Halaman ini memberikan ringkasan tentang kumpulan pribadi dan menjelaskan fiturnya. Jika Anda baru menggunakan Cloud Build, baca Ringkasan Cloud Build.
Ringkasan kumpulan default dan kumpulan pribadi
Secara default, saat Anda menjalankan build di Cloud Build, build akan berjalan di lingkungan terhosting yang aman dengan akses ke internet publik. Setiap build berjalan di worker-nya sendiri dan diisolasi dari beban kerja lainnya. Anda dapat menyesuaikan build dengan berbagai cara, termasuk meningkatkan ukuran jenis mesin atau mengalokasikan lebih banyak ruang disk. Kumpulan default memiliki batasan terkait seberapa banyak Anda dapat menyesuaikan lingkungan, terutama terkait akses jaringan pribadi.
Kumpulan pribadi adalah kumpulan worker khusus dan pribadi yang menawarkan penyesuaian lingkungan build yang lebih baik, termasuk kemampuan untuk mengakses resource di jaringan pribadi. Kumpulan pribadi, mirip dengan kumpulan default, dihosting dan dikelola sepenuhnya oleh Cloud Build serta dapat di-scale up dan down hingga nol, tanpa perlu menyiapkan, mengupgrade, atau menskalakan infrastruktur. Karena kumpulan pribadi adalah resource khusus pelanggan, Anda dapat mengonfigurasinya dengan lebih banyak cara.
Tabel berikut membandingkan fitur kumpulan default dengan kumpulan pribadi:
| Fitur | Kumpulan default | Kolam renang pribadi |
|---|---|---|
| Terkelola sepenuhnya | ||
| Bayar per menit build | ||
| Penskalaan otomatis, penskalaan hingga 0 | ||
| Akses ke internet publik | Dapat Dikonfigurasi | |
| Melakukan peering ke VPC atau VPC bersama untuk mengakses resource pribadi | ||
| Dukungan Kontrol Layanan VPC | ||
| Rentang IP internal statis | ||
| Kemampuan untuk menonaktifkan IP publik | ||
| Build serentak maksimum | 30 | 100+ |
| Jenis mesin | 5 | 64 |
| Wilayah | global, wilayah yang didukung | wilayah yang didukung |
| Region tempat build dijalankan | Build berjalan di region yang ditentukan dalam gcloud builds submit atau di halaman pemicu konsolGoogle Cloud . |
Build berjalan di region tempat Anda membuat kumpulan pribadi. |
Arsitektur jaringan
Kumpulan pribadi adalah resource terkelola sepenuhnya yang dibuat oleh pengguna dalam Google Cloud project. Pool pribadi dapat dibuat, diupdate, dan dihapus melalui API, Google Cloud CLI, Google Cloud konsol, atau dikelola melalui alat penyediaan infrastruktur seperti Terraform.
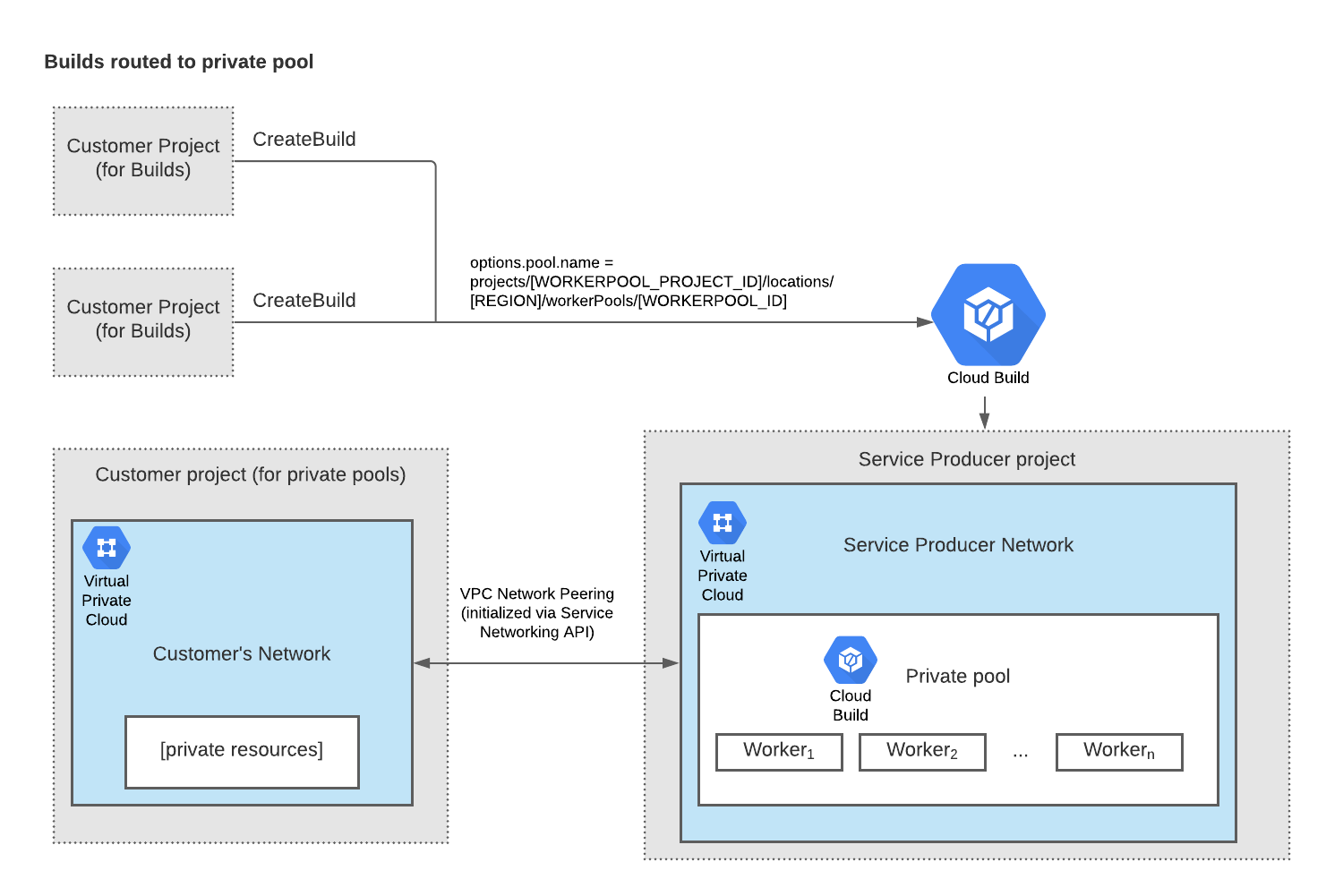
Dengan menggunakan izin Identity and Access Management, build yang dijalankan di kumpulan pribadi dapat dikirimkan di seluruh project; artinya, build tidak harus berasal dari project yang sama dengan kumpulan pribadi. Demikian pula, akun layanan yang menjalankan build dapat dikonfigurasi untuk mengizinkan pekerja mengakses resource dari project Google Cloud lain selama build.
Kumpulan pribadi dihosting di jaringan produsen layanan milik Google yang dilengkapi dengan alamat IP internal. Agar build Anda dapat mengakses resource di jaringan pribadi, Anda dapat membuat koneksi peering VPC pribadi antara jaringan VPC Anda dan jaringan produsen layanan.
Diagram berikut menunjukkan cara build dirutekan ke kumpulan pribadi. Dalam penyiapan ini, pelanggan memiliki dua project yang mengirim build ke Cloud Build. Pelanggan telah mengonfigurasi semua build dari project ini agar dirutekan ke kumpulan pribadinya. Jaringan produsen layanan, tempat pool pribadi berada, di-peering ke jaringan VPC pelanggan sehingga build memiliki akses ke resource pribadi di jaringan VPC pelanggan.
Langkah berikutnya
- Pelajari cara menyiapkan lingkungan untuk membuat kumpulan pribadi.
- Pelajari cara membuat dan mengelola pool pribadi.
- Pelajari cara mengonfigurasi kasus penggunaan jaringan yang umum digunakan.
- Pelajari cara menggunakan Kontrol Layanan VPC dengan kumpulan pribadi.

