This page describes the basic concepts of Identity-Aware Proxy (IAP), a Google Cloud global service.
IAP lets you establish a central authorization layer for applications accessed by HTTPS, so you can use an application-level access control model instead of relying on network-level firewalls.
IAP policies scale across your organization. You can define access policies centrally and apply them to all of your applications and resources. When you assign a dedicated team to create and enforce policies, you protect your project from incorrect policy definition or implementation in any application.
When to use IAP
Use IAP when you want to enforce access control policies for applications and resources. IAP works with signed headers or the App Engine standard environment Users API to secure your app. With IAP, you can set up group-based application access: a resource could be accessible for employees and inaccessible for contractors, or only accessible to a specific department.
How IAP works
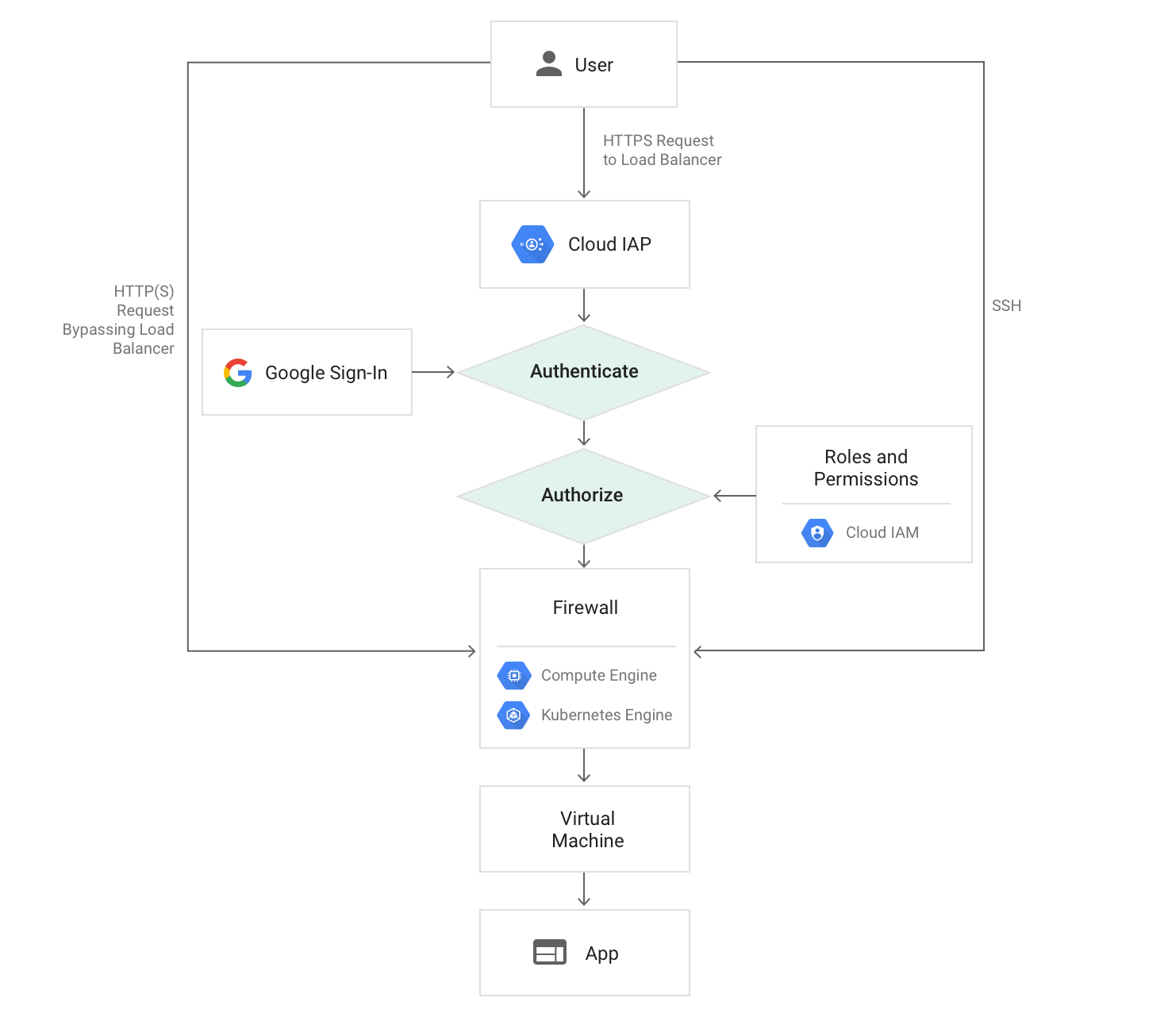
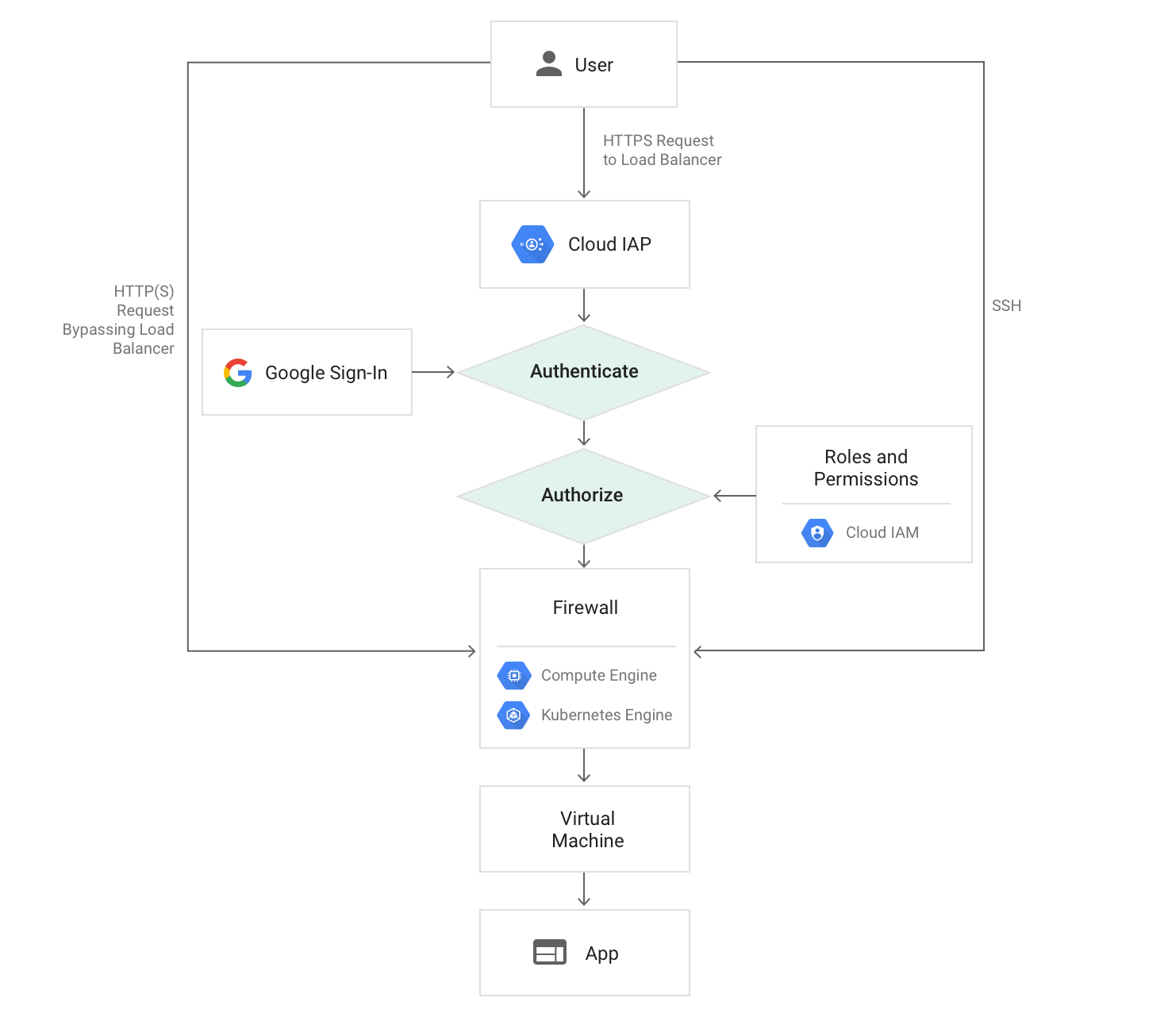
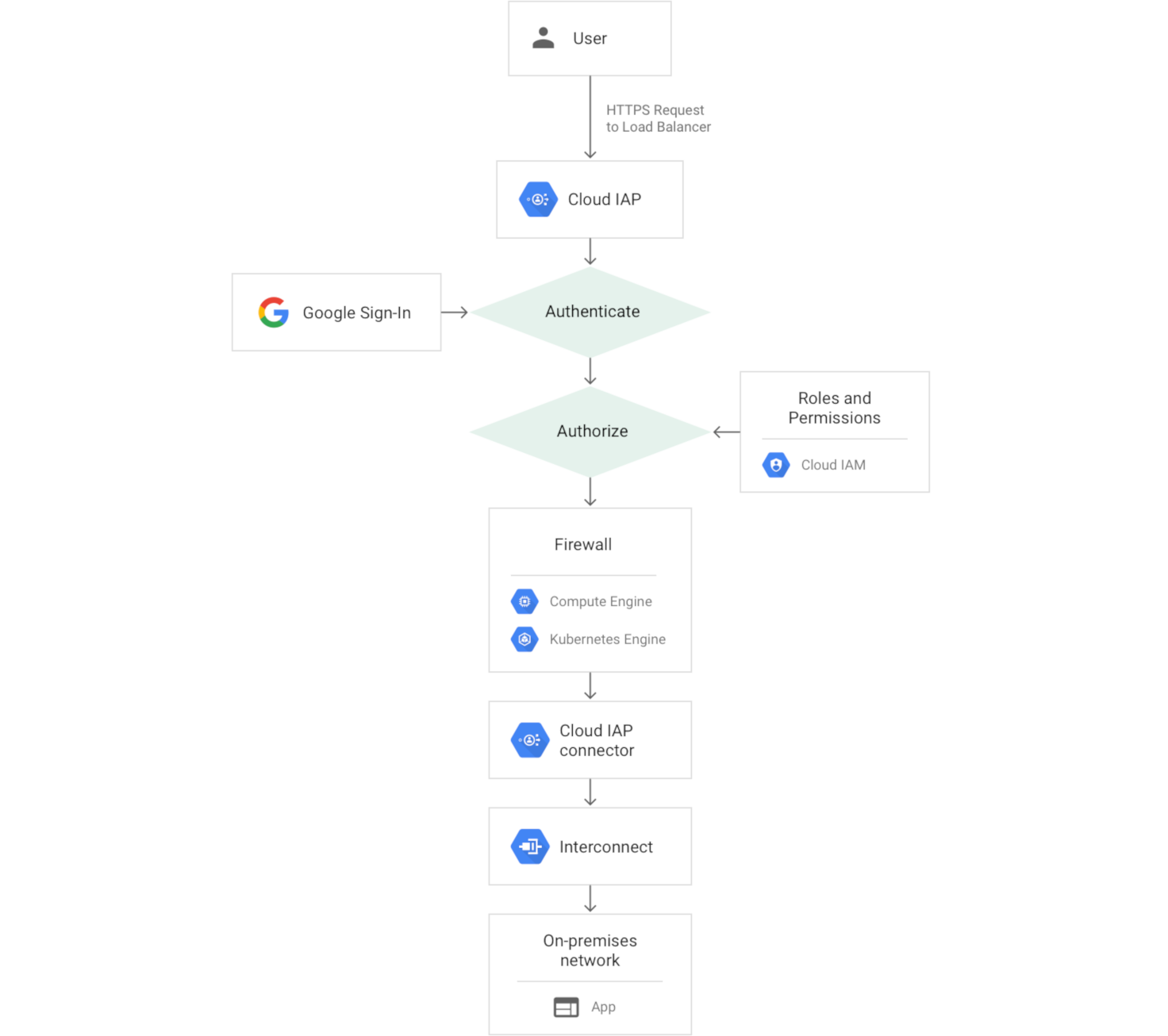
When an application or resource is protected by IAP, it can only be accessed through the proxy by principals, also known as users, who have the correct Identity and Access Management (IAM) role. When you grant a user access to an application or resource by IAP, they're subject to the fine-grained access controls implemented by the product in use without requiring a VPN. When a user tries to access an IAP-secured resource, IAP performs authentication and authorization checks.


Authentication
Requests to your Google Cloud resources come through Cloud Run, App Engine, and Cloud Load Balancing (External and Internal HTTP(S) Load Balancing). The serving infrastructure code for these products checks if IAP is enabled for the app or backend service. If IAP is enabled, information about the protected resource is sent to the IAP authentication server. This includes information like the Google Cloud project number, the request URL, and any IAP credentials in the request headers or cookies.
Next, IAP checks the user's browser credentials. If none exist, the user is redirected to an OAuth 2.0 Google Account sign-in flow that stores a token in a browser cookie for future sign-ins. If you need to create Google Accounts for your existing users, you can use Google Cloud Directory Sync to synchronize with your Active Directory or LDAP server.
If the request credentials are valid, the authentication server uses those credentials to get the user's identity (email address and user ID). The authentication server then uses the identity to check the user's IAM role and check if the user is authorized to access the resource.
If you're using Compute Engine or Google Kubernetes Engine, users who can access the application-serving port of the Virtual Machine (VM) can bypass IAP authentication. Compute Engine and GKE firewall rules can't protect against access from code running on the same VM as the IAP-secured application. Firewall rules can protect against access from another VM, but only if properly configured. Learn about your responsibilities to ensure security.
If you're using Cloud Run, you can enable IAP in the following ways:
- Directly on your Cloud Run services. This enables IAP to protect all ingress paths to Cloud Run, including the auto-assigned URL and any configured load balancer URL. This configuration is useful when you have a single Cloud Run service to enable IAP for.
- Through a load balancer with a Cloud Run backend. This configuration is useful when you have multiple Cloud Run services in different regions behind a single global load balancer. In this configuration, the auto-assigned URL is unprotected by IAP and might be directly accessible. Learn more about your responsibilities to ensure security.
If a Cloud Run service is behind a load balancer, don't enable IAP on both the load balancer and the Cloud Run service.
Authorization
After authentication, IAP applies the relevant IAM policy to check if the user is authorized to access the requested resource. If the user has the IAP-secured Web App User role on the Google Cloud console project where the resource exists, they're authorized to access the application. To manage the IAP-secured Web App User role list, use the IAP panel on the Google Cloud console.
When you turn on IAP for a resource, it automatically creates an OAuth 2.0 client ID and secret. If you delete the automatically generated OAuth 2.0 credentials, IAP won't function correctly. You can view and manage OAuth 2.0 credentials in the Google Cloud console APIs & services.
Context-aware access
As part of the authorization step, you can use context-aware access to provide secure access to the following types of resources:
Google Cloud console and APIs
- First layer of defense in protecting infrastructure access to Google Cloud.
- Advanced context-aware Google Cloud access to users.
Virtual Machines (VMs)
- Enables administrative SSH/RDP access to VMs in Google Cloud and in other clouds.
- Lets you implement robust context-aware controls to restrict access to only designated administrators.
Web applications
- Provides authorization and authentication for web applications hosted in Google Cloud and other clouds.
- Provides continuous authorization to prevent unauthorized access and data loss.
Your responsibilities
IAP secures authentication and authorization of all requests to Cloud Run, App Engine, Cloud Load Balancing (HTTPS), and internal HTTP load balancing.
To ensure security, you must take the following precautions:
- If you're enabling IAP on a load balancer, verify whether the
backend resources can be accessed directly.
- If the backend resource is a VM, configure your firewall rules to protect against traffic that doesn't come through the load balancer. IAP doesn't protect against activity within a project, such as another VM inside the project.
- If the backend resource is a Cloud Run service, you can disable the run.app URL to ensure that all ingress comes in through the load balancer. If you choose to leave the run.app URL enabled, you should use ingress controls to block traffic from outside your network.
- Update your app to use signed headers or use the App Engine standard environment Users API.
What's next
- Get started with IAP by completing one of the following
tasks:
- Enable IAP directly on your Cloud Run services or on a load balancer with a Cloud Run backend.
- Complete the App Engine quickstart to Manage Access with Google Accounts.
- Enable IAP for Compute Engine.
- Enable IAP for GKE.
- Enable IAP for on-premises apps.
- Learn more:
