Auf dieser Seite wird beschrieben, wie Sie dem Cloud Data Fusion-Dienstagenten die Rolle Dienstkontonutzer für das Dataproc-Dienstkonto zuweisen, damit er Pipelines in Dataproc-Clustern bereitstellen und ausführen kann.
Dienstkonten, die von Dataproc verwendet werden, müssen außerdem die Berechtigung datafusion.instances.runtime zum Zugriff auf die Cloud Data Fusion-Laufzeitressourcen erteilen.
Unabhängig davon, ob Sie ein nutzerverwaltetes Dienstkonto oder das Compute Engine-Standarddienstkonto auf den virtuellen Maschinen in einem Cluster verwenden, müssen Sie Cloud Data Fusion die Rolle "Dienstkontonutzer" zuweisen. Andernfalls kann Cloud Data Fusion keinen Dataproc-Cluster bereitstellen und der folgende Fehler wird angezeigt, wenn Sie eine Datenpipeline ausführen:
PROVISION task failed in REQUESTING_CREATE state for program run [pipeline-name] due to Dataproc operation failure: INVALID_ARGUMENT: User not authorized to act as service account '[service-account-name]'
Name des Dienstkontos abrufen
- Rufen Sie in der Google Cloud Console die Seite „Identitäts- und Zugriffsverwaltung“ auf.
Zur IAM-Seite - Wählen Sie in der Projektauswahl oben auf der Seite das Projekt, den Ordner oder die Organisation aus, zu der die Cloud Data Fusion-Instanz gehört.
- Suchen und kopieren Sie den Namen des Cloud Data Fusion-Dienstkontos. Verwenden Sie das folgende Format:
service-[project-number]@gcp-sa-datafusion.iam.gserviceaccount.com.
Dienstkontonutzer die Berechtigung erteilen
- Rufen Sie in der Google Cloud Console die Seite Dienstkonten auf.
Zur Seite „Dienstkonten“ - Klicken Sie auf Projekt auswählen, wählen Sie ein Projekt aus, in dem sich das Dienstkonto befindet, das Sie für den Dataproc-Cluster verwenden möchten, und klicken Sie dann auf Öffnen.
Klicken Sie auf die E-Mail-Adresse des Dataproc-Dienstkontos.
Klicken Sie auf den Tab Berechtigungen. Auf der Seite wird eine Liste der Hauptkonten angezeigt, denen Rollen für das Dienstkonto zugewiesen wurden.
Klicken Sie auf Zugriff erlauben.
Fügen Sie im Feld Neue Hauptkonten den Namen des zuvor kopierten Cloud Data Fusion-Dienstkontos ein.
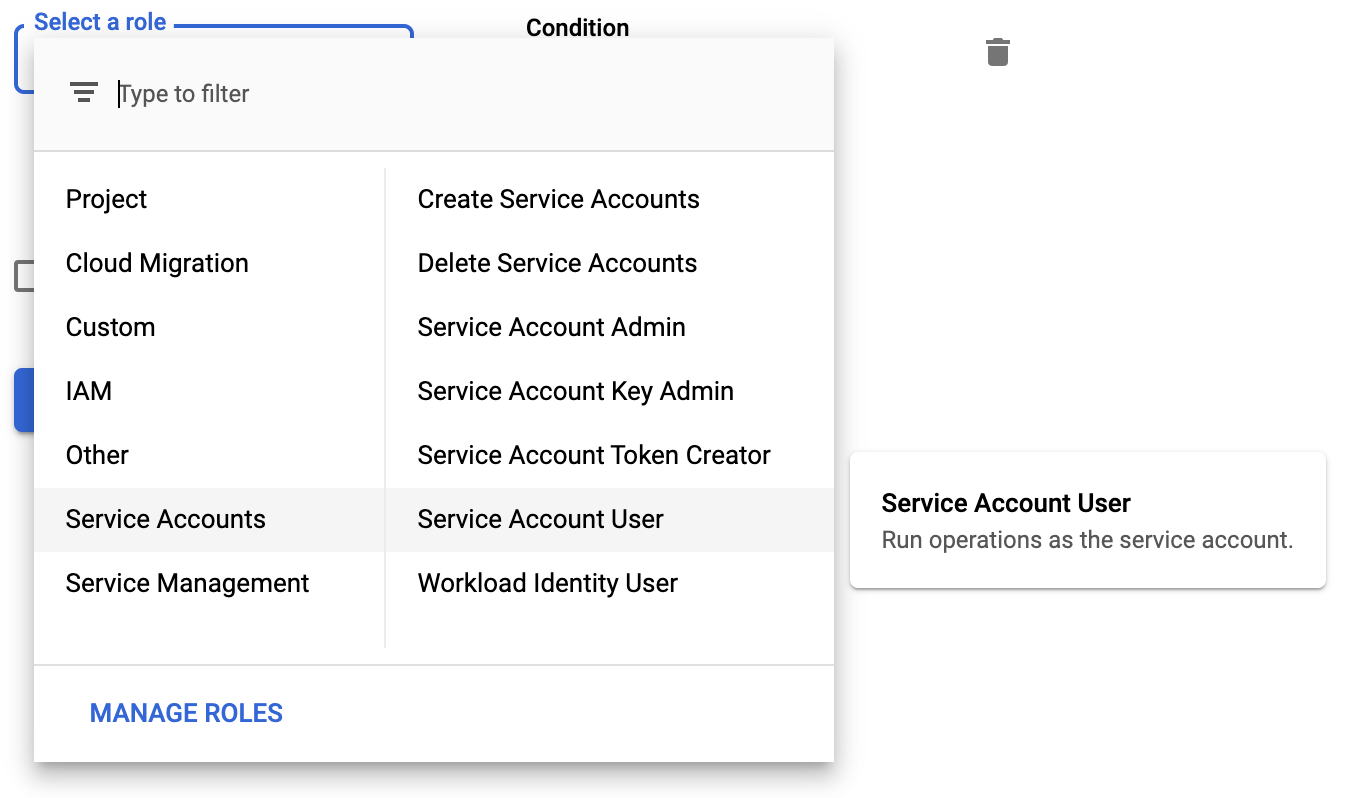
Wählen Sie die Rolle Dienstkontonutzer aus.
Klicken Sie auf Speichern.
Dataproc-Dienstkonten Rollen zuweisen
Rolle „Läufer“ berechtigen
Weisen Sie die Rolle Cloud Data Fusion-Runner (roles/datafusion.runner) zu Dienstkonten zu, die von Dataproc verwendet werden. Dadurch wird das Dataproc-Dienstkonto zum Ausführen von Cloud Data Fusion-Pipelines in Ihrem Projekt autorisiert.
Weitere Informationen finden Sie unter Berechtigung zum Anhängen von Dienstkonten an Ressourcen erfordern.
Cloud Storage-Administratorberechtigung gewähren
Weisen Sie in Cloud Data Fusion Version 6.2.0 und höher die Rolle Cloud Storage-Administrator (roles/storage.admin) Dienstkonten zu, die von Dataproc in Ihrem Projekt verwendet werden.
Nächste Schritte
- Weitere Informationen zur Zugriffssteuerung in Cloud Data Fusion
- Weitere Informationen zu Cloud Data Fusion-Dienstkonten

