Artifact Analysis adalah rangkaian layanan yang menyediakan analisis komposisi software, penyimpanan dan pengambilan metadata. Titik deteksinya digunakan ke dalam sejumlah produk seperti Artifact Registry dan Google Kubernetes Engine (GKE) untuk pengaktifan yang cepat. Google Cloud Layanan ini berfungsi dengan produk pihak pertama Google Cloud' dan juga memungkinkan Anda menyimpan informasi dari sumber pihak ketiga. Layanan pemindaian menggunakan penyimpanan kerentanan umum untuk mencocokkan file dengan kerentanan yang diketahui.
Layanan ini sebelumnya dikenal sebagai Container Analysis. Nama baru ini tidak mengubah produk atau API yang ada, tetapi mencerminkan rangkaian fitur produk yang semakin luas di luar penampung.
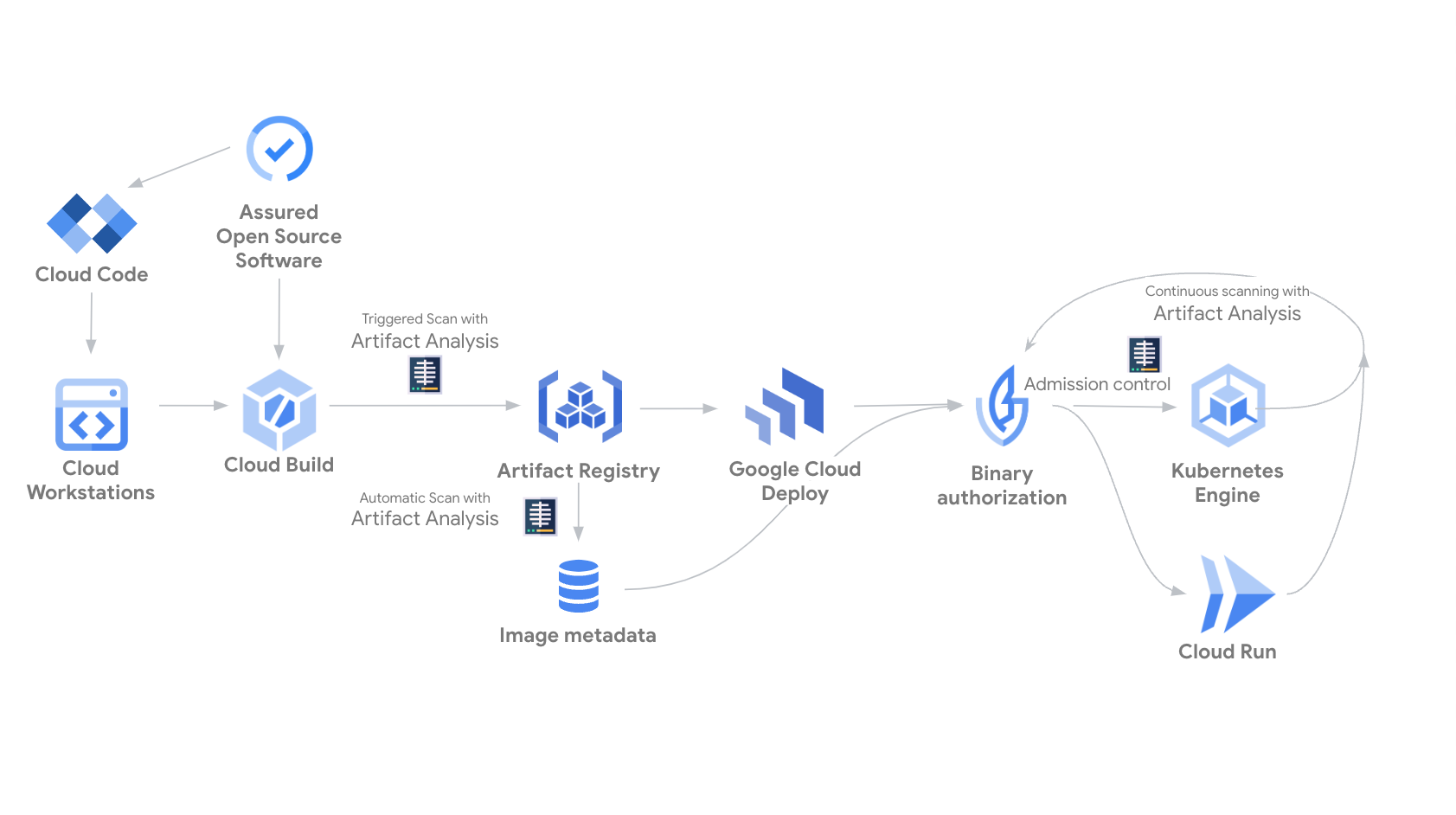
Gambar 1. Diagram yang menunjukkan Analisis Artefak membuat dan berinteraksi dengan metadata di seluruh lingkungan sumber, build, penyimpanan, deployment, dan runtime.
Pemindaian registri
Bagian ini menguraikan fitur pemindaian kerentanan Artifact Analysis berdasarkan Artifact Registry, dan mencantumkan produk terkait tempat Anda dapat mengaktifkan kemampuan pelengkap untuk mendukung postur keamanan Anda. Google Cloud
Pemindaian otomatis di Artifact Registry
- Proses pemindaian dipicu secara otomatis setiap kali Anda mengirimkan image baru ke Artifact Registry. Informasi kerentanan terus diperbarui saat kerentanan baru ditemukan. Artifact Registry menyertakan pemindaian paket bahasa aplikasi. Untuk memulai, aktifkan pemindaian otomatis.
Pengelolaan risiko terpusat dengan Security Command Center
- Security Command Center memusatkan keamanan cloud Anda, dengan menawarkan pemindaian kerentanan, deteksi ancaman, pemantauan postur, dan pengelolaan data. Security Command Center mengagregasi temuan kerentanan dari pemindaian Artifact Registry, sehingga Anda dapat melihat kerentanan image container dalam workload yang sedang berjalan, di semua project bersama dengan risiko keamanan lainnya di Security Command Center. Anda juga dapat mengekspor temuan ini ke BigQuery untuk analisis mendalam dan penyimpanan jangka panjang. Untuk mengetahui informasi selengkapnya, lihat Penilaian kerentanan Artifact Registry.
Pemindaian kerentanan workload GKE - tingkat standar
- Sebagai bagian dari dasbor postur keamanan GKE, pemindaian kerentanan workload mendeteksi kerentanan OS image container. Pemindaian gratis dan dapat diaktifkan per cluster. Hasilnya dapat dilihat di dasbor postur keamanan.
Pemindaian kerentanan workload GKE - insight kerentanan lanjutan
- Selain pemindaian OS container dasar, pengguna GKE dapat mengupgrade ke advanced vulnerability insights untuk memanfaatkan deteksi kerentanan paket bahasa berkelanjutan. Anda harus mengaktifkan fitur ini secara manual di cluster Anda, setelah itu Anda akan menerima hasil kerentanan paket bahasa dan OS. Pelajari lebih lanjut pemindaian kerentanan di workload GKE.
Pemindaian On-Demand
- Layanan ini tidak berkelanjutan; Anda harus menjalankan perintah untuk memulai pemindaian secara manual. Hasil pemindaian tersedia hingga 48 jam setelah pemindaian selesai. Informasi kerentanan tidak diperbarui setelah pemindaian selesai. Anda dapat memindai image yang disimpan secara lokal, tanpa harus mengirimkannya ke runtime GKE atau Artifact Registry terlebih dahulu. Untuk mempelajari lebih lanjut, lihat pemindaian sesuai permintaan.
Mengakses metadata
Artifact Analysis adalah komponen infrastruktur Google Cloud yang memungkinkan Anda menyimpan dan mengambil metadata terstruktur untuk Google Cloudresource. Pada berbagai tahap proses rilis, orang atau sistem otomatis dapat menambahkan metadata yang menjelaskan hasil aktivitas. Misalnya, Anda dapat menambahkan metadata ke gambar yang menunjukkan bahwa gambar tersebut telah lulus rangkaian pengujian integrasi atau pemindaian kerentanan.
Dengan Analisis Artefak yang terintegrasi ke dalam pipeline CI/CD, Anda dapat membuat keputusan berdasarkan metadata. Misalnya, Anda dapat menggunakan Otorisasi Biner untuk membuat kebijakan deployment yang hanya mengizinkan deployment untuk image yang sesuai dari registry tepercaya.
Analisis Artefak mengaitkan metadata dengan gambar melalui catatan dan kemunculan. Untuk mempelajari konsep ini lebih lanjut, lihat halaman pengelolaan metadata.
Untuk mempelajari cara menggunakan Artifact Analysis untuk pengelolaan metadata, dan biaya untuk layanan pemindaian kerentanan opsional, lihat dokumentasi Artifact Analysis.

