SOAR-Logs erfassen
In diesem Dokument wird beschrieben, wie Sie mit dem Google Cloud Logs Explorer SOAR-Logs verwalten und überwachen.
Die Integration bietet die folgenden wichtigen Funktionen:
Zentralisiertes Monitoring: Sie können wichtige Daten ansehen und analysieren, die von den ETL-, Playbook- und Python-Funktionen der Google SecOps SOAR-Plattform erfasst werden, z. B. die Ausführung von Python-Skripts, die Aufnahme von Benachrichtigungen und die Playbook-Leistung.
Benutzerdefinierte Messwerte und Benachrichtigungen: Mit Google Cloud Tools können Sie benutzerdefinierte Messwerte und Benachrichtigungen basierend auf bestimmten Ereignissen konfigurieren, die in den Betriebslogs von Google SecOps SOAR aufgezeichnet werden.
SOAR-Logs einrichten
So richten Sie die SOAR-Logs ein:
- Erstellen Sie ein Dienstkonto im Projekt Google Cloud , in dem Sie die Logs ansehen möchten. Weitere Informationen finden Sie unter Dienstkonten erstellen und verwalten.
- Rufen Sie IAM & Verwaltung > IAM auf.
Suchen Sie das von Ihnen erstellte Dienstkonto und klicken Sie auf Bearbeiten Hauptkonto bearbeiten.
Wählen Sie im Abschnitt Rollen zuweisen die Option Log-Autor aus. Weitere Informationen finden Sie unter Vordefinierte Rolle „Logs Writer“.
Klicken Sie auf Speichern.
Wählen Sie Dienstkonten und dann das von Ihnen erstellte Dienstkonto aus.
Klicken Sie auf das Dreipunkt-Menü Weitere und wählen Sie Berechtigungen verwalten aus.
Klicken Sie im Bereich Berechtigungen auf Zugriff erlauben.
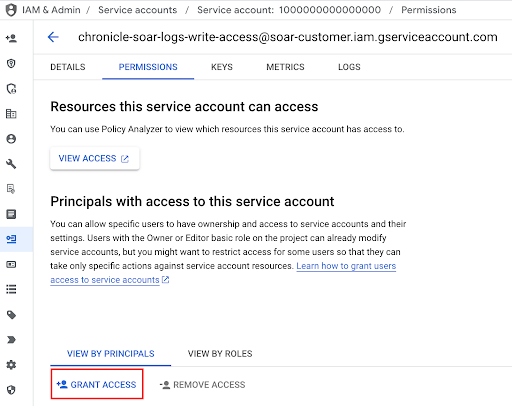
Fügen Sie im Abschnitt Hauptkonto hinzufügen das folgende Hauptkonto hinzu:
gke-init-backgroundservices@{SOAR-GCP-Project-Id}.iam.gserviceaccount.com- Wenn Sie die
SOAR_GCP_Project_Idnicht kennen, senden Sie ein Ticket über den Google-Support.
- Wenn Sie die
Wählen Sie unter Rollen zuweisen die Option Ersteller von Dienstkonto-Tokens aus. Weitere Informationen finden Sie unter Service Account Token Creator.
Klicken Sie auf Speichern.
Geben Sie dem Google SecOps-Supportteam den Namen des konfigurierten Dienstkontos an.
SOAR-Logs
SOAR-Logs werden in einem separaten Namespace namens chronicle-soar geschrieben und nach dem Dienst kategorisiert, der das Log generiert hat.
Da die Logs von einem Hintergrundjob generiert werden, müssen Sie diesen Job zuerst konfigurieren, um die Logs an Google Cloudzu senden:
So greifen Sie auf SOAR-Logs zu:
- Rufen Sie in der Google Cloud Console Logging > Log-Explorer auf.
- Wählen Sie das Projekt Google SecOps Google Cloud aus.
Geben Sie den folgenden Filter in das Feld ein und klicken Sie auf Abfrage ausführen:
resource.labels.namespace_name="chronicle-soar"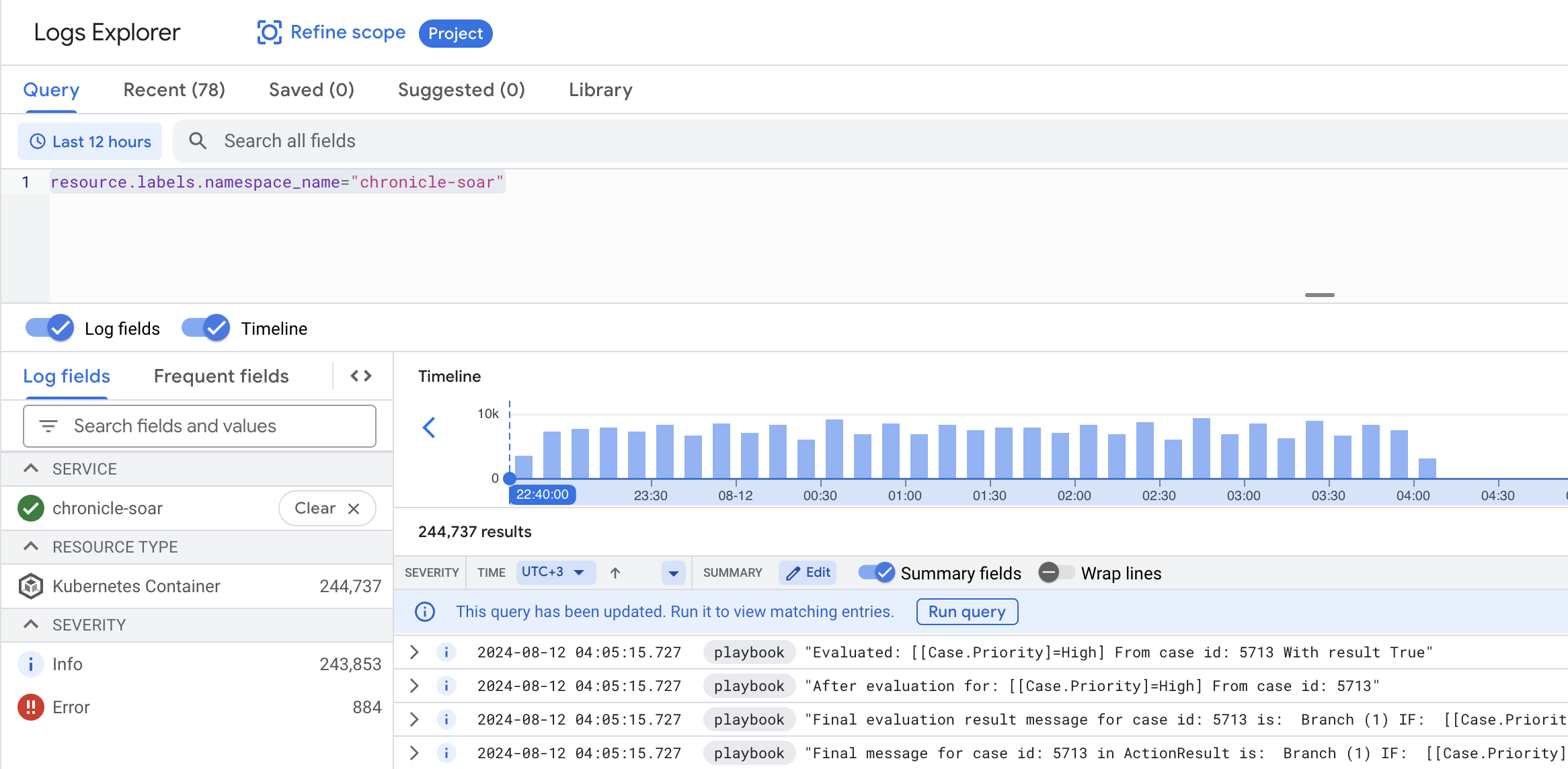
Wenn Sie Logs eines bestimmten Dienstes filtern möchten, geben Sie die folgende Syntax in das Abfragefeld ein und klicken Sie auf Abfrage ausführen:
resource.labels.namespace_name="chronicle-soar" resource.labels.container_name="<container_name>"Ersetzen Sie
<container_name>durch den entsprechenden Servicecontainer:playbook,pythonoderetl.
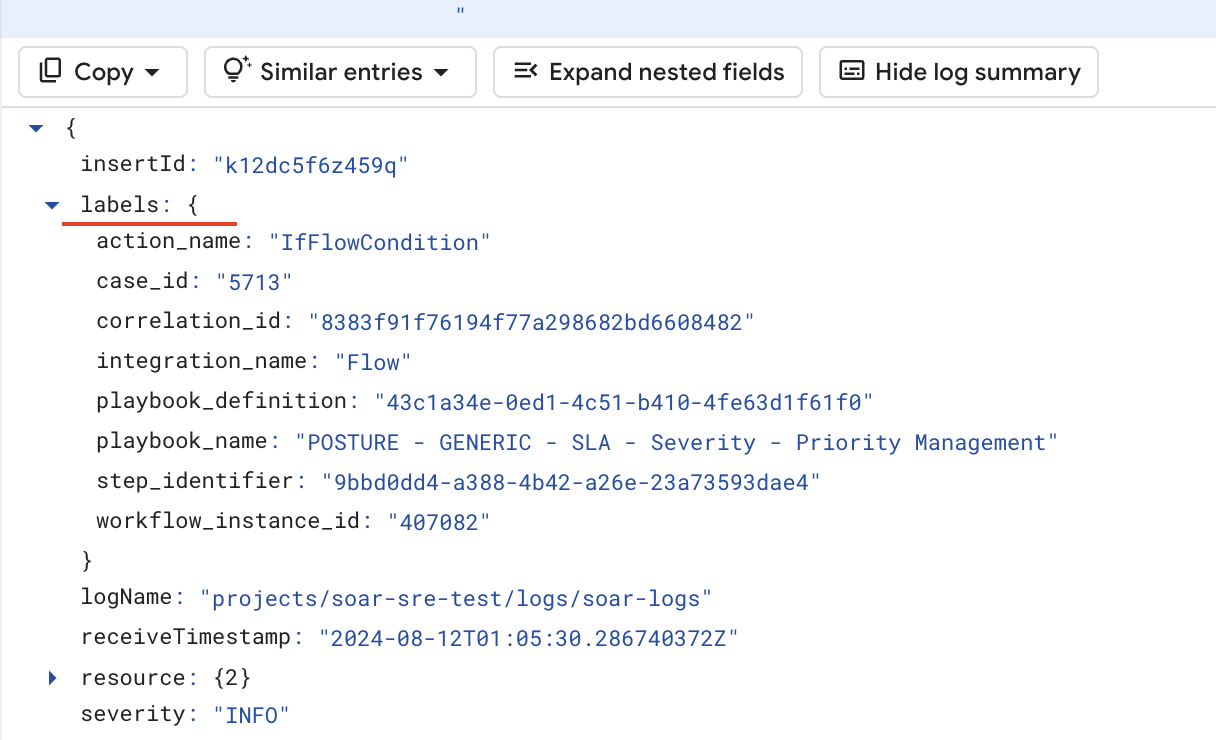
Playbook-Loglabels
Mit Playbook-Loglabels lässt sich der Umfang einer Abfrage effizienter und bequemer eingrenzen. Alle Labels befinden sich im Bereich Labels jeder Log-Nachricht.
Wenn Sie den Logbereich eingrenzen möchten, maximieren Sie die Lognachricht, klicken Sie mit der rechten Maustaste auf die einzelnen Labels und blenden Sie bestimmte Logs ein oder aus:
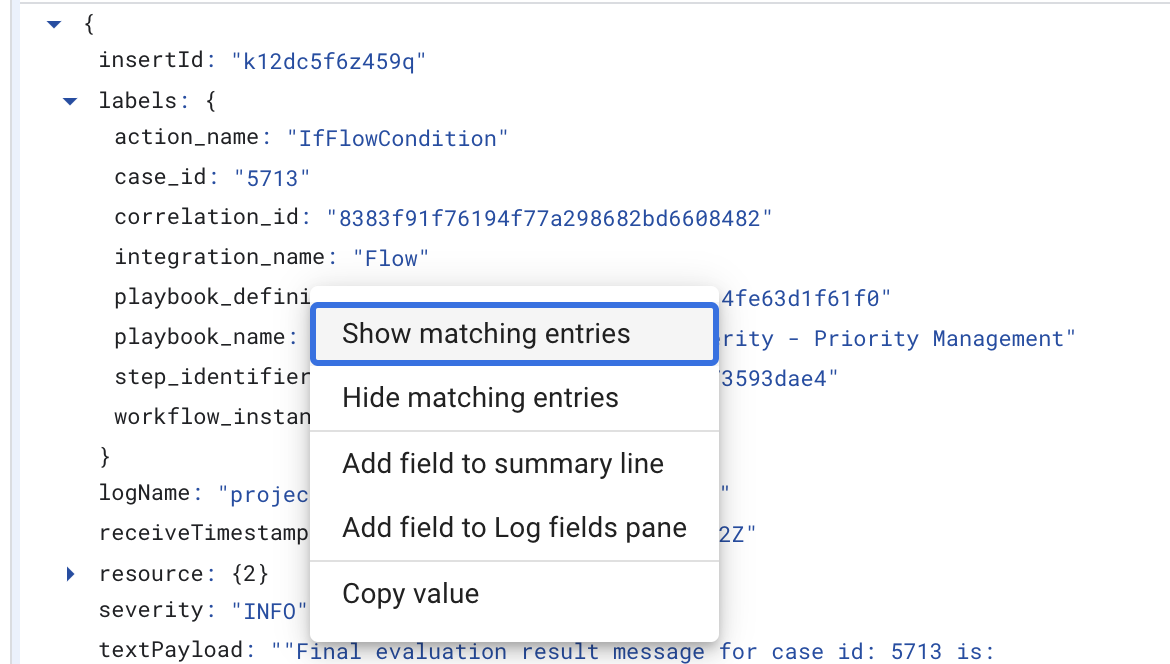
Die folgenden Labels sind verfügbar:
playbook_nameplaybook_definitionblock_nameblock_definitioncase_idcorrelation_idintegration_nameaction_name
Python-Logs
Die folgenden Logs sind für den Python-Dienst verfügbar:
```none
resource.labels.container_name="python"
```
Labels für Integrationen und Connectors:
integration_nameintegration_versionconnector_nameconnector_instance
Job-Labels:
integration_nameintegration_versionjob_name
Aktionslabels:
integration_nameintegration_versionintegration_instancecorrelation_idaction_name
ETL-Logs
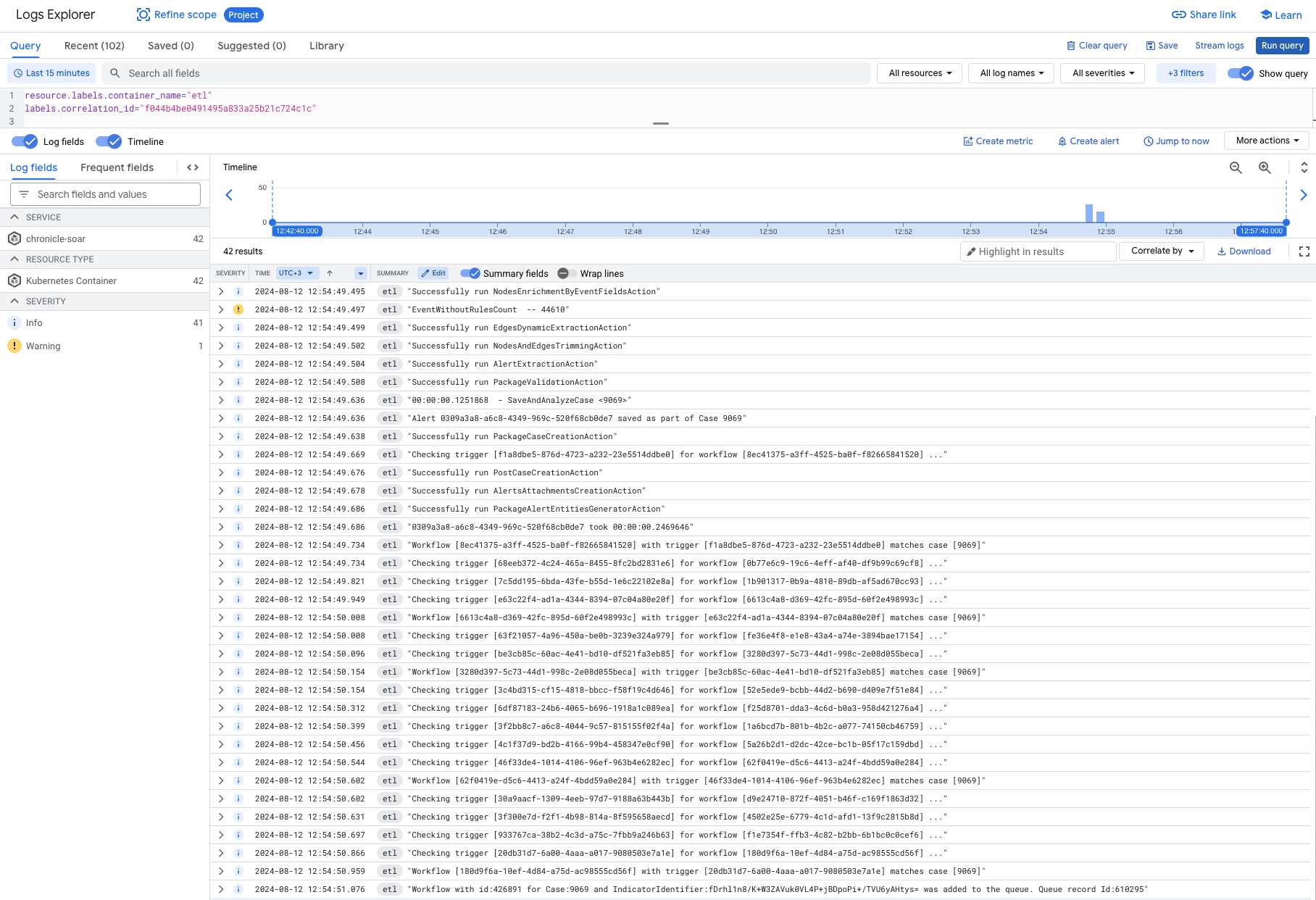
Die folgenden Logs sind für den ETL-Dienst verfügbar:
```none
resource.labels.container_name="etl"
```
ETL-Labels
correlation_id
Wenn Sie beispielsweise den Erfassungsablauf für eine Benachrichtigung angeben möchten, filtern Sie nach correlation_id:
Benötigen Sie weitere Hilfe? Antworten von Community-Mitgliedern und Google SecOps-Experten erhalten

