与在无服务器环境中托管的服务的连接
本页介绍了如何配置 Integration Connectors,以连接到托管在无服务器环境(例如 Google Cloud 中的 Cloud Run)中的服务。
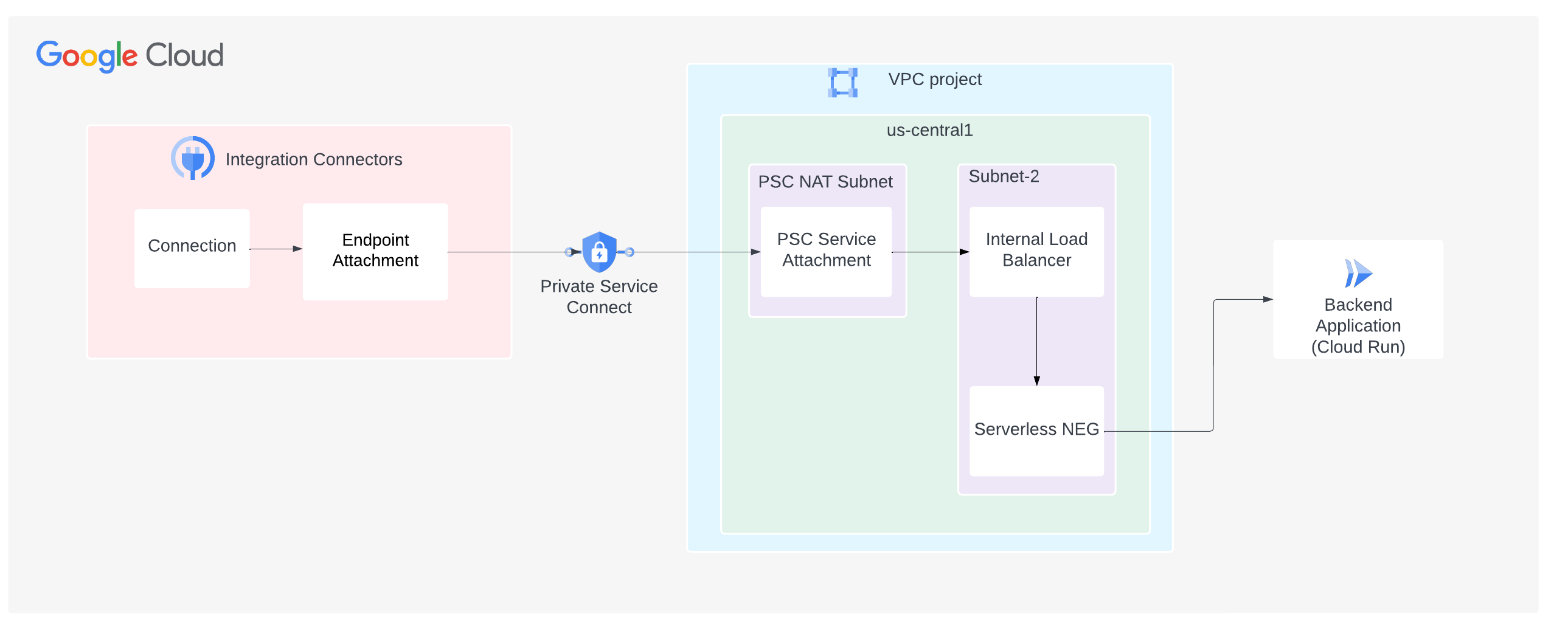
下图显示了从 Integration Connectors 到 Google Cloud 中 Cloud Run 环境中托管的服务的专用网络连接设置:
本页面假定您熟悉以下概念:
注意事项
创建 PSC 服务连接时,请考虑以下要点:
- PSC 服务连接和负载均衡器是在同一 VPC 内的不同子网中创建的。具体而言,服务连接始终是在 NAT 子网中创建的。
- 来自负载均衡器和健康检查探测的流量必须发送到同一端口。
- 配置防火墙规则以促进流量流动。
入站规则
来自 PSC 服务附件的子网的流量必须到达您的后端服务。
出站规则
除非配置了特定的拒绝规则,否则 Google Cloud 项目中默认启用出站流量。
- 您的所有 Google Cloud 组件(例如 PSC 服务连接和负载均衡器)都必须位于同一区域。
创建 PSC 服务连接
如需通过 Integration Connectors 建立专用连接,您必须使用 PSC 服务连接将服务公开给 Integration Connectors。服务附件始终使用负载均衡器。因此,如果您的服务未部署在负载均衡器后面,则需要配置负载均衡器。
- 创建负载均衡器。如果您已有负载均衡器,请跳过此步骤。
按照使用 Cloud Run 设置区域级内部应用负载均衡器中的说明操作,使用无服务器 NEG 作为后端创建应用负载均衡器。
- 创建服务连接
- 为 PSC NAT 创建子网。以下命令会创建一个名称为
psc-nat-subnet1且用途为PRIVATE_SERVICE_CONNECT的子网。gcloud compute networks subnets create psc-nat-subnet1 \ --network=VPC_NETWORK --range=SUBNET_RANGE_1 \ --purpose=PRIVATE_SERVICE_CONNECT - 创建防火墙规则,允许从 PSC NAT 到负载均衡器的流量。
gcloud compute network-firewall-policies rules create PRIORITY --firewall-policy FIREWALL_POLICY_NAME_SA \ --direction=INGRESS --network=VPC_NETWORK \ --action=allow --allow=tcp:BACKEND_SERVER_PORT --src-ip-ranges=SUBNET_RANGE_1
- 创建需要明确批准的服务连接。
gcloud compute service-attachments create SERVICE_ATTACHMENT_NAME --producer-forwarding-rule=FORWARDING_RULE_NAME --connection-preference=ACCEPT_MANUAL --consumer-accept-list=SERVICE_DIRECTORY_PROJECT_ID=LIMIT --nat-subnets=psc-nat-subnet1
在此命令中,LIMIT 是项目的连接限制。连接限制是指可以连接到此服务的使用方 PSC 端点的数量。如需获取 SERVICE_DIRECTORY_PROJECT_ID,请执行以下步骤:
-
您可以创建 PSC 服务附件,使其仅接受来自指定 Google Cloud 项目的请求。不过,为此,您需要与 Google Cloud 项目关联的服务目录的项目 ID。如需获取服务目录的项目 ID,您可以使用 List Connections API,如以下示例所示。
语法
curl -X GET \ -H "authorization: Bearer $(gcloud auth print-access-token)" \ -H "Content-Type: application/json" \ "https://connectors.googleapis.com/v1/projects/CONNECTORS_PROJECT_ID/locations/-/connections"
请替换以下内容:
- CONNECTORS_PROJECT_ID:您创建关联时所用的 Google Cloud 项目的 ID。
示例
此示例会获取
connectors-testGoogle Cloud 项目的服务目录的项目 ID。curl -X GET \ -H "authorization: Bearer $(gcloud auth print-access-token)" \ -H "Content-Type: application/json" \ "https://connectors.googleapis.com/v1/projects/connectors-test/locations/-/connections"
在终端上运行此命令会显示类似如下所示的输出:
..... { "connections": [ { "name": "projects/connectors-test/locations/asia-northeast1/connections/big-query-iam-invalid-sa", "createTime": "2022-10-07T09:02:31.905048520Z", "updateTime": "2022-10-07T09:22:39.993778690Z", "connectorVersion": "projects/connectors-test/locations/global/providers/gcp/connectors/bigquery/versions/1", "status": { "state": "ACTIVE" }, "configVariables": [ { "key": "project_id", "stringValue": "connectors-test" }, { "key": "dataset_id", "stringValue": "testDataset" } ], "authConfig": {}, "serviceAccount": "564332356444-compute@developer.gserviceaccount.com", "serviceDirectory": "projects/abcdefghijk-tp/locations/asia-northeast1/namespaces/connectors/services/runtime", "nodeConfig": { "minNodeCount": 2, "maxNodeCount": 50 } }, ....在示例输出结果中,对于
connectors-testGoogle Cloud 项目,服务目录的项目 ID 为abcdefghijk-tp。
-
- 为 PSC NAT 创建子网。以下命令会创建一个名称为
创建端点连接以使用 PSC 服务连接
将端点附件作为 IP 地址如需了解如何将端点附件创建为 IP 地址,请参阅将端点附件创建为 IP 地址。
将端点连接用作主机名在某些情况下(例如启用了 TLS 的后端),目的地要求您使用主机名(而非专用 IP)来执行 TLS 验证。如果为主机目的地使用专用 DNS 而非 IP 地址,除了将端点附件创建为 IP 地址之外,您还必须配置托管式区域。如需了解如何将端点附件创建为主机名,请参阅将端点附件创建为主机名。
稍后,在配置连接以使用端点连接时,您可以选择此端点连接。
配置连接以使用端点连接
现在,您已创建端点连接,接下来可以在关联中使用该端点连接。创建新连接或更新现有连接时,在“目标”部分中,选择端点连接作为目标类型,然后从端点连接列表中选择您创建的端点连接。
如果您创建了托管区域,请选择主机地址作为目标类型,并使用您在创建托管区域时创建的 A 记录。
问题排查提示
请遵循本部分列出的准则,以免出现常见问题:
- 如需验证端点附件是否设置正确且 PSC 连接是否已建立,请检查连接状态。如需了解详情,请参阅验证端点附件连接。
- 如需了解如何排查负载平衡器问题,请参阅排查内部应用负载平衡器问题。
- Google Cloud 连接性测试可用于找出网络配置中的任何缺口。如需了解详情,请参阅创建和运行 Connectivity Tests。