配置规则排除项
通过“排除对象”标签页创建排除对象
您可能会发现, Google Cloud 威胁情报 (GCTI) 团队提供的精选检测生成了过多的检测结果。您可以为精选的检测规则配置排除对象,以帮助减少这些检测的数量。规则排除项仅适用于 Google Security Operations 精选检测。
如需为精选检测规则配置排除对象,请完成以下步骤:
在导航栏中,选择规则和检测。点击排除对象标签页。
点击创建排除项以创建新的排除项。系统随即会打开创建排除对象窗口。
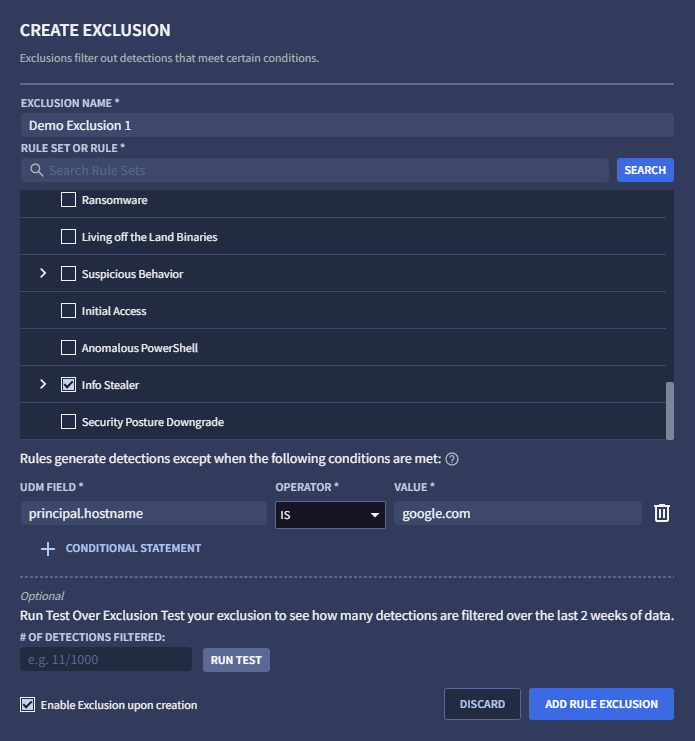
图 1:创建排除对象
指定一个唯一的排除对象名称。此名称将显示在“排除对象”标签页的排除对象列表中。
选择要应用排除规则的规则或规则集。您可以滚动浏览规则列表,也可以使用搜索字段搜索特定规则,然后点击搜索。 只有在规则集中的规则触发检测时,系统才会显示这些规则。
选择 UDM 字段、指定运算符并输入值,以输入要排除的 UDM 值。您必须为每个值按 Enter 键,否则在点击 + 条件语句时会收到错误消息。例如,您可能希望在
principal.hostname = google.com时配置排除项。您可以为条件输入其他值。每次按 Enter 键后,系统都会记录相应值,然后您便可以输入另一个值。一个条件的多个值使用逻辑 OR 进行联接,这意味着如果任何值匹配,排除对象就会匹配。
您可以点击 + 条件语句,为此排除对象添加其他条件。如果您尝试指定无效条件,则会收到错误消息。多个条件使用逻辑 AND 联接,这意味着只有当所有条件都匹配时,排除对象才会匹配。
(可选)点击运行测试,以确定启用排除功能后会排除多少检测结果(通过评估过去两周记录的检测结果来计算)。
(可选)如果您想暂时停用排除对象,请取消选中创建排除对象后即启用(此选项默认处于启用状态)。
准备就绪后,点击添加规则排除对象。
从 UDM 查看器创建排除对象
您还可以通过完成以下步骤,在 UDM 查看器中创建排除对象:
在导航栏中,选择规则和检测。点击精选检测结果标签页。
点击信息中心,然后选择包含检测结果的规则。
在时间轴中找到相应事件,然后点击“原始日志和 UDM 事件查看器”图标。
在 UDM 事件视图中,选择要排除的 UDM 字段,选择查看选项,然后选择排除。系统随即会打开创建排除对象窗口。系统会根据您选择的 UDM 预先填充窗口中的规则、UDM 字段和值。
为新的排除对象指定一个唯一名称。
(可选)点击运行测试,以确定启用排除功能后会排除多少检测结果(通过评估过去两周记录的检测结果来计算)。
准备就绪后,点击添加规则排除对象。
管理排除项
创建一项或多项排除对象后,您可以在排除对象标签页中执行以下操作(在导航栏中,选择规则和检测。点击排除对象标签页):
- 排除对象列在排除对象表中。您可以将已启用开关切换为已停用,以停用列出的任何排除对象。
- 您可以点击过滤图标 ,过滤显示哪些排除对象。根据需要选择已启用、已停用或已归档选项。
- 如需修改排除对象,请点击菜单图标 ,然后选择修改。
- 如需归档排除对象,请点击菜单图标 ,然后选择归档。
- 如需取消归档排除对象,请点击菜单图标 ,然后选择取消归档。
需要更多帮助?从社区成员和 Google SecOps 专业人士那里获得解答。

