En esta página se describe cómo usar claves de encriptado gestionadas por el cliente (CMEK) creadas manualmente en Spanner.
Para obtener más información sobre las CMEKs, consulta el resumen de las claves de encriptado gestionadas por el cliente (CMEKs).
Crear una base de datos con CMEK habilitada
Crea una clave en Cloud Key Management Service (Cloud KMS). Puedes usar los siguientes tipos de claves, que tienen diferentes niveles de protección en Spanner:
La clave debe estar en la misma ubicación que tu instancia de Spanner. Por ejemplo, si la configuración de tu instancia de Spanner está en
us-west1, la ubicación del llavero de claves de Cloud KMS también debe serus-west1.No todas las configuraciones de instancias multirregionales de Spanner tienen una ubicación de conjunto de claves de Cloud KMS correspondiente. En el caso de las bases de datos de Spanner con configuraciones de instancias personalizadas, birregionales o multirregionales, puedes usar varias claves regionales (de una sola región) de Cloud KMS para proteger tu base de datos. Por ejemplo:
- Si tu base de datos de Spanner está en la configuración de instancia multirregión
nam14, puedes crear claves de Cloud KMS enus-east4,northamerica-northeast1yus-east1. - Si tu base de datos tiene una configuración de instancia personalizada que usa
nam3como configuración de instancia base con una réplica de solo lectura adicional enus-central2, puedes crear claves de Cloud KMS enus-east4,us-east1,us-central1yus-central2.
Opcional: Para ver una lista de las ubicaciones de las réplicas en la configuración de tu instancia de Spanner, usa el comando
gcloud spanner instances get-locations:gcloud spanner instances get-locations <var>INSTANCE_ID</var>Para obtener más información, consulta los siguientes recursos:
- Si tu base de datos de Spanner está en la configuración de instancia multirregión
Concede acceso a Spanner a la clave.
En Cloud Shell, crea y muestra el agente de servicio, o muéstralo si la cuenta ya existe:
gcloud beta services identity create --service=spanner.googleapis.com \ --project=PROJECT_IDSi se te pide que instales el componente gcloud Beta Commands, escribe
Y. Una vez finalizada la instalación, el comando se reiniciará automáticamente.El comando
gcloud services identitycrea u obtiene el agente de servicio que Spanner puede usar para acceder a la clave de Cloud KMS en tu nombre.El ID de la cuenta de servicio tiene el formato de una dirección de correo electrónico:
Service identity created: service-xxx@gcp-sa-spanner.iam.gserviceaccount.comAsigna el rol Encargado del encriptado y desencriptado de claves de CryptoKey de Cloud KMS(
cloudkms.cryptoKeyEncrypterDecrypter) a la cuenta de servicio de cada región (--location) de la configuración de tu instancia de Spanner. Para ello, ejecuta el comandogcloud kms keys add-iam-policybinding:gcloud kms keys add-iam-policy-binding KMS_KEY \ --location KMS_KEY_LOCATION \ --keyring KMS_KEY_RING \ --project=PROJECT_ID \ --member serviceAccount:service-xxx@gcp-sa-spanner.iam.gserviceaccount.com \ --role roles/cloudkms.cryptoKeyEncrypterDecrypterEste es un ejemplo de resultado:
Updated IAM policy for key [KMS_KEY]Si usas varias claves de Cloud KMS para proteger tu base de datos, ejecuta el comando
gcloud kms keys add-iam-policybindingpara todas tus claves.Este rol asegura que la cuenta de servicio tenga permiso para encriptar y desencriptar con la clave de Cloud KMS. Para obtener más información, consulta Permisos y roles de Cloud KMS.
Crea la base de datos y especifica tu clave de Cloud KMS.
Consola
Usa la consola para crear bases de datos en configuraciones de instancias regionales.
En la consola, ve a la página Instancias. Google Cloud
Haz clic en la instancia en la que quieras crear una base de datos.
Haz clic en Crear base de datos y rellena los campos obligatorios.
Haz clic en Mostrar opciones de cifrado.
Selecciona Clave de Cloud KMS.
Seleccione una clave de la lista desplegable.
La lista de claves se limita al proyecto actual. Google Cloud Para usar una clave de otro proyecto, crea la base de datos con la CLI de gcloud en lugar de con la consola deGoogle Cloud . Google Cloud
Una vez creada la base de datos, puede verificar que tiene habilitado CMEK en la página Resumen de la base de datos.
gcloud
Para crear una base de datos con CMEK en una configuración de instancia regional, personalizada o multirregional, ejecuta el comando gcloud spanner databases create:
gcloud spanner databases create DATABASE \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_ID \
--ddl="CREATE TABLE Users (Id INT64 NOT NULL, FirstName STRING(100) NOT NULL, LastName STRING(100) NOT NULL,) PRIMARY KEY (Id)" \
--kms-project=KMS_PROJECT_ID \
--kms-location=KMS_KEY_LOCATION \
--kms-keyring=KMS_KEYRING \
--kms-keys=KMS_KEY_1[, KMS_KEY_2 ... ]Para comprobar si una base de datos tiene habilitada la CMEK, ejecuta el comando gcloud spanner databases describe:
gcloud spanner databases describe DATABASE \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDLas bases de datos habilitadas para CMEK incluyen un campo para encryptionConfig, como se muestra en el siguiente ejemplo de salida:
encryptionConfig:
kmsKeyNames:projects/my-kms-project/locations/eur5/keyRings/my-kms-key-ring/cryptoKeys/my-kms-key
name: projects/my-spanner-project/instances/my-instance/databases/my-db
state: READY
Bibliotecas de cliente
C#
Para crear una base de datos con CMEK en una configuración de instancia regional, sigue estos pasos:
Para crear una base de datos con CMEK en una configuración de instancia multirregional, sigue estos pasos:
C++
Para crear una base de datos con CMEK en una configuración de instancia regional, sigue estos pasos:
Para crear una base de datos con CMEK en una configuración de instancia multirregional, sigue estos pasos:
Go
Para crear una base de datos con CMEK en una configuración de instancia regional, sigue estos pasos:
Para crear una base de datos con CMEK en una configuración de instancia multirregional, sigue estos pasos:
Java
Para crear una base de datos con CMEK en una configuración de instancia regional, sigue estos pasos:
Para crear una base de datos con CMEK en una configuración de instancia multirregional, sigue estos pasos:
Node.js
Para crear una base de datos con CMEK en una configuración de instancia regional, sigue estos pasos:
Para crear una base de datos con CMEK en una configuración de instancia multirregional, sigue estos pasos:
PHP
Para crear una base de datos con CMEK en una configuración de instancia regional, sigue estos pasos:
Para crear una base de datos con CMEK en una configuración de instancia multirregional, sigue estos pasos:
Python
Para crear una base de datos con CMEK en una configuración de instancia regional, sigue estos pasos:
Para crear una base de datos con CMEK en una configuración de instancia multirregional, sigue estos pasos:
Ruby
Para crear una base de datos con CMEK en una configuración de instancia regional, sigue estos pasos:
Para crear una base de datos con CMEK en una configuración de instancia multirregional, sigue estos pasos:
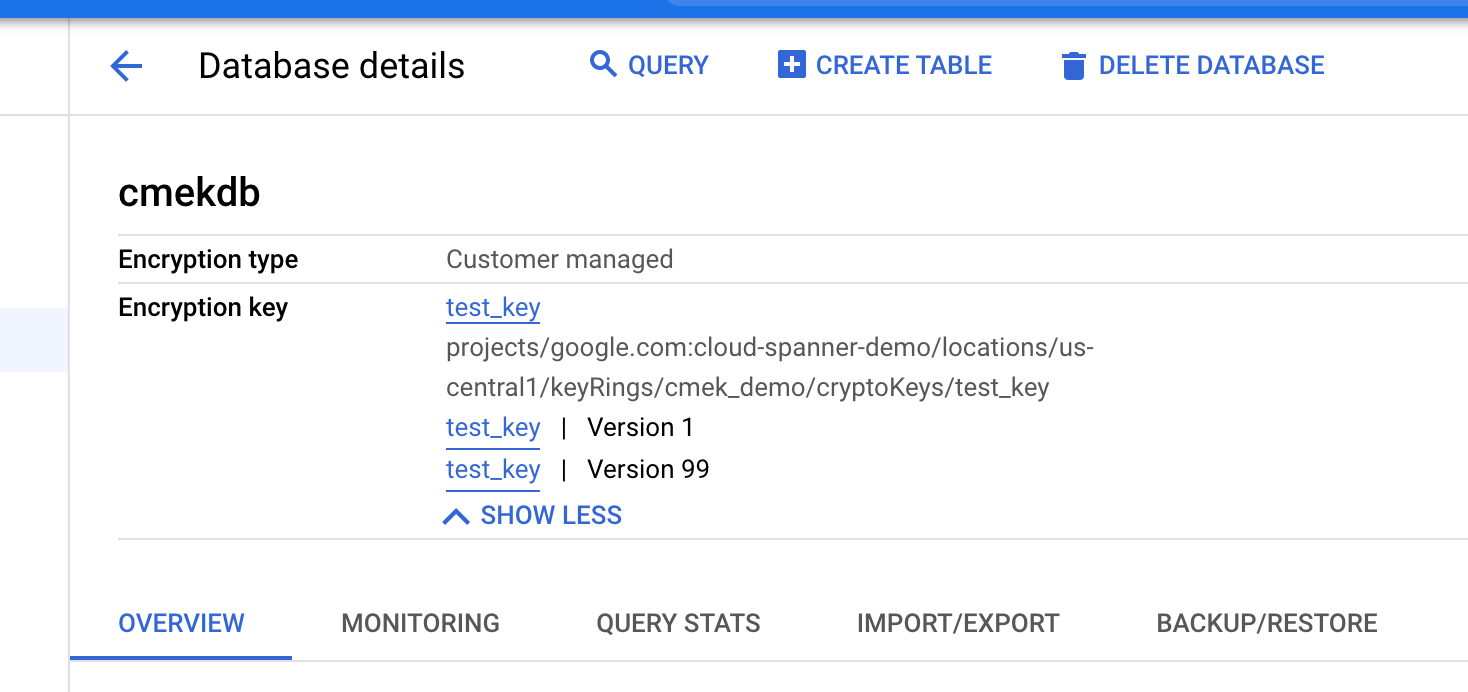
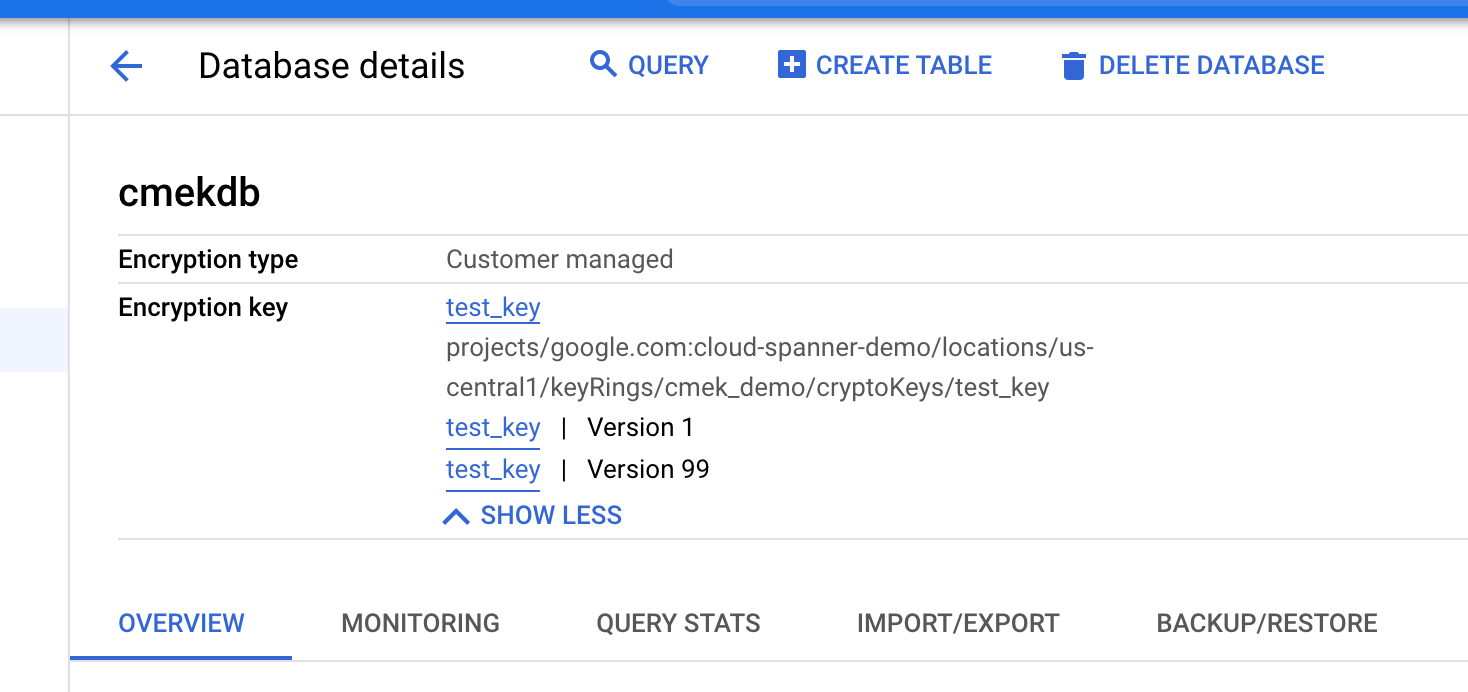
Ver las versiones de clave en uso
El campo encryption_info
de la base de datos muestra información sobre las versiones clave.
Cuando cambia la versión de la clave de una base de datos, el cambio no se propaga inmediatamente a encryption_info. Puede que el cambio tarde en reflejarse en este campo.
Consola
En la consola, ve a la página Instancias. Google Cloud
Haz clic en la instancia que contiene la base de datos que quieres ver.
Haz clic en la base de datos.
La información de cifrado se muestra en la página Detalles de la base de datos.
gcloud
Puedes obtener el encryption_info de una base de datos ejecutando el comando
gcloud spanner databases describe
o gcloud spanner databases list. Por ejemplo:
gcloud spanner databases describe DATABASE \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDEste es un ejemplo de resultado:
name: projects/my-project/instances/test-instance/databases/example-db
encryptionInfo:
- encryptionType: CUSTOMER_MANAGED_ENCRYPTION
kmsKeyVersion: projects/my-kms-project/locations/my-kms-key1-location/keyRings/my-kms-key-ring1/cryptoKeys/my-kms-key1/cryptoKeyVersions/1
- encryptionType: CUSTOMER_MANAGED_ENCRYPTION
kmsKeyVersion: projects/my-kms-project/locations/my-kms-key2-location/keyRings/my-kms-key-ring2/cryptoKeys/my-kms-key2/cryptoKeyVersions/1
Inhabilita la clave
Inhabilita las versiones de clave que estén en uso siguiendo estas instrucciones para cada versión de clave.
Espera a que se aplique el cambio. La inhabilitación de una clave puede tardar hasta tres horas en propagarse.
Para confirmar que ya no se puede acceder a la base de datos, ejecuta una consulta en la base de datos con CMEK inhabilitada:
gcloud spanner databases execute-sql DATABASE \ --project=SPANNER_PROJECT_ID \ --instance=INSTANCE_ID \ --sql='SELECT * FROM Users'Aparece el siguiente mensaje de error:
KMS key required by the Spanner resource is not accessible.
Habilita la clave
Habilita las versiones de clave que usa la base de datos siguiendo estas instrucciones para cada versión de clave.
Espera a que se aplique el cambio. La habilitación de una clave puede tardar hasta tres horas en propagarse.
Para confirmar que ya no se puede acceder a la base de datos, ejecuta una consulta en la base de datos habilitada para CMEK:
gcloud spanner databases execute-sql DATABASE \ --project=SPANNER_PROJECT_ID \ --instance=INSTANCE_ID \ --sql='SELECT * FROM Users'Si el cambio se ha aplicado, el comando se ejecutará correctamente.
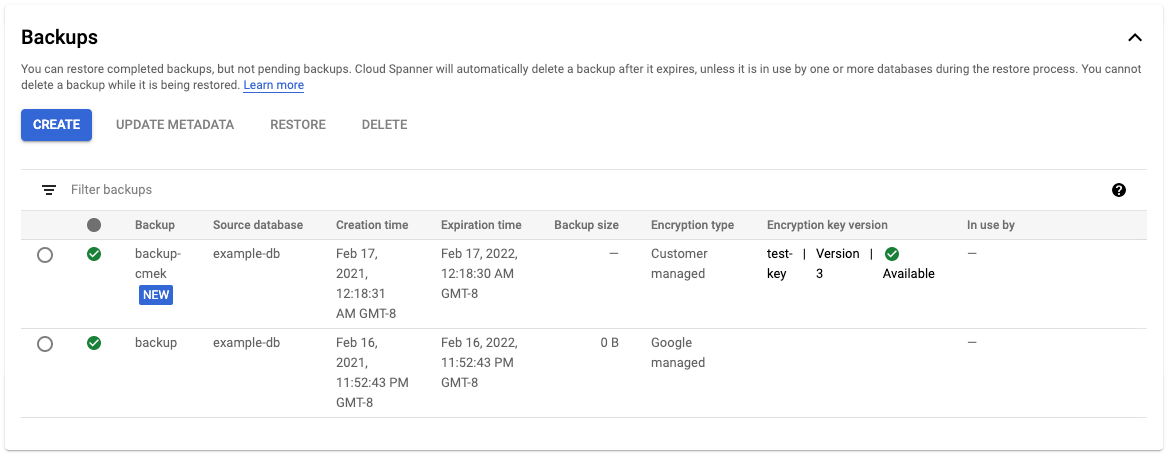
Crear una copia de seguridad de una base de datos
Puede usar las copias de seguridad de Spanner para crear copias de seguridad de sus bases de datos. De forma predeterminada, las copias de seguridad de Spanner creadas a partir de una base de datos usan la misma configuración de cifrado que la propia base de datos. También puedes especificar una configuración de cifrado diferente para una copia de seguridad.
Consola
Usa la consola para crear copias de seguridad en configuraciones de instancias regionales.
En la consola, ve a la página Instancias. Google Cloud
Haga clic en el nombre de la instancia que contiene la base de datos de la que quiere crear una copia de seguridad.
Haz clic en la base de datos.
En el panel de navegación, haz clic en Copia de seguridad o restauración.
En la pestaña Copias de seguridad, haz clic en Crear copia de seguridad.
Escribe un nombre para la copia de seguridad y selecciona una fecha de vencimiento.
Opcional: Haz clic en Mostrar opciones de cifrado.
a. Si quieres usar otra configuración de cifrado para tu copia de seguridad, haz clic en el control deslizante situado junto a Usar cifrado actual.
a. Selecciona Clave de Cloud KMS.
a. Seleccione una clave de la lista desplegable.
La lista de claves se limita al proyecto actual. Google Cloud Para usar una clave de otro proyecto, crea la base de datos con la CLI de gcloud en lugar de con la consola. Google Cloud Google Cloud
Haz clic en Crear.
En la tabla Copias de seguridad se muestra información sobre el cifrado de cada copia de seguridad.
gcloud
Para crear una copia de seguridad con CMEK en una configuración de instancia regional, personalizada o multirregional, ejecuta el comando gcloud spanner backups create:
gcloud spanner backups create BACKUP \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_ID \
--database=DATABASE \
--retention-period=RETENTION_PERIOD \
--encryption-type=customer_managed_encryption \
--kms-project=KMS_PROJECT_ID \
--kms-location=KMS_KEY_LOCATION \
--kms-keyring=KMS_KEY_RING \
--kms-keys=KMS_KEY_1[, KMS_KEY_2 ... ]
--asyncPara verificar que la copia de seguridad creada está cifrada con CMEK, sigue estos pasos:
gcloud spanner backups describe BACKUP \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDBibliotecas de cliente
C#
Para crear una copia de seguridad con CMEK en una configuración de instancia regional, sigue estos pasos:
Para crear una copia de seguridad con CMEK en una configuración de instancia multirregional, sigue estos pasos:
C++
Para crear una copia de seguridad con CMEK en una configuración de instancia regional, sigue estos pasos:
Para crear una copia de seguridad con CMEK en una configuración de instancia multirregional, sigue estos pasos:
Go
Para crear una copia de seguridad con CMEK en una configuración de instancia regional, sigue estos pasos:
Para crear una copia de seguridad con CMEK en una configuración de instancia multirregional, sigue estos pasos:
Java
Para crear una copia de seguridad con CMEK en una configuración de instancia regional, sigue estos pasos:
Para crear una copia de seguridad con CMEK en una configuración de instancia multirregional, sigue estos pasos:
Node.js
Para crear una copia de seguridad con CMEK en una configuración de instancia regional, sigue estos pasos:
Para crear una copia de seguridad con CMEK en una configuración de instancia multirregional, sigue estos pasos:
PHP
Para crear una copia de seguridad con CMEK en una configuración de instancia regional, sigue estos pasos:
Para crear una copia de seguridad con CMEK en una configuración de instancia multirregional, sigue estos pasos:
Python
Para crear una copia de seguridad con CMEK en una configuración de instancia regional, sigue estos pasos:
Para crear una copia de seguridad con CMEK en una configuración de instancia multirregional, sigue estos pasos:
Ruby
Para crear una copia de seguridad con CMEK en una configuración de instancia regional, sigue estos pasos:
Para crear una copia de seguridad con CMEK en una configuración de instancia multirregional, sigue estos pasos:
Copiar una copia de seguridad
Puedes copiar una copia de seguridad de tu base de datos de Spanner de una instancia a otra en otra región u otro proyecto. De forma predeterminada, una copia de seguridad utiliza la misma configuración de cifrado (gestionada por Google o por el cliente) que la copia de seguridad de origen. Puedes anular este comportamiento especificando una configuración de cifrado diferente al copiar la copia de seguridad. Si quieres que la copia de seguridad se cifre con CMEK al copiarla entre regiones, especifica las claves de Cloud KMS correspondientes a las regiones de destino.
Consola
Usa la consola para copiar una copia de seguridad en una configuración de instancia regional.
En la consola, ve a la página Instancias. Google Cloud
Haga clic en el nombre de la instancia que contiene la base de datos de la que quiere crear una copia de seguridad.
Haz clic en la base de datos.
En el panel de navegación, haz clic en Copia de seguridad o restauración.
En la tabla Copias de seguridad, selecciona Acciones en la copia de seguridad y haz clic en Copiar.
Rellena el formulario. Para ello, elige una instancia de destino, proporciona un nombre y selecciona una fecha de vencimiento para la copia de seguridad.
Opcional: Si quieres usar una configuración de cifrado diferente para tu copia de seguridad, haz clic en Mostrar opciones de cifrado.
a. Selecciona Clave de Cloud KMS.
a. Seleccione una clave de la lista desplegable.
La lista de claves se limita al proyecto actual. Google Cloud Para usar una clave de otro proyecto, crea la base de datos con la CLI de gcloud en lugar de con la consola. Google Cloud Google Cloud
Haz clic en Copiar.
gcloud
Para copiar una copia de seguridad con una nueva configuración de cifrado en otra instancia del mismo proyecto, ejecuta el siguiente comando gcloud spanner backups copy:
gcloud spanner backups copy --async \
--source-instance=INSTANCE_ID \
--source-backup=SOURCE_BACKUP_NAME \
--destination-instance=DESTINATION_INSTANCE_ID \
--destination-backup=DESTINATION_BACKUP_NAME \
--expiration-date=EXPIRATION_DATE \
--encryption-type=CUSTOMER_MANAGED_ENCRYPTION \
--kms-keys=KMS_KEY_1[, KMS_KEY_2 ... ]Para copiar una copia de seguridad con una nueva configuración de cifrado en otra instancia
de otro proyecto, ejecuta el siguiente comando gcloud spanner backups copy:
gcloud spanner backups copy --async \
--source-backup=SOURCE_BACKUP_NAME \
--destination-backup=DESTINATION_BACKUP_NAME \
--encryption-type=CUSTOMER_MANAGED_ENCRYPTION \
--kms-keys=KMS_KEY_1[, KMS_KEY_2 ... ]Para verificar que la copia de seguridad copiada está cifrada con CMEK, sigue estos pasos:
gcloud spanner backups describe BACKUP \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDBibliotecas de cliente
C#
Para copiar una copia de seguridad con CMEK habilitada en una configuración de instancia multirregional, sigue estos pasos:
C++
Para copiar una copia de seguridad con CMEK habilitada en una configuración de instancia multirregional, sigue estos pasos:
Go
Para copiar una copia de seguridad con CMEK habilitada en una configuración de instancia multirregional, sigue estos pasos:
Java
Para copiar una copia de seguridad con CMEK habilitada en una configuración de instancia multirregional, sigue estos pasos:
Node.js
Para copiar una copia de seguridad con CMEK habilitada en una configuración de instancia multirregional, sigue estos pasos:
PHP
Para copiar una copia de seguridad con CMEK habilitada en una configuración de instancia multirregional, sigue estos pasos:
Python
Para copiar una copia de seguridad con CMEK habilitada en una configuración de instancia multirregional, sigue estos pasos:
Ruby
Para copiar una copia de seguridad con CMEK habilitada en una configuración de instancia multirregional, sigue estos pasos:
Restaurar a partir de copia de seguridad
Puedes restaurar una copia de seguridad de una base de datos de Spanner en una base de datos nueva. De forma predeterminada, las bases de datos que se restauran a partir de una copia de seguridad usan la misma configuración de cifrado que la propia copia de seguridad, pero puedes anular este comportamiento especificando una configuración de cifrado diferente para la base de datos restaurada. Si la copia de seguridad está protegida por CMEK, la versión de la clave que se usó para crearla debe estar disponible para que se pueda descifrar.
Consola
Usa la consola para restaurar una copia de seguridad en una configuración de instancia regional.
En la consola, ve a la página Instancias. Google Cloud
Haz clic en la instancia que contiene la base de datos que quieres restaurar.
Haz clic en la base de datos.
En el panel de navegación, haz clic en Copia de seguridad o restauración.
En la tabla Copias de seguridad, selecciona Acciones en la copia de seguridad que quieras restaurar y haz clic en Restaurar.
Selecciona la instancia que quieras restaurar y asigna un nombre a la base de datos restaurada.
Opcional: Si quieres usar otra configuración de cifrado con tu base de datos restaurada, haz clic en el control deslizante situado junto a Usar cifrado actual.
a. Selecciona Clave de Cloud KMS.
a. Seleccione una clave de la lista desplegable.
La lista de claves se limita al proyecto actual. Google Cloud Para usar una clave de otro proyecto, crea la base de datos con la CLI de gcloud en lugar de con la consola. Google Cloud Google Cloud
Haz clic en Restaurar.
gcloud
Para restaurar una copia de seguridad con una nueva configuración de cifrado, ejecuta el siguiente comando:
gcloud spanner databases restore
gcloud spanner databases restore --async \
--project=SPANNER_PROJECT_ID \
--destination-instance=DESTINATION_INSTANCE_ID \
--destination-database=DESTINATION_DATABASE_ID \
--source-instance=SOURCE_INSTANCE_ID \
--source-backup=SOURCE_BACKUP_NAMEPara verificar que la base de datos restaurada está cifrada con CMEK, sigue estos pasos:
gcloud spanner databases describe DATABASE \
--project=SPANNER_PROJECT_ID \
--instance=INSTANCE_IDPara obtener más información, consulta Restaurar desde una copia de seguridad.
Bibliotecas de cliente
C#
Para restaurar una copia de seguridad habilitada para CMEK en una configuración de instancia regional, sigue estos pasos:
Para restaurar una copia de seguridad habilitada para CMEK en una configuración de instancia multirregional, sigue estos pasos:
C++
Para restaurar una copia de seguridad habilitada para CMEK en una configuración de instancia regional, sigue estos pasos:
Para restaurar una copia de seguridad habilitada para CMEK en una configuración de instancia multirregional, sigue estos pasos:
Go
Para restaurar una copia de seguridad habilitada para CMEK en una configuración de instancia regional, sigue estos pasos:
Para restaurar una copia de seguridad habilitada para CMEK en una configuración de instancia multirregional, sigue estos pasos:
Java
Para restaurar una copia de seguridad habilitada para CMEK en una configuración de instancia regional, sigue estos pasos:
Para restaurar una copia de seguridad habilitada para CMEK en una configuración de instancia multirregional, sigue estos pasos:
Node.js
Para restaurar una copia de seguridad habilitada para CMEK en una configuración de instancia regional, sigue estos pasos:
Para restaurar una copia de seguridad habilitada para CMEK en una configuración de instancia multirregional, sigue estos pasos:
PHP
Para restaurar una copia de seguridad habilitada para CMEK en una configuración de instancia regional, sigue estos pasos:
Para restaurar una copia de seguridad habilitada para CMEK en una configuración de instancia multirregional, sigue estos pasos:
Python
Para restaurar una copia de seguridad habilitada para CMEK en una configuración de instancia regional, sigue estos pasos:
Para restaurar una copia de seguridad habilitada para CMEK en una configuración de instancia multirregional, sigue estos pasos:
Ruby
Para restaurar una copia de seguridad habilitada para CMEK en una configuración de instancia regional, sigue estos pasos:
Para restaurar una copia de seguridad habilitada para CMEK en una configuración de instancia multirregional, sigue estos pasos:
Ver los registros de auditoría de la clave de Cloud KMS
Asegúrate de que el registro esté habilitado para la API Cloud KMS en tu proyecto.
En la Google Cloud consola, ve a Explorador de registros.
Limita las entradas de registro a tu clave de Cloud KMS añadiendo las siguientes líneas al creador de consultas:
resource.type="cloudkms_cryptokey" resource.labels.location="KMS_KEY_LOCATION" resource.labels.key_ring_id="KMS_KEY_RING_ID" resource.labels.crypto_key_id="KMS_KEY_ID"En condiciones normales, las acciones de cifrado y descifrado se registran con la gravedad
INFO. Estas entradas se registran cuando las zonas de tu instancia de Spanner consultan la clave de Cloud KMS cada cinco minutos aproximadamente.Si Spanner no puede acceder a la clave, las operaciones se registran como
ERROR.

