Halaman ini berlaku untuk Apigee, tetapi tidak untuk Apigee Hybrid.
Lihat dokumentasi
Apigee Edge.
![]()
Apigee memfasilitasi komunikasi antara permintaan API klien dan layanan Apigee dan Cloud melalui koneksi antara dua jaringan: VPC Apigee (atau runtime plane) dan VPC Pelanggan. Kedua jaringan ini diikat bersama menggunakan koneksi pribadi dalam proses yang dikenal sebagai peering VPC.
Contoh berikut menunjukkan cara peering VPC memungkinkan komunikasi antara VPC Apigee dan VPC Pelanggan:
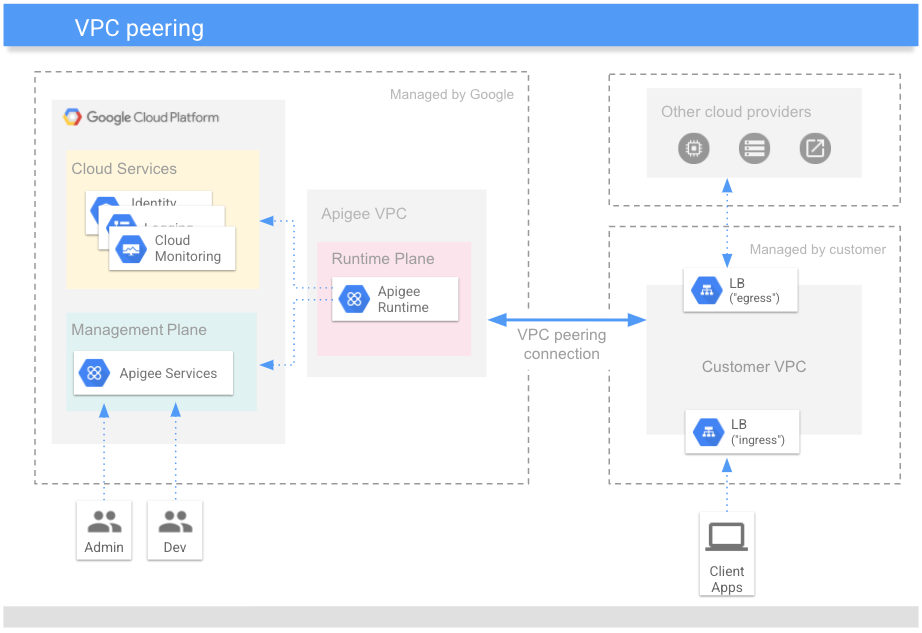
Peering VPC memungkinkan VPC Apigee memproses permintaan dan respons yang dikirim ke VPC Pelanggan:
-
Traffic ke utara: Permintaan proxy API yang dikirim dari klien ke VPC Pelanggan yang diteruskan ke bidang runtime Apigee untuk diproses. Layanan tambahan seperti logging, pengelolaan identitas, dan metrik juga dapat diakses oleh bidang runtime.
-
Traffic ke hilir: Permintaan proxy API yang harus mengakses API target atau layanan backend lainnya di VPC Pelanggan merupakan rute ke hilir. Layanan southbound ini memproses respons sebelum menampilkannya ke VPC Pelanggan untuk diproses lebih lanjut oleh runtime Apigee sebelum respons dikirim ke klien.
Langkah penyediaan Apigee, Konfigurasi Service Networking, melakukan peering VPC dan mengalokasikan Rentang Alamat IP (rentang CIDR) ke Apigee.
Penentuan ukuran jaringan
Setiap instance Apigee memerlukan rentang CIDR /22 yang tidak tumpang-tindih. Bidang runtime Apigee (alias bidang data) diberi alamat IP dari dalam rentang CIDR. Oleh karena itu, rentang tersebut harus dicadangkan untuk Apigee dan tidak digunakan oleh aplikasi lain di jaringan VPC pelanggan.
Instance dibuat saat:
- Organisasi Apigee disediakan terlebih dahulu, baik melalui wizard UI atau antarmuka command line (CLI).
- Saat memperluas Apigee ke region Cloud baru untuk organisasi yang sudah ada. Lihat juga Memperluas Apigee ke beberapa region.
Saat membuat instance, ada dua opsi untuk menentukan rentang IP jaringan:
- Alokasikan rentang secara otomatis - Saat Anda membuat instance Apigee, izinkan Apigee untuk mengalokasikan rentang yang tersedia dan tidak tumpang-tindih dari rentang yang lebih besar yang dialokasikan ke Google. Setiap kali instance dibuat ulang, rentang IP akan dialokasikan secara otomatis. Dalam kasus tersebut, instance baru mungkin menggunakan rentang IP baru, jika tersedia dan tidak tumpang-tindih dengan produk atau layanan lain.
- Tentukan rentang IP - Anda dapat menentukan rentang IP yang akan digunakan Apigee. Rentang IP ini harus berasal dari rentang yang tidak tumpang-tindih yang di-peering dengan Apigee. Opsi ini berguna jika Anda ingin mengalokasikan rentang IP yang lebih besar untuk beberapa produk Cloud, seperti Cloud SQL, Cloud Memorystore, Apigee, dan lainnya, dan Anda juga ingin dapat menentukan rentang IP aktual untuk setiap produk ini. Rentang ini dapat berupa rentang IP non-RFC 1918 selama rentang tersebut bukan alamat IP publik yang digunakan secara pribadi (PUPI). .
Setelah membuat instance, Anda tidak dapat mengubah rentang CIDR. Untuk mengubah rentang CIDR, Anda harus menghapus instance dan mengonfigurasi ulang instance baru. Berhati-hatilah jika Anda hanya memiliki satu instance dalam organisasi.
Pertimbangan
Sebelum mengalokasikan rentang CIDR, lihat Pertimbangan dalam dokumentasi Virtual Private Cloud.
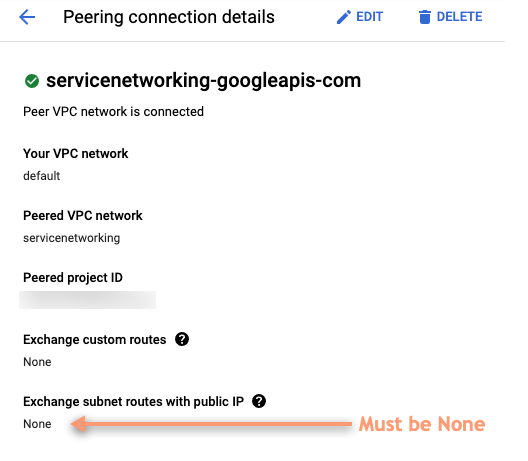
Saat membuat koneksi peering dengan Google, pastikan IP publik tidak dipertukarkan. Untuk memeriksa:
- Di Google Cloud konsol, buka halaman VPC Network Peering. Lihat juga Menggunakan Peering Jaringan VPC.
- Pilih koneksi peering jaringan VPC Anda.
- Di bagian Detail koneksi peering, pastikan Tukar rute subnet dengan IP publik disetel ke
Tidak Ada, seperti yang ditunjukkan pada screenshot berikut.