This document shows you how to set up Chrome Enterprise Premium integration with Microsoft Intune. Setting up this integration involves setting up Intune, setting up Endpoint Verification, setting up Azure workload identity, and enabling Microsoft Intune on your organizational units.
Before you begin
-
To set up Intune for Chrome Enterprise Premium, do the following:
- Understand the supported configurations and ensure that your environment satisfies the networking requirements.
- Sign in to your trial subscription or create a new Intune subscription.
- Set DNS registration to connect your company's domain name with Intune.
- Add users and groups, or connect Active Directory to sync with Intune.
- Give users permission to use Intune by assigning licenses.
For more information, see Set up Intune.
Ensure that the devices in your organization run one of the following operating systems:
- macOS version 10.11 or later
- Microsoft® Windows 10 or later
- Set up Endpoint Verification for your organization.
Connect to Intune
- Find your Microsoft 365 tenant ID.
- Register your application to obtain an application ID.
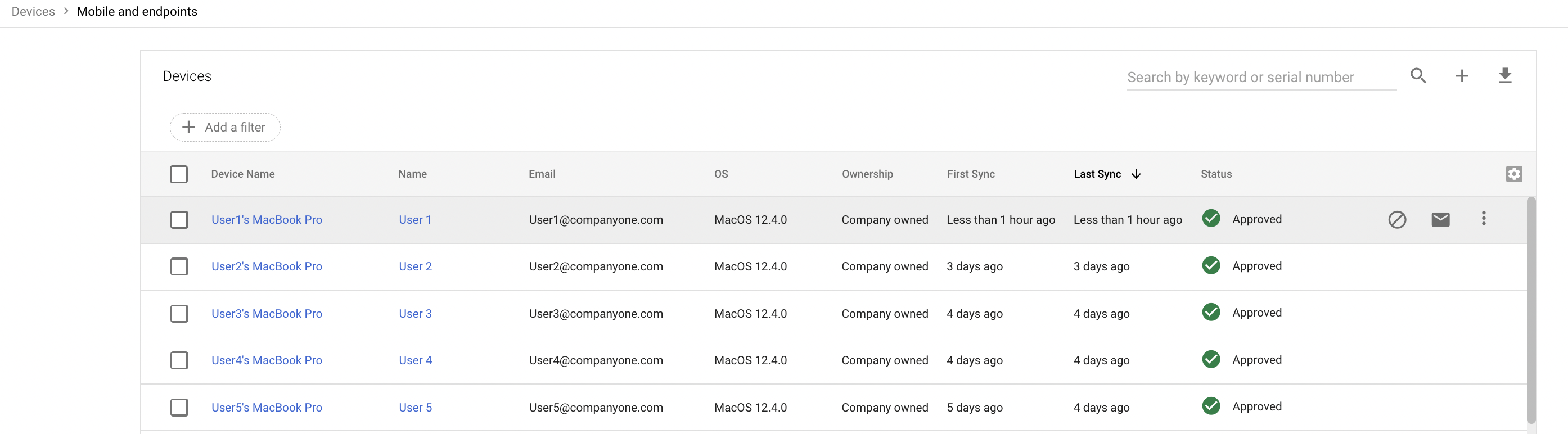
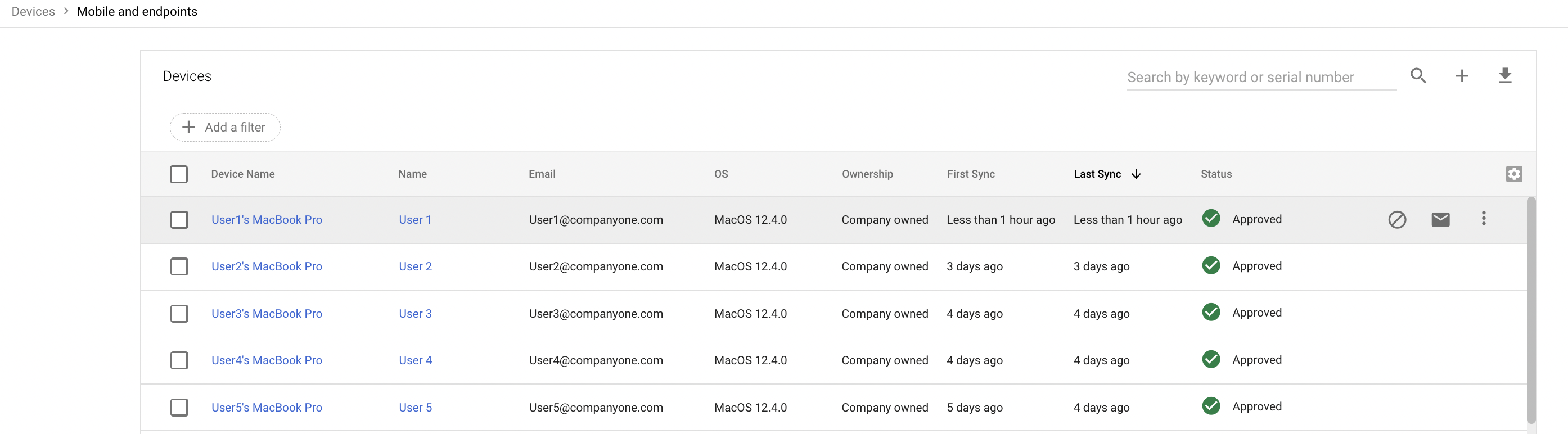
From the Admin console Home page, go to Devices.
Go to Devices- In the navigation menu, click Mobile & endpoints > Settings > Third-party integrations > Security and MDM partners > Manage.
- Look for Microsoft Intune and click Open connection.
In the Connect to Intune dialog, enter the tenant ID in the Azure directory tenant id field and application ID in the Azure application id field.
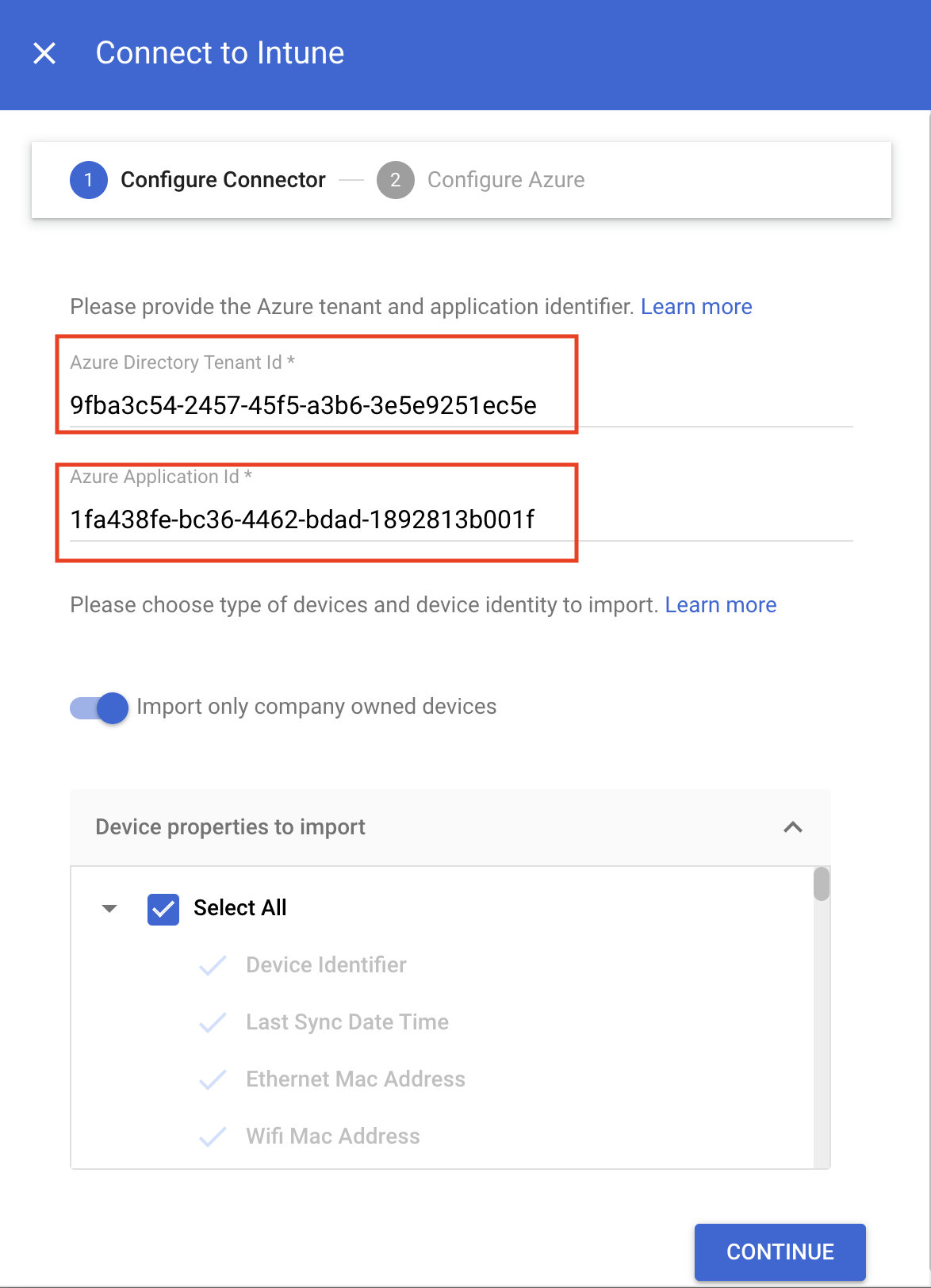
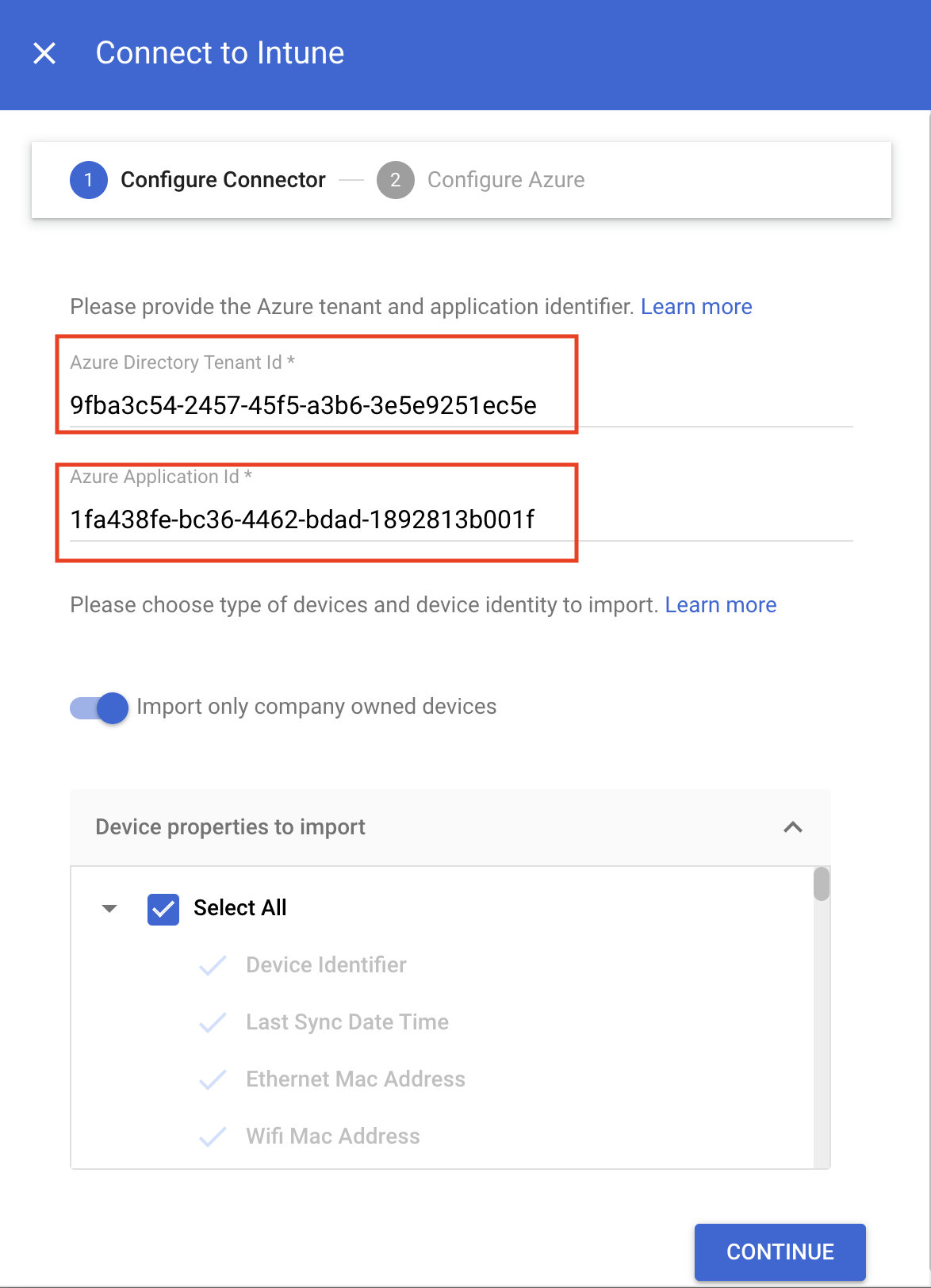
- Depending on whether you want to import only company-owned devices or import all devices, perform the appropriate action:
- To import only company-owned devices, click the Import only company-owned devices toggle. In the Device properties to import section, select the properties that must be stored in Chrome Enterprise Premium.
To import all devices, in the Device properties to import section, select the properties that must be stored in Chrome Enterprise Premium.
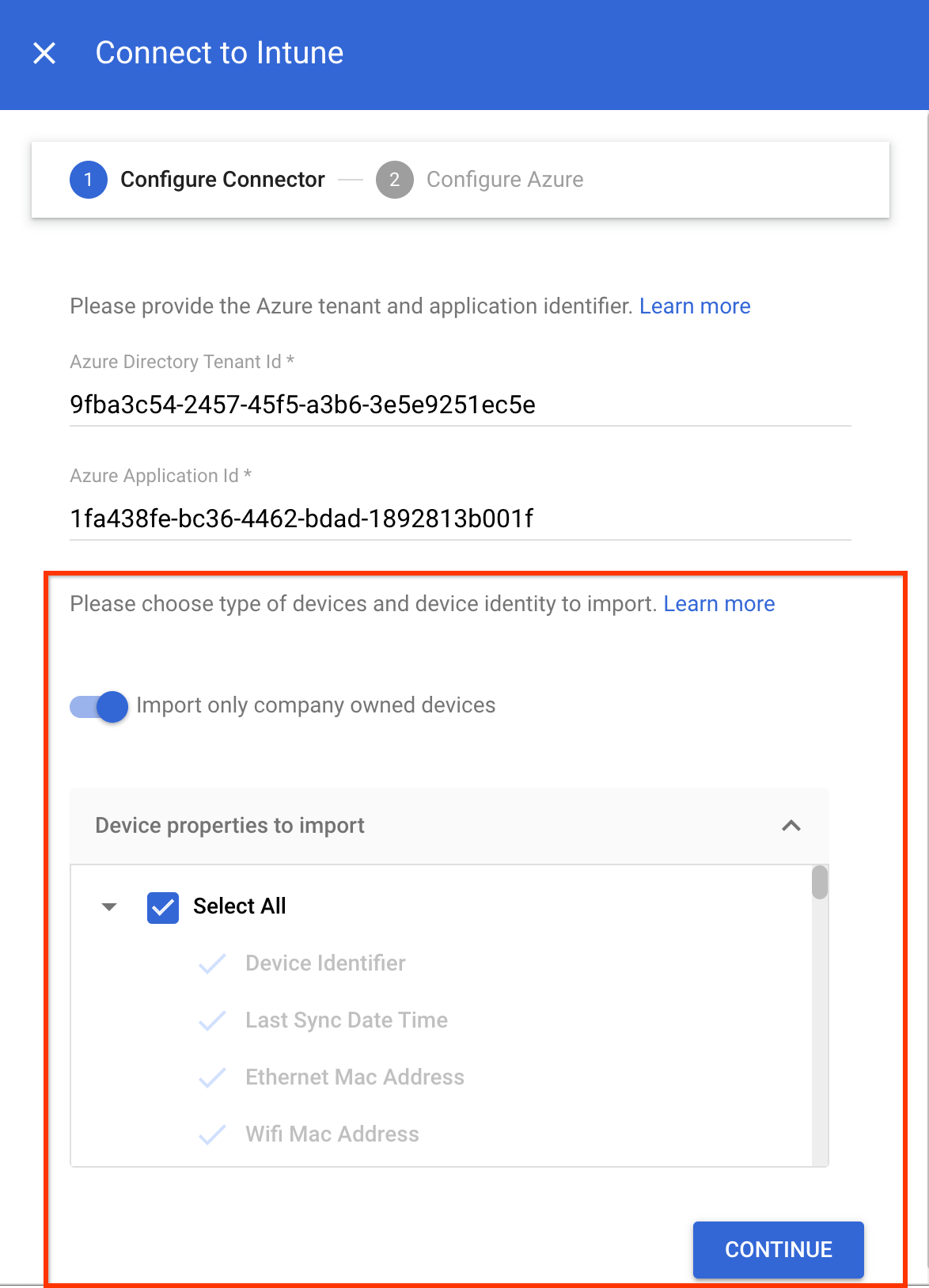
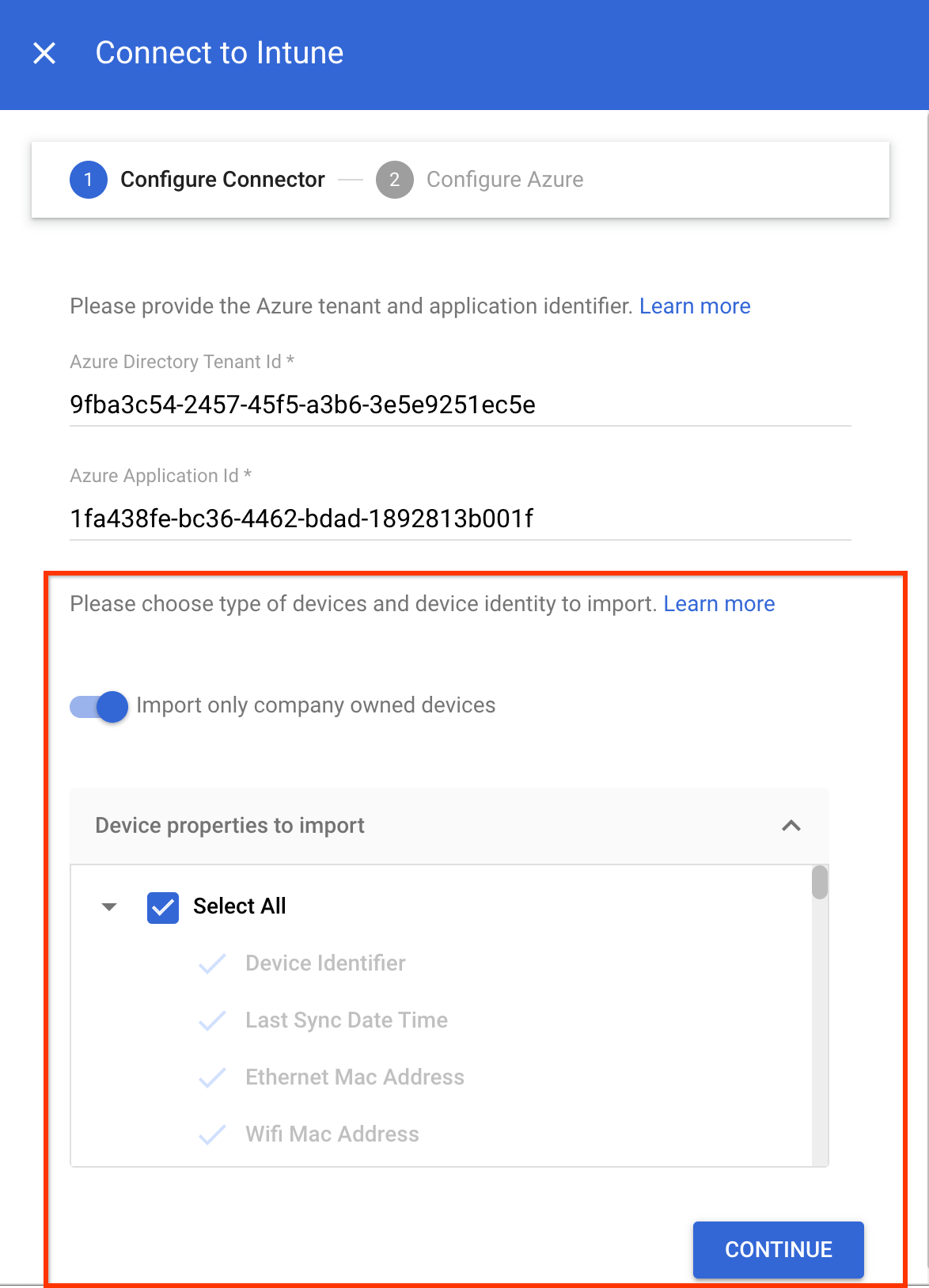
The mandatory device properties such as
device identifier,last sync time,serial number, andwifi MAC addressare collected by default.For more information about the device properties that Intune collects, see Intune device properties.
- Click Continue.
- Copy the Service account ID.
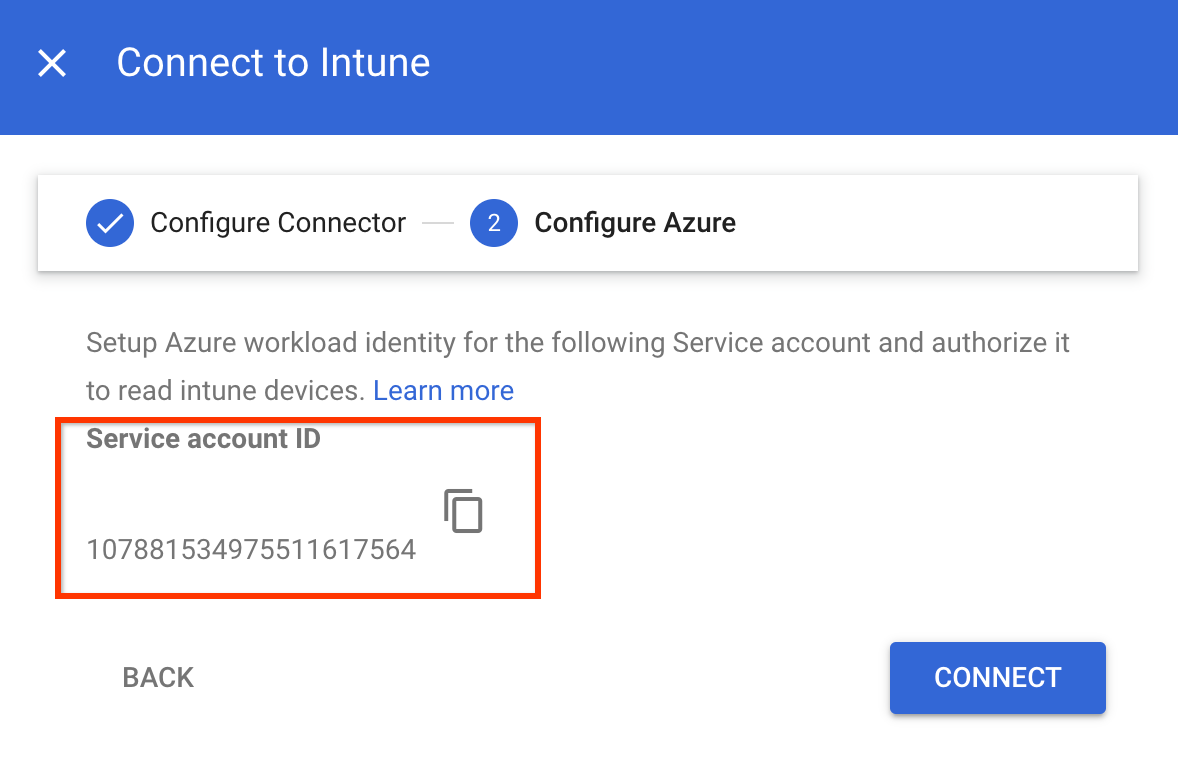
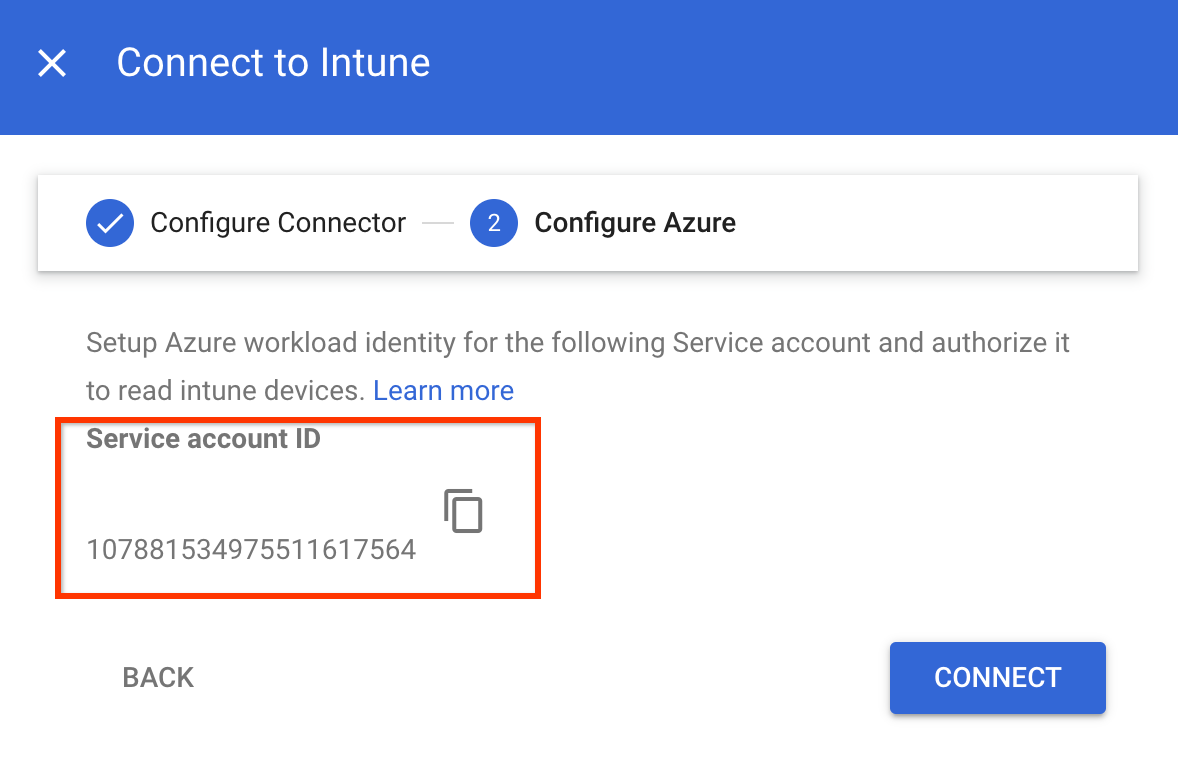
- Use the Service account ID to authorize Azure workload identity
to collect data from the Intune devices:
- Configure your app to trust an external identity provider.
Specify the following values in the corresponding fields:
- Name: Any name for the federated credential.
- Subject identifier: The Service account ID that you copied.
- Issuer:
https://accounts.google.com.
- Grant your app permissions:
- Search for
DeviceManagementManagedDevices.Read.AllandDeviceManagementApps.Read.Allpermissions and add these permissions to Microsoft Graph. When requesting the API permissions, select Application permissions.DeviceManagementManagedDevices.Read.Allprovides read access to all devices and their properties managed by Intune, andDeviceManagementApps.Read.Allprovides read access to the Intune audit logs for device deletion events. - Grant admin consent to the permissions configured for your application.
- Search for
- Configure your app to trust an external identity provider.
- In the Connect to Intune dialog, click Connect.
The connection to Intune is set to open.
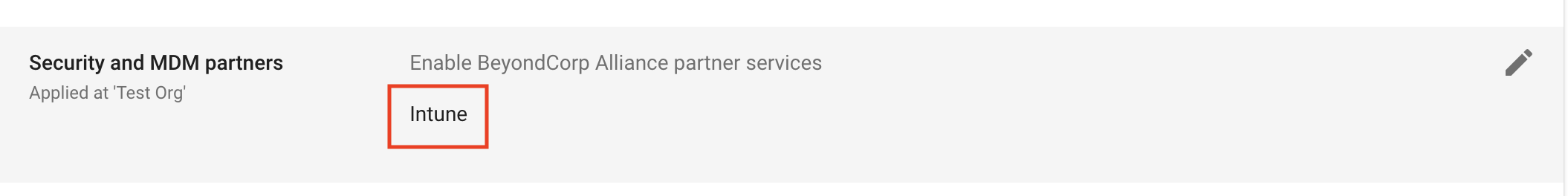
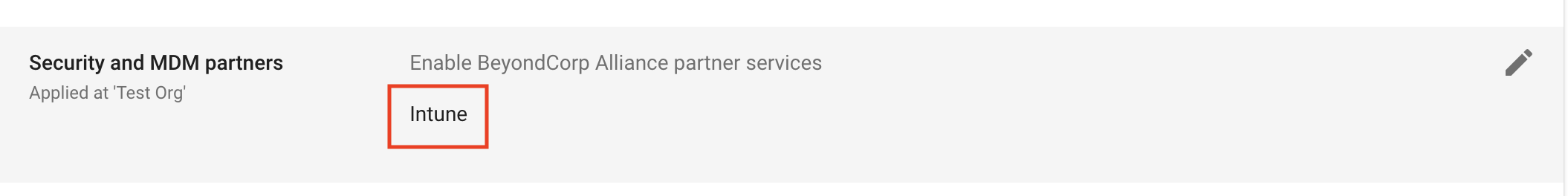
Enable Intune for your organizational unit
To collect device information by using Intune, enable Intune for your organizational unit by doing the following:
From the Admin console Home page, go to Devices.
Go to Devices- In the navigation menu, click Mobile & endpoints > Settings > Third-party integrations > Security and MDM partners.
- From the Organizational units pane, select your organization unit.
Select the checkbox for Microsoft Intune, and click Save.
Microsoft Intune is now listed in the Security and MDM partners section. Depending on the size of your organization, it might take a few seconds to establish the connection between Endpoint Verification and Intune. After the connection is established, the devices might take a few minutes to an hour to report Intune data.
Verify Intune data on devices
From the Admin console Home page, go to Devices.
Go to Devices- Click Endpoints.
Select any device from your organizational unit for which Intune is enabled.
Verify that the Microsoft Intune data is listed in the Third-party services section.
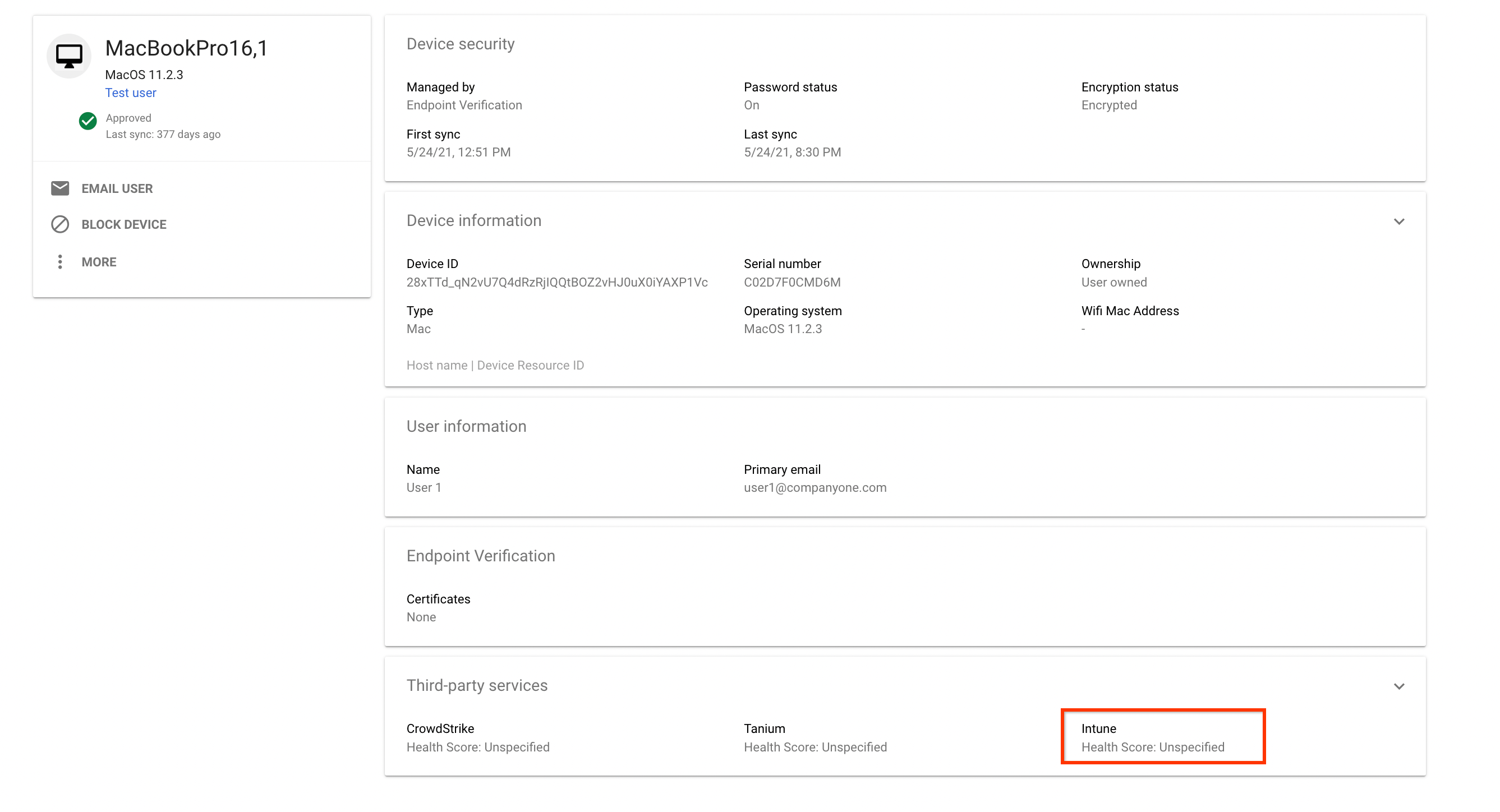
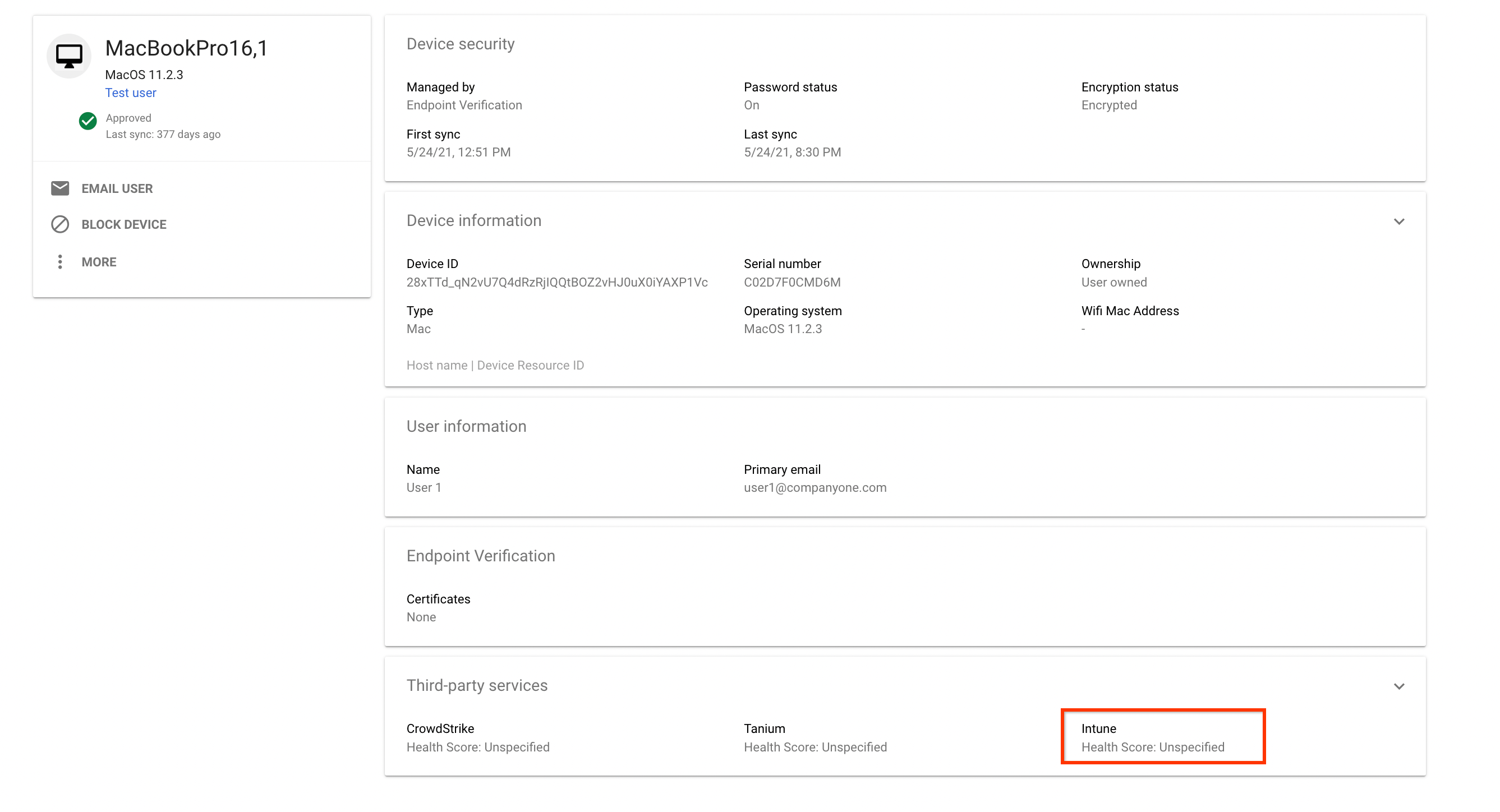
To see the complete details, expand the Third-party services section.
The following image shows details of the data collected by Intune:
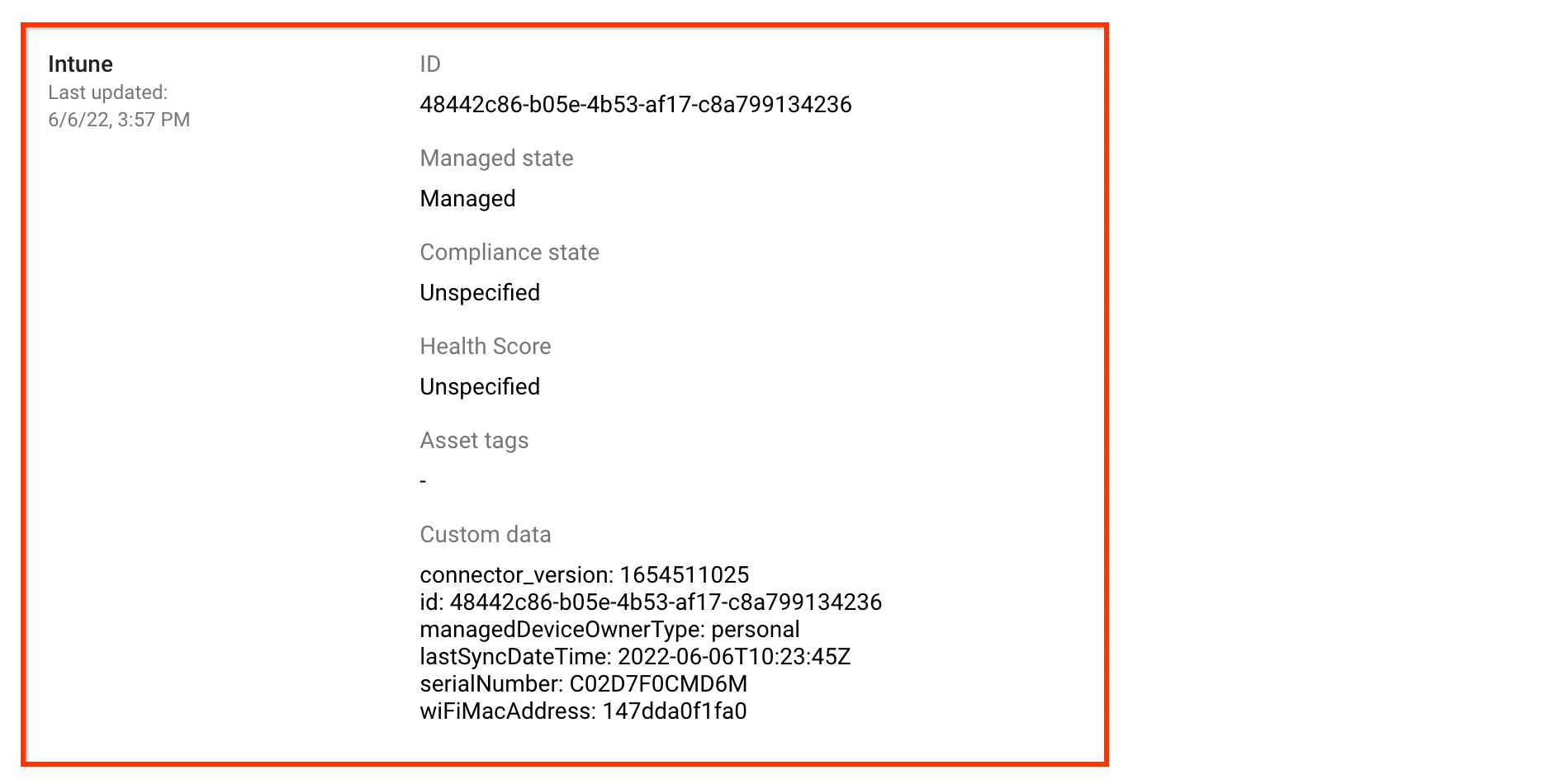
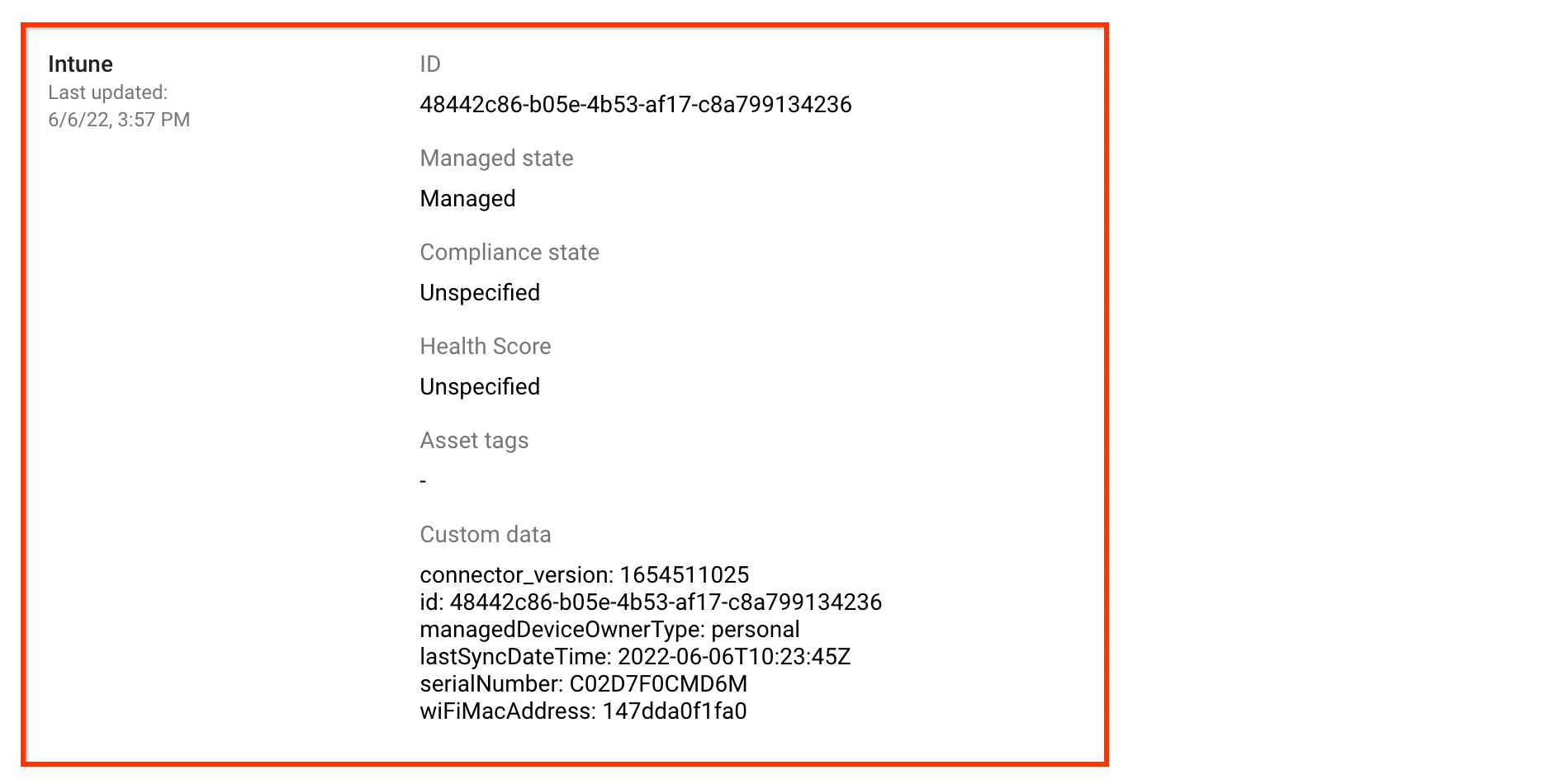
The compliance states reported by Intune are broadly categorized into the following compliance states:
| Compliance states on the Google Admin console | Compliance states reported by Intune |
|---|---|
COMPLIANCE_STATE_UNSPECIFIED |
unknown, configManager |
COMPLIANT |
compliant |
NON_COMPLIANT |
noncompliant, conflict, error,
inGracePeriod |
