Understanding which ports the hybrid runtime plane uses is important for enterprise implementations. This section describes the ports used for secure communications within the runtime plane as well as external ports used for communications with external services.
Internal connections
Communication between the runtime plane and management plane is secured with TLS 1-way and OAuth 2.0. Individual services use different protocols, depending on which service they are communicating with.
The certificates used for intra-component communication are generated by Apigee's certificate manager. You do not have to provide a certificate or manage it.
The following image shows the ports and communications channels within the hybrid runtime plane:
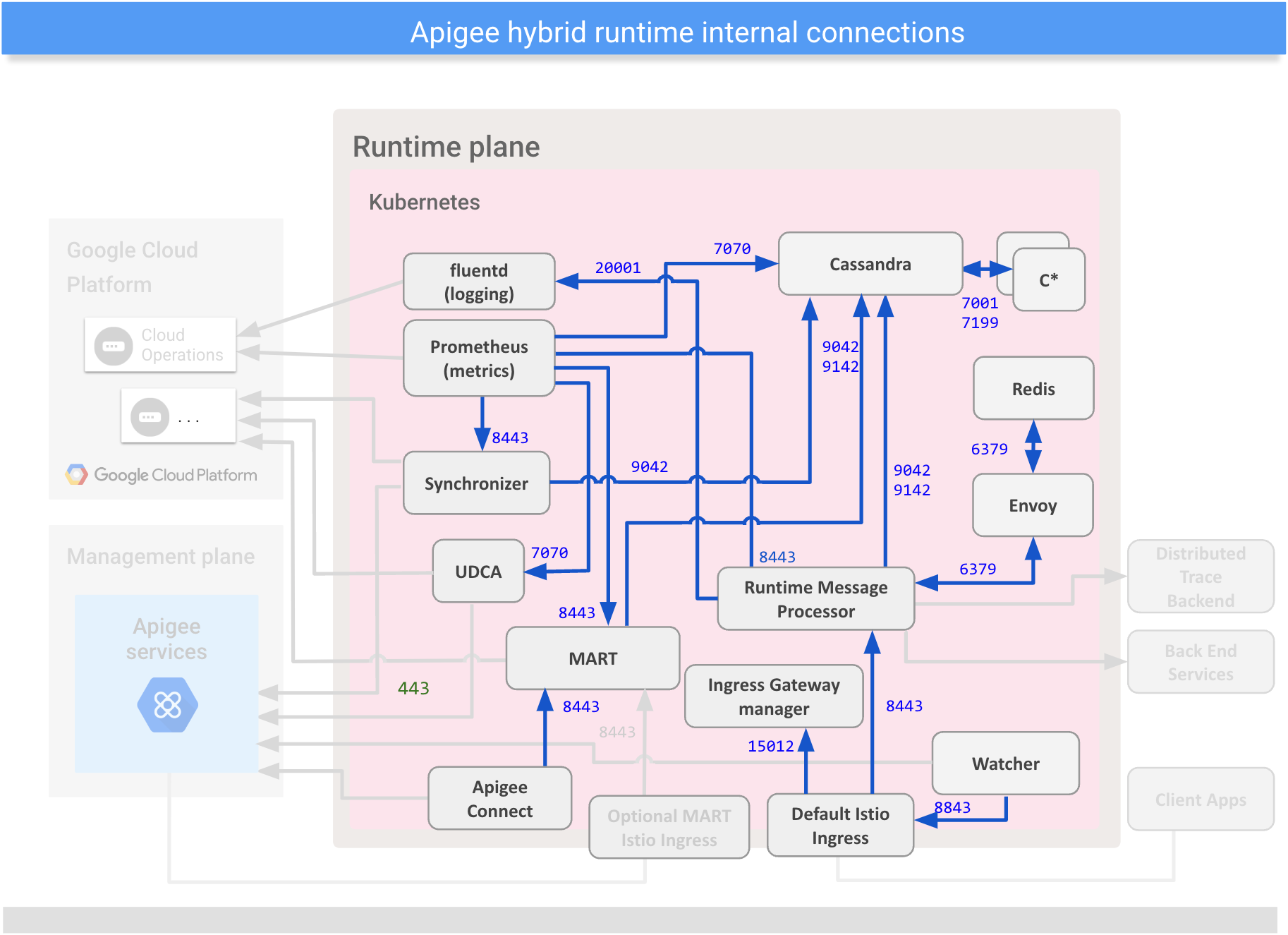
The following table describes the ports and communications channels within the hybrid runtime plane:
| Internal Connections | |||||
|---|---|---|---|---|---|
| Source | Destination | Protocol/Ports | Security protocol | Description | |
| MART | Cassandra | TCP/9042 TCP/9142 |
mTLS | Sends data for persistence. | |
| Apigee Connect | MART | TCP/8443 | TLS | Requests from the management plane go through Apigee Connect. Apigee Connect initiates the connection. | |
| Default Istio Ingress | Message Processor | TCP/8443 | TLS (Apigee-generated, self-signed cert) | Processes incoming API requests. | |
| Message Processor | Cassandra | TCP/9042 TCP/9142 |
mTLS | Sends data for persistence. | |
| Message Processor | fluentd (analytics / logging) | TCP/20001 | mTLS | Streams data to the data collection pod. | |
| Cassandra | Cassandra | TCP/7001 TCP/7199 |
mTLS | Intra-node cluster communications. | |
| Cassandra | Cassandra | TCP/7001 | mTLS | Inter-region communications. | |
| Synchronizer | Cassandra | TCP/9042 TCP/9142 |
mTLS | Sends data for persistence. | |
| Prometheus (metrics) | Cassandra | TCP/7070 (HTTPS) | TLS | Scrapes metrics data from various services. | |
| MART | TCP/8843 (HTTPS) | TLS | |||
| Message Processor | TCP/8843 (HTTPS) | TLS | |||
| Synchronizer | TCP/8843 (HTTPS) | TLS | |||
| UDCA | TCP/7070 (HTTPS) | TLS | |||
| Watcher | Ingress pods | TCP/8843 | TLS | Polls to get deployment status. | |
External connections
To appropriately configure your network firewall, you should know the inbound and outbound ports used by hybrid to communicate with external services.
The following image shows the ports used for external communications with the hybrid runtime plane:
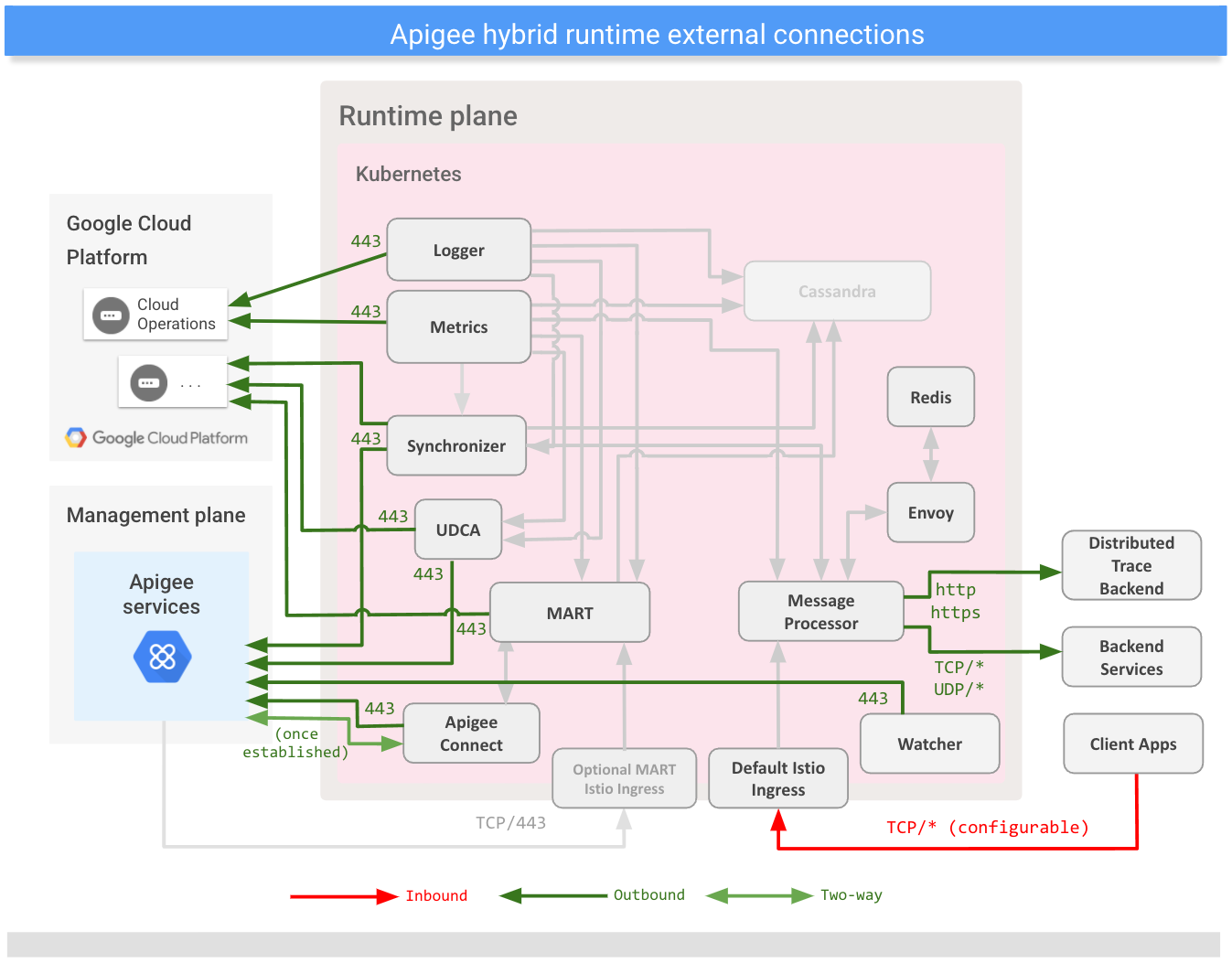
The following table describes the ports used for external communications with the hybrid runtime plane:
| External Connections | |||||
|---|---|---|---|---|---|
| Source | Destination | Protocol/Port(s) | Security Protocol | Description | |
| Inbound Connections (exposed externally) | |||||
| OPTIONAL: Apigee Services Only if not using Apigee Connect (recommended). See Two-way Connections below. |
MART Istio Ingress | TCP/443 | OAuth over TLS 1.2 | Hybrid API calls from the management plane. | |
| Client Apps | Default Istio Ingress | TCP/* | None/OAuth over TLS 1.2 | API requests from external apps. | |
| Outbound Connections | |||||
| Message Processor | Backend services | TCP/* UDP/* |
None/OAuth over TLS 1.2 | Sends requests to customer-defined hosts. | |
| Synchronizer | Apigee Services | TCP/443 | OAuth over TLS 1.2 | Fetches configuration data; connects to
apigee.googleapis.com. |
|
| Google Cloud | Connects to iamcredentials.googleapis.com for
authorization. |
||||
| UDCA (Analytics) | Apigee Services (UAP) | TCP/443 | OAuth over TLS 1.2 | Sends data to UAP in the management plane and to Google Cloud; connects to
apigee.googleapis.com and
storage.googleapis.com. |
|
| Apigee Connect | Apigee Services | TCP/443 | TLS | Establishes the connection with the management plane; connects to
apigeeconnect.googleapis.com. |
|
| Prometheus (metrics) | Google Cloud (Cloud Operations) | TCP/443 | TLS | Sends data to Cloud Operations in the management plane; connects to
monitoring.googleapis.com. |
|
| fluentd (logging) | Google Cloud (Cloud Operations) | TCP/443 | TLS | Sends data to Cloud Operations in the management plane; connects to
logging.googleapis.com |
|
| MART | Google Cloud | TCP/443 | OAuth over TLS 1.2 | Connects to iamcredentials.googleapis.com for authorization. |
|
| Message Processor | Distributed Trace back end | http or https | TLS (configurable) | (Optional) Communicates trace information to the Distributed Trace back end service. Configure the service and protocol in the TraceConfig API. The back end for Distributed Trace is usually Cloud Trace or Jaeger. | |
| Two-way Connections | |||||
| Apigee Connect | Apigee Services | TCP/443 | TLS | Communicates management data between the managemennt plane and the Management API for
runtime data (MART) in the runtime plane. Apigee Connect initiates the connection;
connects to apigeeconnect.googleapis.com. Therefore, you
do not need to configure your firewall for inbound connectivity. |
|
| * indicates that the port is configurable. Apigee recommends using port 443. | |||||
You should not allow external connections for specific IP addresses associated with
*.googleapis.com. The IP addresses can change since the domain currently resolves to
multiple addresses.
