针对历史数据运行规则
创建和启用新规则后,规则会开始根据您的 Google Security Operations 账号接收的事件实时搜索检测。借助 Retrohunt 功能,您可以使用所选规则在 Google SecOps 中的现有数据中搜索检测。当有可用资源可供运行时,系统会安排回溯性搜索。回溯性搜索的运行时间可能会有所不同。
如需开始 Retrohunt,请完成以下步骤:
转到“规则信息中心”。
点击规则的“规则选项”图标,然后选择 Yara-L Retrohunt。
 YARA-L Retrohunt 选项
YARA-L Retrohunt 选项在 YARA-L Retrohunt 窗口中,选择搜索的开始时间和结束时间。默认值为一周。此窗口提供了可用的日期和时间范围。对于多事件规则,回溯搜索范围必须大于或等于匹配窗口大小。
点击运行。
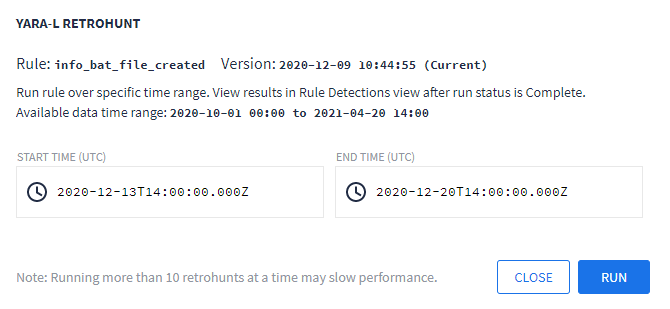
Yara-L Retrohunt 对话框窗口
您可以通过“规则检测”视图来查看 Retrohunt 运行的进度。如果您取消正在进行的 Retrohunt,则仍可以查看其在运行时可用的检测结果。
如果您已完成多个 Retrohunt,则可以点击日期范围链接来查看过去的运行结果,如下图所示。每次运行的结果都会显示在“规则检测”视图的“时间轴”和“检测”图中。
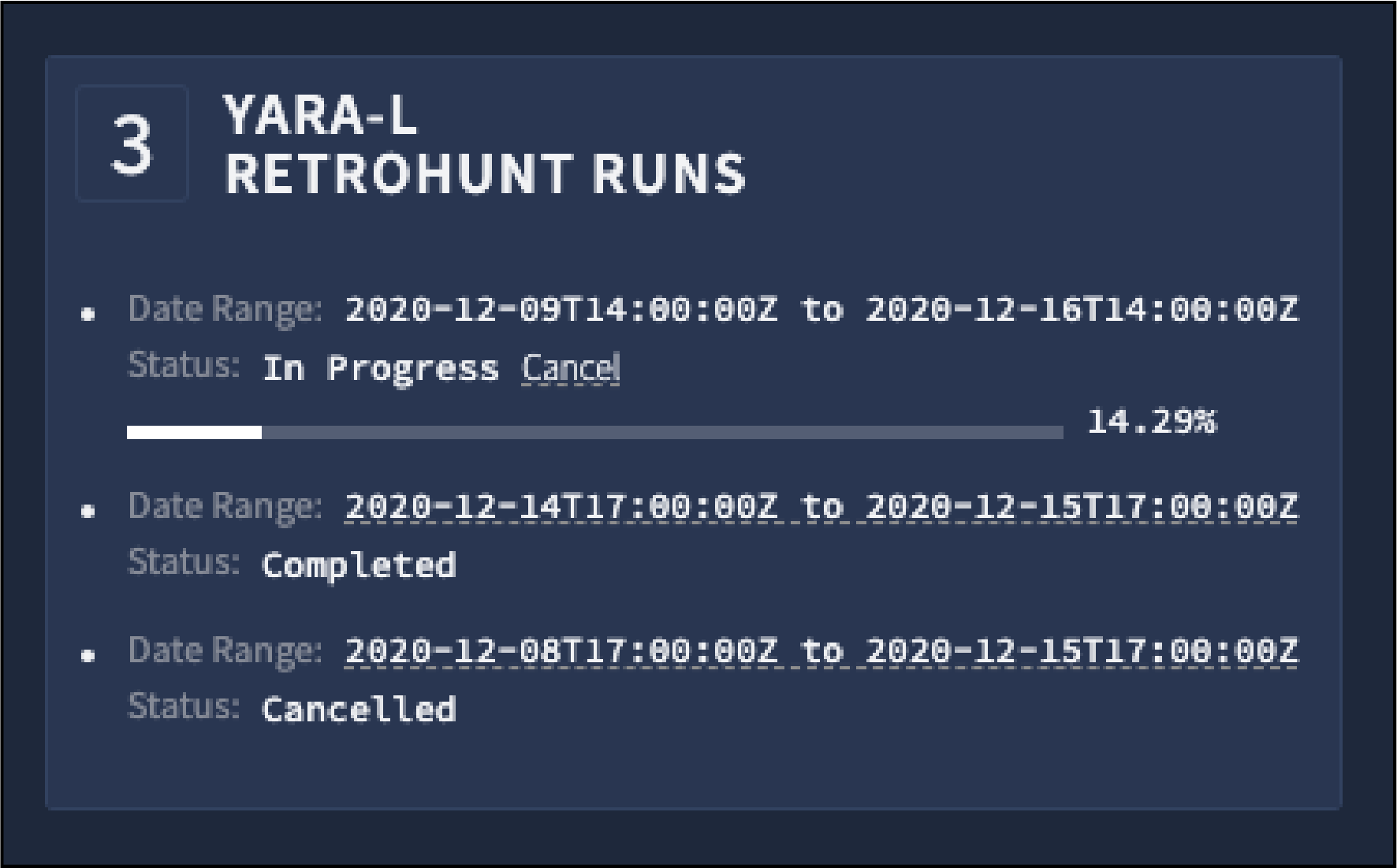
Yara-L Retrohunt 运行
如果您在规则中使用参考列表,运行回溯搜索,然后从该列表中移除项目,则需要将该规则修订为新版本,才能看到新结果。Google SecOps 不会从参考列表中删除检测结果,因此刷新规则不会更新结果。
需要更多帮助?从社区成员和 Google SecOps 专业人士那里获得解答。

