 1.32.9-gke.1010000
- 1.33 to 1.33.4-gke.1350000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Stable channel
- Version 1.33.4-gke.1172000 is now the default version for cluster creation in the Stable channel.
- The following versions are now available in the Stable channel:
- The following versions are no longer available in the Stable channel:
- 1.30.14-gke.1108000
- 1.30.14-gke.1130000
- 1.32.8-gke.1108000
- 1.33.4-gke.1134000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.31 to 1.32.8-gke.1134000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.32 to 1.32.8-gke.1134000
- 1.33 to 1.33.4-gke.1172000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Extended channel
- Version 1.33.4-gke.1350000 is now the default version for cluster creation in the Extended channel.
- The following versions are now available in the Extended channel:
- The following versions are no longer available in the Extended channel:
- 1.28.15-gke.2630000
- 1.28.15-gke.2740000
- 1.29.15-gke.1851000
- 1.29.15-gke.1979000
- 1.31.11-gke.1036000
- 1.32.8-gke.1170000
- 1.33.4-gke.1245000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.27 to 1.28.15-gke.2697000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.28 to 1.28.15-gke.2697000
- 1.29 to 1.29.15-gke.1936000
- 1.31 to 1.31.12-gke.1220000
- 1.32 to 1.32.9-gke.1010000
- 1.33 to 1.33.4-gke.1350000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
No channel
- Version 1.33.4-gke.1350000 is now the default version for cluster creation.
- The following versions are now available:
- The following node versions are now available:
- The following versions are no longer available:
- 1.30.14-gke.1108000
- 1.30.14-gke.1130000
- 1.30.14-gke.1150000
- 1.30.14-gke.1267000
- 1.30.14-gke.1316000
- 1.30.14-gke.1325000
- 1.32.6-gke.1060000
- 1.32.8-gke.1108000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.12-gke.1220000
- 1.31 to 1.32.8-gke.1134000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.12-gke.1220000
- 1.32 to 1.32.8-gke.1134000
- 1.33 to 1.33.4-gke.1350000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R42) Security updates
This release includes new GKE versions that use updated Container-Optimized OS images. These updated images are cumulative, incorporating security fixes from all Container-Optimized OS versions released since the previous GKE release.
To identify the specific vulnerabilities that were resolved in each updated Container-Optimized OS image, see the Security release notes for that image. The following table includes links to the release notes for each updated Container-Optimized OS image:
| GKE version | Container-Optimized OS version | Details |
|---|---|---|
| 1.33.5-gke.1162000 | cos-121-18867-199-80 | cos-121-18867-199-80 release notes |
| 1.34.1-gke.1279000 | cos-121-18867-199-80 | cos-121-18867-199-80 release notes |
| 1.28.15-gke.2751000 | cos-113-18244-448-58 | cos-113-18244-448-58 release notes |
| 1.29.15-gke.1989000 | cos-113-18244-448-58 | cos-113-18244-448-58 release notes |
| 1.30.14-gke.1336000 | cos-113-18244-448-58 | cos-113-18244-448-58 release notes |
| 1.31.13-gke.1023000 | cos-117-18613-339-77 | cos-117-18613-339-77 release notes |
| 1.32.9-gke.1108000 | cos-117-18613-339-77 | cos-117-18613-339-77 release notes |
(2025-R42) Version updates
- Version 1.33.4-gke.1350000 is now the default version for cluster creation in the Extended channel.
- The following versions are now available in the Extended channel:
- The following versions are no longer available in the Extended channel:
- 1.28.15-gke.2630000
- 1.28.15-gke.2740000
- 1.29.15-gke.1851000
- 1.29.15-gke.1979000
- 1.31.11-gke.1036000
- 1.32.8-gke.1170000
- 1.33.4-gke.1245000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.27 to 1.28.15-gke.2697000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.28 to 1.28.15-gke.2697000
- 1.29 to 1.29.15-gke.1936000
- 1.31 to 1.31.12-gke.1220000
- 1.32 to 1.32.9-gke.1010000
- 1.33 to 1.33.4-gke.1350000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R42) Version updates
- Version 1.33.4-gke.1350000 is now the default version for cluster creation.
- The following versions are now available:
- The following node versions are now available:
- The following versions are no longer available:
- 1.30.14-gke.1108000
- 1.30.14-gke.1130000
- 1.30.14-gke.1150000
- 1.30.14-gke.1267000
- 1.30.14-gke.1316000
- 1.30.14-gke.1325000
- 1.32.6-gke.1060000
- 1.32.8-gke.1108000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.12-gke.1220000
- 1.31 to 1.32.8-gke.1134000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.12-gke.1220000
- 1.32 to 1.32.8-gke.1134000
- 1.33 to 1.33.4-gke.1350000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R42) Version updates
- The following versions are now available in the Rapid channel:
- The following versions are no longer available in the Rapid channel:
- 1.30.14-gke.1267000
- 1.30.14-gke.1316000
- 1.30.14-gke.1325000
- 1.31.12-gke.1220000
- 1.32.9-gke.1010000
- 1.33.4-gke.1350000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.12-gke.1265000
- 1.31 to 1.32.9-gke.1072000
- 1.32 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.12-gke.1265000
- 1.32 to 1.32.9-gke.1072000
- 1.33 to 1.33.5-gke.1080000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R42) Version updates
- Version 1.33.4-gke.1350000 is now the default version for cluster creation in the Regular channel.
- The following versions are now available in the Regular channel:
- The following versions are no longer available in the Regular channel:
- 1.30.14-gke.1150000
- 1.30.14-gke.1267000
- 1.31.11-gke.1036000
- 1.32.8-gke.1170000
- 1.33.4-gke.1245000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.30 to 1.31.12-gke.1220000
- 1.31 to 1.32.9-gke.1010000
- 1.32 to 1.33.4-gke.1350000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.31 to 1.31.12-gke.1220000
- 1.32 to 1.32.9-gke.1010000
- 1.33 to 1.33.4-gke.1350000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
(2025-R42) Version updates
- Version 1.33.4-gke.1172000 is now the default version for cluster creation in the Stable channel.
- The following versions are now available in the Stable channel:
- The following versions are no longer available in the Stable channel:
- 1.30.14-gke.1108000
- 1.30.14-gke.1130000
- 1.32.8-gke.1108000
- 1.33.4-gke.1134000
- Clusters in this channel running the listed minor version have new general auto-upgrade targets. GKE can upgrade control planes and nodes to the following new versions with this release:
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
- 1.31 to 1.32.8-gke.1134000
- GKE upgrades clusters to the following new patch versions if no minor version upgrade is available, or if the cluster has maintenance exclusions or other factors preventing minor version upgrades:
- 1.32 to 1.32.8-gke.1134000
- 1.33 to 1.33.4-gke.1172000
- GKE upgrades clusters to the following new minor versions if there are no factors, such as maintenance exclusions or deprecated APIs, preventing upgrades:
Multi-stage queries in YARA-L
This feature is currently in Preview.
Multi-stage queries in YARA-L are now available as a Preview feature. Multi-stage queries in YARA-L let you feed the output of one query stage directly into the input of a subsequent stage. This process gives you greater control over data transformation than single, monolithic query. They are supported in both Dashboards and Search. Multi-stage queries can contain between 1 and 4 named stages, in addition to a root stage.
For more information, see Create multi-stage queries in YARA-L.
Multi-stage queries in YARA-L
This feature is currently in Preview.
Multi-stage queries in YARA-L are now available as a Preview feature. Multi-stage queries in YARA-L let you feed the output of one query stage directly into the input of a subsequent stage. This process gives you greater control over data transformation than single, monolithic query. They are supported in both Dashboards and Search. Multi-stage queries can contain between 1 and 4 named stages, in addition to a root stage.
For more information, see Create multi-stage queries in YARA-L.
Multi-stage queries in YARA-L
This feature is currently in Preview.
Multi-stage queries in YARA-L are now available as a Preview feature. Multi-stage queries in YARA-L let you feed the output of one query stage directly into the input of a subsequent stage. This process gives you greater control over data transformation than single, monolithic query. They are supported in both Dashboards and Search. Multi-stage queries can contain between 1 and 4 named stages, in addition to a root stage.
For more information, see Create multi-stage queries in YARA-L.
BigQuery Connector for SAP version 2.10
Version 2.10 of the BigQuery Connector for SAP is generally available (GA). This version resolves the non-ASCII character handling issue in CDC replication through Pub/Sub and enhances server-side error handling.
For more information, see What's new with BigQuery Connector for SAP.
ABAP SDK for Google Cloud version 1.12 (On-premises or any cloud edition)
Version 1.12 of the on-premises or any cloud edition of the ABAP SDK for Google Cloud is generally available (GA). This version lets you integrate Gemma models into your ABAP applications. In addition, the SDK improves your interaction with Gemini models by letting you control the randomness of the model's output and gain insight into the model's reasoning.
For more information, see What's new with the on-premises or any cloud edition of the ABAP SDK for Google Cloud.
October 07, 2025
Apigee UIOn October 7, 2025, we released an updated version of the Apigee UI.
Output from print statements is now displayed in the Debug session viewer
A new option has been added to the transaction navigation table header in the Debug session viewer that opens the Transaction output window. The Transaction output window displays print() output from either all transactions in the debug session, or a specific transaction from the session. See Creating a debug session for details.
Previously unreported customer DNS misconfigurations now result in DNS errors
Apigee removed the automatic DNS fallback functionality that was in 1-16-0-apigee-2. This removal surfaces customer DNS misconfigurations that previously did not show as DNS errors.
hybrid v1.14.3
On October 7, 2025 we released an enhancement to Apigee hybrid version 1.14.3, recurring, top-up, and setup fees for Apigee hybrid monetization.
- For complete information on the contents of the v1.14.3 release, see Apigee hybrid v1.14.3 release notes.
Recurring, top-up, and setup fees for Apigee hybrid monetization
Apigee hybrid now supports recurring, top-up, and setup fees for monetization. For information see Enabling monetization for Apigee hybrid.
| Bug ID | Description |
|---|---|
| 419578402 | Mint-Mart forward proxy compatible. |
As of February 25, 2025, enhancements to the workload management autoscaler that were announced on July 31, 2024 have rolled out to all users. These enhancements are generally available (GA).
You can connect to Bigtable from Java applications and other reporting tools that support a generic JDBC adapter by using the Bigtable JDBC driver. This feature is available in Preview.
The Cassandra-Bigtable proxy adapter, which lets you connect your Apache Cassandra-based applications to Bigtable, is generally available (GA).
Cloud CDN provides predefined dashboards that are enabled by default for a quick insight into system health and performance. These dashboards display key metrics that enable you to monitor traffic distribution and cache effectiveness without manual configuration. This feature is Generally Available.
For more information, see Predefined dashboards.
Cloud Run functions (1st gen) supports the Node.js 22 runtime at the General Availability release level.
Post-startup scripts
Preview: You can use a post-startup script to perform tasks after the startup process of your Colab Enterprise runtime. For example, you can use a post-startup script to install specific packages or make specific changes to your runtime's VM. For more information, see Use a post-startup script.
Config Connector version 1.136.1 is now available.
New Fields:
ComposerEnvironment- Added
spec.storageConfigfield. - Added
spec.config.workloadsConfig.dagProcessorfield. - Added
spec.config.workloadsConfig.triggererfield. - Added
spec.config.softwareConfig.webServerPluginsModefield. - Added
spec.config.softwareConfig.cloudDataLineageIntegrationfield.
- Added
Bug Fixes:
- Added support for checking
etagin spec for alpha resources. - Fixed an issue where
CloudIdentityMembershiproles comparison would fail. - Fixed a bug where the wrong GVK was reported in IAM controller.
- Fixed a bug where errors were swallowed when reading a Secret.
- Fixed an issue with LRO endTime in mockgcp.
- Fixed a bug in the
etagmapper. - Fixed a bug in the mapper generator for slice and single object map.
- Fixed a bug in the mapper generator for OneOf if the input is not proto.Message.
- Fixed an import for refs in the same package in
controllerbuilder.
New Beta Resources (Direct Reconciler):
Reconciliation Improvements:
- Introduced Stateful Reconciliation for Direct Controllers. With stateful reconciliation, the direct controller stores a hash of the last successfully applied
.specin the resource's.status. This provides a lightweight, GitOps-safe record when a user has modified the desired state of the resource.
Bug fixes in VS Code
Various bug fixes and minor product enhancements.
The following Qwen models are available in Model Garden:
- Qwen-Image
- Qwen-Image-Edit
- Qwen-Image-Edit-2509
Save and share prompts in Vertex AI Studio: You can now save and share prompts in Vertex AI Studio. Sharing prompts lets you collaborate with team members, ensure consistency, and build a library of effective prompts for various tasks. For more information, see Save and share prompts.
The Gemini 2.5 Computer Use model and tool (gemini-2.5-computer-use-preview-10-2025) is now available in Preview. The Computer Use model and tool lets you enable your applications to interact with and automate tasks in the browser. With the Computer Use model and tool, you can build agents that can:
Automate repetitive data entry or form filling on websites.
Navigate websites to gather information.
Assist users by performing sequences of actions in web applications.
Starting with GKE version 1.33.2-gke.1240000 and later, you can specify the
network tier (Standard or Premium) for ephemeral IP addresses used by
the gke-l7-regional-external-managed-mc GatewayClass. For more information,
see Configure Network
Tier.
Manage parser versions
This feature is in preview.
You now have granular control over how new pre-built parser versions are deployed within your environment.
This feature lets you manage parser updates by taking the following actions:
Opt in or opt out of automatic parser updates.
Review and compare the processing logic between different parser versions.
Manually update a parser to a newer version.
Revert to a previously deployed, stable parser version.
For details, see Manage prebuilt parser versions.
Azure AD Organizational Context default parser rollback
The recent update to the pre-built Azure AD Organizational Context (AZURE_AD_CONTEXT) parser has been rolled back. This action was necessary to resolve a performance degradation issue that was introduced in the latest parser version. For more information about the exact changes and rollback timeline, see the change log for the pre-built parser.
Manage parser versions
This feature is in preview.
You now have granular control over how new pre-built parser versions are deployed within your environment.
This feature lets you manage parser updates by taking the following actions:
Opt in or opt out of automatic parser updates.
Review and compare the processing logic between different parser versions.
Manually update a parser to a newer version.
Revert to a previously deployed, stable parser version.
For details, see Manage prebuilt parser versions.
Manage parser versions
This feature is in preview.
You now have granular control over how new pre-built parser versions are deployed within your environment.
This feature lets you manage parser updates by taking the following actions:
Opt in or opt out of automatic parser updates.
Review and compare the processing logic between different parser versions.
Manually update a parser to a newer version.
Revert to a previously deployed, stable parser version.
For details, see Manage prebuilt parser versions.
Azure AD Organizational Context default parser rollback
The recent update to the pre-built Azure AD Organizational Context (AZURE_AD_CONTEXT) parser has been rolled back. This action was necessary to resolve a performance degradation issue that was introduced in the latest parser version. For more information about the exact changes and rollback timeline, see the change log for the pre-built parser.
Azure AD Organizational Context default parser rollback
The recent update to the pre-built Azure AD Organizational Context (AZURE_AD_CONTEXT) parser has been rolled back. This action was necessary to resolve a performance degradation issue that was introduced in the latest parser version. For more information about the exact changes and rollback timeline, see the change log for the pre-built parser.
Google Cloud console pages for all Security Command Center tiers have been enhanced.
The following changes were made to all service tiers—Standard, Premium, and Enterprise:
- You can refresh findings in the Finding query results panel.
- The JSON tab on the detail pane of the Findings page displays the raw findings JSON object, making it compatible with APIs.
- Autocompletion of a query in the Findings page query editor is improved.
- The Findings > Quick filters panel shows default values if there is an error fetching results.
- The Findings > Quick filters panel shows separate State and Mute filter sections.
The following changes were made to the Enterprise service tier:
- Added support for the Vulnerabilities page.
- Added support for security marks.
- Added support for the Threats dashboard on the Risk overview page.
- The finding detail panel on the Issues page is updated. Open the panel using the View details button when viewing a toxic combination issue type.
- Additional query operators and query functions are available.
- The opt-out banner is no longer available.
October 06, 2025
Access TransparencyVertex AI Agent Engine is generally available (GA).
AlloyDB supports the tds_fdw extension, which provides a foreign data wrapper
for accessing databases—such as Microsoft SQL Server and Sybase—that
use the Tabular Data Stream (TDS) protocol. For more information, see Supported database extensions. This feature is
generally available (GA).
The BigQuery Data Transfer Service can now transfer data from the following data sources:
Transfers from these data sources are supported in preview.
The BigQuery Data Transfer Service can now transfer reporting data from Google Analytics 4 into BigQuery. You can also include custom reports from Google Analytics 4 in your data transfer. This feature is generally available (GA).
You can now set the priority of BigQuery jobs initiated by Dataform workflows to run queries as interactive jobs that start running as quickly as possible or as batch jobs with lower priority. For more information, see Create a pipeline schedule and InvocationConfig. This feature is generally available (GA).
The INFORMATION_SCHEMA.SHARED_DATASET_USAGE view
now includes the following schema fields to support usage metrics for
external tables and routines:
shared_resource_id: the ID of the queried resourceshared_resource_type: the type of the queried resourcereferenced_tables: Containsproject_id,dataset_id,table_id, andprocessed_bytesfields of the base table.
These fields are generally available (GA).
Starting March 17, 2026, the BigQuery Data Transfer Service will require the
bigquery.datasets.setIamPolicy and the bigquery.datasets.getIamPolicy
permissions on the target dataset to create or update a transfer configuration.
For more information, see Changes to dataset-level access controls.
You can optimize storage with Bigtable tiered storage, reduce storage costs, and retain data for longer. This feature is available in Preview.
Percentage-based request mirroring is now supported for the global and regional external Application Load Balancers (classic is not supported). By default, the mirrored backend service receives all requests, even if the original traffic is being split between multiple weighted backend services. You
can now configure the mirrored backend service to receive only a percentage of the
requests by using the mirrorPercent flag to specify the percentage of
requests to be mirrored, expressed as a value between 0 and 100.0.
For an example, see Set up traffic management for regional external Application Load Balancers.
This feature is available in General availability.
Support for applying maximum instance configuration at the service level is in General Availability (GA).
You can now assess the upgrade readiness of your Cloud SQL for PostgreSQL instances before a major version upgrade by running a precheck. This precheck either confirms your instance can be upgraded, or lists issues and their solutions that need to be fixed prior to upgrading. For more information, see Assess upgrade readiness for your instance.
You can now use advanced disaster recovery (DR) for your Private Service Connect (PSC) enabled Cloud SQL Enterprise Plus edition instances. With advanced DR, you can:
- Designate a cross-region disaster recovery (DR) replica
- Perform a cross-region replica failover for disaster recovery
- Restore your original deployment by using zero-data loss switchover
The Google Cloud optimized (-optimized-gcp) and accelerated
(optimized-gcp-nvidia-*) versions of the Rocky Linux images include the
CIQ SIG/Cloud Next repository,
which provides a cloud-optimized kernel. The accelerated
images also include the CIQ SIG/Cloud Next Nonfree
repository,
which provides proprietary GPU drivers for the cloud-optimized kernel.
This update applies to images created on or after September 12, 2025.
For more information about Rocky Linux OS images, see Rocky Linux on the operating system details page.
cos-beta-125-19216-0-76
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.46 | v27.5.1 | v2.1.3 | See List |
Configured the cos-gpu-installer to use R580 drivers as the default GPU drivers.
Add support for NVIDIA MFT Tools v4.33.0.
Updated dev-python/urllib3 to v1.26.18 and fixed CVE-2025-50181.
Updated dev-python/jinja to v3.1.6. This resolves CVE-2024-56326, CVE-2024-56201 and CVE-2025-27516.
Fixed CVE-2025-39913 in the Linux kernel.
Fixed CVE-2025-39914 in the Linux kernel.
Fixed CVE-2025-39911 in the Linux kernel.
Fixed CVE-2025-39926 in the Linux kernel.
Fixed CVE-2025-39917 in the Linux kernel.
Fixed CVE-2025-22106 in the Linux kernel.
Fixed KCTF-1b34cbb in the Linux kernel.
Fixed CVE-2025-39886 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811504 -> 811450
cos-121-18867-199-88
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.105 | v27.5.1 | v2.0.6 | See List |
Add support for NVIDIA MFT Tools v4.33.0.
Fixed CVE-2025-50181 in dev-python/urllib3.
Fixed CVE-2025-39914 in the Linux kernel.
Fixed CVE-2025-39913 in the Linux kernel.
Fixed CVE-2025-39911 in the Linux kernel.
Fixed CVE-2025-22106 in the Linux kernel.
Fixed KCTF-1b34cbb in the Linux kernel.
Fixed CVE-2025-39882 in the Linux kernel.
Fixed CVE-2025-39886 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811826 -> 811724
cos-117-18613-339-84
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.105 | v24.0.9 | v1.7.28 | See List |
Add support for NVIDIA MFT Tools v4.33.0.
Fixed CVE-2025-50181 in dev-python/urllib3.
Fixed CVE-2025-39914 in the Linux kernel.
Fixed CVE-2025-39913 in the Linux kernel.
Fixed CVE-2025-39911 in the Linux kernel.
Fixed CVE-2025-22106 in the Linux kernel.
Fixed KCTF-1b34cbb in the Linux kernel.
Fixed CVE-2025-39882 in the Linux kernel.
Fixed CVE-2025-39886 in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 811817 -> 811788
cos-dev-129-19302-0-0
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.49 | v27.5.1 | v2.1.3 | See List |
Updated the Linux kernel to v6.12.49.
Configured the cos-gpu-installer to use R580 drivers as the default GPU drivers.
Add support for NVIDIA MFT Tools v4.33.0.
Updated dev-python/jinja to v3.1.6. This resolves CVE-2024-56326, CVE-2024-56201 and CVE-2025-27516.
Runtime sysctl changes:
- Changed: fs.file-max: 811490 -> 811493
- Changed: net.ipv4.udp_mem: 188034 250715 376068 -> 188034 250714 376068
cos-113-18244-448-63
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.1.151 | v24.0.9 | v1.7.27 | See List |
Fixed CVE-2025-50181 in dev-python/urllib3.
Fixed CVE-2025-39914 in the Linux kernel.
Fixed CVE-2025-39913 in the Linux kernel.
Fixed KCTF-1b34cbb in the Linux kernel.
Runtime sysctl changes:
- Changed: fs.file-max: 812039 -> 811950
You can use custom constraints with Organization Policy to provide more granular control over specific fields for some Dataform resources. For more information, see Create custom organization policy constraints. This feature is generally available (GA).
You can set the priority of BigQuery jobs in Dataform to run queries as interactive jobs that start running as quickly as possible or as batch jobs with lower priority. For more information, see Create a workflow configuration and InvocationConfig. This feature is generally available (GA).
Dataproc on Compute Engine: The following diagnostic properties are now enabled by default for new Dataproc clusters created with 2.0+ image versions:
dataproc:diagnostic.capture.enabled: Collects checkpoint diagnostic data in the cluster temp bucket.dataproc:dataproc.logging.extended.enabled: Collects logs for the Knox, Zeppelin, Ranger-usersync, Jupyter_notebook, Jupyter_kernel_gateway components and the Spark History-Server in Cloud Logging.dataproc:dataproc.logging.syslog.enabled: Collects VM syslogs in Cloud Logging.
Note: To disable any of these features, set the corresponding property to false during cluster creation.
To continue using the Ops Agent initialization action opsagent.sh to ingest syslogs from Dataproc cluster nodes, do one of the following:
- Recommended: Use
opsagent_nosyslog.shsince VM syslogs are emitted by default from Dataproc clusters. - Set the
dataproc:dataproc.logging.syslog.enabled=falseand continue usingopsagent.shto ingest syslogs.
Serverless for Apache Spark: Upgraded Apache Spark to version 3.5.3 in the latest 2.3 Serverless for Apache Spark runtime versions.
New Serverless for Apache Spark runtime versions:
- 2.3.13
- 3.0.0-RC5
Capacity reservation is available for Document AI in Preview. This lets you grant capacity to selected processors and maintain a steady real-time, high-volume processing flow for document processing requests.
For the necessary steps, read make a capacity reservation request section of "Quotas".
Custom extractor model
pretrained-foundation-model-v1.5.1-2025-08-07 with improved adaptive few-shot
learning is available as Release Candidate
(Preview).
Support for confidence scores in Custom classifier
models pretrained-foundation-model-v1.4-2025-05-16 and pretrained-classifier-v1.5-2025-08-05
is in Preview.
For best performance, use them with fine-tuned models.
A weekly digest of client library updates from across the Cloud SDK.
Java
Changes for google-cloud-datastore
2.32.2 (2025-10-04)
Dependencies
Updated pricing for Vertex AI Agent Engine: Starting on November 6, 2025, Vertex AI Agent Engine Runtime will start charging for runtime usage for the following regions:
asia-southeast1(Singapore)australia-southeast2(Melbourne)europe-west2(London)europe-west3(Frankfurt)europe-west4(Netherlands)
For more details, see Pricing for Vertex AI Agent Engine.
Access Transparency for Vertex AI Agent Engine: Access Transparency is now available for Vertex AI Agent Engine. For more information, see the overview for Enterprise security.
We've updated the Cloud Commerce Procurement API's GET Account resource to
provide the reseller parent Cloud Billing account ID for transactions
associated with resold Cloud Billing accounts. For transactions on
direct Cloud Billing accounts, no value is returned for the reseller
parent Cloud Billing account id. For details, see the
Cloud Commerce Procurement API documentation.
We've updated the Cloud Commerce Procurement API's GET Account resource to
provide the reseller parent Cloud Billing account ID for transactions
associated with resold Cloud Billing accounts. For transactions on
direct Cloud Billing accounts, no value is returned for the reseller
parent Cloud Billing account id. For details, see the
Cloud Commerce Procurement API documentation.
Advanced BigQuery Export
This feature is in preview.
This feature is available for Google SecOps Enterprise Plus customers only.
Advanced BigQuery Export automatically provisions and manages essential Google SecOps datasets in a secure, Google-managed BigQuery project. You gain secure, read-only access to this data through a BigQuery linked dataset, which appears directly in your own Google Cloud project. This functionality lets you query your security data as if it were stored locally, but without the overhead of managing the data pipeline or storage.
For details, see Use Advanced BigQuery Export.
Advanced BigQuery Export
This feature is in preview.
This feature is available for Google SecOps Enterprise Plus customers only.
Advanced BigQuery Export automatically provisions and manages essential Google SecOps datasets in a secure, Google-managed BigQuery project. You gain secure, read-only access to this data through a BigQuery linked dataset, which appears directly in your own Google Cloud project. This functionality lets you query your security data as if it were stored locally, but without the overhead of managing the data pipeline or storage.
For details, see Use Advanced BigQuery Export.
Looker 25.18 is expected to include the following changes, features, and fixes:
Expected Looker (original) deployment start: Tuesday, October 7, 2025
Expected Looker (original) final deployment and download available: Thursday, October 16, 2025
Expected Looker (Google Cloud core) deployment start: Tuesday, October 7, 2025
Expected Looker (Google Cloud core) final deployment: Monday, October 20, 2025
Conversational Analytics users with the save_agents permission can now share data agents, which lets other users chat with the data agent and its Explores. (This release note was added on October 9, 2025.)
The Athena JDBC driver version has been upgraded from 2.1.5 to 2.2.2. The Athena JDBC driver is used for connections to Amazon Athena.
You can now set the Auto Resize Value setting on single value visualizations. This setting has no effect if the Smart Single Value Text Size setting is enabled on the Admin > General Settings page.
An issue has been fixed where the maximum column limit warning could obscure the contents of a visualization. This feature now performs as expected.
An issue has been fixed where, when dashboard filters were updated, table visualizations could get incorrectly cropped to exclude the Total row and scroll bar. This feature now performs as expected.
An issue has been fixed where certain countries would not be displayed when a custom TopoJSON file was used. The following country names are now supported:
- Czechia for Czech Republic
- Eswatini for Swaziland
- Brunei Darussalam for Brunei
- North Macedonia for Macedonia
- Timor-Leste for East Timor
Looker 25.18 contains the following accessibility improvements:
You can navigate drill menus by using a keyboard.
When you select a button toggle with a keyboard, the focus ring uses more contrasting colors.
You can switch button toggles on or off by using the Enter key.
When you use a keyboard to select a Look, dashboard, or folder that's inside a folder, a focus ring will appear around the selected item.
You can now use a keyboard to edit boards.
You can now use the keyboard to access LookML field definitions in the field picker.
The Alerts dialog is now compatible with screen readers.
The Series tab of the visualization editor is now compatible with screen readers.
Tile notes are now added to ARIA descriptions.
Actions for pivot columns are now accessible with a keyboard.
The color contrast has been improved on large text boxes such as the custom filter editor.
The options in the visualization settings panel now have names that can be read by screen readers.
The state of expanded dialogs on the Explore page, such as the field picker and visualization settings panel, can now be read by screen readers.
An issue has been fixed where non-string values that were entered in the expression element of the dynamic_fields section of a LookML dashboard could cause the LookML validator to crash. This feature now performs as expected.
An issue has been fixed where the Collapse Subtotal toggle wasn't collapsing subtotals on table visualizations. This feature now performs as expected.
An issue has been fixed where users couldn't sort tables that included pivoted values. This feature now performs as expected.
An issue has been fixed where subtotal values could display incorrect values after a filter was added or updated. This feature now performs as expected.
LookML project parse errors now include the LookML file path as well as the line number of the error.
LookML dashboards that aren't deployed to production can no longer be moved into folders other than the LookML Dashboards folder.
An issue has been fixed where Databricks connections that used OAuth could not be saved if the password field was blank. You can now use OAuth without entering a password on the connections page.
An issue has been fixed where, when dashboard filters were updated, column widths could resize on table visualizations that included pivoted values. This feature now performs as expected.
An issue has been fixed where users were sometimes unable to add line breaks to table calculations. This feature now performs as expected.
The Reduce Filter Queries feature is now generally available on the Admin > Settings page.
The Data History Playback feature is now generally available on the Admin > Settings page.
The API endpoint search_lookml_dashboards is now generally available. This endpoint is similar to the search_dashboards endpoint except that it searches LookML dashboards instead of user-defined dashboards.
The Smart single value text size feature is now generally available on the Admin > General Settings page.
The Prerender iframes for custom visualizations feature is now generally available on the Admin > Content Guardrails page.
Looker admins can no longer create or edit individual users' API keys. Instead, from the Admin > Users page, admins can enable users to manage their own API keys. Once a user has API key management enabled, they can create, view, edit, and delete their API keys from their Looker account page. Note: This item was changed on October 9, 2025 to specify that it supports Looker (Google Cloud core) only, and it was changed again on October 22, 2025 to indicate that it's a breaking change.
The Prerender iframes for custom visualizations feature is now out of Labs and generally available on the Admin > Content Guardrails page.
The API endpoint search_lookml_dashboards is now out of Labs and generally available. This endpoint is similar to the search_dashboards endpoint except that it searches LookML dashboards instead of user-defined dashboards.
The Smart single value text size feature is now out of Labs and generally available on the Admin > General Settings page.
The Reduce Filter Queries Labs feature is now is now out of Labs and generally available on the Admin > Settings page.
The Data History Playback Labs feature is is now out of Labs and generally available on the Admin > Settings page.
For each primary node of a Memorystore for Valkey instance, you can now have up to five replica nodes. For more information, see Memorystore for Valkey overview. This feature is Generally Available.
You can use custom constraints with Organization Policy to provide more granular control over specific fields for some Dataform resources. For more information, see Create custom organization policy constraints. This feature is generally available (GA).
Updated pricing for Vertex AI Agent Engine: Starting on November 6, 2025, Vertex AI Agent Engine Runtime will start charging for runtime usage for the following regions:
asia-southeast1(Singapore)australia-southeast2(Melbourne)europe-west2(London)europe-west3(Frankfurt)europe-west4(Netherlands)
For more details, see Pricing for Vertex AI Agent Engine.
October 05, 2025
Google SecOpsNew parser documentation now available
New parser documentation is available to help you ingest and normalize logs from the following sources:
- Collect AlphaSOC alert logs
- Collect AlphaSOC alert logs
- Collect Cisco vManage SD-WAN logs
- Collect Citrix Analytics logs
- Collect Citrix Monitor Service logs
- Collect Citrix StoreFront logs
- Collect Delinea SSO logs
- Collect SailPoint IAM logs
- Collect Sentry logs
- Collect Snipe-IT logs
- Collect Sophos AV logs
- Collect Sophos Capsule8 logs
- Collect Sophos DHCP logs
- Collect Sophos Intercept EDR logs
- Collect Swimlane Platform logs
- Collect Symantec WSS logs
- Collect Tailscale logs
- Collect Tanium Asset logs
- Collect Tanium audit logs
- Collect Tanium Comply logs
- Collect Tanium Discover logs
- Collect Tanium Insight logs
- Collect Tanium Integrity Monitor logs
- Collect Tanium Patch logs
- Collect Tanium Question logs
- Collect Tanium Reveal logs
- Collect Tanium Stream logs
- Collect Tanium Threat Response logs
- Collect TeamViewer logs
- Collect Tines audit logs
New parser documentation now available
New parser documentation is available to help you ingest and normalize logs from the following sources:
- Collect AlphaSOC alert logs
- Collect AlphaSOC alert logs
- Collect Cisco vManage SD-WAN logs
- Collect Citrix Analytics logs
- Collect Citrix Monitor Service logs
- Collect Citrix StoreFront logs
- Collect Delinea SSO logs
- Collect SailPoint IAM logs
- Collect Sentry logs
- Collect Snipe-IT logs
- Collect Sophos AV logs
- Collect Sophos Capsule8 logs
- Collect Sophos DHCP logs
- Collect Sophos Intercept EDR logs
- Collect Swimlane Platform logs
- Collect Symantec WSS logs
- Collect Tailscale logs
- Collect Tanium Asset logs
- Collect Tanium audit logs
- Collect Tanium Comply logs
- Collect Tanium Discover logs
- Collect Tanium Insight logs
- Collect Tanium Integrity Monitor logs
- Collect Tanium Patch logs
- Collect Tanium Question logs
- Collect Tanium Reveal logs
- Collect Tanium Stream logs
- Collect Tanium Threat Response logs
- Collect TeamViewer logs
- Collect Tines audit logs
New parser documentation now available
New parser documentation is available to help you ingest and normalize logs from the following sources:
- Collect AlphaSOC alert logs
- Collect AlphaSOC alert logs
- Collect Cisco vManage SD-WAN logs
- Collect Citrix Analytics logs
- Collect Citrix Monitor Service logs
- Collect Citrix StoreFront logs
- Collect Delinea SSO logs
- Collect SailPoint IAM logs
- Collect Sentry logs
- Collect Snipe-IT logs
- Collect Sophos AV logs
- Collect Sophos Capsule8 logs
- Collect Sophos DHCP logs
- Collect Sophos Intercept EDR logs
- Collect Swimlane Platform logs
- Collect Symantec WSS logs
- Collect Tailscale logs
- Collect Tanium Asset logs
- Collect Tanium audit logs
- Collect Tanium Comply logs
- Collect Tanium Discover logs
- Collect Tanium Insight logs
- Collect Tanium Integrity Monitor logs
- Collect Tanium Patch logs
- Collect Tanium Question logs
- Collect Tanium Reveal logs
- Collect Tanium Stream logs
- Collect Tanium Threat Response logs
- Collect TeamViewer logs
- Collect Tines audit logs
Release 6.3.63 is being rolled out to the first phase of regions as listed here.
This release contains internal and customer bug fixes.
Release 6.3.63 is being rolled out to the first phase of regions as listed here.
This release contains internal and customer bug fixes.
October 04, 2025
Google SecOps SIEMRelease 6.3.62 is now available for all regions.
Release 6.3.62 is now available for all regions.
October 03, 2025
Access ApprovalNCC Gateway is available in Preview.
NCC Gateway is available in Preview.
Preview: Capacity Planner supports the following:
- Usage and forecast data for Hyperdisk volumes
- Usage and forecast data for Persistent Disk and Hyperdisk volume IOPS and throughput
- Usage data for Spot VMs
For more information, see View usage and forecast data.
Cloud SQL for PostgreSQL now supports PostgreSQL version 18 in Preview.
PostgreSQL 18 is a newly supported version. We strongly recommend that you review the changes in the release and validate the readiness of your instance thoroughly prior to upgrading your instance to this version.
The following information applies to flags and extensions for PostgreSQL 18:
Flags
The following new flags are available for PostgreSQL 18 only:
autovacuum_vacuum_max_thresholdautovacuum_worker_slotsenable_distinct_reorderingenable_self_join_elimitationio_max_concurrencyio_methodio_workerslog_lock_failuresmax_active_replecation_originstrack_cost_delay_timingvacuum_max_eager_freeze_failure_ratevacuum_truncate
For more information, see Configure database flags.
Extensions
The following extensions aren't available for PostgreSQL 18:
pgRoutingplpgsql_checkpg_hint_planpgroutinganonymizerpg_wait_samplingtds_fdw
For more information, see Configure PostgreSQL extensions.
To create a new instance using PostgreSQL 18, see Create instances.
New Confidential Space images (251000 and 251001) are now available.
New Dataproc on Compute Engine subminor image versions:
- 2.0.150-debian10, 2.0.150-ubuntu18, 2.0.150-rocky8
- 2.1.99-debian11, 2.1.99-ubuntu20, 2.1.99-ubuntu20-arm, 2.1.99-rocky8
- 2.2.67-debian12, 2.2.67-ubuntu22, 2.2.67-ubuntu22-arm, 2.2.67-rocky9
- 2.3.14-debian12, 2.3.14-ubuntu22, 2.3.14-ubuntu22-arm, 2.3.14-ml-ubuntu22, 2.3.14-rocky9
Bug fixes in VS Code
Various bug fixes and minor product enhancements.
Prompt management
Vertex AI offers tooling to help manage prompts and prompt versions. In addition to the prompt management capabilities in Vertex AI Studio, prompts can be stored and versioned using the Vertex AI SDK.
For more information, see the Prompt management API reference.
This is to notify you about upcoming changes in licensing model with Google Cloud VMware Engine following Broadcom's recent announcement to move to a "bring your own" subscription model for VMware Cloud Foundation (VCF).
You can renew or add additional capacity of VMware Engine nodes with VCF-license included until October 15, 2025. After that, Google Cloud will not be able to sell new VMware Engine VCF license-included nodes. You can buy new VMware Engine BYOL nodes and use them with "bring your own" VCF subscriptions (purchased by you from Broadcom) for new capacity after October 15, 2025.
For any questions, please reach out to your Google Cloud sales team, who can help review your specific scenarios, discuss the implications of these changes for your organization, and help you manage this transition.
For more details, see the October 3, 2025 service announcement.
Customer-managed encryption key compliance now includes support for data tables
Google SecOps has expanded its coverage of Customer-Managed Encryption Key (CMEK) compliance to now include support for data tables.
For more information, see CMEK for Google SecOps.
Customer-managed encryption key compliance now includes support for data tables
Google SecOps has expanded its coverage of Customer-Managed Encryption Key (CMEK) compliance to now include support for data tables.
For more information, see CMEK for Google SecOps.
Customer-managed encryption key compliance now includes support for data tables
Google SecOps has expanded its coverage of Customer-Managed Encryption Key (CMEK) compliance to now include support for data tables.
For more information, see CMEK for Google SecOps.
Select Workload Identity Federation resources let you use custom constraints to define your own restrictions on Google Cloud services. To learn which Workload Identity Federation resources support custom constraints and to view sample use cases, see Use custom organization policies for Workload Identity Federation.
This feature is available in General Availability.
New SAP certification for operating system: RHEL for SAP 9.6
For use with SAP HANA and SAP NetWeaver on Google Cloud, SAP has certified the operating system Red Hat Enterprise Linux (RHEL) for SAP 9.6.
For more information about SAP-certified operating systems, see:
October 02, 2025
Apigee Advanced API SecurityOn October 2, 2025 we released an updated version of Advanced API Security Abuse Detection
Note: Rollouts of this release to production instances will begin within two business days and may take four or more business days to complete across all Google Cloud zones. Your instances may not have the feature available until the rollout is complete.
Introduction of exclusion lists for Abuse Detection and incidents
You can now specify CIDR ranges and IP addresses to exclude from future incident reports. Use this feature to exclude traffic known to be safe, such as requests related to automated testing.
The new functionality includes the ability to create and manage multiple "exclusion lists" which define traffic to exclude and the reasons it is excluded.
Note: Exclusion lists are not available for VPC-SC customers at this time.
For usage information, see Exclude traffic from abuse detection in the documentation.
You can now use the notebook gallery in the BigQuery web UI as your central hub for discovering and using prebuilt notebook templates. This feature is in preview.
Application Monitoring is now generally available (GA). Application Monitoring lets you monitor the resources and infrastructure from the perspective of an App Hub application. The out-of-the-box dashboards that Application Monitoring creates can help you understand how your application's resources are performing, and they can help you diagnose issues.
- Application Monitoring overview provides a brief overview of this feature.
- Set up application monitoring describes how to configure an observability scope so that you have an aggregated view of your log, metric, and trace data.
- View application telemetry describes the labels attached to your telemetry data and provides guidance about how to explore the OOTB dashboards.
- Supported infrastructure.
Version 20250930.01 of the guest agent, which introduces the plugin-based
architecture to Debian 11, is now available.
For more information about the plugin-based architecture, see Guest agent.
Gemini Code Assist tools are deprecated and replaced by agent mode (Preview)
Gemini Code Assist tools are deprecated and will be removed on October 14, 2025.
Gemini Code Assist tools are replaced by Gemini Code Assist agent mode. After
October 14, 2025, using the @ symbol followed by the name of a tool won't
connect to Gemini Code Assist tools.
Agent mode in Gemini Code Assist can connect to external services using Model Context Protocol (MCP) servers. For more information, read Configure MCP servers.
Gemini Code Assist tools are deprecated and replaced by agent mode
Gemini Code Assist tools are deprecated and will be removed on October 14, 2025.
Gemini Code Assist tools are replaced by Gemini Code Assist agent mode. After
October 14, 2025, using the @ symbol followed by the name of a tool won't
connect to Gemini Code Assist tools.
Agent mode in Gemini Code Assist can connect to external services using Model Context Protocol (MCP) servers. For more information, read Configure MCP servers.
Gemini Enterprise: Configure prompt chips
You can create, delete, edit, and enable or disable Google-provided and custom prompts that provide better guidance to your users.
For more information, see Configure prompt chips.
Gemini Enterprise: Generate images using Nano Banana
Image generation and editing with Nano Banana (Gemini 2.5 Flash Image) is Generally Available (GA) in Gemini Enterprise across Global, EU, and US multi-regions.
For more information on generating images, see Generate an image.
Gemini 2.5 Flash Image (gemini-2.5-flash-image) is now generally available. This GA release adds support for aspect ratio controls, image-only response modality, regional endpoints, support for batch predictions, image generation from multiple reference images, and improved multi-turn image editing.
See Gemini 2.5 Flash Image for more information.
Google Gen AI SDK in C# Preview
Preview: The Google Gen AI SDK is available in C#. See googleapis/dotnet-genai.
This release includes support for GenerateContentAsync, GenerateContentStreamAsync, GenerateImagesAsync, and three Live APIs, which includes SendClientContentAsync, SendRealtimeInputAsync, and SendToolResponseAsync.
The following issues were fixed in 1.33.100-gke.89:
- Fixed vulnerabilities listed in Vulnerability fixes.
Google Distributed Cloud (software only) for VMware 1.33.100-gke.89 is now available for download. To upgrade, see Upgrade a cluster. Distributed Cloud 1.33.100-gke.89 runs on Kubernetes v1.33.4-gke.900.
If you are using a third-party storage vendor, check the GDC Ready storage partners document to make sure the storage vendor has already passed the qualification for this release.
After a release, it takes approximately 7 to 14 days for the version to become available for use with GKE On-Prem API clients: the Google Cloud console, the gcloud CLI, and Terraform.
The following issues were fixed in 1.33.100-gke.89:
Fixed an issue where the cluster restore process leaves the Kubelet certificate files as regular files instead of symbolic links, preventing certificate rotation.
Fixed the
etcd-cleanupjob timeout issue caused by the use of incorrect certificates.This patch release doesn't include new fixes for specific, externally-cited vulnerabilities.
Google Distributed Cloud for bare metal 1.33.100-gke.89 is now available for download. To upgrade, see Upgrade clusters. Distributed Cloud for bare metal 1.33.100-gke.89 runs on Kubernetes v1.33.4-gke.900.
After a release, it takes approximately 7 to 14 days for the version to become available for installations or upgrades with the GKE On-Prem API clients: the Google Cloud console, the gcloud CLI, and Terraform.
If you use a third-party storage vendor, check the Ready storage partners document to make sure the storage vendor has already passed the qualification for this release of Distributed Cloud for bare metal.
For information about the latest known issues, see Google Distributed Cloud for bare metal known issues in the Troubleshooting section.
(2025-R41) Version updates
- Version 1.33.4-gke.1245000 is now the default version for cluster creation in the Extended channel.
- The following versions are now available in the Extended channel:
- The following versions are no longer available in the Extended channel:
- 1.28.15-gke.2610000
- 1.28.15-gke.2730000
- 1.29.15-gke.1835000
- 1.29.15-gke.1971000
- 1.30.14-gke.1130000
- 1.31.12-gke.1110000
- 1.32.8-gke.1134000
- 1.33.4-gke.1172000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.27 to version 1.28.15-gke.2630000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.28 to version 1.28.15-gke.2630000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.29 to version 1.29.15-gke.1851000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.30 to version 1.30.14-gke.1150000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.32 to version 1.32.8-gke.1170000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.33 to version 1.33.4-gke.1245000 with this release.
(2025-R41) Version updates
- Version 1.33.4-gke.1245000 is now the default version for cluster creation.
- The following versions are now available:
- The following node versions are now available:
- The following versions are no longer available:
- 1.30.14-gke.1059000
- 1.31.12-gke.1110000
- 1.32.6-gke.1025000
- 1.33.3-gke.1136000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled will be upgraded from version 1.29 to version 1.30.14-gke.1150000 with this release.
- Control planes and nodes with auto-upgrade enabled will be upgraded from version 1.31 to version 1.32.8-gke.1108000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled will be upgraded from version 1.30 to version 1.30.14-gke.1150000 with this release.
- Control planes and nodes with auto-upgrade enabled will be upgraded from version 1.32 to version 1.32.8-gke.1108000 with this release.
- Control planes and nodes with auto-upgrade enabled will be upgraded from version 1.33 to version 1.33.4-gke.1245000 with this release.
(2025-R41) Version updates
- Version 1.34.0-gke.2201000 is now the default version for cluster creation in the Rapid channel.
- The following versions are now available in the Rapid channel:
- The following versions are no longer available in the Rapid channel:
- 1.31.12-gke.1110000
- 1.32.8-gke.1170000
- 1.34.0-gke.1662000
- 1.34.0-gke.2011000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.30 to version 1.31.12-gke.1220000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.31 to version 1.32.9-gke.1010000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.31 to version 1.31.12-gke.1220000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.32 to version 1.32.9-gke.1010000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.34 to version 1.34.0-gke.2201000 with this release.
(2025-R41) Version updates
- Version 1.33.4-gke.1245000 is now the default version for cluster creation in the Regular channel.
- The following versions are now available in the Regular channel:
- The following versions are no longer available in the Regular channel:
- 1.30.14-gke.1130000
- 1.31.12-gke.1110000
- 1.32.8-gke.1134000
- 1.33.4-gke.1172000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.29 to version 1.30.14-gke.1150000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.31 to version 1.32.8-gke.1170000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.32 to version 1.33.4-gke.1245000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.30 to version 1.30.14-gke.1150000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.32 to version 1.32.8-gke.1170000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.33 to version 1.33.4-gke.1245000 with this release.
(2025-R41) Version updates
- Version 1.33.4-gke.1134000 is now the default version for cluster creation in the Stable channel.
- The following versions are now available in the Stable channel:
- The following versions are no longer available in the Stable channel:
- 1.30.14-gke.1059000
- 1.32.6-gke.1060000
- 1.33.3-gke.1136000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled in the Stable channel will be upgraded from version 1.29 to version 1.30.14-gke.1108000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Stable channel will be upgraded from version 1.31 to version 1.32.8-gke.1108000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled in the Stable channel will be upgraded from version 1.30 to version 1.30.14-gke.1108000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Stable channel will be upgraded from version 1.32 to version 1.32.8-gke.1108000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Stable channel will be upgraded from version 1.33 to version 1.33.4-gke.1134000 with this release.
(2025-R41) Version updates
GKE cluster versions have been updated.
New versions available for upgrades and new clusters.
The following versions are now available for new GKE clusters, and for manual control plane upgrades and node upgrades for existing clusters. For more information about versioning and upgrades, see GKE versioning and support and About GKE cluster upgrades.
Rapid channel
- Version 1.34.0-gke.2201000 is now the default version for cluster creation in the Rapid channel.
- The following versions are now available in the Rapid channel:
- The following versions are no longer available in the Rapid channel:
- 1.31.12-gke.1110000
- 1.32.8-gke.1170000
- 1.34.0-gke.1662000
- 1.34.0-gke.2011000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.30 to version 1.31.12-gke.1220000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.31 to version 1.32.9-gke.1010000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.31 to version 1.31.12-gke.1220000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.32 to version 1.32.9-gke.1010000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.34 to version 1.34.0-gke.2201000 with this release.
Regular channel
- Version 1.33.4-gke.1245000 is now the default version for cluster creation in the Regular channel.
- The following versions are now available in the Regular channel:
- The following versions are no longer available in the Regular channel:
- 1.30.14-gke.1130000
- 1.31.12-gke.1110000
- 1.32.8-gke.1134000
- 1.33.4-gke.1172000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.29 to version 1.30.14-gke.1150000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.31 to version 1.32.8-gke.1170000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.32 to version 1.33.4-gke.1245000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.30 to version 1.30.14-gke.1150000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.32 to version 1.32.8-gke.1170000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.33 to version 1.33.4-gke.1245000 with this release.
Stable channel
- Version 1.33.4-gke.1134000 is now the default version for cluster creation in the Stable channel.
- The following versions are now available in the Stable channel:
- The following versions are no longer available in the Stable channel:
- 1.30.14-gke.1059000
- 1.32.6-gke.1060000
- 1.33.3-gke.1136000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled in the Stable channel will be upgraded from version 1.29 to version 1.30.14-gke.1108000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Stable channel will be upgraded from version 1.31 to version 1.32.8-gke.1108000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled in the Stable channel will be upgraded from version 1.30 to version 1.30.14-gke.1108000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Stable channel will be upgraded from version 1.32 to version 1.32.8-gke.1108000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Stable channel will be upgraded from version 1.33 to version 1.33.4-gke.1134000 with this release.
Extended channel
- Version 1.33.4-gke.1245000 is now the default version for cluster creation in the Extended channel.
- The following versions are now available in the Extended channel:
- The following versions are no longer available in the Extended channel:
- 1.28.15-gke.2610000
- 1.28.15-gke.2730000
- 1.29.15-gke.1835000
- 1.29.15-gke.1971000
- 1.30.14-gke.1130000
- 1.31.12-gke.1110000
- 1.32.8-gke.1134000
- 1.33.4-gke.1172000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.27 to version 1.28.15-gke.2630000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.28 to version 1.28.15-gke.2630000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.29 to version 1.29.15-gke.1851000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.30 to version 1.30.14-gke.1150000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.32 to version 1.32.8-gke.1170000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.33 to version 1.33.4-gke.1245000 with this release.
No channel
- Version 1.33.4-gke.1245000 is now the default version for cluster creation.
- The following versions are now available:
- The following node versions are now available:
- The following versions are no longer available:
- 1.30.14-gke.1059000
- 1.31.12-gke.1110000
- 1.32.6-gke.1025000
- 1.33.3-gke.1136000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled will be upgraded from version 1.29 to version 1.30.14-gke.1150000 with this release.
- Control planes and nodes with auto-upgrade enabled will be upgraded from version 1.31 to version 1.32.8-gke.1108000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled will be upgraded from version 1.30 to version 1.30.14-gke.1150000 with this release.
- Control planes and nodes with auto-upgrade enabled will be upgraded from version 1.32 to version 1.32.8-gke.1108000 with this release.
- Control planes and nodes with auto-upgrade enabled will be upgraded from version 1.33 to version 1.33.4-gke.1245000 with this release.
Version 20250930.01 of the guest agent, which introduces the plugin-based
architecture to Debian 11, is now available.
For more information about the plugin-based architecture, see Guest agent.
The sql_preamble parameter now supports Liquid statements. This update is supported on Looker 25.12 and later versions.
More data from Google Ads
You can visualize the following fields using the the Google Ads connector:
- Conversions (by conv. date)
- Conv. value (by conv. date)
- All conv. (by conv. date)
- All conv. value (by conv. date)
- New vs. returning customers
- Gross profit
- Gross profit margin
Double-click to resize chart margins
You can now double-click the chart boundaries of a time, a bar, a line, an area, or a scatter chart to reset the boundaries to their default settings.
This is an addition to the May 1 release note announcing the deprecation of the ability to send inspection and discovery results from Sensitive Data Protection to Data Catalog.
If you have workflows that create inspection jobs or job triggers and set the
deprecated
PublishFindingsToCloudDataCatalog
action, you must update those workflows by January 30, 2026. On or after this
date, new jobs and job triggers that are created by those workflows will fail.
You can now use repeatable read isolation (in Preview) to reduce latency and transaction abort rates for workloads that have many reads contending with fewer writes. For more information, see Repeatable read isolation.
Vertex AI Search: Renamed from AI Applications
The AI Applications product has been renamed as Vertex AI Search in the following contexts:
- The documentation set. See What is Vertex AI Search?
- The marketing collateral. See Vertex AI Search.
What has not changed:
- The user interface in the Google Cloud console is still referred to as AI Applications. See AI Applications.
- The APIs still use the DiscoveryEngine API endpoints. See APIs and reference.
Despite the rebrand, the product functionality remains the same.
October 01, 2025
Access ApprovalCertificate Manager is generally available (GA).
Certificate Manager is generally available (GA).
Smart compose is no longer in use and will be permanently removed in October 2025. Refer to Generative smart reply for an alternative.
You can now apply SQL query generated in the Gemini Cloud Assist chat to the query open in your editor. This feature is in Preview.
Cloud Carbon Footprint launched an improved data export experience in the Cloud Carbon console, now available in Experimental Preview.
When you click Data export on the Cloud Carbon console Ul for a given billing account, you can now see Carbon Footprint exports that you have access to for that billing account, in addition to the ability to create a new data export. This feature helps you better manage your Carbon Footprint exports in BigQuery. Read more for details.
In some cases, the list of exports may not be complete for the following reasons:
- Permissions: The export was configured in a project that you don't have permission to view.
- Performance Optimization: To optimize performance and prevent latency when you have access to a very large number of projects, the search may not display exports in all projects.
Cloud Run functions now provides an upgrade tool for upgrading 1st gen functions to Cloud Run. This feature is in Preview.
Support for Kafka Connect is now generally available (GA). Kafka Connect lets you stream data at scale between Managed Service for Apache Kafka clusters and other systems, such as external Kafka deployments, BigQuery, Cloud Storage, or Pub/Sub. For more information, see Kafka Connect overview.
The GKE cluster autoscaler now allows for a significantly longer node drain time. From GKE version 1.32.7-gke.1079000 and later, the graceful node drain timeout has been increased from 10 minutes to 1 hour. For more information, see How cluster autoscaler works.
The InPlaceOrRecreate mode for Vertical Pod Autoscaler (VPA) is now available for Public Preview in GKE.
This mode uses In-Place Pod Resize (IPPR/IPPU), which allows VPA to automatically adjust workload resources, without requiring Pod recreation. This seamless rightsizing capability helps ensure better service continuity and helps minimize costs by optimizing resource allocation, particularly during idle periods.
VPA is enabled by default in Autopilot clusters. For Standard clusters, you must first enable VPA. For more information on configuring a VPA object, see Set Pod resource requests automatically.
The manual QoS feature is now generally available for Google Cloud NetApp Volumes, supporting the Standard, Premium, and Extreme service levels. For more information, see Manual QoS.
Oracle Database@Google Cloud supports customer-managed encryption keys (CMEK) using Cloud Key Management Service. You can enable CMEK on Exadata VM Clusters and Autonomous Databases. This feature is generally available (GA).
The Spanner CLI is generally available. Bundled with gcloud, you can use the Spanner command-line interface to open an interactive session or automate SQL executions from the shell or an input file.
Generally available (GA): You can use Workforce Identity Federation with Vertex AI Workbench instances. Workforce Identity Federation lets you create and manage Vertex AI Workbench instances with credentials provided by an external identity provider (IdP). For more information, see Create an instance with third party credentials.
September 30, 2025
AlloyDB for PostgreSQLYou can enable alloydb.enable_cache_aware_costing to turn on
cache awareness for AlloyDB for PostgreSQL's query planner. This improves index
scan query plans for query performance and reduces IO costs. This feature
is in Preview.
DAG UI now correctly generates error messages about malformed serialized DAG.
The following Cloud Composer versions and builds have reached their end of support period: composer-2.9.4-*, composer-3-airflow-2.9.1 builds from build.0 to build.7, and composer-3-airflow-2.7.3-build.16.
New images are available in Cloud Composer 2:
(Airflow 2.10.5) CloudComposerDAGRunSensor is broken in the
apache-airflow-providers-google package version 17.2.0. This package is used
by Cloud Composer versions and builds with Airflow 2.10.5 available in this
release. If your DAGs use this sensor, we recommend you postpone upgrading
until the issue is resolved.
New Airflow builds are available in Cloud Composer 3:
The GCE_METADATA_TIMEOUT environment variable is changed to reserved. This
change addresses an issue where setting a low timeout value disrupted the
environment's operations that relied on the metadata server.
(Airflow 2.10.5) The apache-airflow-providers-cncf-kubernetes package was
upgraded to version 10.8.0
from version 10.7.0. For changes in other packages, see the
preinstalled packages changelog.
(Airflow 2.10.5) The apache-airflow-providers-google package was upgraded
to version 17.2.0 in Cloud Composer 2 images and Cloud Composer 3 builds.
For more information about changes, see the apache-airflow-providers-google changelog from version 17.1.0 to version 17.2.0.
Alias records are available in GA.
This custom record type provides CNAME-like functionality at the zone apex, mapping the apex domain name to a canonical target.
You can now configure traffic routing using Cloud Service Mesh service routing APIs between Cloud Run and Cloud Run, Google Kubernetes Engine, and Google Compute Engine services. (GA).
Managed Cloud Service Mesh with a TD control plane in the Rapid release channel will start using proxy images with an internal envoy version.
All features supported by Managed (TD) control planes are supported by this proxy. To identify which proxy version is used in a cluster, see Identify the proxy versions used in the cluster.
This release uses the version csm_istio_proxy_20250611.00_p0. More details about the proxy version can be found on the Versions page.
Object contexts are now available in Preview. Object contexts let you attach contextual information to your objects to help you manage and discover data.
Cloud VPN supports customizable cipher options for your VPN tunnels. You can configure ciphers as per your security requirements. This feature is Generally Available.
For more information, see Configure ciphers in Cloud VPN tunnel.
Version 20250930.01 includes the following fixes for issues found in the
plugin-based architecture. For more information about the plugin-based
architecture, see Guest agent.
- Fixes an issue where the networking module incorrectly added routes when
ip_forwardingandtarget_instance_ipssettings were disabled in/etc/default/instance_configs.cfg. - Prevents unnecessary error logs in the OS Login module caused by attempts to read a non-existent file.
Datastream support for Salesforce as a source is now generally available (GA). For more information, see the documentation.
DeepSeek-V3.2-Exp is available through Model Garden.
Customize Events table columns in Search
You can now specify which columns appear in the Events table on the
Search page and in tables within your dashboard widgets. Use the select
and unselect keywords to define the displayed columns.
For more information, see Control columns using select and unselect keywords.
Customize Events table columns in Search
You can now specify which columns appear in the Events table on the
Search page and in tables within your dashboard widgets. Use the select
and unselect keywords to define the displayed columns.
For more information, see Control columns using select and unselect keywords.
Customize Events table columns in Search
You can now specify which columns appear in the Events table on the
Search page and in tables within your dashboard widgets. Use the select
and unselect keywords to define the displayed columns.
For more information, see Control columns using select and unselect keywords.
Version 20250930.01 includes the following fixes for issues found in the
plugin-based architecture. For more information about the plugin-based
architecture, see Guest agent.
- Fixes an issue where the networking module incorrectly added routes when
ip_forwardingandtarget_instance_ipssettings were disabled in/etc/default/instance_configs.cfg. - Prevents unnecessary error logs in the OS Login module caused by attempts to read a non-existent file.
The following features are coming soon for use with Conversational Analytics:
New model-specific Looker permissions are available to manage and use the Conversational Analytics data agents that are created to chat with Looker Explores. You can grant these to users as part of a custom role, or use one of two new default roles, Conversational Analytics Agent Manager and Conversational Analytics User, to manage and use agents, respectively.
You can now select up to five Looker Explores as data sources for a data agent.
You can now share data agents to let other users chat with your agent and its Explores.
Network Analyzer no longer generates the following insight types and subtypes:
- Recommender insight type and subtypes:
google.networkanalyzer.managedservices.cloudSqlInsight, includingBLOCKED_BY_EGRESS_FIREWALL,BLOCKED_BY_ROUTING_ISSUE, andINSTANCE_NOT_RUNNINGCONTROL_PLANE_TO_NODE_BLOCKED_BY_INGRESS_FIREWALLCONTROL_PLANE_TO_NODE_BLOCKED_BY_ROUTING_ISSUEEXTERNAL_IP_UNASSIGNEDMISSING_ROUTES_TO_GOOGLE_APIS_AND_SERVICESPRIVATE_GOOGLE_ACCESS_DISABLED
- Cloud Logging insight types:
CLOUD_SQL_PRIVATE_IP_BLOCKED_BY_EGRESS_FIREWALLCLOUD_SQL_PRIVATE_IP_BLOCKED_BY_ROUTING_ISSUECLOUD_SQL_PRIVATE_IP_INSTANCE_NOT_RUNNINGGKE_CONTROL_PLANE_TO_NODE_BLOCKED_BY_INGRESS_FIREWALL_ON_NODEGKE_CONTROL_PLANE_TO_NODE_BLOCKED_BY_ROUTING_ISSUE
A monthly digest of client library updates from across the Cloud SDK.
Go
Changes for spanner/admin/database/apiv1
1.86.0 (2025-09-26)
Features
Bug Fixes
1.85.0 (2025-08-28)
Features
Performance Improvements
1.85.1 (2025-09-12)
Bug Fixes
Documentation
- spanner: A comment for enum Kind is changed (51583bd)
- spanner: A comment for enum Priority is changed (51583bd)
- spanner: A comment for enum value LOCK_HINT_EXCLUSIVE in enum LockHint is changed (51583bd)
- spanner: A comment for enum value LOCK_HINT_UNSPECIFIED in enum LockHint is changed (51583bd)
- spanner: A comment for enum value ORDER_BY_PRIMARY_KEY in enum OrderBy is changed (51583bd)
- spanner: A comment for enum value ORDER_BY_UNSPECIFIED in enum OrderBy is changed (51583bd)
- spanner: A comment for enum value PROFILE in enum QueryMode is changed (51583bd)
- spanner: A comment for enum value SERIALIZABLE in enum IsolationLevel is changed (51583bd)
- spanner: A comment for field approximate_last_use_time in message .google.spanner.v1.Session is changed (51583bd)
- spanner: A comment for field auto_failover_disabled in message .google.spanner.v1.DirectedReadOptions is changed (51583bd)
- spanner: A comment for field columns in message .google.spanner.v1.Mutation is changed (51583bd)
- spanner: A comment for field data_boost_enabled in message .google.spanner.v1.ExecuteSqlRequest is changed (51583bd)
- spanner: A comment for field data_boost_enabled in message .google.spanner.v1.ReadRequest is changed (51583bd)
- spanner: A comment for field exclude_replicas in message .google.spanner.v1.DirectedReadOptions is changed (51583bd)
- spanner: A comment for field exclude_txn_from_change_streams in message .google.spanner.v1.BatchWriteRequest is changed (51583bd)
- spanner: A comment for field include_replicas in message .google.spanner.v1.DirectedReadOptions is changed (51583bd)
- spanner: A comment for field index in message .google.spanner.v1.PlanNode is changed (51583bd)
- spanner: A comment for field insert_or_update in message .google.spanner.v1.Mutation is changed (51583bd)
- spanner: A comment for field key_set in message .google.spanner.v1.Mutation is changed (51583bd)
- spanner: A comment for field key_set in message .google.spanner.v1.PartitionReadRequest is changed (51583bd)
- spanner: A comment for field key_set in message .google.spanner.v1.ReadRequest is changed (51583bd)
- spanner: A comment for field kind in message .google.spanner.v1.PlanNode is changed (51583bd)
- spanner: A comment for field last_statement in message .google.spanner.v1.ExecuteSqlRequest is changed (51583bd)
- spanner: A comment for field last_statements in message .google.spanner.v1.ExecuteBatchDmlRequest is changed (51583bd)
- spanner: A comment for field limit in message .google.spanner.v1.ReadRequest is changed (51583bd)
- spanner: A comment for field location in message .google.spanner.v1.DirectedReadOptions is changed (51583bd)
- spanner: A comment for field max_commit_delay in message .google.spanner.v1.CommitRequest is changed (51583bd)
- spanner: A comment for field max_partitions in message .google.spanner.v1.PartitionOptions is changed (51583bd)
- spanner: A comment for field multiplexed in message .google.spanner.v1.Session is changed (51583bd)
- spanner: A comment for field mutation_key in message .google.spanner.v1.BeginTransactionRequest is changed (51583bd)
- spanner: A comment for field optimizer_statistics_package in message .google.spanner.v1.ExecuteSqlRequest is changed (51583bd)
- spanner: A comment for field optimizer_version in message .google.spanner.v1.ExecuteSqlRequest is changed (51583bd)
- spanner: A comment for field order_by in message .google.spanner.v1.ReadRequest is changed (51583bd)
- spanner: A comment for field param_types in message .google.spanner.v1.ExecuteBatchDmlRequest is changed (51583bd)
- spanner: A comment for field param_types in message .google.spanner.v1.ExecuteSqlRequest is changed (51583bd)
- spanner: A comment for field param_types in message .google.spanner.v1.PartitionQueryRequest is changed (51583bd)
- spanner: A comment for field params in message .google.spanner.v1.ExecuteBatchDmlRequest is changed (51583bd)
- spanner: A comment for field params in message .google.spanner.v1.ExecuteSqlRequest is changed (51583bd)
- spanner: A comment for field params in message .google.spanner.v1.PartitionQueryRequest is changed (51583bd)
- spanner: A comment for field partition_size_bytes in message .google.spanner.v1.PartitionOptions is changed (51583bd)
- spanner: A comment for field partition_token in message .google.spanner.v1.ExecuteSqlRequest is changed (51583bd)
- spanner: A comment for field partition_token in message .google.spanner.v1.Partition is changed (51583bd)
- spanner: A comment for field partition_token in message .google.spanner.v1.ReadRequest is changed (51583bd)
- spanner: A comment for field plan_nodes in message .google.spanner.v1.QueryPlan is changed (51583bd)
- spanner: A comment for field precommit_token in message .google.spanner.v1.CommitRequest is changed (51583bd)
- spanner: A comment for field precommit_token in message .google.spanner.v1.ExecuteBatchDmlResponse is changed (51583bd)
- spanner: A comment for field ranges in message .google.spanner.v1.KeySet is changed (51583bd)
- spanner: A comment for field replace in message .google.spanner.v1.Mutation is changed (51583bd)
- spanner: A comment for field request_options in message .google.spanner.v1.BeginTransactionRequest is changed (51583bd)
- spanner: A comment for field request_tag in message .google.spanner.v1.RequestOptions is changed (51583bd)
- spanner: A comment for field return_commit_stats in message .google.spanner.v1.CommitRequest is changed (51583bd)
- spanner: A comment for field seqno in message .google.spanner.v1.ExecuteBatchDmlRequest is changed (51583bd)
- spanner: A comment for field seqno in message .google.spanner.v1.ExecuteSqlRequest is changed (51583bd)
- spanner: A comment for field session_count in message .google.spanner.v1.BatchCreateSessionsRequest is changed (51583bd)
- spanner: A comment for field session_template in message .google.spanner.v1.BatchCreateSessionsRequest is changed (51583bd)
- spanner: A comment for field short_representation in message .google.spanner.v1.PlanNode is changed (51583bd)
- spanner: A comment for field single_use_transaction in message .google.spanner.v1.CommitRequest is changed (51583bd)
- spanner: A comment for field sql in message .google.spanner.v1.PartitionQueryRequest is changed (51583bd)
- spanner: A comment for field transaction in message .google.spanner.v1.ExecuteSqlRequest is changed (51583bd)
- spanner: A comment for field transaction in message .google.spanner.v1.PartitionQueryRequest is changed (51583bd)
- spanner: A comment for field transaction_tag in message .google.spanner.v1.RequestOptions is changed (51583bd)
- spanner: A comment for field values in message .google.spanner.v1.Mutation is changed (51583bd)
- spanner: A comment for field variable in message .google.spanner.v1.PlanNode is changed (51583bd)
- spanner: A comment for message DirectedReadOptions is changed (51583bd)
- spanner: A comment for message DirectedReadOptions is changed (51583bd)
- spanner: A comment for message DirectedReadOptions is changed (51583bd)
- spanner: A comment for message Mutation is changed (51583bd)
- spanner: A comment for message PartitionOptions is changed (51583bd)
- spanner: A comment for message PlanNode is changed (51583bd)
- spanner: A comment for method BatchWrite in service Spanner is changed (51583bd)
- spanner: A comment for method Commit in service Spanner is changed (51583bd)
- spanner: A comment for method CreateSession in service Spanner is changed (51583bd)
- spanner: A comment for method DeleteSession in service Spanner is changed (51583bd)
- spanner: A comment for method ExecuteSql in service Spanner is changed (51583bd)
- spanner: A comment for method ExecuteStreamingSql in service Spanner is changed (51583bd)
- spanner: A comment for method GetSession in service Spanner is changed (51583bd)
- spanner: A comment for method PartitionQuery in service Spanner is changed (51583bd)
- spanner: A comment for method PartitionRead in service Spanner is changed (51583bd)
- spanner: A comment for method Read in service Spanner is changed (51583bd)
- spanner: A comment for method Rollback in service Spanner is changed (51583bd)
Java
Changes for google-cloud-spanner
6.99.0 (2025-08-26)
Features
Bug Fixes
- deps: Update the Java code generator (gapic-generator-java) to 2.62.0 (52c68db)
- GetCommitResponse() should return error if tx has not committed (#4021) (a2c179f)
Dependencies
6.100.0 (2025-09-11)
Features
Bug Fixes
- deps: Update the Java code generator (gapic-generator-java) to 2.62.1 (e9773a7)
- Disable afe_connectivity_error_count metric (#4041) (f89c1c0)
- Skip session delete in case of multiplexed sessions (#4029) (8bcb09d)
Dependencies
Documentation
- A comment for field
rangesin message.google.spanner.v1.KeySetis changed (e9773a7)
6.101.1 (2025-09-26)
Bug Fixes
6.101.0 (2025-09-26)
Features
Bug Fixes
- deps: Update the Java code generator (gapic-generator-java) to 2.62.2 (8d6cbf6)
- Potential NullPointerException in Value#hashCode (#4046) (74abb34)
- Recalculate remaining statement timeout after retry (#4053) (5e26596)
Dependencies
Node.js
Changes for @google-cloud/spanner
8.2.0 (2025-08-26)
Features
- spanner: Add support for multiplexed session for r/w transactions (#2351) (6a9f1a2)
- spanner: Support setting read lock mode (#2388) (bd66f61)
Bug Fixes
- deps: Add uuid to dependencies (#2376) (0b2060b)
- deps: Update dependency @grpc/proto-loader to ^0.8.0 (#2354) (75dc4da)
- deps: Update dependency google-gax to v5.0.1 (#2362) (9223470)
- Provide option to disable built in metrics (#2380) (b378e2e)
- Race condition among transactions when running parallely (#2369) (f8b6f63)
8.2.1 (2025-09-12)
Bug Fixes
Python
Changes for google-cloud-spanner
3.58.0 (2025-09-10)
Features
Dependencies
Gemini-TTS is generally available (GA) and provides support for 30 voices and over 70 locales. You can synthesize single or multi-speaker speech from short snippets to long-form narratives. You can precisely dictate style, accent, pace, tone, and even emotional expression using natural-language prompts.
For more information, see Gemini TTS. Give it a try in Media Studio.
DeepSeek-V3.2-Exp is available through Model Garden.
September 29, 2025
AlloyDB for PostgreSQLThe alloydb_scann extension version 0.1.3 is updated to include the following vector search improvements in (Preview):
- You can now automatically create ScaNN indexes that are optimized for search performance or for a balance between index build times and search performance with the auto index feature.
- AlloyDB AI's adaptive filtering for filtered vector searches now dynamically switches between pre-filtering and inline filtering. This enhancement further optimizes query performance by allowing the query optimizer to dynamically choose the most efficient filtering strategy. For more information, see Activate adaptive filtering in AlloyDB AI.
- AlloyDB AI now integrates ScaNN indexes with the columnar engine. You can now accelerate your vector similarity search by loading ScaNN indexes into the columnar engine.
- The
alloydb_scannextension now provides a satisfy limit feature that improves query recall for vector searches. If a search returns fewer results than specified in theLIMITclause, the scan continues until theLIMITis met or a configured upper bound is reached. To enable this feature, set thescann.satisfy_limitflag torelaxed order. You can also use thescann.max_pct_leaves_to_searchflag to configure the upper bound for the search. - You can enable vector search index recommendations for Scalable Nearest Neighbors (ScaNN) indexes using the AlloyDB index advisor. For more information, see Use the AlloyDB index advisor with query insights or View the index advisor's index recommendations.
You can configure automatic index maintenance using the following flags:
scann.max_background_workersflag to control the number of background workers and increase throughput across multiple indexes.scann.maintenance_background_naptime_sflag to control the minimum delay between maintenance runs.
hybrid v1.14.3
On September 29, 2025 we released an updated version of the Apigee hybrid software, 1.14.3.
- For information on upgrading, see Upgrading Apigee hybrid to version 1.14.
- For information on new installations, see The big picture.
| Bug ID | Description |
|---|---|
| 451841788 | Apigee hybrid required the mintTaskScheduler.serviceAccountPath property even when Monetization was not enabled. |
| 451375397 | The apigee-pull-push.sh script could return a "No such image" error message. |
| 423597917 | Post of an AppGroupAppKey scopes should result in insert operation instead of update. |
| 420675540 | Fixed Cassandra based replication for runtime contracts in synchronizer. |
| 416634326 | Presence of istio.io Custom Resource Definitions (CRDs) in an Apigee hybrid cluster could cause failure in apigee-ingressgateway-manager pods. |
| 414499328 | ApigeeTelemetry could become stuck in creating state |
| 412740465 | Fixed issue where zipkin headers were not generated by Apigee Ingress Gateway. |
| 409048431 | Fixes a vulnerability which could allow a SAML signature verification to be bypassed. |
| 395272878 | Separate Forward proxy support for googleapis.com and non-googleapis.com runtime traffic. |
| 378686709 | The use of wildcards (*) in Apigee proxy basepaths would conflict with other explicit basepaths, resulting in a 404 error. To apply this fix, follow the procedure in Known issue 378686709. |
| 367815792 | Two new Flow Variables: app_group_app and app_group_name have been added to VerifyApiKey and Access Token policy. |
| Bug ID | Description |
|---|---|
| 433952146 | Security fix. This addresses the following vulnerability: |
| 433951774 | Security fix. This addresses the following vulnerability: |
| 433950558 | Security fix. This addresses the following vulnerability: |
| 433950370 | Security fix. This addresses the following vulnerability: |
| N/A | Security fixes for apigee-asm-ingress. This addresses the following vulnerability: |
| N/A | Security fixes for apigee-asm-istiod. This addresses the following vulnerability: |
| N/A | Security fixes for apigee-envoy. This addresses the following vulnerability: |
| N/A | Security fixes for apigee-fluent-bit. This addresses the following vulnerabilities: |
| N/A | Security fixes for apigee-hybrid-cassandra. This addresses the following vulnerabilities: |
| N/A | Security fixes for apigee-hybrid-cassandra-client. This addresses the following vulnerability: |
| N/A | Security fixes for apigee-kube-rbac-proxy. This addresses the following vulnerability: |
| N/A | Security fixes for apigee-mart-server. This addresses the following vulnerabilities: |
| N/A | Security fixes for apigee-operators. This addresses the following vulnerability: |
| N/A | Security fixes for apigee-stackdriver-logging-agent. This addresses the following vulnerabilities:
|
| N/A | Security fixes for apigee-watcher. This addresses the following vulnerability: |
You can now create BigQuery non-incremental materialized views over Spanner data to improve query performance by periodically caching results. This feature is in Preview.
To simplify access management for your Iceberg tables, you can use credential vending mode with the Apache Iceberg REST catalog in BigLake metastore. Credential vending removes the need for catalog users to have direct access to Cloud Storage buckets. This feature is in Preview.
BigQuery data preparation supports unnesting arrays, which expands each array element into its own row for easier analysis. For more information, see Unnest arrays. This feature is generally available (GA).
History-based query optimizations are now enabled by default. If history-based optimizations have been previously disabled, you can re-enable history-based optimizations for your project or organization.
A weekly digest of client library updates from across the Cloud SDK.
Java
Changes for google-cloud-bigtable
2.67.0 (2025-09-24)
Features
- Idle channel eviction (#2651) (70c05c9)
- Load balancing options for BigtableChannelPool (#2667) (5adaa84)
Bug Fixes
- Add missing break; to PROTO and ENUM value type check (#2672) (337e432)
- Remove beta api annotation for query paginator (#2660) (f68a1fa)
Dependencies
Developer Connect build triggers are now generally available.
You can now create build triggers that build from repositories connected to Developer Connect using the Google Cloud Console, gcloud, the Cloud Build API, and Terraform.
VPC Service Controls support for Cloud Scheduler jobs has been extended to Google Cloud APIs that are VPC Service Controls-compliant. For more information, see Secure cron jobs with VPC Service Controls.
| CVE | CNI | MDP Controller |
| CVE-2025-4802 | Yes | Yes |
| CVE-2023-29383 | Yes | Yes |
| CVE-2024-56406 | Yes | Yes |
| CVE-2023-7008 | Yes | Yes |
| CVE-2025-1377 | Yes | Yes |
| CVE-2023-4039 | Yes | Yes |
| CVE-2025-46836 | Yes | Yes |
| CVE-2023-50495 | Yes | Yes |
| CVE-2025-4598 | Yes | Yes |
| CVE-2025-3576 | Yes | Yes |
| CVE-2025-30258 | Yes | Yes |
| CVE-2017-11164 | Yes | Yes |
| CVE-2022-41409 | Yes | Yes |
| CVE-2025-1372 | Yes | Yes |
| CVE-2022-27943 | Yes | Yes |
| CVE-2022-4899 | Yes | Yes |
| CVE-2023-34969 | Yes | Yes |
| CVE-2023-45918 | Yes | Yes |
CNI/managed data plane controller version 1.23.6-asm.15 is rolling out to all release channels.
A weekly digest of client library updates from across the Cloud SDK.
Go
Changes for storage/internal/apiv2
1.57.0 (2025-09-23)
Features
- storage/control: Add new GetIamPolicy, SetIamPolicy, and TestIamPermissions RPCs (d73f912)
- storage: Post support dynamic key name (#12677) (9e761f9)
- storage: WithMeterProvider allows custom meter provider configuration (#12668) (7f574b0)
Bug Fixes
- storage: Free buffers in Bidi Reader (#12839) (bc247fd)
- storage: Make Writer thread-safe. (#12753) (9ea380b)
- storage: No progress report for oneshot write (#12746) (b97c286)
Performance Improvements
Java
Changes for google-cloud-storage
2.58.0 (2025-09-23)
Features
- storagecontrol: Add GetIamPolicy, SetIamPolicy, and TestIamPermissions RPCs (c884551)
Bug Fixes
- deps: Update the Java code generator (gapic-generator-java) to 2.62.2 (984f8ca)
- Fix appendable upload finalization race condition (#3295) (485be18)
- Fix IllegalMonitorStateException thrown from BlobAppendableUpload.isOpen() (#3302) (aa90468)
- Update object context diff logic to be shallow rather than deep (#3287) (2fd15f6)
Dependencies
cos-beta-125-19216-0-62
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.46 | v27.5.1 | v2.1.3 | See List |
Updated app-admin/node-problem-detector to v0.8.21.
Updated golang.org/x/oauth2, golang.org/x/net, golang.org/x/crypto, and github.com/golang-jwt/jwt/v5 in Docker.
Fixed CVE-2025-39882 in the Linux kernel.
Fixed KCTF-0aeb54a in the Linux Kernel.
Fixed CVE-2025-39884 in the Linux kernel.
Fixed CVE-2025-40300 in the Linux kernel.
Fixed CVE-2025-39881 in the Linux kernel.
Fixed CVE-2025-39883 in the Linux kernel.
cos-dev-129-19290-0-0
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.48 | v27.5.1 | v2.1.3 | See List |
Updated the Linux kernel to v6.12.48.
Added CPU balloon support for ARM CPUs.
Added support for the fwctl subsystem and the Mellanox fwctl driver for ARM64.
Upgraded sys-auth/pambase to v20250906.
Upgraded app-admin/google-guest-configs to v20250913.00.
Upgraded dev-libs/expat to v2.7.2.
Updated golang.org/x/oauth2, golang.org/x/net, golang.org/x/crypto, and github.com/golang-jwt/jwt/v5 in Docker.
cos-117-18613-339-77
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.105 | v24.0.9 | v1.7.28 | See List |
Updated golang.org/x/crypto, golang.org/x/net, golang.org/x/oauth2, and github.com/golang-jwt/jwt/v4 in Docker.
Updated dev-python/jinja to v3.1.6. This resolves CVE-2024-56326, CVE-2024-56201 and CVE-2025-27516.
Fixed KCTF-0aeb54a in the Linux Kernel.
Fixed CVE-2025-39881 in the Linux kernel.
Fixed CVE-2025-39883 in the Linux kernel.
Fixed CVE-2025-40300 in the Linux kernel.
cos-113-18244-448-58
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.1.151 | v24.0.9 | v1.7.27 | See List |
Added support for NVIDIA driver v580.82.07. Updated all latest driver version and default driver versions for NVIDIA_B200 to v580.82.07.
Updated dev-python/jinja to v3.1.6. This resolves CVE-2024-56326, CVE-2024-56201 and CVE-2025-27516.
Fixed KCTF-0aeb54a in the Linux Kernel.
Fixed CVE-2025-39881 in the Linux kernel.
Fixed CVE-2025-39883 in the Linux kernel.
Fixed CVE-2025-40300 in the Linux kernel.
cos-121-18867-199-80
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.105 | v27.5.1 | v2.0.6 | See List |
Updated golang.org/x/oauth2, golang.org/x/net, golang.org/x/crypto, and github.com/golang-jwt/jwt/v5 in Docker.
Updated dev-python/jinja to v3.1.6. This resolves CVE-2024-56326, CVE-2024-56201 and CVE-2025-27516.
Fixed KCTF-0aeb54a in the Linux Kernel.
Fixed CVE-2025-39881 in the Linux kernel.
Fixed CVE-2025-39883 in the Linux kernel.
Fixed CVE-2025-40300 in the Linux kernel.
Column-level lineage is generally available (GA). The feature provides a granular view of your data by tracking the flow between individual columns within tables. You can perform functions such as root cause analysis, impact analysis, and data source verification for specific columns. Column-level lineage is only supported for BigQuery jobs. For more information about column-level lineage, see Column-level lineage.
Add code snippets to the chat context
You can now select, attach, and direct Gemini to focus on code snippets with IntelliJ Gemini Code Assist. Code snippet selection enables discrete analysis of smaller code blocks instead of entire files.
Add code snippets to the chat context
You can now select, attach, and direct Gemini to focus on code snippets with IntelliJ Gemini Code Assist. Code snippet selection enables discrete analysis of smaller code blocks instead of entire files.
(2025-R40) Version updates
- Version 1.33.4-gke.1172000 is now the default version for cluster creation in the Extended channel.
- The following versions are now available in the Extended channel:
- The following versions are no longer available in the Extended channel:
- 1.28.15-gke.2599000
- 1.28.15-gke.2697000
- 1.29.15-gke.1820000
- 1.29.15-gke.1936000
- 1.30.14-gke.1108000
- 1.31.12-gke.1083000
- 1.32.8-gke.1108000
- 1.33.4-gke.1134000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.27 to version 1.28.15-gke.2610000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.28 to version 1.28.15-gke.2610000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.29 to version 1.29.15-gke.1835000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.30 to version 1.30.14-gke.1130000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.32 to version 1.32.8-gke.1134000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.33 to version 1.33.4-gke.1172000 with this release.
To improve security and workload isolation, GKE has introduced a new, dedicated service agent for logging and monitoring of GKE nodes on clusters running version 1.33 and later. For more information, see GKE service agents.
What's changing?
GKE will now use the following service agent for logging and monitoring on your nodes:
service-{PROJECT_NUMBER}@gcp-sa-gkenode.iam.gserviceaccount.com
This service agent has the minimal permissions GKE needs to operate nodes, which are included in the role/container.defaultNodeServiceAgent IAM role.
Using a dedicated service agent helps to isolate the requirements of GKE-managed workloads from your own workloads.
What's the impact?
- This change affects only GKE system workloads, which will now use the new service agent for their logging and monitoring capabilities. Your own workloads are not impacted.
- You might notice missing logs or metrics for your nodes if the new service agent doesn't have the necessary permissions.
What do I need to do?
In the vast majority of cases, no action is needed, as the role role/container.defaultNodeServiceAgent has been automatically granted to the new GKE Node Service Agent on your cluster project.
However, you will need to re-apply the role role/container.defaultNodeServiceAgent to the new service agent in the following scenarios:
- You have automation that might have removed this role.
- You notice missing logs or metrics for your nodes.
You can find the full list of permissions for this role in the IAM documentation.
(2025-R40) Version updates
- Version 1.33.4-gke.1172000 is now the default version for cluster creation.
- The following versions are now available:
- The following node versions are now available:
- The following versions are no longer available:
- 1.30.14-gke.1036000
- 1.31.12-gke.1083000
- 1.32.8-gke.1026000
- 1.33.4-gke.1036000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled will be upgraded from version 1.29 to version 1.30.14-gke.1130000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled will be upgraded from version 1.30 to version 1.30.14-gke.1130000 with this release.
- Control planes and nodes with auto-upgrade enabled will be upgraded from version 1.33 to version 1.33.4-gke.1172000 with this release.
(2025-R40) Version updates
- The following versions are now available in the Rapid channel:
- The following versions are no longer available in the Rapid channel:
- 1.30.14-gke.1150000
- 1.33.4-gke.1245000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.29 to version 1.30.14-gke.1267000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.32 to version 1.33.4-gke.1350000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.30 to version 1.30.14-gke.1267000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.33 to version 1.33.4-gke.1350000 with this release.
(2025-R40) Version updates
- Version 1.33.4-gke.1172000 is now the default version for cluster creation in the Regular channel.
- The following versions are now available in the Regular channel:
- The following versions are no longer available in the Regular channel:
- 1.30.14-gke.1108000
- 1.31.12-gke.1083000
- 1.32.8-gke.1108000
- 1.33.4-gke.1134000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.29 to version 1.30.14-gke.1130000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.31 to version 1.32.8-gke.1134000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.32 to version 1.33.4-gke.1172000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.30 to version 1.30.14-gke.1130000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.32 to version 1.32.8-gke.1134000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.33 to version 1.33.4-gke.1172000 with this release.
(2025-R40) Version updates
- The following versions are now available in the Stable channel:
- The following versions are no longer available in the Stable channel:
- 1.30.14-gke.1036000
- 1.32.8-gke.1026000
- 1.33.4-gke.1036000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled in the Stable channel will be upgraded from version 1.29 to version 1.30.14-gke.1059000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled in the Stable channel will be upgraded from version 1.30 to version 1.30.14-gke.1059000 with this release.
(2025-R40) Version updates
GKE cluster versions have been updated.
New versions available for upgrades and new clusters.
The following versions are now available for new GKE clusters, and for manual control plane upgrades and node upgrades for existing clusters. For more information about versioning and upgrades, see GKE versioning and support and About GKE cluster upgrades.
Rapid channel
- The following versions are now available in the Rapid channel:
- The following versions are no longer available in the Rapid channel:
- 1.30.14-gke.1150000
- 1.33.4-gke.1245000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.29 to version 1.30.14-gke.1267000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.32 to version 1.33.4-gke.1350000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.30 to version 1.30.14-gke.1267000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Rapid channel will be upgraded from version 1.33 to version 1.33.4-gke.1350000 with this release.
Regular channel
- Version 1.33.4-gke.1172000 is now the default version for cluster creation in the Regular channel.
- The following versions are now available in the Regular channel:
- The following versions are no longer available in the Regular channel:
- 1.30.14-gke.1108000
- 1.31.12-gke.1083000
- 1.32.8-gke.1108000
- 1.33.4-gke.1134000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.29 to version 1.30.14-gke.1130000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.31 to version 1.32.8-gke.1134000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.32 to version 1.33.4-gke.1172000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.30 to version 1.30.14-gke.1130000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.32 to version 1.32.8-gke.1134000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Regular channel will be upgraded from version 1.33 to version 1.33.4-gke.1172000 with this release.
Stable channel
- The following versions are now available in the Stable channel:
- The following versions are no longer available in the Stable channel:
- 1.30.14-gke.1036000
- 1.32.8-gke.1026000
- 1.33.4-gke.1036000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled in the Stable channel will be upgraded from version 1.29 to version 1.30.14-gke.1059000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled in the Stable channel will be upgraded from version 1.30 to version 1.30.14-gke.1059000 with this release.
Extended channel
- Version 1.33.4-gke.1172000 is now the default version for cluster creation in the Extended channel.
- The following versions are now available in the Extended channel:
- The following versions are no longer available in the Extended channel:
- 1.28.15-gke.2599000
- 1.28.15-gke.2697000
- 1.29.15-gke.1820000
- 1.29.15-gke.1936000
- 1.30.14-gke.1108000
- 1.31.12-gke.1083000
- 1.32.8-gke.1108000
- 1.33.4-gke.1134000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.27 to version 1.28.15-gke.2610000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.28 to version 1.28.15-gke.2610000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.29 to version 1.29.15-gke.1835000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.30 to version 1.30.14-gke.1130000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.32 to version 1.32.8-gke.1134000 with this release.
- Control planes and nodes with auto-upgrade enabled in the Extended channel will be upgraded from version 1.33 to version 1.33.4-gke.1172000 with this release.
No channel
- Version 1.33.4-gke.1172000 is now the default version for cluster creation.
- The following versions are now available:
- The following node versions are now available:
- The following versions are no longer available:
- 1.30.14-gke.1036000
- 1.31.12-gke.1083000
- 1.32.8-gke.1026000
- 1.33.4-gke.1036000
- Auto-upgrade targets are now available for the following minor versions:
- Control planes and nodes with auto-upgrade enabled will be upgraded from version 1.29 to version 1.30.14-gke.1130000 with this release.
- The following patch-only version auto-upgrade targets are now available for clusters with maintenance exclusions or other factors preventing minor version upgrades:
- Control planes and nodes with auto-upgrade enabled will be upgraded from version 1.30 to version 1.30.14-gke.1130000 with this release.
- Control planes and nodes with auto-upgrade enabled will be upgraded from version 1.33 to version 1.33.4-gke.1172000 with this release.
For Exadata Database Service, Oracle Database@Google Cloud supports region australia-southeast2 (Melbourne, Australia).
For a full list of supported locations, see Regional availability
A weekly digest of client library updates from across the Cloud SDK.
Go
Changes for pubsub/apiv1
2.1.0 (2025-09-25)
Features
A weekly digest of client library updates from across the Cloud SDK.
Java
Changes for google-cloud-pubsub
1.141.5 (2025-09-24)
Bug Fixes
- deps: Update the Java code generator (gapic-generator-java) to 2.62.2 (c02d304)
Dependencies
- Update actions/checkout action to v5 (#2539) (83144e6)
- Update actions/github-script action to v8 (#2542) (0e6f0da)
- Update dependency com.google.cloud:google-cloud-bigquery to v2.55.0 (#2553) (15b9e66)
- Update dependency com.google.cloud:google-cloud-core to v2.60.1 (#2543) (fbb45ce)
- Update dependency com.google.cloud:google-cloud-storage to v2.57.0 (#2547) (133f8c7)
- Update dependency com.google.cloud:sdk-platform-java-config to v3.52.2 (#2558) (0623ac5)
- Update dependency com.google.protobuf:protobuf-java-util to v4.32.1 (#2551) (49722cb)
- Update googleapis/sdk-platform-java action to v2.62.2 (#2559) (3f1d901)
You can now create BigQuery non-incremental materialized views over Spanner data to improve query performance by periodically caching results. This feature is in Preview.
September 28, 2025
Google SecOpsForwarder component: end-of-life and migration
The forwarder component is being phased out of the Google SecOps platform and will reach end-of-life (EOL) in January 2027. This impact will change all any data collection pipelines that currently use the forwarder.
Action required: If you're currently using the forwarder component, you must migrate your data collection workflows to an alternative mechanism before April 1, 2027. You'll need to use another data pipeline management application for log ingestion.
We recommend that you migrate to the Bindplane OpenTelemetry (OTel) collector, which provides a scalable, open-standard solution for log and metric ingestion.
The following are key dates to note:
- Apr 1, 2026: New Google SecOps customers cannot use the forwarder component.
- Jan 1, 2027: The forwarder is officially EOL. No further patches, including security patches, will be released.
- Apr 1, 2027: Data is no longer allowed to be ingested from the forwarder component.
Increased Alert Trimming limit for Remote Agent
The default setting for Alert Trimming has been increased to 25 MB.
Podman support for Remote Agents
You can now install a Remote Agent using Podman. This new functionality provides a streamlined deployment workflow—a lightweight alternative to existing installation methods. For details, see Deploy an agent with Podman.
Update CrowdStrike API permissions before decommission
CrowdStrike is decommissioning its Detects API on September 30, 2025. This API has been replaced by the Alerts API. To ensure that your data feeds continue without interruption, you may need to update your API permissions.
This change impacts you if your Google SecOps tenant meets both of the following conditions:
- You use the CrowdStrike Detection Monitoring API connector, which ingests the
CS_DETECTSlog type. - The CrowdStrike API client configured for that feed lacks the permissions to read alerts Read.
To prevent disruption to your CrowdStrike data ingestion, you must update your API client permissions before September 30, 2025. Follow the instructions in Migrate from CrowdStrike Detects API to Alerts API to migrate your configuration to use the Alerts API.
For more details, see CrowdStrike’s official decommissioning notice.
Debian support for remote agents
You can now install a Remote Agent using Debian. This new functionality provides a streamlined deployment workflow—an alternative to existing installation methods. For details, see Deploy an agent with Debian.
Publisher Connector package size limit enforced
The maximum allowed size for a Publisher's Connector Package is now limited to 25 MB.
Remote Agent, Release 2.5.0 contains the following changes:
Forwarder component: end-of-life and migration
The forwarder component is being phased out of the Google SecOps platform and will reach end-of-life (EOL) in January 2027. This impact will change all any data collection pipelines that currently use the forwarder.
Action required: If you're currently using the forwarder component, you must migrate your data collection workflows to an alternative mechanism before April 1, 2027. You'll need to use another data pipeline management application for log ingestion.
We recommend that you migrate to the Bindplane OpenTelemetry (OTel) collector, which provides a scalable, open-standard solution for log and metric ingestion.
The following are key dates to note:
- Apr 1, 2026: New Google SecOps customers cannot use the forwarder component.
- Jan 1, 2027: The forwarder is officially EOL. No further patches, including security patches, will be released.
- Apr 1, 2027: Data is no longer allowed to be ingested from the forwarder component.
Forwarder component: end-of-life and migration
The forwarder component is being phased out of the Google SecOps platform and will reach end-of-life (EOL) in January 2027. This impact will change all any data collection pipelines that currently use the forwarder.
Action required: If you're currently using the forwarder component, you must migrate your data collection workflows to an alternative mechanism before April 1, 2027. You'll need to use another data pipeline management application for log ingestion.
We recommend that you migrate to the Bindplane OpenTelemetry (OTel) collector, which provides a scalable, open-standard solution for log and metric ingestion.
The following are key dates to note:
- Apr 1, 2026: New Google SecOps customers cannot use the forwarder component.
- Jan 1, 2027: The forwarder is officially EOL. No further patches, including security patches, will be released.
- Apr 1, 2027: Data is no longer allowed to be ingested from the forwarder component.
Update CrowdStrike API permissions before decommission
CrowdStrike is decommissioning its Detects API on September 30, 2025. This API has been replaced by the Alerts API. To ensure that your data feeds continue without interruption, you may need to update your API permissions.
This change impacts you if your Google SecOps tenant meets both of the following conditions:
- You use the CrowdStrike Detection Monitoring API connector, which ingests the
CS_DETECTSlog type. - The CrowdStrike API client configured for that feed lacks the permissions to read alerts Read.
To prevent disruption to your CrowdStrike data ingestion, you must update your API client permissions before September 30, 2025. Follow the instructions in Migrate from CrowdStrike Detects API to Alerts API to migrate your configuration to use the Alerts API.
For more details, see CrowdStrike’s official decommissioning notice.
Increased Alert Trimming limit for Remote Agent
The default setting for Alert Trimming has been increased to 25 MB.
Podman support for Remote Agents
You can now install a Remote Agent using Podman. This new functionality provides a streamlined deployment workflow—a lightweight alternative to existing installation methods. For details, see Deploy an agent with Podman.
Update CrowdStrike API permissions before decommission
CrowdStrike is decommissioning its Detects API on September 30, 2025. This API has been replaced by the Alerts API. To ensure that your data feeds continue without interruption, you may need to update your API permissions.
This change impacts you if your Google SecOps tenant meets both of the following conditions:
- You use the CrowdStrike Detection Monitoring API connector, which ingests the
CS_DETECTSlog type. - The CrowdStrike API client configured for that feed lacks the permissions to read alerts Read.
To prevent disruption to your CrowdStrike data ingestion, you must update your API client permissions before September 30, 2025. Follow the instructions in Migrate from CrowdStrike Detects API to Alerts API to migrate your configuration to use the Alerts API.
For more details, see CrowdStrike’s official decommissioning notice.
Debian support for remote agents
You can now install a Remote Agent using Debian. This new functionality provides a streamlined deployment workflow—an alternative to existing installation methods. For details, see Deploy an agent with Debian.
Publisher Connector package size limit enforced
The maximum allowed size for a Publisher's Connector Package is now limited to 25 MB.
Remote Agent, Release 2.5.0 contains the following changes:
Increased Alert Trimming limit for Remote Agent
The default setting for Alert Trimming has been increased to 25 MB.
Deploy an agent with Debian
You can now install a Remote Agent using Debian. This new functionality provides a streamlined deployment workflow—an alternative to existing installation methods.
For more information, see Deploy an agent with Debian.
Release 6.3.62 is being rolled out to the first phase of regions, as outlined in our Google SecOps release plan.
This release contains the following changes:
Remote Agent, Release 2.5.0 contains the following changes:
Podman support for Remote Agents
You can now install a Remote Agent using Podman. This new functionality provides a streamlined deployment workflow—a lightweight alternative to existing installation methods.
For more information, see Deploy an agent with Podman.
Publisher Connector package size limit enforced
The maximum allowed size for a Publisher's Connector Package is now limited to 25 MB.
Increased Alert Trimming limit for Remote Agent
The default setting for Alert Trimming has been increased to 25 MB.
Deploy an agent with Debian
You can now install a Remote Agent using Debian. This new functionality provides a streamlined deployment workflow—an alternative to existing installation methods.
For more information, see Deploy an agent with Debian.
Release 6.3.62 is being rolled out to the first phase of regions, as outlined in our Google SecOps release plan.
This release contains the following changes:
Remote Agent, Release 2.5.0 contains the following changes:
Podman support for Remote Agents
You can now install a Remote Agent using Podman. This new functionality provides a streamlined deployment workflow—a lightweight alternative to existing installation methods.
For more information, see Deploy an agent with Podman.
Publisher Connector package size limit enforced
The maximum allowed size for a Publisher's Connector Package is now limited to 25 MB.
September 27, 2025
Google SecOpsUse joins in YARA-L Search queries
These changes are currently in Preview.
You can now use joins in statistical Search queries that include a match section
to correlate data from multiple sources. This feature lets you link related
sources directly within a single query.
For more information, see Use joins in Search.
Use joins in YARA-L Search queries
These changes are currently in Preview.
You can now use joins in statistical Search queries that include a match section
to correlate data from multiple sources. This feature lets you link related
sources directly within a single query.
For more information, see Use joins in Search.
Use joins in YARA-L Search queries
These changes are currently in Preview.
You can now use joins in statistical Search queries that include a match section
to correlate data from multiple sources. This feature lets you link related
sources directly within a single query.
For more information, see Use joins in Search.
Release 6.3.61 is now available for all regions.
Release 6.3.61 is now available for all regions.
Model Armor limits the maximum input size for files and text to 4 MB, automatically skipping any content that exceeds this threshold.
September 26, 2025
Access ApprovalMemorystore for Valkey is generally available (GA).
Memorystore for Redis Cluster is generally available (GA).
Memorystore for Valkey is generally available (GA).
Memorystore for Redis Cluster is generally available (GA).
Version 20250926.00 of the guest agent is now available. This guest agent
version introduces the plugin-based architecture to Debian 12.
For more information about the plugin-based architecture, see Guest agent.
Next Edit Predictions in VS Code (Preview)
Next Edit Predictions, which predicts the next code suggestions throughout the code file that you're currently in, are now available in VS Code Gemini Code Assist, in Preview.
You can cycle through multiple suggestions, dismiss suggestions, or ignore them and continue coding.
Enable Next Edit Predictions in your IDE to get started.
Cloud Hub Optimization and Cost Explorer integrations
Gemini Cloud Assist can now answer questions about your resource cost and utilization. To learn more about what permissions you need to enable this functionality, see the Optimize resource costs and utilization setup and the Optimize costs with Cost Explorer setup.
Next Edit Predictions in VS Code (Preview)
Next Edit Predictions, which predicts the next code suggestions throughout the code file that you're currently in, are now available in VS Code Gemini Code Assist, in Preview.
You can cycle through multiple suggestions, dismiss suggestions, or ignore them and continue coding.
Enable Next Edit Predictions in your IDE to get started.
Gemini Enterprise: Manage image and video generation on the web app
By default, image and video generation are enabled in the Agentspace web app. To turn off these features, admins must navigate to the Configurations > Feature Management tab, and turn off the Enable video generation and Enable image generation options.
VMware Engine ve2 nodes are now available in the following additional region:
- Doha, Qatar (
me-central1,v-zone-a)
Version 20250926.00 of the guest agent is now available. This guest agent
version introduces the plugin-based architecture to Debian 12.
For more information about the plugin-based architecture, see Guest agent.
For Privileged Access Manager, notification emails for grant activation, activation failure, or denial no longer include approver details.
To learn how to view the approver details, see Check grant status.
Privileged Access Manager (PAM) offers the following features in preview:
Selective file restore feature is now generally available for Google Cloud NetApp Volumes, supporting the Standard, Premium, and Extreme service levels. For more information, see Selective file restore.
The following features of VPC Flow Logs are available in General Availability:
- Logging for RDMA over Falcon transport
- Enhanced round-trip time precision for TCP and Falcon traffic
For more information, see About VPC Flow Logs records.
September 25, 2025
Access ApprovalCloud TPU is generally available (GA).
Cloud TPU is generally available (GA).
BigQuery data canvas now supports destination table nodes. Destination table nodes let you persist query results to a new or existing table. This feature is generally available (GA).
The
ARRAY_FIRST,
ARRAY_LAST,
and
ARRAY_SLICE
GoogleSQL functions are now
generally available (GA).
Cloud SQL for MySQL now supports minor version 8.0.43. To upgrade your existing instance to the new version, see Upgrade the database minor version.
Cloud SQL Managed Connection Pooling is now generally available (GA). Managed Connection Pooling lets you scale your workloads by optimizing resource utilization for Cloud SQL instances using pooling. You can now also use IAM authentication to secure connections when using Managed Connection Pooling.
For more information, see Managed Connection Pooling overview.
Support for the following features will end on March 17, 2027:
- GKE on AWS
- GKE on Azure
- EKS Attached Clusters on AWS
- Azure Attached Clusters with AKS
Note that there are no changes to the other features of GKE attached clusters or Google Distributed Cloud (software only or air-gapped),
You must migrate to an alternative service mesh solution or an alternative Istio-based solution using your existing CSM configuration files by March 17, 2027.
You can now use the Filestore CSI driver to create Filestore regional instances. For more information, see Access Filestore instances with the Filestore CSI driver.
New preview models for Gemini 2.5 Flash and 2.5 Flash-Lite are now available. These models are available at the following versioned endpoints:
gemini-2.5-flash-preview-09-2025gemini-2.5-flash-lite-preview-09-2025
Web SDK version 2 will be shut down on June 26, 2026
On June 26, 2025, we announced the launch of Web SDK version 3. Starting on June 26, 2026, the web SDK v2 will no longer function. Be sure to update your website to use the web SDK v3 before that date to avoid breaking your integration with the web SDK. We are no longer adding new features to the web SDK v2.
You can now let GKE auto-create node pools with ComputeClasses without having to enable node auto-provisioning for the entire cluster. This provides more granular control over auto-created node pools, enabling you to target specific workloads and optimize resource usage. For more information, see Node auto-provisioning and ComputeClasses.
To use this feature, your cluster must meet both of the following requirements:
- Enrolled in the Rapid release channel.
- Running GKE version 1.33.3-gke.1136000 or later.
GKE Standard clusters now support Autopilot features, including the container-optimized compute platform and fully managed nodes, letting you use Autopilot's advantages without migrating to a dedicated Autopilot cluster. For more information, see Run Autopilot workloads in GKE Standard clusters.
To use these features, your cluster must meet the following requirements:
- Enrolled in the Rapid release channel.
- Running GKE version 1.33.1-gke.1107000 or later.
Issue with A4X machine type compatibility on certain GKE versions
Certain GKE versions are not compatible with the A4X machine type. The issue is that a Container-Optimized OS (COS) image that these GKE versions depend on was not built as a multi-architecture image. This incompatibility causes an exec format error on the Arm-based A4X machines. The issue affects GKE versions 1.33.2-gke.1377000 or later, and any versions earlier than 1.33.4-gke.1036000.
Orca Security: Version 12.0
Integration: (REGRESSIVE) Updated to support the latest API version.
Ontology has been updated. Overwrite current ontology mapping to align with the new API alert structure.
Any.Run: Version 8.0
Updated the available privacy settings in the following actions:
Analyze URL
Analyze File URL
Analyze File
CrowdStrike Falcon: Version 64.0
Updated timeout handling in the following connector:
- Crowdstrike Falcon - Streaming Events Connector
Integration: Updated authentication to support multi-tenancy execution.
Google Workspace: Version 21.0
Expanded capabilities of the following action:
- List OU Of Account
Updated processing of the organization unit inside the following actions:
Block Extension
Delete Extension
List OU Of Account
New Apache Kafka integration
Google Chronicle: Version 65.0
Updated the filtering mechanism of the following action:
- Get Data Tables
Microsoft Azure Sentinel: Version 57.0
The following new job has been added:
- Sync Incidents
Orca Security: Version 12.0
Integration: (REGRESSIVE) Updated to support the latest API version.
Ontology has been updated. Overwrite current ontology mapping to align with the new API alert structure.
Any.Run: Version 8.0
Updated the available privacy settings in the following actions:
Analyze URL
Analyze File URL
Analyze File
CrowdStrike Falcon: Version 64.0
Updated timeout handling in the following connector:
- Crowdstrike Falcon - Streaming Events Connector
Integration: Updated authentication to support multi-tenancy execution.
Google Workspace: Version 21.0
Expanded capabilities of the following action:
- List OU Of Account
Updated processing of the organization unit inside the following actions:
Block Extension
Delete Extension
List OU Of Account
New Apache Kafka integration
Google Chronicle: Version 65.0
Updated the filtering mechanism of the following action:
- Get Data Tables
Microsoft Azure Sentinel: Version 57.0
The following new job has been added:
- Sync Incidents
Orca Security: Version 12.0
Integration: (REGRESSIVE) Updated to support the latest API version.
Ontology has been updated. Overwrite current ontology mapping to align with the new API alert structure.
Any.Run: Version 8.0
Updated the available privacy settings in the following actions:
Analyze URL
Analyze File URL
Analyze File
CrowdStrike Falcon: Version 64.0
Updated timeout handling in the following connector:
- Crowdstrike Falcon - Streaming Events Connector
Integration: Updated authentication to support multi-tenancy execution.
Google Workspace: Version 21.0
Expanded capabilities of the following action:
- List OU Of Account
Updated processing of the organization unit inside the following actions:
Block Extension
Delete Extension
List OU Of Account
New Apache Kafka integration
Google Chronicle: Version 65.0
Updated the filtering mechanism of the following action:
- Get Data Tables
Microsoft Azure Sentinel: Version 57.0
The following new job has been added:
- Sync Incidents
Table charts support up to 10 sort fields
Report editors can now configure up to 10 sort fields for table charts.
Partner connection launch update The following partner connectors have been added to the Looker Studio Connector Gallery:
- Odoo Appointment AppiWorks by Jivrus Technologies. Sources: Odoo Appointments
- Snowflake by Supermetrics. Sources: Snowflake
- GA4 Annotations by ReallyGoodData. Sources: Google Analytics
- 800.com Call Analytics by 800.com. Sources: 800com
- TikTok Shop by Supermetrics. Sources: Tiktok Shop
- seoClarity Keyword Details by seoClarity. Sources: Seoclarity
- seoClarity Domain Summary by seoClarity. Sources: Seoclarity
The following partner connectors were released during the week of Sep 15, 2025:
- Odoo Subscription AppiWorks by Jivrus Technologies. Sources: OdOo Subscription
- Amazon DSP by Dataslayer. Sources: Amazon Ads
- Etsy by Power My Analytics. Sources: Etsy
- SeoSamba CRM by SeoSamba. Sources: Seosamba CRM
- Google BigQuery by Supermetrics. Sources: Google BigQuery
- Microsoft Ads by Porter Metrics. Sources: Microsoft Ads
- Outbrain DSP by Catchr. Sources: Outbrain
- The Trade Desk by Catchr. Sources: The Trade Desk
- Close.com by Windsor.ai. Sources: Close
- Odoo Invoice AppiWorks by Jivrus Technologies. Sources: Odoo Invoice
User interface change: "Add quick filter" is now "Add filter"
We've made a wording change to the filter bar in the report editor. The button label that previously said "Add quick filter" is now "Add filter." The functionality of quick filters hasn't changed. Learn more about quick filters.
Looker connector enhancements
Looker data sources now display the names of fields without their prepended view names. Fields are now nested under their corresponding views.
Learn more about how Looker Explore data appears in Looker Studio.
The Cassandra interface for Spanner is now generally available. The Cassandra interface lets you take advantage of Spanner's fully managed, scalable, and highly available infrastructure using familiar Cassandra tools and syntax. For more information, see Cassandra interface, Migrate from Cassandra to Spanner, and Connect to Spanner using the Cassandra interface.
The following features of VPC Flow Logs are available in General Availability through the Network Management API:
- Enabling VPC Flow Logs for an organization
- Enabling VPC Flow Logs for a VPC network
- Enabling VPC Flow Logs for a subnet
For more information, see Supported configurations.
September 24, 2025
Access ApprovalVM Manager is generally available (GA).
VM Manager is generally available (GA).
You can create and manage query plan patches. Query plan patches let you specify the details of the execution plan of your queries. This feature is generally available (GA).
On September 24, 2025, we released an updated version of Apigee.
ApigeeBackendService for the Apigee Operator for Kubernetes (GA)
The ApigeeBackendService resource for the Apigee Operator for Kubernetes is Generally Available (GA).
This new resource enables the integration of the Apigee Operator for Kubernetes with the Google Kubernetes Engine (GKE) Inference Gateway. The GKE Inference Gateway is an extension to the GKE Gateway that provides optimized routing and load balancing for serving generative Artificial Intelligence (AI) workloads. It simplifies the deployment, management, and observability of AI inference workloads.
With this new integration, GKE Inference Gateway users can now leverage Apigee's full suite of features to manage, govern and monetize their AI workload through APIs.
To learn more, see Create an ApigeeBackendService.
On September 24, 2025, we released an updated version of Apigee.
ApigeeBackendService for the Apigee Operator for Kubernetes (GA)
The ApigeeBackendService resource for the Apigee Operator for Kubernetes is Generally Available (GA).
This new resource enables the integration of the Apigee Operator for Kubernetes with the Google Kubernetes Engine (GKE) Inference Gateway. The GKE Inference Gateway is an extension to the GKE Gateway that provides optimized routing and load balancing for serving generative Artificial Intelligence (AI) workloads. It simplifies the deployment, management, and observability of AI inference workloads.
With this new integration, GKE Inference Gateway users can now leverage Apigee's full suite of features to manage, govern and monetize their AI workload through APIs.
To learn more, see Create an ApigeeBackendService.
Apigee Operator for Kubernetes for Apigee Hybrid (Preview)
On September 24, 2025 we released the Apigee Operator for Kubernetes for Apigee Hybrid 1.15.0 and newer.
The Apigee Operator for Kubernetes allows you to perform API management tasks, such as defining API products and operations, using Kubernetes tools. This preview release allows you to integrate this capability with your Apigee hybrid (v1.15.0 or newer) installation.
For more information, see:
For command-line users, BigQuery is now integrated with the Gemini CLI to provide an agentic CLI experience. Using the dedicated Gemini CLI extensions for BigQuery, you can search, explore, analyze, and gain insights from your data by asking natural language questions, generating forecasts, and running contribution analysis directly from the command line. This feature is available in beta.
BigQuery ML now supports
visualization of model monitoring metrics.
This feature lets you use charts and graphs to
analyze model monitoring function output.
You can use metric visualization with the
ML.VALIDATE_DATA_SKEW
and
ML.VALIDATE_DATA_DRIFT
functions. This feature is
generally available
(GA).
Support for setting multiple environment variables using the .env file is in General Availability (GA). For more information, see Configure environment variables for services, jobs, and worker pools.
Cloud SQL for MySQL 8.4.5 is upgraded to MySQL 8.4.6. For more information, see the MySQL 8.4.6 Release Notes.
Bug Fixes:
Config Connector version 1.134.1 is now available.
cos-beta-125-19216-0-53
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.46 | v27.5.1 | v2.1.3 | See List |
Updated cos-gpu-installer to v2.5.7.
Added support for the fwctl subsystem and the Mellanox fwctl driver for ARM64.
Added support for NVIDIA driver v580.82.07. Updated all latest driver version and default driver versions for NVIDIA_GB200 and NVIDIA_B200 to v580.82.07.
Upgraded dev-libs/libxslt to version 1.1.43-r1.
Updated the Linux kernel to v6.12.46.
Upgraded dev-libs/libxml2 to version 2.13.9. This fixes CVE-2025-9714.
Runtime sysctl changes:
- Changed: fs.file-max: 811500 -> 811534
Enabled Coherent Driver Memory Management by default when installing GPU drivers on GB2000.
cos-117-18613-339-70
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.105 | v24.0.9 | v1.7.28 | See List |
Updated cos-gpu-installer to v2.5.7.
Updated golang.org/x/crypto in google-osconfig-agent to v0.31.0.
Added support for NVIDIA driver v580.82.07. Updated all latest driver version and default driver versions for NVIDIA_GB200 and NVIDIA_B200 to v580.82.07.
Upgraded dev-libs/libxslt to version 1.1.43-r1.
Updated the Linux kernel to v6.6.105.
Upgraded dev-libs/libxml2 to version 2.13.9. This fixes CVE-2025-9714.
Runtime sysctl changes:
- Changed: fs.file-max: 811774 -> 811794
Enabled Coherent Driver Memory Management by default when installing GPU drivers on GB2000.
cos-113-18244-448-50
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.1.151 | v24.0.9 | v1.7.27 | See List |
Updated cos-gpu-installer to v2.5.7.
Updated golang.org/x/crypto in google-guest-agent to v0.31.0.
Updated golang.org/x/crypto in google-osconfig-agent to v0.31.0.
Upgraded dev-libs/libxslt to version 1.1.43-r1.
Updated the Linux kernel to v6.1.151.
Upgraded dev-libs/libxml2 to version 2.13.9. This fixes CVE-2025-9714.
Runtime sysctl changes:
- Changed: fs.file-max: 811983 -> 812054
Enabled Coherent Driver Memory Management by default when installing GPU drivers on GB2000.
cos-dev-129-19284-0-0
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.12.47 | v27.5.1 | v2.1.3 | See List |
Updated cos-gpu-installer to v2.5.7.
Updated the Linux kernel to v6.12.47.
Added support for NVIDIA driver v580.82.07. Updated all latest driver version and default driver versions for NVIDIA_GB200 and NVIDIA_B200 to v580.82.07.
Upgraded dev-libs/libxslt to version 1.1.43-r1.
Upgraded dev-libs/libxml2 to version 2.13.9. This fixes CVE-2025-9714, CVE-2025-32415 and CVE-2025-32414.
Runtime sysctl changes:
- Changed: fs.file-max: 811423 -> 811483
- Changed: net.ipv4.udp_mem: 188034 250715 376068 -> 188034 250714 376068
Enabled Coherent Driver Memory Management by default when installing GPU drivers on GB2000.
cos-109-17800-570-50
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.1.151 | v24.0.9 | v1.7.27 | See List |
Updated cos-gpu-installer to v2.5.7.
Updated golang.org/x/crypto in google-osconfig-agent to v0.31.0.
Upgraded dev-libs/libxslt to version 1.1.43-r1.
Updated the Linux kernel to v6.1.151.
Upgraded dev-libs/libxml2 to version 2.13.9. This fixes CVE-2025-9714.
Runtime sysctl changes:
- Changed: fs.file-max: 812272 -> 812258
Enabled Coherent Driver Memory Management by default when installing GPU drivers on GB2000.
cos-121-18867-199-73
| Kernel | Docker | Containerd | GPU Drivers |
| COS-6.6.105 | v27.5.1 | v2.0.6 | See List |
Updated cos-gpu-installer to v2.5.7.
Added support for NVIDIA driver v580.82.07. Updated all latest driver version and default driver versions for NVIDIA_GB200 and NVIDIA_B200 to v580.82.07.
Upgraded dev-libs/libxslt to version 1.1.43-r1.
Upgraded dev-libs/libxml2 to version 2.13.9. This fixes CVE-2025-9714.
Runtime sysctl changes:
- Changed: fs.file-max: 811710 -> 811752
Enabled Coherent Driver Memory Management by default when installing GPU drivers on GB2000.
For jobs that use GPUs, Dataflow now supports the flex-start provisioning model. This flex-start provisioning model can improve your ability to get access to constrained GPU resources for short-duration workloads. This feature is available in Preview and is for batch pipelines only. For more information, see Configure a provisioning model.
Eventarc Advanced support for publishing events from multiple projects is available in Preview.
Gemini Enterprise: Knowledge base filter for catalog entities in ServiceNow connectors (GA)
In your ServiceNow connectors, you can filter your knowledge base entities by catalog IDs. This lets you selectively ingest only those catalog entities whose catalogSysId matches the filter.
If no values are specified, then the connector ingests all catalog entities. This feature is Generally Available (GA).
For information about ServiceNow connectors, see Connect ServiceNow.
Gemini Enterprise: Interface updates
- File uploads can be canceled at any time.
- The Star and Share buttons now appear after a user has initiated a session by submitting a prompt.
Access to Gemini's 1.5 models has been discontinued. For more information, see our Model versions page.
Cloud Armor's support for Autonomous System Numbers (ASNs) in globally scoped edge security policies for Media CDN edge cache services is Generally Available.
Cloud Armor's support for Network Threat Intelligence (NTI) in globally scoped edge security policies for Media CDN edge cache services is Generally Available.
Integration with VPC Service Controls is generally available (GA).
All 3-year Committed Use Discounts (CUDs) for VMware Engine ve1 SKUs are now End-of-Sale across all regions where the service is available.
The following specific 3-year commitments are impacted by this change:
- 3-year commitment (monthly payments), Fully Licensed Pricing - "postpaid"
- 3-year commitment (upfront payments), Fully Licensed Pricing - "prepay"
- 3-year commitment (monthly payments), Fully Licensed convertible commitment - "postpaid"
- 3-year commitment (upfront payments), Fully Licensed convertible commitment - "prepay"
- 3-year commitment (monthly payments), Portable License Pricing - "postpaid"
- 3-year commitment (upfront payments), Portable License Pricing - "prepay"
- 3-year commitment (monthly payments), Protected License Pricing - "postpaid"
- 3-year commitment (upfront payments), Protected License Pricing - "prepay"
Refer to VMware Engine node types for the regional availability of ve1 SKUs.
Google Distributed Cloud (software only) for VMware 1.32.500-gke.48 is now available for download. To upgrade, see Upgrade a cluster. Distributed Cloud 1.32.500-gke.48 runs on Kubernetes v1.32.8-gke.500.
If you are using a third-party storage vendor, check the GDC Ready storage partners document to make sure the storage vendor has already passed the qualification for this release.
After a release, it takes approximately 7 to 14 days for the version to become available for use with GKE On-Prem API clients: the Google Cloud console, the gcloud CLI, and Terraform.
The following issues were fixed in 1.32.500-gke.48:
- Fixed vulnerabilities listed in Vulnerability fixes.
For information about the latest known issues, see Google Distributed Cloud for bare metal known issues in the Troubleshooting section.
The following issues were fixed in 1.32.500-gke.48:
Fixed an issue where the cluster restore process leaves the Kubelet certificate files as regular files instead of symbolic links, preventing certificate rotation.
This patch release doesn't include new fixes for specific, externally-cited vulnerabilities.
Google Distributed Cloud for bare metal 1.32.500-gke.48 is now available for download. To upgrade, see Upgrade clusters. Google Distributed Cloud for bare metal 1.32.500-gke.48 runs on Kubernetes v1.32.8-gke.500.
After a release, it takes approximately 7 to 14 days for the version to become available for installations or upgrades with the GKE On-Prem API clients: the Google Cloud console, the gcloud CLI, and Terraform.
If you use a third-party storage vendor, check the Ready storage partners document to make sure the storage vendor has already passed the qualification for this release of Google Distributed Cloud for bare metal.
You can use Network Threat Intelligence (NTI) from Cloud Armor in Edge Security Policies for Media CDN edge cache services for Enterprise users. NTI helps identify and block requests originating from known malicious IP addresses and networks. This feature is Generally Available.
For an example, see Example: Block traffic from known malicious IPs.
For more information, see Google Cloud Armor support.
You can use Autonomous System Numbers (ASN) based rules from Cloud Armor for Media CDN. ASN-based rules allow you to create security policies that specifically permit or deny traffic based on the ASN of the client requesting your content. This feature is Generally Available.
For more information, see Google Cloud Armor support.
Google Cloud NetApp Volumes now supports the FlexCache feature in allow-listed General Availability (GA) for the Premium and Extreme service levels. For more information, see FlexCache.
September 23, 2025
Agent AssistAgent Assist offers a bidirectional API for next-generation audio and multi-modal experiences in both Conversational Agents and Agent Assist. The BiDiStreamingAnalyzeContent API facilitates the streaming of audio data and returns either transcripts or human agent suggestions to you.
You can now provision, manage, and query your databases using the dedicated Gemini CLI extensions for AlloyDB. The extensions provide full lifecycle control of your database - from provisioning instances to exploring schemas and troubleshooting issues. This feature is available in beta.
Layer-based scanning for Artifact Analysis is in Preview. You can view vulnerability metadata for a specific layer of your image digest in the Google Cloud Console and in the GCloud CLI. For more information, see the following topics:
Google Cloud Console:
- View layer metadata for Go images
- View layer metadata for Java images
- View layer metadata for Node.js images
- View layer metadata for Python images
GCloud CLI
Cloud KMS now supports key encapsulation mechanisms (KEMs) for sharing secrets in Preview. KEMs are designed to be resistant to post-quantum attacks. You can use the following KEM algorithms:
ML_KEM_768ML_KEM_1024KEM_XWING
For more information about key encapsulation mechanisms, see Key encapsulation mechanisms. To learn how to use key encapsulation mechanisms to share secrets, see Encapsulate and decapsulate using KEMs.
Cloud NAT gateways for Public NAT support source-based NAT rules for IPv4 addresses. This feature is available in Preview.
You can use the URL filtering service to filter your workload traffic by using domain and Server Name Indication (SNI) information available in the egress HTTP(S) messages. For more information, see URL filtering service overview. This feature is available in Preview.
You can specify mount options when you configure Cloud Storage volume mounts for Cloud Run services, jobs, and worker pools. (GA)
You can now provision, manage and query your databases using the dedicated Gemini CLI extension for Cloud SQL for MySQL. The extension provides full lifecycle control of your database—from provisioning instances, to exploring schemas and troubleshooting issues—from your command-line interface.
For more information, see Use Cloud SQL for MySQL with MCP, Gemini CLI, and other agents.
You can now retain point-in-time recovery (PITR) logs for an instance after its deletion for a specified retention period. These logs can be used to restore the deleted instance to a specific point in time. For more information, see Restore a deleted instance using PITR.
You can now provision, manage and query your databases using the dedicated Gemini CLI extension for Cloud SQL for PostgreSQL. The extension provides full lifecycle control of your database—from provisioning instances, to exploring schemas and troubleshooting issues—from your command-line interface.
For more information, see Use Cloud SQL for PostgreSQL with MCP, Gemini CLI, and other agents.
You can now retain point-in-time recovery (PITR) logs for an instance after its deletion for a specified retention period. These logs can be used to restore the deleted instance to a specific point in time. For more information, see Restore a deleted instance using PITR.
You can now provision, manage and query your databases using the dedicated Gemini CLI extension for Cloud SQL for SQL Server. The extension provides full lifecycle control of your database—from provisioning instances, to exploring schemas and troubleshooting issues—from your command-line interface.
For more information, see Use Cloud SQL for SQL Server with MCP, Gemini CLI, and other agents.
You can now retain point-in-time recovery (PITR) logs for an instance after its deletion for a specified retention period. These logs can be used to restore the deleted instance to a specific point in time. For more information, see Restore a deleted instance using PITR.
1.27.1-asm.2 is now available for in-cluster Cloud Service Mesh.
You can now download 1.27.1-asm.2 for in-cluster Cloud Service Mesh. It includes the features of Istio 1.27.1 subject to the list of supported features.
The following environment variables and annotations are not supported:
ENVOY_STATUS_PORT_ENABLE_PROXY_PROTOCOLPILOT_DNS_CARES_UDP_MAX_QUERIESPILOT_IP_AUTOALLOCATE_IPV4_PREFIXandPILOT_IP_AUTOALLOCATE_IPV6_PREFIXsidecar.istio.io/bootstrapOverride
For details on upgrading Cloud Service Mesh, see Upgrade Cloud Service Mesh. Cloud Service Mesh version 1.27.1-asm.2 uses Envoy v 1.35.3-dev.
You can now connect your Dataplex Universal Catalog instance to your favorite developer tools, such as the Gemini CLI and other IDEs. This integration enables AI-driven data discovery and asset management directly within your development environment. For more information, see Use Dataplex Universal Catalog with MCP, Gemini, and other agents.
Datastream support for MongoDB as a source is now generally available (GA). For more information, see the documentation.
Custom classifier
model pretrained-classifier-v1.5-2025-08-05
powered by Gemini 2.5 Flash is in Preview. It has ML processing available for US and EU regions, a
maximum page limit of 30 pages,
and processing requests of 120 pages per minute.
Unlike the prior custom classifier, which used classical machine learning, this version features a new platform. It accommodates:
- High accuracy immediately, based on the document classes you define.
- Few-shot learning to further improve accuracy.
- Use of descriptions when labeling for more context and insight for document classes.
- More accurate results with the same training dataset on the fine-tuned generative AI model, compared to the trained version.
- Autolabeling documents for fine-tuning and evaluation.
- Generative AI to fine-tune and heighten accuracy.
For more information on processor versions, see Managing processor versions.
You can now query your databases and update data using the dedicated Gemini CLI extension for Firestore. This feature is available in beta.
Revert to a checkpoint in IntelliJ (GA)
Reverting to a checkpoint for chat code suggestions with IntelliJ Gemini Code Assist is now generally available. Reverting to a checkpoint lets you revert affected source files to a point before any code suggestions were applied.
Access saved prompts in the Prompt Library
You can access saved prompts
in the Prompt Library when you type @ in Gemini chat and select the prompt you
want.
To view the Prompt Library settings, go to Settings > Tools > Gemini > Prompt Library.
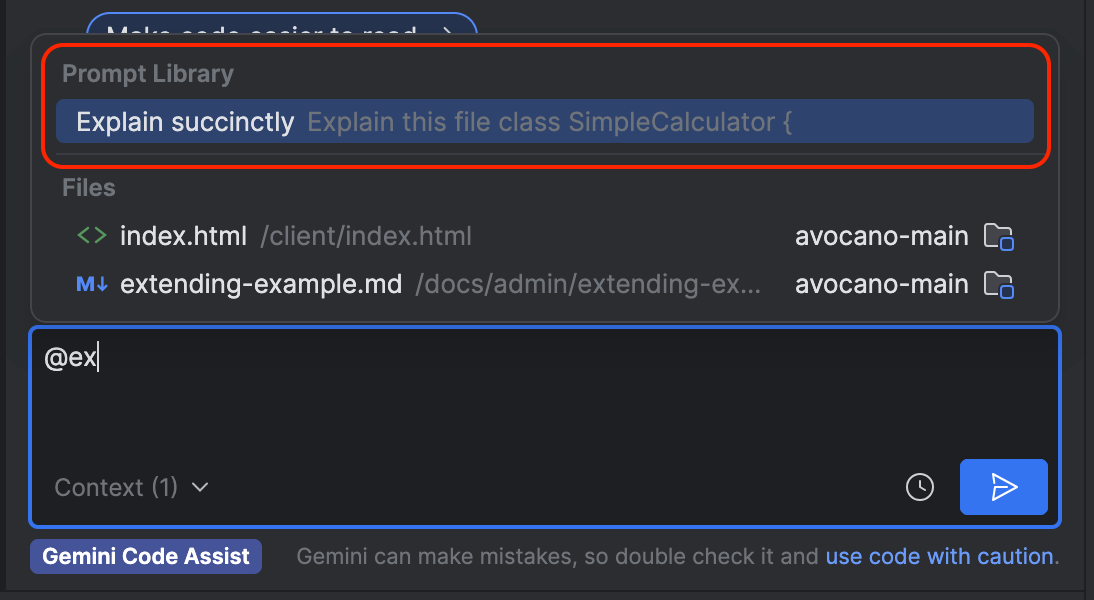
Inline diff is generally available (GA) for VS Code
Inline diff is generally available for VS Code Gemini Code Assist. With the inline diff view, chat generated code suggestions are visually highlighted directly in your editor—green for additions, red for deletions. This feature boosts productivity by offering immediate visibility on modifications, streamlining reviews, and enabling precise control over integrating new code, all without leaving your current view.
If preferred, you can also change the diff view settings to have a side-by-side diff window instead of the inline diff.
Copy sign-in link
As an alternative to clicking Sign in when signing into your Google Account to use IntelliJ Gemini Code Assist, you can click Copy link and manually paste the link in your browser's URL bar.
Revert to a checkpoint in IntelliJ (GA)
Reverting to a checkpoint for chat code suggestions with IntelliJ Gemini Code Assist is now generally available. Reverting to a checkpoint lets you revert affected source files to a point before any code suggestions were applied.
Inline diff is generally available (GA) for VS Code
Inline diff is generally available for VS Code Gemini Code Assist. With the inline diff view, you can visually highlight code changes directly in your editor—green for additions, red for deletions. This feature boosts productivity by offering immediate visibility on modifications, streamlining reviews, and enabling precise control over integrating new code, all without leaving your current view.
If preferred, you can also change the diff view settings to have a side-by-side diff window instead of the inline diff.
Access saved prompts in the Prompt Library
You can access saved prompts
in the Prompt Library when you type @ in Gemini chat and select the prompt you
want.
To view the Prompt Library settings, go to Settings > Tools > Gemini > Prompt Library.
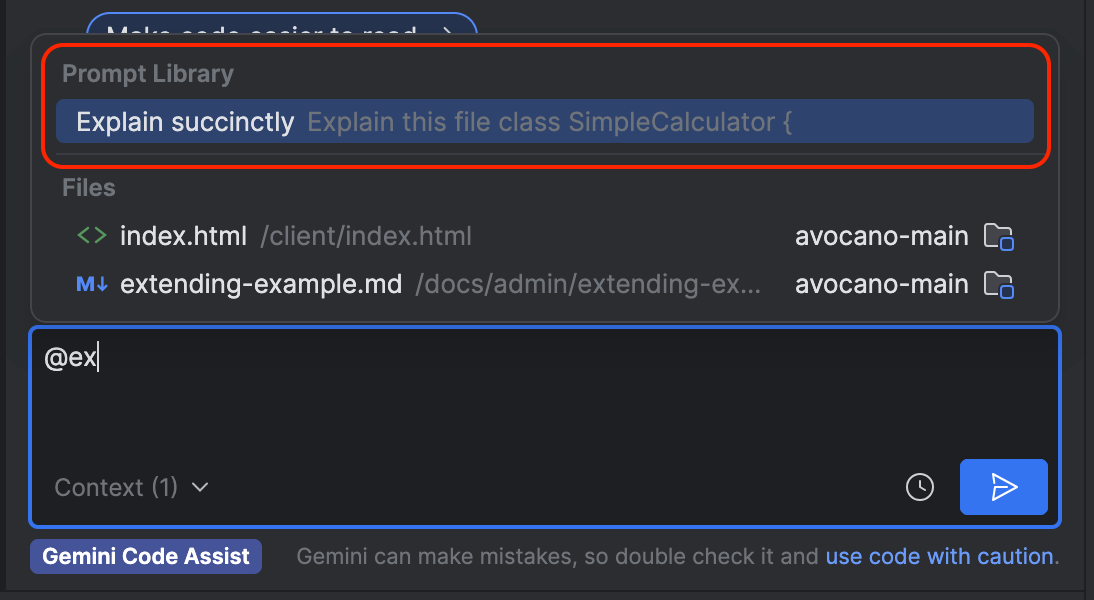
Copy sign-in link
As an alternative to clicking Sign in when signing into your Google Account to use IntelliJ Gemini Code Assist, you can click Copy link and manually paste the link in your browser's URL bar.
Gemini Enterprise: Change in ACLs for incidents in ServiceNow
The access-control list (ACL) behavior for ServiceNow incidents has significantly changed, from too permissive to least-privilege behavior. This change drastically reduces the possibility of data leaks, but might be too restrictive for your needs.
For more information about ServiceNow, see Connect ServiceNow and Add ServiceNow actions.
Gemini 2.5 Flash with Live API Native Audio Preview
Gemini 2.5 Flash with Live API Native Audio (gemini-live-2.5-flash-preview-native-audio-09-2025) is available in Preview. A single, unified model processes audio input and generates audio output directly, eliminating separate text-to-speech/speech-to-text conversions. This results in-low latency, high-quality, and incredibly human-like conversations. New features and capabilities include:
Improved Barge-in: Interrupt Gemini more naturally and reliably, even in loud and noisy environments.
Robust Function Calling: We've improved the triggering rate, allowing Gemini to successfully execute the functions you define with greater precision.
Accurate Transcription: The accuracy of audio-to-text transcription has been significantly enhanced.
Seamless Multilingual Support: Speak to Gemini in multiple languages, and it will effortlessly switch between them without any pre-configuration. Language is no longer a barrier!
Enhanced Audio Quality: Experience a dramatically improved audio quality that truly feels like speaking with a person.
Proactive Audio: Define Gemini's expertise and set conditions for when it should respond. Gemini can act as a "silent listener," only chiming in when the conversation touches upon its designated area of expertise.
Affective Dialog: Gemini can adapt and adjust its generated voice to match the emotional tone of the speaker, creating more empathetic and natural interactions.
Watch our comprehensive demo to see these features in action, including seamless language switching, expert mode, emotionally aware responses, memory recall, and interactive screen sharing for engineering tasks – all demonstrated directly within Vertex AI Studio without writing a single line of code!
The following metrics are now only billed through Cloud Monitoring. If you were using any of these features through GKE Enterprise, your billing is automatically transitioned to the Cloud Monitoring SKU.
These metrics use Google Cloud Managed Service for Prometheus to load metrics into Cloud Monitoring. The Cloud Monitoring charges for the ingestion of these metrics are based on the number of samples ingested. For more information, see Cloud Monitoring pricing.
Transport-layer migration for third-party API feeds
Google SecOps is migrating the transport layer for third-party API feeds to a new platform to improve performance and reliability. This migration will be completed in phases and is expected to finish by the end of October 2025. The migration should not impact any existing or new, third-party API feeds. If you experience any unexpected issues with your feeds during the migration, contact your Google SecOps representative.
You can now connect to your Looker instance with the Gemini CLI using a dedicated Gemini extension. The Gemini extension can run queries, create Looks and dashboards, and retrieve elements of your LookML models.
Google Cloud Managed Lustre now supports file system quotas, allowing you to set limits on the amount of disk space and the number of files that users, groups, or projects can consume within your file system.
For details, see File system quotas in the Managed Lustre documentation.
Oracle Database@Google Cloud supports Exadata Database Service on Exascale Infrastructure, which lets you create and manage Exascale VM Clusters and Exascale Storage Vaults. This feature is generally available (GA).
Bulk export findings to BigQuery is available in General Availability. Bulk exports are supported for organizations, projects, and folders.
The upgraded model for the prompt injection and jailbreak detection filter is available in EU multi-region. This model has improved detection rates across several attack vectors, including the following:
- Do Anything Now prompts
- System instruction manipulation
- Unauthorized action execution
- Sensitive information retrieval
You can now use read lease regions to reduce latency for strong reads in multi-region or dual-region instances. Read leases use designated non-leader, read-write or read-only regions to serve strong reads locally, eliminating the network round trip to the leader region that is typically required. This feature is generally available (GA).
You can now use the dedicated Gemini CLI extension for Spanner to execute SQL statements and query your Spanner instance using natural language controls.
General availability support for the following integration:
General availability support for the following integration:
Service producers can publish services that are hosted on cross-region internal Application Load Balancers. This feature is available in General Availability. For more information, see Publish services by using Private Service Connect.
September 22, 2025
AlloyDB for PostgreSQLThe available memory metric now accurately reflects the memory available to AlloyDB by taking into consideration usable memory from the OS page cache. This improvement can lead to a lower value of the metric, which you might notice when you update your version to PG 17 or later. This feature is generally available (GA) and is available for AlloyDB for PostgreSQL version 17 and later. For more information, see System insights metrics reference.
Database server compatibility with PostgreSQL version 17 is now generally available (GA). You can create AlloyDB clusters with PostgreSQL 17 compatibility.
You can now run federated queries against PostgreSQL dialect databases in Spanner using BigQuery external datasets with GoogleSQL; this includes cross-region federated queries. This feature is generally available (GA).
Cloud Logging has removed the quota for write requests per minute, which has been replaced by volume-based regional quotas. We've also removed the references to August dates for the removal of the old quota from the public documentation. For more information, see Logging API quotas and limits.
A weekly digest of client library updates from across the Cloud SDK.
Go
Changes for storage/internal/apiv2
1.56.2 (2025-09-15)
Bug Fixes
Python
Changes for google-cloud-storage
3.4.0 (2025-09-15)
Features
- experimental: Add async grpc client (#1537) (ac57b8d)
- experimental: Add grpc client (#1533) (5674587)
Bug Fixes
Generally available: You can create and use Flex-start VMs. Flex-start VMs are virtual machine (VM) instances that can run for up to seven days, and that use the flex-start provisioning model. This model provisions resources from a secure pool of capacity, increasing your chances of obtaining high-demand resources like GPUs. These features make Flex-start VMs suitable for short-duration workloads that can start at any time, such as the following:
- Small model pre-training
- Model fine-tuning
- High performance computing (HPC) simulation
- Batch inference
You can create standalone Flex-start VMs, or add Flex-start VMs all at once to a managed instance group (MIG) by using resize requests. Based on the machine type that your Flex-start VMs use, you get discounts for vCPUs, memory, and any attached GPUs.
For more information, see About Flex-start VMs.
Modified Beta Reconciliation: We migrated the following resources from the Terraform-based or DCL-based controller to the new Direct Controller.
VMWareEngineExternalAddress
New Beta Resources (Direct Reconciler):
AssetSavedQueryPubSubSnapshot
New Fields:
AlloyDBCluster- Added
spec.databaseVersionfield
- Added
Config Connector version 1.135.0 is now available.
Bug Fixes:
- PR#5009 Fix the nil pointer dereference error in AlloyDB direct controller
DeepSeek-V3.1-Terminus is available through Model Garden.
Graph search lets you explore the security graph using custom queries. This product is available in Preview in the Security Command Center Enterprise tier.
The DOCUMENT_TYPE/FINANCE/INVOICE and DOCUMENT_TYPE/MEDICAL/RECORD infoType detectors are available in global and the asia, europe, and us multi-regions. For more information about all infoTypes, see InfoType detector reference.
You can now run federated queries against PostgreSQL dialect databases in Spanner using BigQuery external datasets using GoogleSQL; this includes cross-region federated queries. This feature is generally available (GA).
DeepSeek-V3.1-Terminus is available through Model Garden.
