Meninjau dan menyetujui permintaan akses menggunakan kunci penandatanganan kustom
Dokumen ini menunjukkan cara menyiapkan Persetujuan Akses menggunakan konsolGoogle Cloud dan kunci penandatanganan kustom untuk menerima notifikasi email tentang permintaan akses pada sebuah project.
Persetujuan Akses memastikan bahwa persetujuan yang ditandatangani secara kriptografis ada agar personel Google dapat mengakses konten Anda yang disimpan di Google Cloud.
Persetujuan Akses memungkinkan Anda membawa kunci kriptografi Anda sendiri untuk menandatangani permintaan akses. Anda dapat membuat kunci menggunakan Cloud Key Management Service atau menggunakan kunci yang dikelola secara eksternal menggunakan Cloud External Key Manager.
Sebelum memulai
- Aktifkan Transparansi Akses untuk organisasi Anda. Untuk mengetahui informasi selengkapnya, lihat Mengaktifkan Transparansi Akses.
- Pastikan Anda memiliki peran IAM
Access Approval Config Editor
(
roles/accessapproval.configEditor).
Mendaftar ke Access Approval
Untuk mendaftar ke Persetujuan Akses, lakukan hal berikut:
Di konsol Google Cloud , pilih project yang ingin Anda aktifkan Persetujuan Aksesnya.
Buka halaman Persetujuan Akses.
Untuk mendaftar ke Access Approval, klik Daftar.
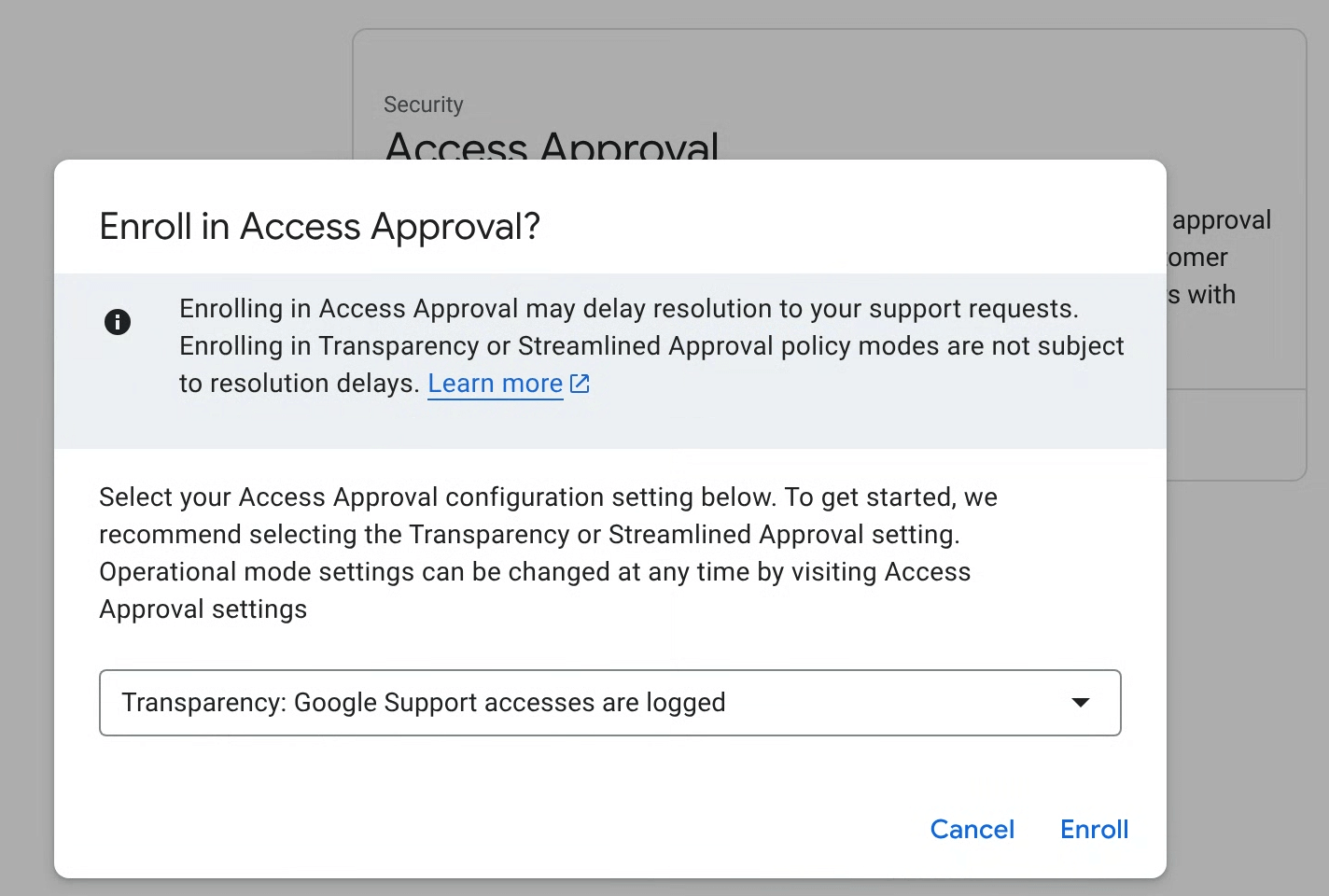
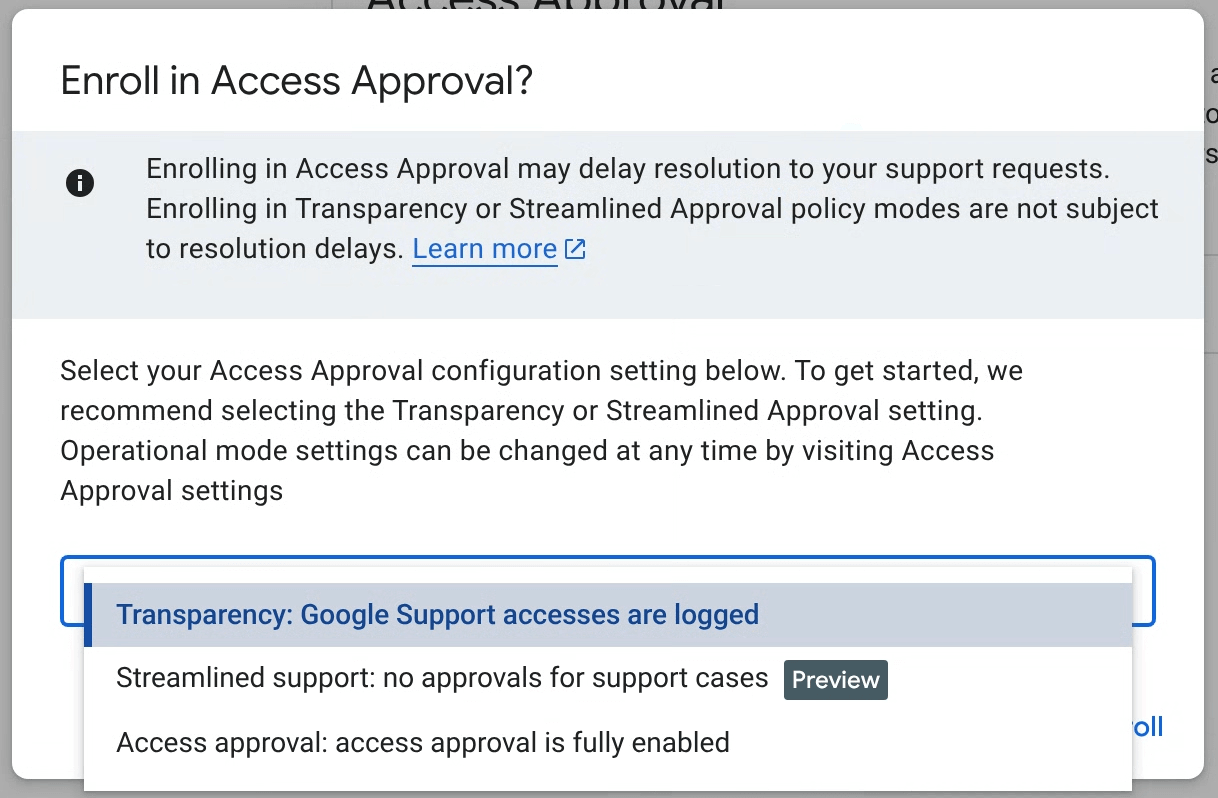
Pada dialog, pilih mode pendaftaran untuk kebijakan Anda, lalu klik Daftarkan.
Mode pendaftaran utama Access Approval
Anda dapat mengonfigurasi Persetujuan Akses dalam salah satu dari tiga mode, dan dapat mengubah mode kapan saja di setelan Persetujuan Akses. Mode berikut dapat dipilih:
- Transparansi (Direkomendasikan): Gunakan mode ini untuk mencatat akses administratif Google ke workload Anda saja tanpa mengganggu dukungan Google untuk kasus dukungan atau pemeliharaan proaktif pada workload Anda. Lihat dokumen Transparansi Akses untuk informasi selengkapnya.
- Dukungan yang disederhanakan (Pratinjau): Gunakan mode ini untuk menyetujui akses Layanan Pelanggan secara otomatis untuk menangani kasus dukungan Anda. Akses pemeliharaan dan perbaikan proaktif akan diminta untuk disetujui dengan Persetujuan Akses. Fitur ini berada dalam tahap peluncuran Pratinjau.
- Persetujuan Akses: Gunakan mode ini untuk mengaktifkan fungsi Persetujuan Akses penuh untuk semua akses.
Log Transparansi Akses dibuat secara otomatis untuk semua kebijakan Persetujuan Akses.
Mengonfigurasi setelan
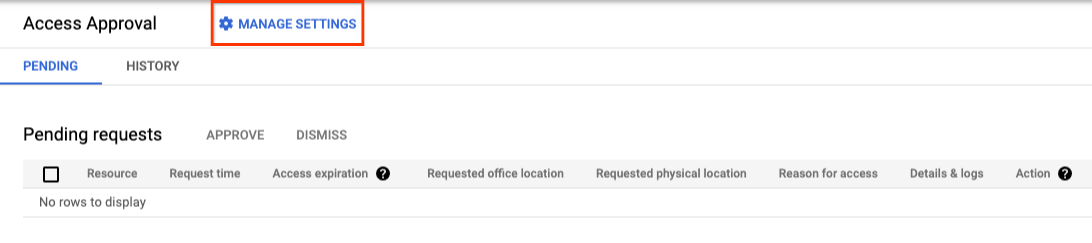
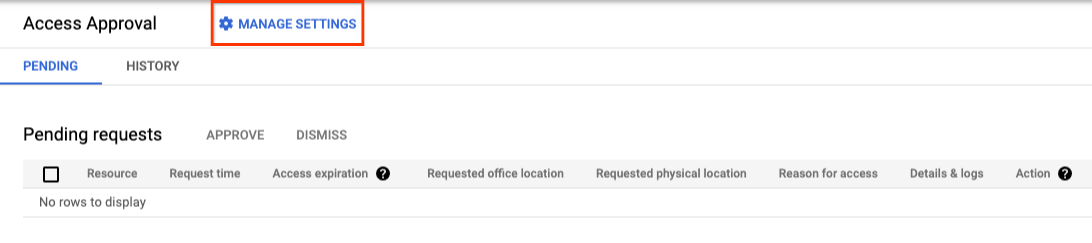
Di halaman Persetujuan Akses di konsol Google Cloud , klik Kelola setelan.
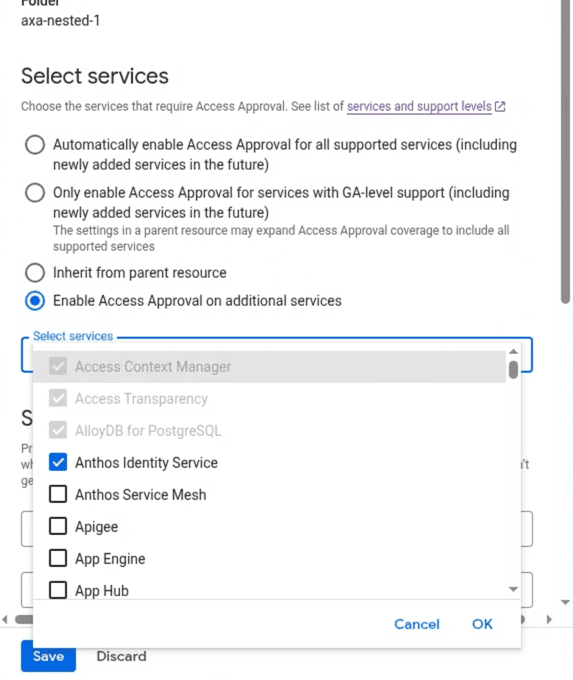
Pilih layanan
Setelan Access Approval, termasuk daftar produk yang diaktifkan, diwarisi dari resource induk. Anda dapat memperluas cakupan pendaftaran dengan mengaktifkan Persetujuan Akses untuk semua atau layanan tambahan tertentu yang didukung.
Menyiapkan notifikasi email
Bagian ini menjelaskan cara Anda dapat menerima notifikasi permintaan akses untuk project ini.
Memberikan peran IAM yang diperlukan
Untuk melihat dan menyetujui permintaan akses, Anda harus memiliki peran IAM Access Approval Approver (roles/accessapproval.approver).
Untuk memberikan peran IAM ini kepada diri Anda sendiri, lakukan hal berikut:
- Buka halaman IAM di konsol Google Cloud .
- Di tab Lihat menurut akun utama, klik Beri akses.
- Di kolom Akun utama baru di panel kanan, masukkan alamat email Anda.
- Klik kolom Pilih peran, lalu pilih peran Penyetuju Persetujuan Akses dari menu.
- Klik Simpan.
Menambahkan diri Anda sebagai pemberi persetujuan untuk permintaan Persetujuan Akses
Untuk menambahkan diri Anda sebagai pemberi persetujuan sehingga Anda dapat meninjau dan menyetujui permintaan akses, lakukan hal berikut:
Buka halaman Persetujuan Akses di konsol Google Cloud .
Klik Kelola setelan.
Di bagian Siapkan notifikasi persetujuan, tambahkan alamat email Anda di kolom Email pengguna atau grup.
Untuk menyimpan setelan notifikasi, klik Simpan.
Menggunakan kunci penandatanganan kustom
Persetujuan Akses menggunakan kunci penandatanganan untuk memverifikasi integritas permintaan Persetujuan Akses.
Jika Cloud EKM diaktifkan, Anda dapat memilih kunci penandatanganan yang dikelola secara eksternal. Untuk mengetahui informasi tentang penggunaan kunci eksternal, lihat Ringkasan Cloud EKM.
Anda juga dapat memilih untuk membuat kunci penandatanganan Cloud KMS dengan algoritma pilihan Anda. Untuk mengetahui informasi selengkapnya, lihat Membuat kunci asimetris.
Untuk menggunakan kunci penandatanganan kustom, ikuti petunjuk di bagian ini.
Dapatkan alamat email akun layanan
Alamat email untuk akun layanan memiliki format berikut:
service-pPROJECT_NUMBER@gcp-sa-accessapproval.
Ganti PROJECT_NUMBER dengan nomor project.
Misalnya, alamat emailnya adalah service-p123456789@gcp-sa-accessapproval.
untuk akun layanan dalam project yang nomor projectnya adalah 123456789.
Untuk menggunakan kunci penandatanganan Anda, lakukan hal berikut:
Di halaman Persetujuan Akses di konsol Google Cloud , pilih Gunakan kunci penandatanganan Cloud KMS (lanjutan).
Tambahkan ID resource versi kunci kriptografis.
ID resource versi kunci kriptografis harus memiliki format berikut:
projects/PROJECT_ID/locations/LOCATION/keyRings/KEYRING_ID/cryptoKeys/CRYPTOKEY_ID/cryptoKeyVersions/KEY_ID
Untuk mengetahui informasi selengkapnya, lihat Mendapatkan ID resource Cloud KMS.
Untuk menyimpan setelan Anda, klik Simpan.
Untuk menggunakan kunci penandatanganan kustom, Anda harus memberikan peran IAM Cloud KMS CryptoKey Signer/Verifier (
roles/cloudkms.signerVerifier) kepada akun layanan Persetujuan Akses untuk project Anda.Jika akun layanan Persetujuan Akses tidak memiliki izin untuk menandatangani dengan kunci yang Anda berikan, Anda dapat memberikan izin yang diperlukan dengan mengklik Berikan. Setelah memberikan izin, klik Simpan.


Meninjau permintaan Persetujuan Akses
Setelah mendaftar ke Persetujuan Akses dan menambahkan diri Anda sebagai pemberi persetujuan untuk permintaan akses, Anda akan menerima notifikasi email untuk permintaan akses.
Gambar berikut menunjukkan contoh notifikasi email yang dikirim Persetujuan Akses saat personel Google meminta akses ke Data Pelanggan.


Untuk meninjau dan menyetujui permintaan akses masuk, lakukan hal berikut:
Buka halaman Persetujuan Akses di konsol Google Cloud .
Untuk membuka halaman ini, Anda juga dapat mengklik link di email yang dikirimkan kepada Anda berisi permintaan persetujuan.
Klik Approve.
Setelah Anda menyetujui permintaan, personel Google dengan karakteristik yang cocok dengan persetujuan, seperti justifikasi, lokasi, atau lokasi meja yang sama dapat mengakses resource yang ditentukan dan resource turunannya dalam jangka waktu yang disetujui.
Pembersihan
-
Untuk membatalkan pendaftaran dari Access Approval, lakukan hal berikut:
- Di halaman Persetujuan Akses di konsol Google Cloud , klik Kelola setelan.
- Klik Batalkan pendaftaran.
- Pada dialog yang terbuka, klik Batalkan pendaftaran.
- Untuk menonaktifkan Transparansi Akses bagi organisasi Anda, hubungi Cloud Customer Care.
Tidak ada langkah tambahan yang diperlukan untuk menghindari pengenaan biaya ke akun Anda.
Langkah berikutnya
- Pelajari anatomi permintaan akses.
- Pelajari cara menyetujui permintaan Persetujuan Akses.
- Pelajari cara melihat histori permintaan Persetujuan Akses.

