使用“精选检测”页面
本文档介绍了如何使用精选检测页面。
对于 Google Security Operations 客户, Google Cloud Threat Intelligence (GCTI) 团队正在提供开箱即用的威胁分析,作为 Google Cloud 安全共同命运模型的一部分。作为这些精选检测规则的一部分,GCTI 提供并管理一组 YARA-L 规则,以帮助客户识别企业面临的威胁。 这些由 GCTI 管理的规则:
为客户提供可立即采取行动的智能分析,以便他们根据提取的数据采取行动。
通过为客户提供在 Google SecOps 中使用 Google 威胁情报的方式,充分利用 Google 的威胁情报。
准备工作
如需了解预定义的威胁检测政策,请参阅以下内容:
- “云威胁”类别概览
- “Chrome 企业版威胁”类别概览
- “Windows 威胁”类别概览
- “Linux 威胁”类别概览
- “macOS 威胁”类别概览
- UEBA 类别的风险分析概览
- “实用威胁情报”类别概览
如需验证每项政策所需的数据是否采用正确的格式,请参阅使用测试规则验证日志数据注入。
精选检测功能
以下是精选检测功能的一些主要特点:
精选检测:由 GCTI 为 Google SecOps 客户创建和管理的精选检测。
规则集:由 GCTI 为 Google SecOps 客户管理的一组规则。GCTI 提供并维护多个规则集。客户可以选择在 Google SecOps 账号中启用或停用这些规则,以及启用或停用针对这些规则的提醒。随着威胁形势的变化,GCTI 会定期提供新的规则和规则集。
打开精选检测页面和规则集
如需打开精选检测页面,请完成以下步骤:
从主菜单中选择规则。
点击精选检测以打开规则集视图。
“精选检测”页面会提供有关您的 Google SecOps 账号中处于有效状态的每个规则集的信息,包括:
上次更新时间:GCTI 上次更新规则集的时间。
已启用的规则:指明了每个规则集启用了哪些精确规则和宽泛规则。精确的规则会发现恶意威胁,且可信度高。宽泛的规则会搜索可能更常见的可疑行为,并产生更多误报。一个规则集可能同时包含精确规则和宽泛规则。
提醒:指示每个规则集的精确规则和宽泛规则中哪些已启用提醒。
Mitre 策略:每个规则集涵盖的 Mitre ATT&CK® 策略的标识符。MITRE ATT&CK® 策略代表恶意行为背后的意图。
Mitre 技术:每个规则集涵盖的 Mitre ATT&CK® 技术的标识符。Mitre ATT&CK® 技术代表恶意行为的具体做法
在此页面上,您还可以启用或停用相应规则以及针对该规则的提醒。您可以针对宽泛规则或精细规则执行此操作。
打开精选检测信息中心
精选检测信息中心会显示每项精选检测的相关信息,这些检测已针对您 Google SecOps 账号中的日志数据生成检测结果。检测到问题的规则按规则集分组。
如需打开精选的检测信息中心,请完成以下步骤:
从主菜单中选择规则。默认标签页是精选检测,默认视图是规则集。
点击信息中心。
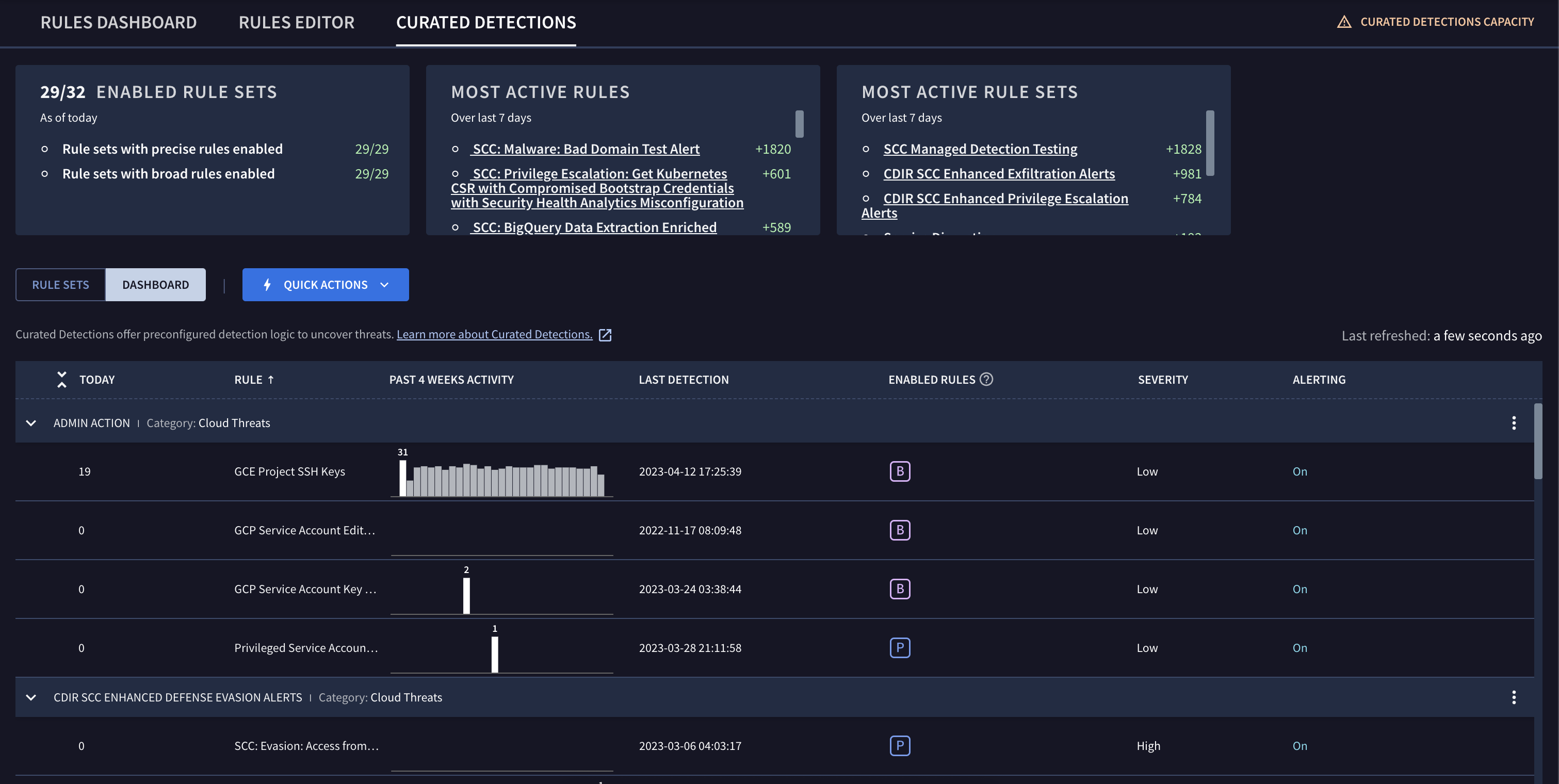
图 2:精选检测信息中心
“精选检测”信息中心会显示您的 Google SecOps 账号可用的每个规则集。每个展示广告都包含以下内容:
图表,用于跟踪与规则集关联的每条规则的当前活动。
上次检测的时间。
每条规则的状态。
近期检测结果的严重程度。
提醒功能处于启用还是停用状态。
您可以点击菜单图标 或规则集名称来修改规则设置。
点击规则集可切换回规则集视图。“规则集”视图会提供有关您的 Google SecOps 账号中处于有效状态的每个规则集的信息。
查看规则集的详细信息
您可以修改任何精选检测的设置,方法是点击规则集的菜单图标 ,然后选择查看和修改规则设置。
您可以在设置部分下启用或停用规则集。 通过状态和提醒切换开关,您可以启用或停用规则集中的精确规则和宽泛规则。您还可以开启或关闭提醒功能。
您还可以查看为规则集配置的所有排除对象。您可以点击查看来修改排除对象。如需了解详情,请参阅配置规则排除项。
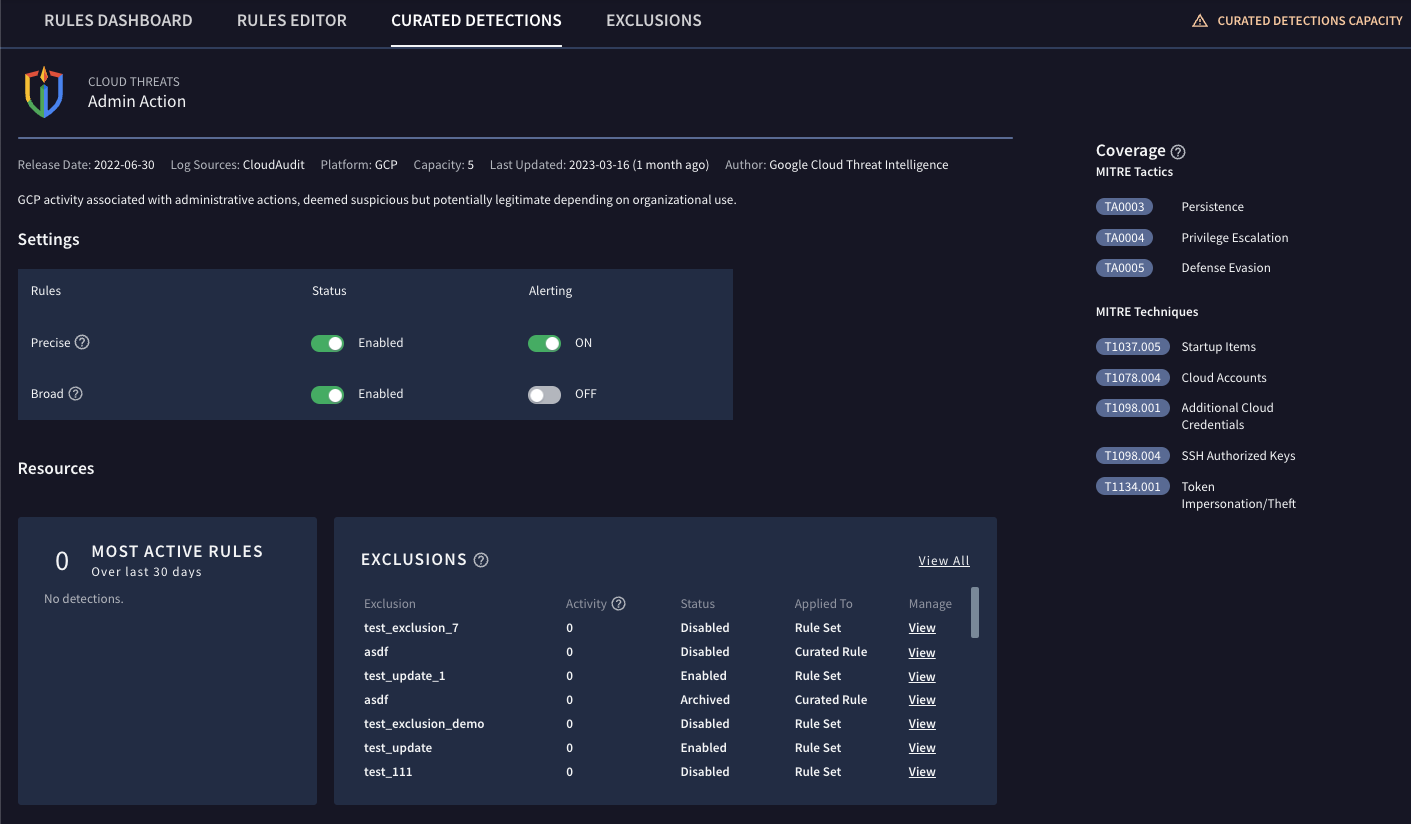
图 3:规则设置
修改规则集中的所有规则
设置部分会显示规则集中所有规则的设置。您可以修改设置,以创建专门针对组织使用情况和需求的精选检测。
精确的规则:可发现恶意行为,且可信度高,假正例较少,因为规则更具体。
宽泛的规则:发现可能有恶意的行为或异常情况,但由于规则的通用性更强,假正例通常较多。
状态:将相应状态选项设置为已启用,即可将规则的状态设为“精细”或“宽泛”。
提醒:将提醒选项设置为开启,即可启用提醒功能,以便接收相应精确规则或宽泛规则创建的检测。
配置规则排除项
如需管理 GCTI 精选检测的提醒量,您可以配置规则排除项。如需了解详情,请参阅配置规则排除对象。
查看精选检测
您可以在“精选检测”视图中查看任何精选检测。在此视图中,您可以检查与规则相关联的任何检测结果,并从时间轴切换到其他视图,例如资产视图。
如需打开精选检测视图,请完成以下步骤:
点击信息中心。
点击“规则”列中的规则名称链接。
后续步骤
需要更多帮助?从社区成员和 Google SecOps 专业人士那里获得解答。

