Meninjau pemberitahuan menggunakan Google Security Operations
Apa yang dimaksud dengan peringatan?
Peringatan adalah Indikator Gangguan (IOC), yang ditandai oleh Google Security Operations, yang menunjukkan anomali dalam alur kerja traffic yang normal dalam perusahaan. Anda harus menyelidiki pemberitahuan sebagai kemungkinan pelanggaran keamanan.
Bagaimana cara pemberitahuan masuk ke Google Security Operations?
Google Security Operations memanfaatkan berbagai sumber eksternal dalam komunitas keamanan menggunakan database di seluruh industri yang terus diperbarui. Google Security Operations juga memiliki bahasa pemrograman kaya fitur, YARA-L, sehingga Anda dapat membuat aturan kustom sendiri.
Untuk mengetahui informasi selengkapnya tentang YARA-L, lihat Ringkasan bahasa YARA-L 2.0. Untuk mengetahui informasi selengkapnya tentang aturan, lihat Mengelola Aturan Menggunakan Editor Aturan.
Sebelum memulai
Anda dapat melakukan langkah-langkah ini dari instance Google Security Operations perusahaan Anda atau dari lingkungan demo Google Security Operations.
Google Security Operations dirancang untuk berfungsi secara eksklusif dengan browser Google Chrome atau Mozilla Firefox.
Google merekomendasikan agar Anda mengupgrade browser ke versi terbaru. Anda dapat mendownload Chrome versi terbaru dari https://www.google.com/chrome/.
Google SecOps terintegrasi ke dalam solusi single sign-on (SSO) Anda. Anda dapat login ke Google SecOps menggunakan kredensial yang disediakan oleh perusahaan Anda.
Luncurkan Chrome atau Firefox.
Pastikan Anda memiliki akses ke akun perusahaan Anda.
Untuk mengakses aplikasi Google SecOps, dengan customer_subdomain adalah ID khusus pelanggan Anda, buka: https://customer_subdomain.backstory.chronicle.security.
Melihat Pemberitahuan dan Kecocokan IOC
Di panel navigasi, pilih Detection > Alerts and IOCs.
Tab Alerts dan IOC Matches ditampilkan. Anda mungkin harus menyesuaikan rentang waktu menggunakan kontrol kalender di kanan atas agar kecocokan dan pemberitahuan muncul.
Beralih ke tampilan Aset
Selanjutnya, lihat detail aset tertentu yang mungkin telah disusupi.
Dari tab IOC Matches, klik domain untuk membuka tampilan Domain.
Pilih tab Linimasa.
Untuk beralih ke tampilan Aset, pilih peristiwa dengan mengklik waktunya. Tampilan aset menampilkan detail aset yang dipilih di sekitar linimasa pemicu pemberitahuan, seperti yang ditunjukkan pada gambar berikut.
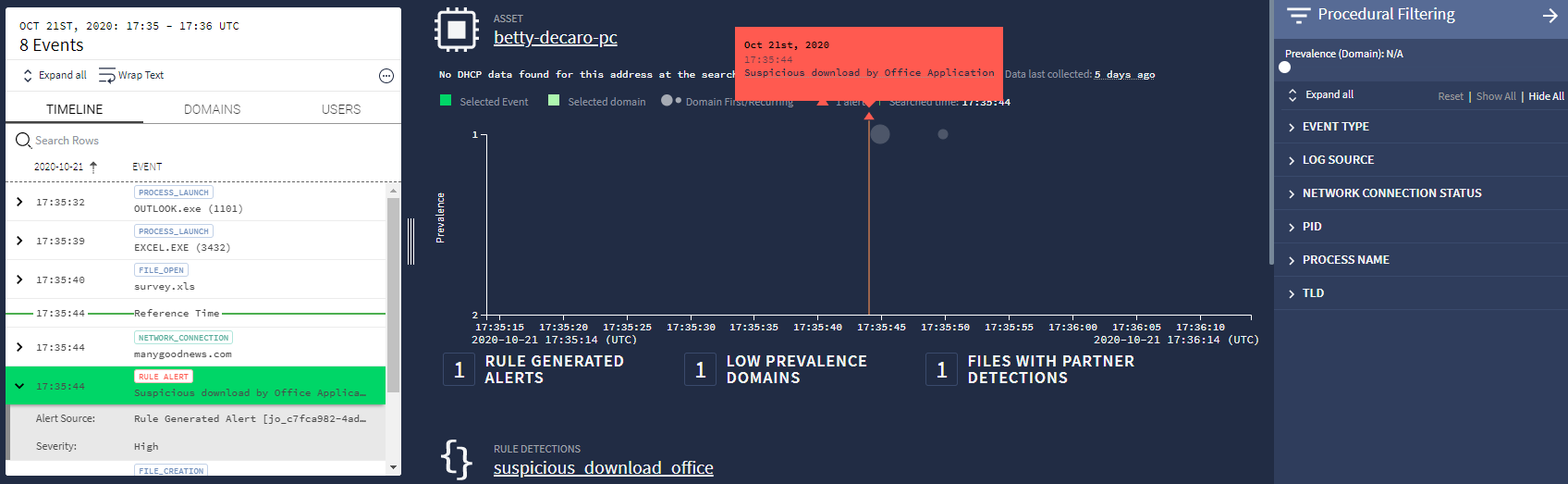 Tampilan aset
Tampilan asetBalon di jendela utama menunjukkan prevalensi aset. Grafik disusun sehingga peristiwa yang lebih jarang terjadi berada di bagian atas. Peristiwa dengan prevalensi rendah ini dianggap mencurigakan. Gunakan Penggeser waktu di kanan atas untuk memperbesar peristiwa yang memerlukan penyelidikan.
Jika menu Pemfilteran Prosedural tidak terlihat, buka dengan mengklik ikon Filter
 (di dekat sudut kanan atas).
(di dekat sudut kanan atas).Di bagian atas menu, sesuaikan penggeser Prevalensi untuk memfilter peristiwa umum. Menggunakan penggeser Waktu dan Prevalensi untuk mengidentifikasi peristiwa mencurigakan.
Buka notifikasi dari daftar sidebar Linimasa. Di panel kiri, pilih tab Linimasa yang menampilkan peristiwa yang terjadi di sekitar pemberitahuan. Peristiwa pemicu disorot dengan warna hijau.
Menyelidiki apa yang memicu notifikasi
Ada beberapa cara untuk mendapatkan lebih banyak insight tentang peristiwa pemicu.
Di panel tengah, kotak dialog berwarna oranye dapat muncul di atas segitiga oranye kecil yang menunjukkan lokasi, dalam waktu, peringatan. Jika kotak dialog tidak ditampilkan, mengarahkan kursor ke segitiga akan membuatnya muncul. Dialog berisi tanggal, waktu, dan deskripsi notifikasi.
Panel kiri di tampilan Aset menampilkan tab Linimasa. Jika diberi label Pemberitahuan Aturan, acara tersebut juga akan menyebutkan deskripsi pemberitahuan.
Mengarahkan kursor ke peristiwa Rule Alert akan menyebabkan ikon Perluas
 muncul di sisi kanan peristiwa. Mengklik ikon ini akan membuka jendela baru dengan detail selengkapnya tentang peristiwa dalam format UDM, seperti yang ditunjukkan pada gambar berikut.
muncul di sisi kanan peristiwa. Mengklik ikon ini akan membuka jendela baru dengan detail selengkapnya tentang peristiwa dalam format UDM, seperti yang ditunjukkan pada gambar berikut.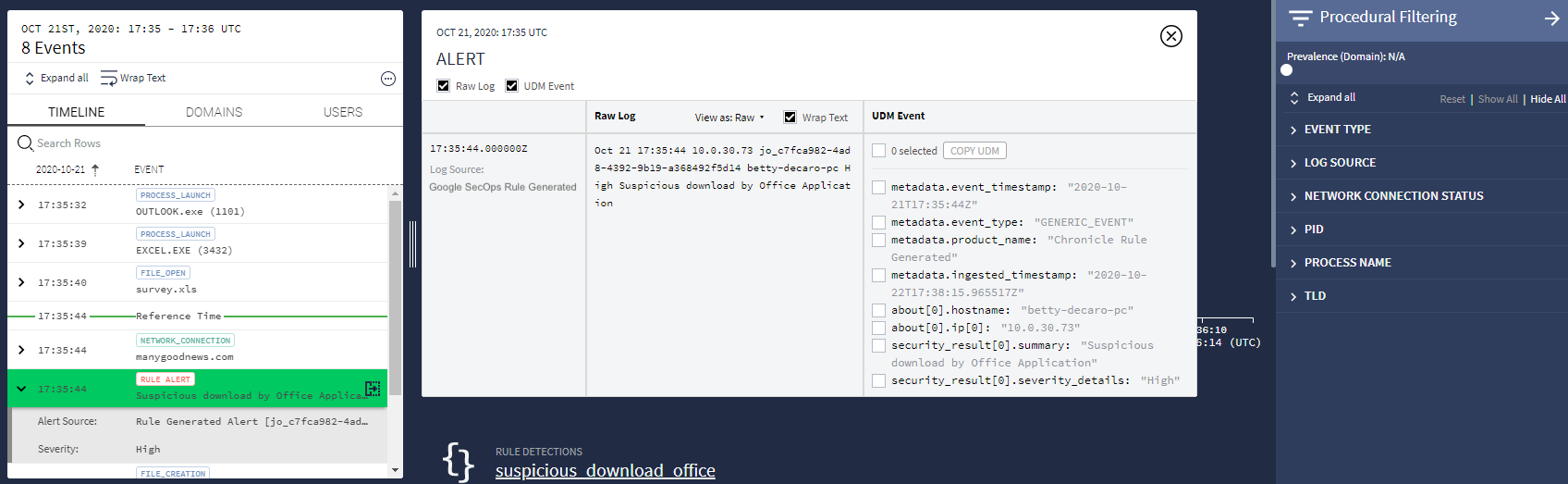 Detail Acara
Detail Acara
Perlu bantuan lain? Dapatkan jawaban dari anggota Komunitas dan profesional Google SecOps.

