使用自定义签名密钥查看和批准访问权限请求
本文档介绍了如何使用Google Cloud 控制台和自定义签名密钥设置 Access Approval,以接收项目访问请求的电子邮件通知。
Access Approval 可确保 Google 员工在访问您存储在Google Cloud中的内容时,必须获得经过加密签名的批准。
借助 Access Approval,您可以使用自己的加密密钥对访问请求进行签名。您可以使用 Cloud Key Management Service 创建密钥,也可以使用 Cloud External Key Manager 引入外部管理的密钥。
准备工作
- 为组织启用 Access Transparency。如需了解详情,请参阅启用 Access Transparency。
- 确保您拥有 Access Approval Config Editor (
roles/accessapproval.configEditor) IAM 角色。
注册 Access Approval
如需注册 Access Approval,请执行以下操作:
在 Google Cloud 控制台中,选择要为其启用访问审批的项目。
前往 Access Approval 页面。
如需注册 Access Approval,请点击注册。
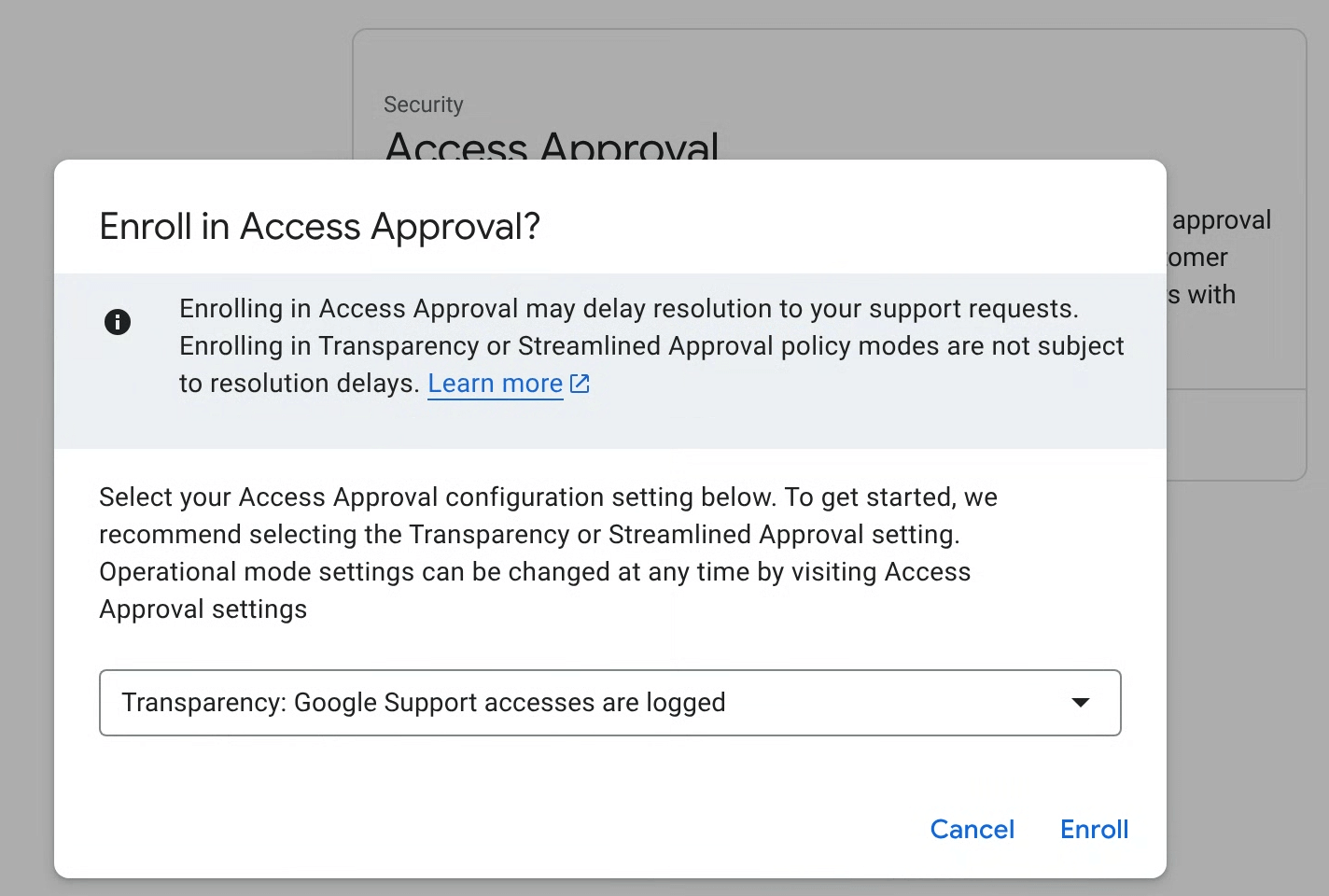
在对话框中,为您的政策选择注册模式,然后点击注册。
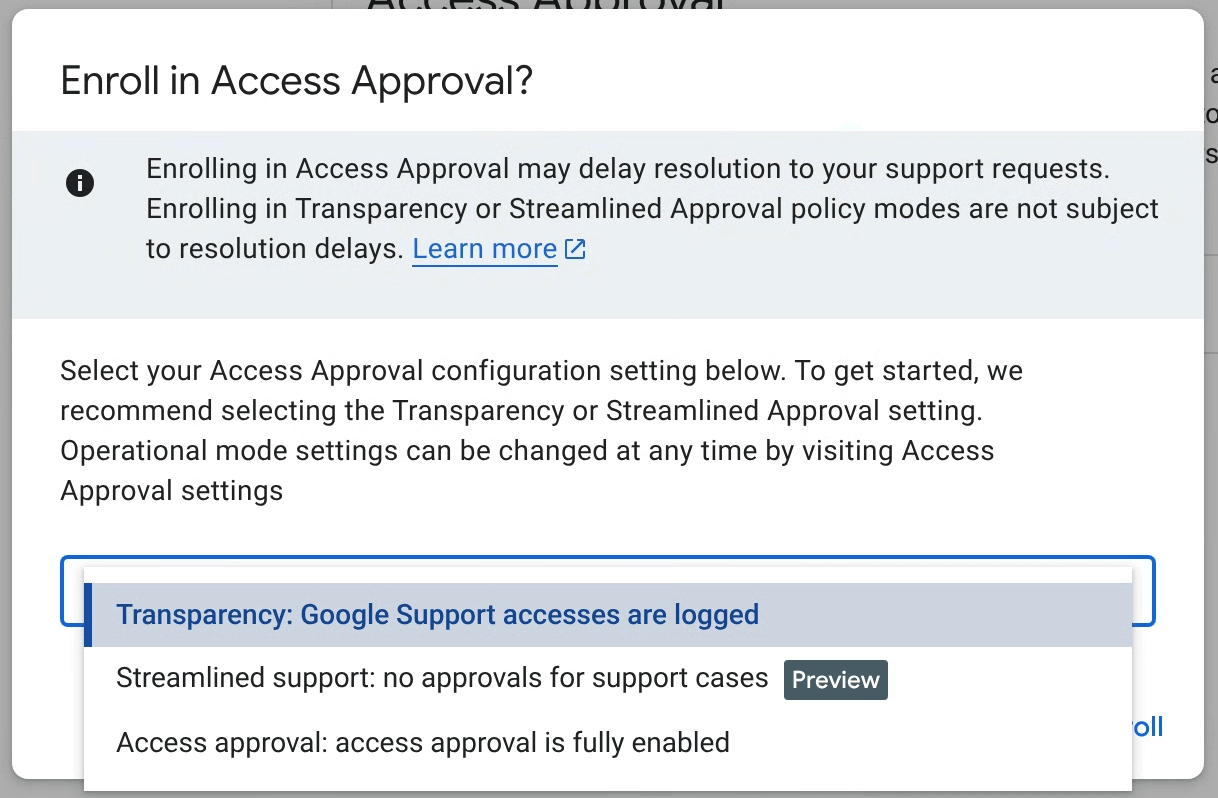
Access Approval 主要注册模式
您可以通过以下三种模式之一配置 Access Approval,并且可以随时在 Access Approval 设置中更改模式。您可以选择以下模式:
- 透明模式(推荐):使用此模式可仅记录 Google 对工作负载的管理访问权限,而不会中断 Google 对支持服务工单的支持或对工作负载的主动维护。如需了解详情,请参阅 Access Transparency 文档。
- 简化支持(预览版):使用此模式可自动批准客户服务团队访问您的支持请求,以便他们处理这些请求。系统会通过 Access Approval 请求批准主动维护和维修访问权限。此功能尚处于预览版发布阶段。
- Access Approval:使用此模式可为所有访问启用完整的 Access Approval 功能。
系统会自动为所有 Access Approval 政策生成 Access Transparency 日志。
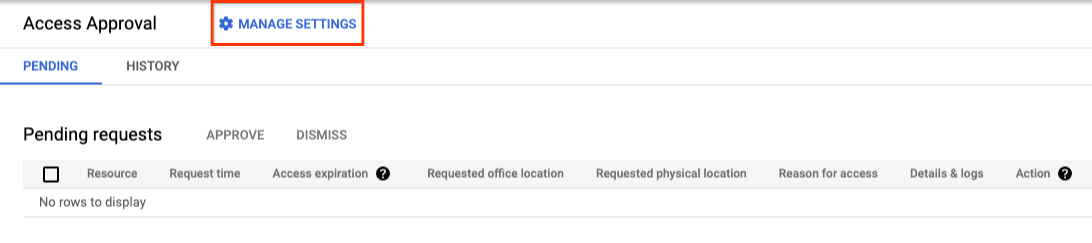
配置设置
在 Google Cloud 控制台的访问权限审批页面上,点击 管理设置。
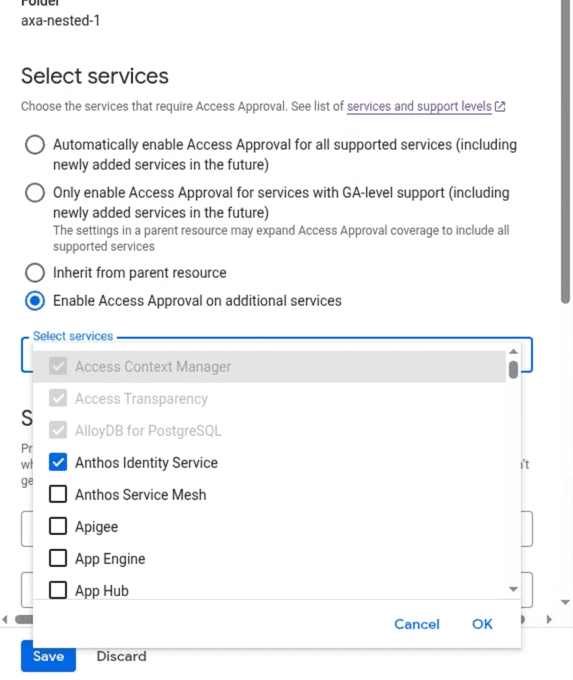
选择服务
Access Approval 设置(包括已启用产品的列表)继承自父资源。您可以为所有或选定的其他支持的服务启用 Access Approval,从而扩大注册范围。
设置电子邮件通知
本部分介绍了如何接收此项目的访问权限请求通知。
授予所需的 IAM 角色
如需查看和批准访问权限请求,您必须拥有 Access Approval Approver (roles/accessapproval.approver) IAM 角色。
如需为自己授予此 IAM 角色,请执行以下操作:
- 前往 Google Cloud 控制台中的 IAM 页面。
- 在按主账号查看标签页中,点击 授予访问权限。
- 在右侧窗格的新的主账号字段中,输入您的电子邮件地址。
- 点击选择角色字段,然后从菜单中选择访问权限审批者角色。
- 点击保存。
将自己添加为访问权限审批请求的审批者
如需将自己添加为审批人,以便查看和批准访问权限请求,请执行以下操作:
前往 Google Cloud 控制台中的 Access Approval 页面。
点击 管理设置。
在设置审批通知下,在用户或群组电子邮件地址字段中添加您的电子邮件地址。
如需保存通知设置,请点击保存。
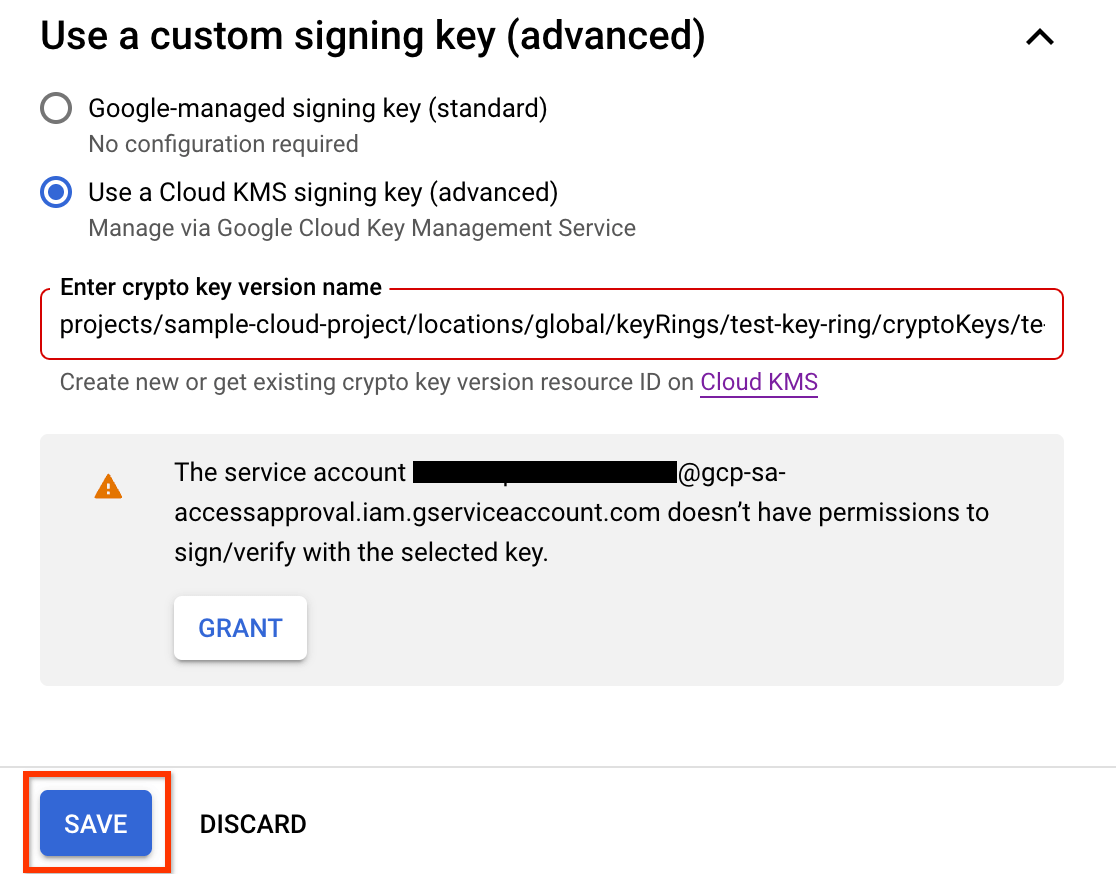
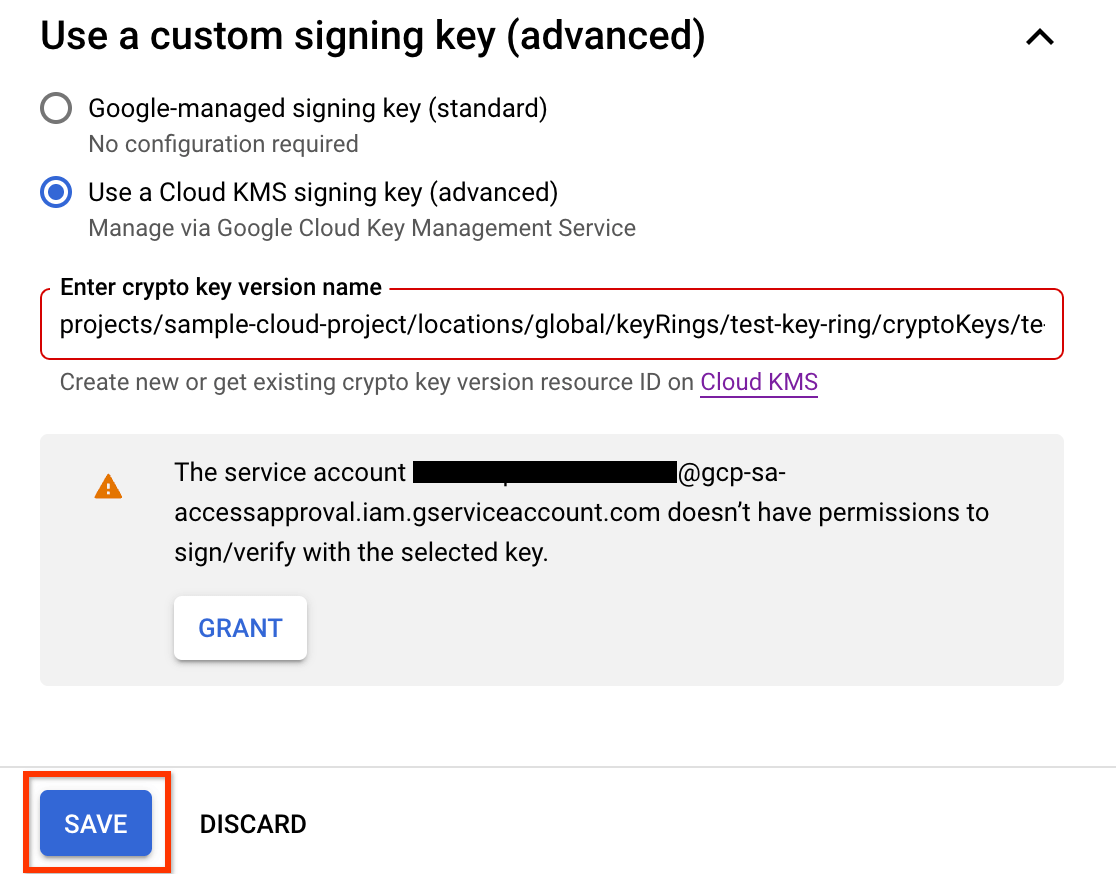
使用自定义签名密钥
Access Approval 使用签名密钥来验证 Access Approval 请求的完整性。
如果您已启用 Cloud EKM,则可以选择外部管理的签名密钥。如需了解如何使用外部密钥,请参阅 Cloud EKM 概览。
您还可以选择使用所选算法创建 Cloud KMS 签名密钥。如需了解详情,请参阅创建非对称密钥。
如需使用自定义签名密钥,请按照本部分中的说明操作。
获取服务账号的电子邮件地址
服务账号的电子邮件地址采用以下格式:
service-pPROJECT_NUMBER@gcp-sa-accessapproval.iam.gserviceaccount.com
将 PROJECT_NUMBER 替换为项目编号。
例如,如果某个项目的项目编号为 123456789,则该项目中的服务账号的电子邮件地址为 service-p123456789@gcp-sa-accessapproval.iam.gserviceaccount.com。
如需使用签名密钥,请执行以下操作:
在 Google Cloud 控制台的访问审批页面上,选择使用 Cloud KMS 签名密钥(高级)。
添加加密密钥版本资源 ID。
加密密钥版本资源 ID 必须采用以下格式:
projects/PROJECT_ID/locations/LOCATION/keyRings/KEYRING_ID/cryptoKeys/CRYPTOKEY_ID/cryptoKeyVersions/KEY_ID
如需了解详情,请参阅获取 Cloud KMS 资源 ID。
如需保存设置,请点击保存。
如需使用自定义签名密钥,您必须为项目的访问审批服务账号提供 Cloud KMS CryptoKey Signer/Verifier (
roles/cloudkms.signerVerifier) IAM 角色。如果访问审批服务账号没有使用您提供的密钥进行签名的权限,您可以点击授予来授予所需的权限。授予权限后,点击保存。
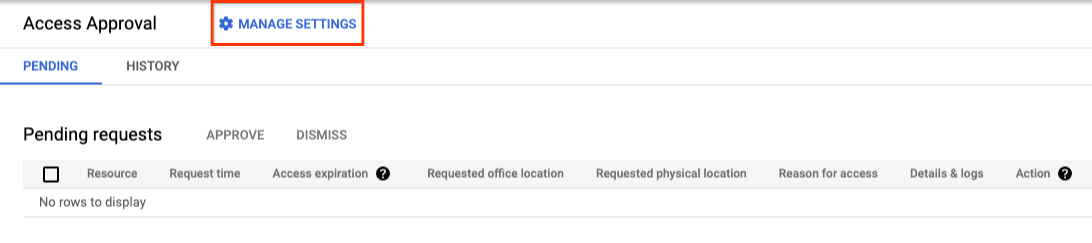
审核 Access Approval 请求
您现在已注册 Access Approval,并将自己添加为访问权限请求的审批者,因此您会收到有关访问权限请求的电子邮件通知。
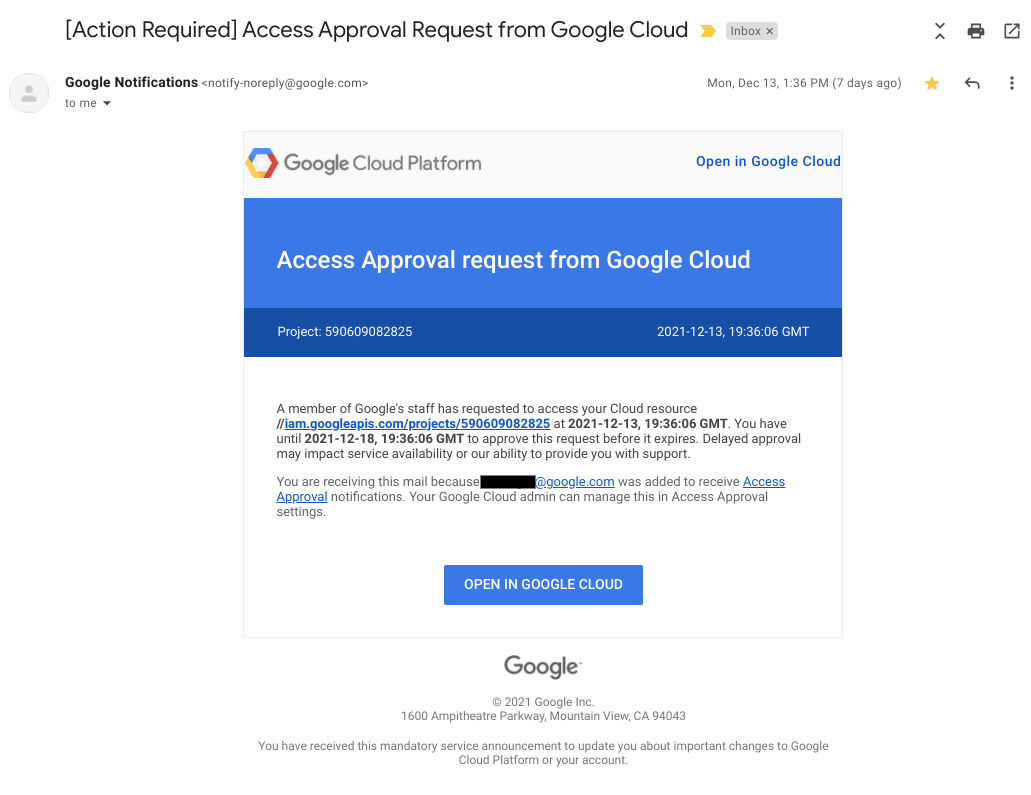
下图显示了 Access Approval 在 Google 员工请求访问客户数据时发送的电子邮件通知示例。
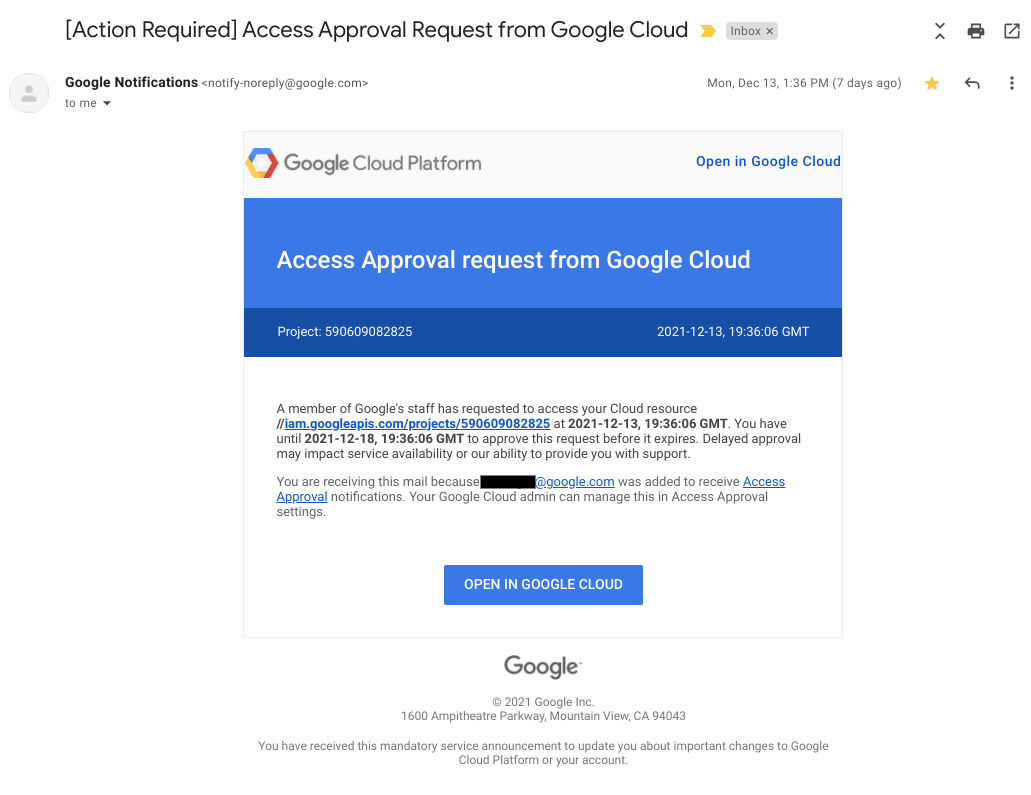
如需查看并批准收到的访问权限请求,请执行以下操作:
前往 Google Cloud 控制台中的 Access Approval 页面。
如需前往此页面,您也可以点击发送给您的电子邮件中带有批准请求的链接。
点击批准。
您批准请求后,具有与批准相匹配的特征(例如,相同的理由、位置或办公桌位置)的 Google 员工可以在批准的时间范围内访问指定资源及其子资源。
清理
-
如需取消注册 Access Approval,请执行以下操作:
- 在 Google Cloud 控制台的访问权限审批页面上,点击管理设置。
- 点击取消注册。
- 在随即打开的对话框中,点击退订。
- 如需为组织停用 Access Transparency,请与 Cloud Customer Care 联系。
无需采取其他步骤即可避免您的账号产生费用。
后续步骤
- 了解访问请求的结构。
- 了解如何批准 Access Approval 请求。
- 了解如何查看 Access Approval 历史请求。

