Menyiapkan perimeter layanan menggunakan Kontrol Layanan VPC
Pelajari cara menyiapkan perimeter layanan menggunakan Kontrol Layanan VPC di konsol Google Cloud .
Sebelum memulai
Sebaiknya periksa apakah Anda memiliki peran Identity and Access Management (IAM) yang diperlukan untuk mengelola Kontrol Layanan VPC.
Jika Anda tidak memiliki peran IAM yang diperlukan, lihat Mengelola akses ke project, folder, dan organisasi untuk mengetahui informasi tentang cara memberikan peran IAM.
Menyiapkan perimeter Kontrol Layanan VPC
Di bagian berikut, Anda menentukan detail perimeter, menambahkan project dan layanan yang akan dilindungi, serta membuat perimeter.
Tambahkan detail perimeter Kontrol Layanan VPC
Di konsol Google Cloud , buka halaman VPC Service Controls.
Untuk membuat perimeter baru menggunakan kebijakan akses default, pilih organisasi Anda dari menu pemilih project.
Jika organisasi Anda tidak memiliki kebijakan akses, ikuti langkah-langkah berikut:
Di halaman VPC Service Controls, klik Kelola kebijakan.
Di halaman Kelola Kontrol Layanan VPC, klik Buat.
Di halaman Buat kebijakan akses, di kolom Judul kebijakan akses, masukkan
access_policy_1.Klik Buat kebijakan akses.
Di halaman VPC Service Controls, klik New perimeter.
Di halaman Create a service perimeter, di kolom Title, masukkan
perimeter_storage_services.Untuk Jenis perimeter dan Mode penerapan, pertahankan pilihan default.
Klik Lanjutkan.
Menambahkan project ke perimeter
Untuk menambahkan project ke perimeter, klik Tambahkan project.
Di panel Tambahkan Project, pilih project yang ingin Anda tambahkan ke perimeter, lalu klik Tambahkan project yang dipilih.
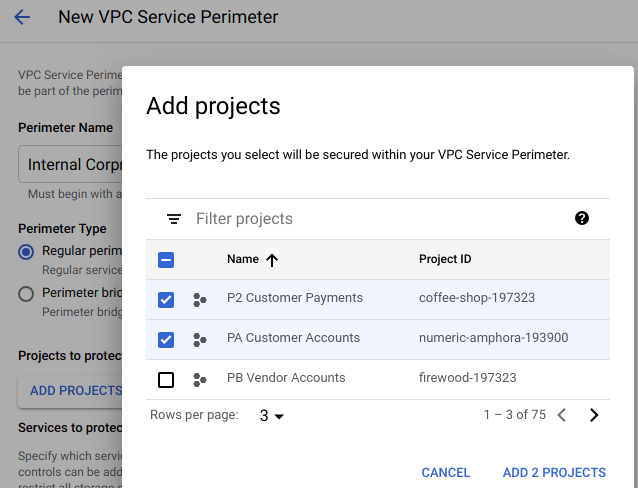
Klik Lanjutkan.
Mengamankan layanan BigQuery dan Cloud Storage dalam perimeter
Di panel Layanan yang dibatasi, klik Tambahkan layanan.
Di panel Add services, centang kotak untuk BigQuery dan Cloud Storage API.
Untuk menemukan layanan, Anda dapat menggunakan kueri filter.
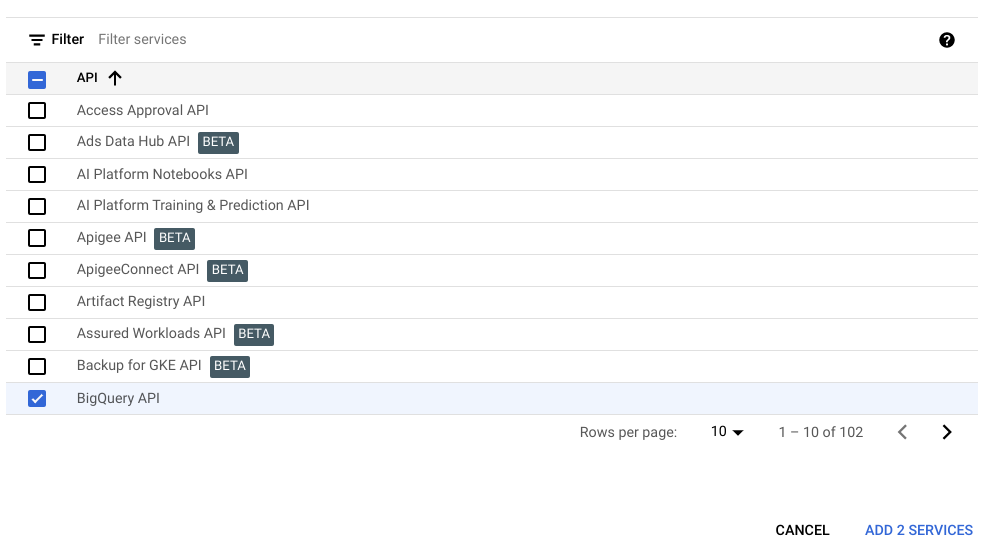
Klik Tambahkan layanan yang dipilih.
Klik Buat.
Anda baru saja membuat perimeter. Anda dapat melihat perimeter Anda yang tercantum di halaman Kontrol Layanan VPC. Perimeter mungkin memerlukan waktu hingga 30 menit untuk diterapkan dan berlaku. Setelah perubahan diterapkan, akses ke layanan BigQuery dan Cloud Storage dibatasi untuk project yang Anda tambahkan ke perimeter.
Selain itu, antarmuka konsol untuk layanan BigQuery dan Cloud Storage yang Anda lindungi dengan perimeter mungkin menjadi sebagian atau sepenuhnya tidak dapat diakses. Google Cloud
Pembersihan
Agar akun Google Cloud Anda tidak dikenai biaya untuk resource yang digunakan pada halaman ini, ikuti langkah-langkah berikut.
Di konsol Google Cloud , buka halaman VPC Service Controls.
Di halaman VPC Service Controls, pada baris yang sesuai dengan perimeter yang Anda buat, klik Hapus.
Di kotak dialog, klik Hapus untuk mengonfirmasi bahwa Anda ingin menghapus perimeter.
Langkah berikutnya
- Pelajari lebih lanjut cara membuat perimeter layanan.
- Pelajari cara mengelola perimeter layanan yang ada.
- Pelajari batasan penggunaan layanan tertentu dengan Kontrol Layanan VPC.

