Nesta página, descrevemos como conceder o papel de usuário da conta de serviço na conta de serviço do Dataproc ao agente de serviço do Cloud Data Fusion para permitir que ele provisione e execute pipelines em clusters do Dataproc.
Para contas de serviço usadas pelo Dataproc, também é necessário
conceder a permissão datafusion.instances.runtime para acessar
os recursos de execução do Cloud Data Fusion.
Se você usa uma conta de serviço padrão do Compute Engine ou uma gerenciada pelo usuário nas máquinas virtuais de um cluster, é necessário conceder o papel de usuário da conta de serviço ao Cloud Data Fusion. Caso contrário, o produto não poderá provisionar um cluster do Dataproc, e o seguinte erro será exibido quando você executar um pipeline de dados:
PROVISION task failed in REQUESTING_CREATE state for program run [pipeline-name] due to Dataproc operation failure: INVALID_ARGUMENT: User not authorized to act as service account '[service-account-name]'
Conseguir o nome da conta de serviço
- No Google Cloud console, acesse a página "Gerenciamento de identidade e acesso".
Acessar a página "IAM" - No seletor de projetos na parte de cima da página, escolha o projeto, a pasta ou a organização à qual a instância do Cloud Data Fusion pertence.
- Encontre e copie o nome da conta de serviço do Cloud Data Fusion. Use o seguinte formato:
service-[project-number]@gcp-sa-datafusion.iam.gserviceaccount.com.
Conceder permissão de usuário da conta de serviço
- No Google Cloud console, acesse a página Contas de serviço.
Acessar a página "Contas de serviço" - Clique em Selecionar um projeto, escolha aquele em que está localizada a conta de serviço que você quer usar para o cluster do Dataproc e clique em Abrir.
Clique no endereço de e-mail da conta de serviço do Dataproc.
Clique na guia Permissões. A página mostra uma lista de participantes que receberam papéis na conta de serviço.
Clique em CONCEDER ACESSO.
No campo Novos principais, cole o nome da conta de serviço do Cloud Data Fusion que você copiou anteriormente.
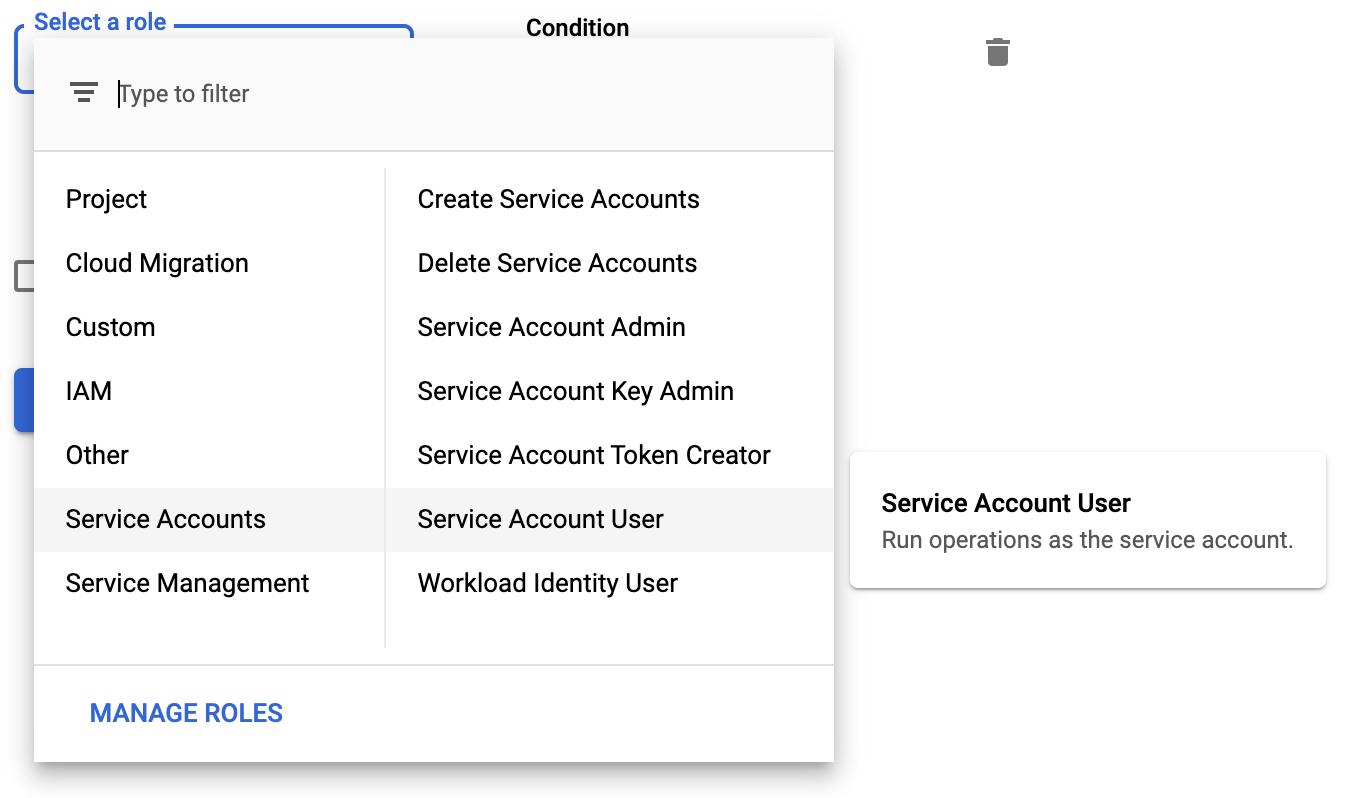
Selecione o papel Usuário da conta de serviço.
Clique em Salvar.
Conceder papéis a contas de serviço do Dataproc
Conceder permissão de papel de execução
Conceda o papel de executor do Cloud Data Fusion
(roles/datafusion.runner) às contas de serviço usadas pelo
Dataproc. Isso autoriza a conta de serviço do Dataproc a executar pipelines do Cloud Data Fusion no seu projeto.
Para mais informações, consulte Como exigir permissão para anexar contas de serviço a recursos.
Conceder permissões de administrador do Cloud Storage
Nas versões 6.2.0 e mais recentes do Cloud Data Fusion, conceda o
papel de administrador do Cloud Storage
(roles/storage.admin) às contas de serviço usadas pelo
Dataproc no projeto.
A seguir
- Saiba mais sobre o controle de acesso no Cloud Data Fusion.
- Saiba mais sobre as contas de serviço do Cloud Data Fusion.

