Virtual Private Cloud (VPC) firewall rules apply to a single VPC network. To have finer control over the traffic sent or received by the virtual machine (VM) instances in your VPC network, you can use network tags or service accounts in the VPC firewall rules. However, VPC firewall rules have the following limitations:
No batch editing: VPC firewall rules are applied on a per-rule basis and must be edited individually, which can be inefficient.
Limited Identity and Access Management (IAM) control: Network tags don't offer the robust IAM controls needed for strict traffic segmentation.
To address the limitations of VPC firewall rules, Cloud Next Generation Firewall supports global and regional network firewall policies. You can define and apply network firewall policies to multiple VPC networks across multiple regions. These policies also support IAM-governed secure tags that let you enforce granular control at the VM level for safe and reliable micro-segmentation of all types of network traffic.
For more information, see Benefits of migrating VPC firewall rules to a network firewall policy.
To control access to your VPC network, you can migrate your existing VPC firewall rules to a global network firewall policy to take advantage of the capabilities of network firewall policies.
Benefits of migrating VPC firewall rules to a network firewall policy
A network firewall policy delivers a consistent firewall experience across the Google Cloud resource hierarchy and offers multiple operational benefits over VPC firewall rules.
Provides granular security and access control by using IAM governed Tags. Google Cloud lets you attach separate Tags to each network interface of a VM. Based on the Tags, you can define your firewall policy rules to restrict unauthorized access to your resources and workload traffic. So, you gain a finer level of control over your resources, which helps to ensure a least-privilege, self-service environment for each user group or application. VPC firewall rules use network tags, which don't support IAM access control.
Enables simplified rule management. Network firewall policies support batch editing, which lets you edit multiple rules within a single policy. VPC firewall rules operate only at a per-rule level.
Provides ease of operations. Network firewall policies support the use of features, such as fully qualified domain name (FQDN) objects, geolocation objects, threat detection, intrusion prevention, and address groups. VPC firewall rules don't support these advanced features.
Supports flexible data residency. Network firewall policies can be applied to either multiple regions or a single region of a network. VPC firewall rules can only be applied globally.
VPC firewall rules migration tool
The VPC firewall rules migration tool can automatically migrate VPC firewall rules to a global network firewall policy. The tool is a command-line utility that you can access using the Google Cloud CLI.
Specifications
The migration tool creates a global network firewall policy, converts the existing VPC firewall rules into firewall policy rules, and adds the new rules to the policy.
If two or more VPC firewall rules have the same priority, the migration tool automatically updates the rule priorities to avoid any overlap. A rule with a
denyaction is given a higher priority than a rule with anallowaction. While updating the priorities, the tool preserves the relative sequence of the original VPC firewall rules.For example, if you have four VPC firewall rules with a priority of
1000and a fifth rule with a priority of2000, the migration tool assigns a unique priority number to the first four rules with the sequence—1000,1001,1002, and1003. The fifth rule with the priority of2000is assigned a new unique priority of1004. This ensures that the new priorities for the first four rules are higher than that of all rules that have priority lower than1000.If your VPC firewall rules contain dependencies, such as network tags or service accounts, the migration tool can take advantage of IAM-governed Tags that serve as a replacement to those network tags and services accounts.
If your VPC network contains VPC firewall rules and an associated network firewall policy, the migration tool moves the compatible VPC firewall rules as well as the network firewall policy rules to the new global network firewall policy.
The migration tool preserves the log settings of the existing VPC firewall rules. If a VPC firewall rule has logging turned on, the migration tool keeps it on. If logging is off, the migration tool keeps it turned off.
The migration tool generates the global network firewall policy only. The tool does not delete existing VPC firewall rules or associate the new global network firewall policy with the required VPC network. You must manually associate the global network firewall policy with the required VPC network, and then remove the association between the VPC firewall rules and the VPC network.
After you associate the global network firewall policy with the required VPC network, you can disable the VPC firewall rules if the policy rules in the global network firewall policy are working as intended.
If necessary, you can associate the new global network firewall policy as well as the VPC firewall rules with the same VPC network because the rules are applied according to the policy and rule evaluation order. However, we recommend you disable the VPC firewall rules.
Migration scenarios
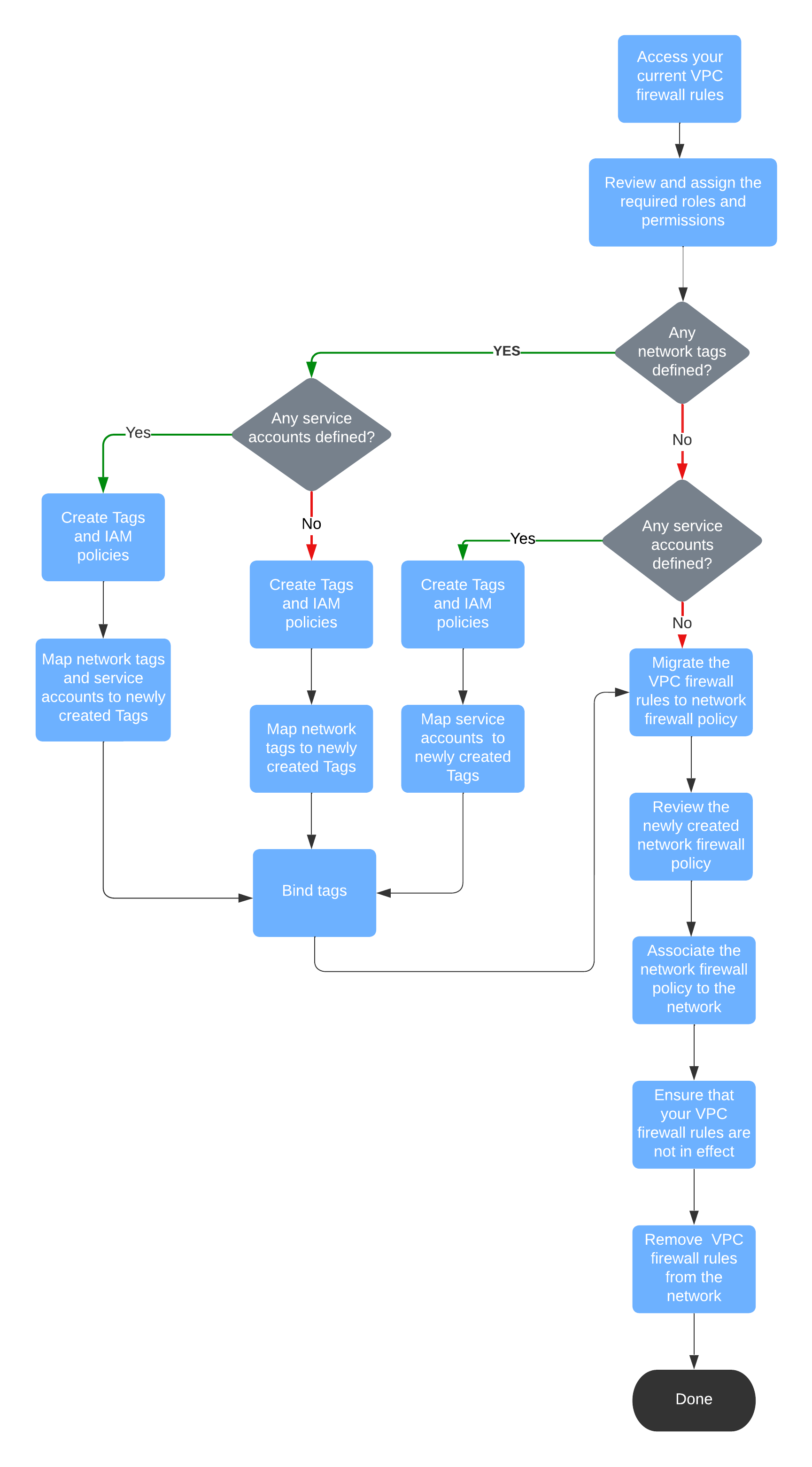
Consider the following scenarios when you migrate your VPC firewall rules to a global network firewall policy:
- VPC firewall rules don't contain network tags or service accounts.
- VPC firewall rules contain network tags or target service accounts, or both.
The following diagram shows the migration workflow for the preceding configuration combinations. Choose the workflow that matches your network requirements.
What's next
- Migrate VPC firewall rules that don't use network tags and service accounts
- Migrate VPC firewall rules that use network tags and service accounts
