Spanner 精细的访问权限控制兼具 Identity and Access Management (IAM) 和基于角色的 SQL 访问权限控制的优势。借助精细的访问权限控制,您可以定义数据库角色、向这些角色授予权限,并创建 IAM 政策以向 IAM 主账号授予对数据库角色的权限。本页面介绍了如何将精细访问权限控制与 Spanner 搭配使用,以用于 GoogleSQL 方言数据库和 PostgreSQL 方言数据库。
作为管理员,您必须为各个 IAM 主账号启用精细访问权限控制。已启用精细访问权限控制的主账号(“精细访问权限控制用户”)必须承担数据库角色才能访问 Spanner 资源。
对于非精细访问权限控制用户,资源访问权限由 IAM 数据库级角色控制。 精细访问权限控制完全兼容,可以与现有的 IAM 数据库级访问权限控制共存。您可以使用它来访问各个数据库对象。如需控制对整个数据库的访问权限,请使用 IAM 角色。
借助精细的访问权限控制,您可以控制对表、列、视图和变更数据流的访问权限。
如需管理精细访问权限控制,您可以使用以下 DDL 语句:
- 用于创建和删除数据库角色的
CREATE和DROP语句。 数据库角色是权限的集合。您最多可以为数据库创建 100 个角色。 GRANT和REVOKE语句,用于向数据库角色授予权限和从数据库角色撤消权限。权限包括SELECT、INSERT、UPDATE、DELETE和EXECUTE。权限名称与同名的 SQL 语句相对应。例如,具有INSERT权限的角色可以对GRANT语句中指定的表执行INSERTSQL 语句。以下 DDL 语句向
hr_rep数据库角色授予对表employees的SELECT权限。GoogleSQL
CREATE ROLE hr_rep; GRANT SELECT ON TABLE employees TO ROLE hr_rep;PostgreSQL
CREATE ROLE hr_rep; GRANT SELECT ON TABLE employees TO hr_rep;如需详细了解权限,请参阅精细访问权限控制权限参考文档。
GRANT语句,用于向其他角色授予角色,以创建具有权限继承功能的角色层次结构。
使用场景
以下是精细访问权限控制的示例用例:
- 一个具有销售薪酬分析师、销售管理人员和人力资源分析师角色的 HR 信息系统,每个角色对数据具有不同的访问权限级别。例如,薪酬分析师和销售管理人员不应看到社会保障号。
- 一个拼车应用,为乘客和司机提供不同的服务账号和权限。
- 允许
SELECT和INSERT操作但不允许UPDATE和DELETE操作的账本。
Spanner 资源及其权限
以下列出了 Spanner 资源以及您可以为其授予的精细访问权限控制权限。
- 架构
- 您可以向特定数据库角色授予对架构的
USAGE权限。对于非默认架构,数据库角色必须具有USAGE权限才能访问数据库对象。权限检查如下所示 :
您是否拥有架构的 USAGE 权限?
否:拒绝访问。
是:您是否还拥有该表的相应权限?
否:拒绝访问。
是:您可以访问该表。
- 表
- 您可以向数据库角色授予针对表的
SELECT、INSERT、UPDATE和DELETE权限。对于交织表,在父表上授予的权限不会传播到子表。 - 列
- 您可以针对表中的部分列授予
SELECT、INSERT和UPDATE权限。然后,相应权限仅对这些列有效。不允许在列级层使用DELETE。 - 视图
- 您可以授予对视图的
SELECT权限。对于视图,仅支持SELECT。Spanner 同时支持调用方权限视图和定义方权限视图。如果您创建具有调用方权限的视图,则数据库角色或用户需要对该视图拥有SELECT权限,并且对该视图中引用的底层对象也拥有SELECT权限,才能查询该视图。如果您创建具有定义方权限的视图,则数据库角色或用户只需对该视图拥有SELECT权限即可查询该视图。如需了解详情,请参阅视图概览。 - 变更流
- 您可以授予对变更数据流的
SELECT权限。您还必须对与变更数据流关联的读取函数授予EXECUTE权限。如需了解相关信息,请参阅变更数据流的精细访问权限控制。 - 序列
- 您可以针对序列授予
SELECT和UPDATE。如需了解详情,请参阅序列的精细访问权限控制。 - 模型
- 您可以为模型授予
EXECUTE。如需了解详情,请参阅模型的精细访问权限控制。
精细访问权限控制系统角色
精细访问权限控制为每个数据库预定义了系统角色。与用户定义的数据库角色一样,系统角色也可以控制对 Spanner 资源的访问权限。
例如,精细访问权限控制用户需要被授予 spanner_sys_reader 系统角色才能访问 Key Visualizer,并且需要 spanner_info_reader 系统角色才能在查询 INFORMATION_SCHEMA 表时看到未经过滤的结果。
如需了解详情,请参阅精细访问权限控制系统角色。
数据库角色层次结构和继承
您可以创建数据库角色层次结构,其中子角色会继承父角色的权限。子角色称为父角色的成员。
例如,请参考以下 GRANT 语句:
GoogleSQL
GRANT SELECT ON TABLE employees TO ROLE pii_access;
GRANT ROLE pii_access TO ROLE hr_manager, hr_director;
PostgreSQL
GRANT SELECT ON TABLE employees TO pii_access;
GRANT pii_access TO hr_manager, hr_director;
hr_manager 和 hr_director 是角色 pii_access 的成员,并继承了表 employees 的 SELECT 权限。
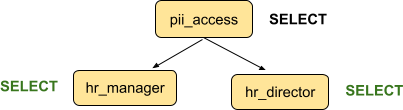
hr_manager 和 hr_director 也可以有成员,这些成员将继承 employees 的 SELECT 权限。
角色层次结构的深度不受限制,但如果角色层次结构过深过广,查询性能可能会下降。
备份和恢复
Spanner 备份包含数据库角色定义。从备份恢复数据库时,系统会重新创建数据库角色并授予相应权限。不过,IAM 政策不属于数据库备份的一部分,因此您必须重新向已恢复数据库中的数据库角色授予对主账号的访问权限。
设置精细访问权限控制的概览
以下是您为开始使用精细访问权限控制来保护数据而需要执行的高级步骤。如需了解详情,请参阅配置精细访问权限控制。
您必须获得 roles/spanner.admin 或 roles/spanner.databaseAdmin IAM 角色才能执行这些任务。
- 创建数据库角色并向这些角色授予权限。
- 可选:通过向其他角色授予角色来创建具有继承功能的角色层次结构。
- 针对每个要成为精细访问权限控制用户的主账号执行以下步骤:
- 为主账号启用精细访问权限控制。
然后,系统会自动向该主账号授予
public数据库角色,该角色默认情况下没有任何权限。对于每个主账号,此操作只需执行一次。 - 向主账号授予一个或多个数据库角色的 IAM 权限。
- 向主账号授予所有必需的数据库角色后,如果该主账号具有数据库级 IAM 角色,请考虑撤消这些数据库级角色,以便仅通过一种方法管理该主账号的访问权限控制。
- 为主账号启用精细访问权限控制。
然后,系统会自动向该主账号授予
限制
- 导出操作不会导出数据库角色和权限,导入操作也无法导入这些内容。导入完成后,您必须手动设置角色和权限。
- Google Cloud 控制台的表格页面上的数据标签页不适用于精细的访问权限控制用户。
后续步骤
- 使用精细访问权限控制访问数据库
- 变更数据流的精细访问权限控制
- 配置精细访问权限控制
- 精细访问权限控制权限参考文档
- 精细访问权限控制系统角色
- GoogleSQL
GRANT和REVOKE语句 - PostgreSQL
GRANT和REVOKE语句 - 序列的精细访问权限控制
- 模型的精细访问权限控制
