Artifact Analysis 是一系列服务,可提供软件组成分析、元数据存储和检索。其检测点内置于 Artifact Registry 和 Google Kubernetes Engine (GKE) 等多种 Google Cloud 产品中,可快速启用。该服务可与 Google Cloud的第一方产品配合使用,还支持您存储来自第三方数据源的信息。扫描服务会利用通用漏洞存储区将文件与已知漏洞进行匹配。
此服务以前称为 Container Analysis。新名称不会改变现有产品或 API,但反映了产品不断扩展的功能范围,而不仅仅是容器。
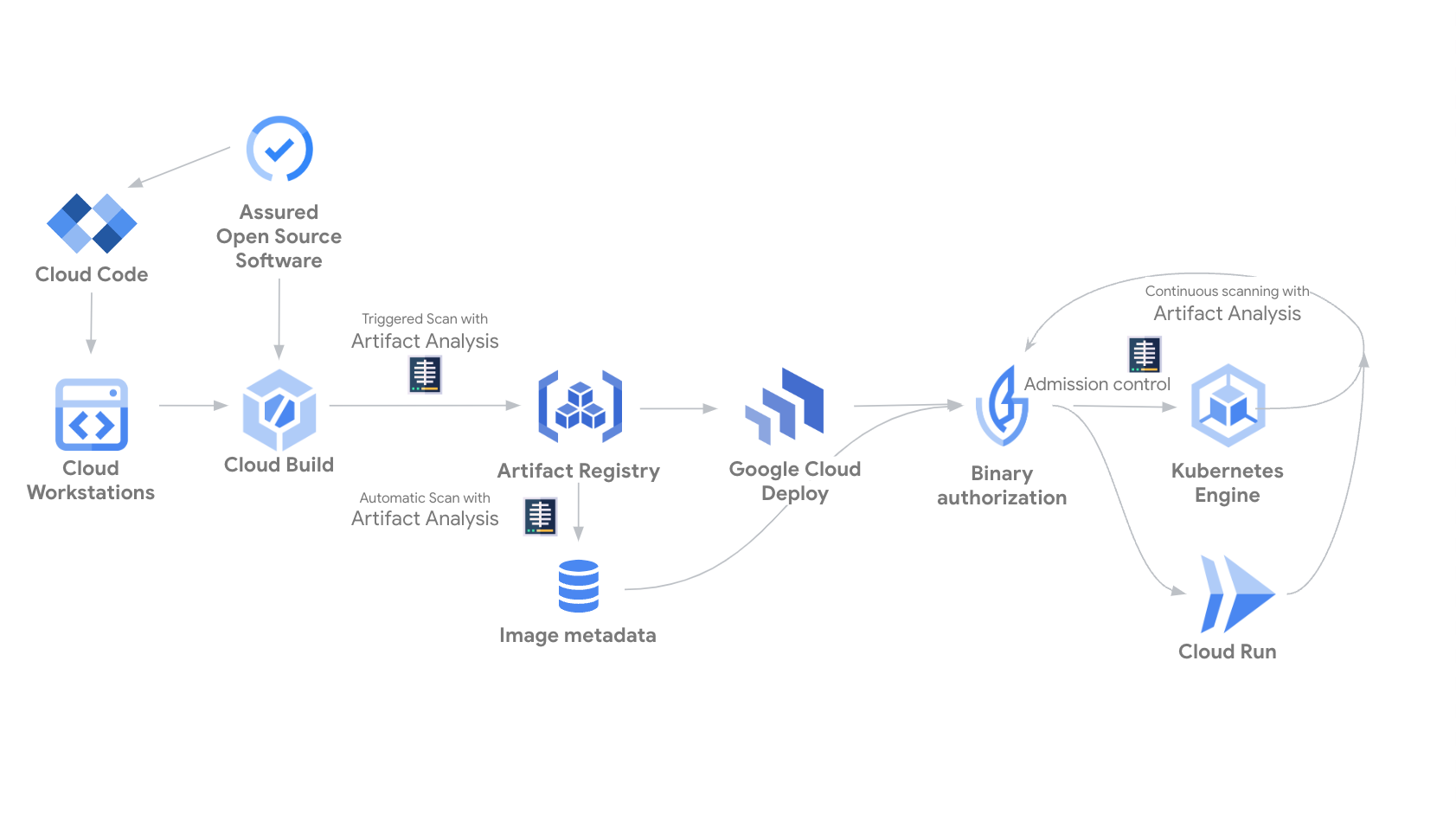
图 1. 图表:显示了 Artifact Analysis 如何在来源、构建、存储、部署和运行时环境中创建元数据并与之互动。
注册表扫描
本部分概述了基于 Artifact Registry 的 Artifact Analysis 漏洞扫描功能,并列出了相关的 Google Cloud产品,您可以在其中启用补充功能来支持您的安全态势。
Artifact Registry 中的自动扫描
- 您每次将新映像推送到 Artifact Registry 时,系统都会自动触发扫描流程。发现新漏洞时,漏洞信息会持续更新。Artifact Registry 包含应用语言包扫描功能。首先,请启用自动扫描。
使用 Security Command Center 进行集中式风险管理
- Security Command Center 可集中管理您的云安全,提供漏洞扫描、威胁检测、安全状况监控和数据管理功能。 Security Command Center 会汇总 Artifact Registry 扫描的漏洞发现结果,让您能够在 Security Command Center 中查看所有项目中的运行工作负载内的容器映像漏洞,以及其他安全风险。您还可以将这些发现结果导出到 BigQuery,以便进行深入分析和长期存储。 如需了解详情,请参阅 Artifact Registry 漏洞评估。
GKE 工作负载漏洞扫描 - 标准层级
- 作为 GKE 安全状况信息中心的一部分,工作负载漏洞扫描可检测容器映像操作系统漏洞。扫描功能免费提供,可按集群启用。您可以在安全状况信息中心内查看结果。
GKE 工作负载漏洞扫描 - Advanced Vulnerability Insights
- 除了基本的容器操作系统扫描之外,GKE 用户还可以升级到 Advanced Vulnerability Insights,以利用持续的语言包漏洞检测功能。您必须在集群上手动启用此功能,然后才能收到操作系统和语言包漏洞结果。详细了解 GKE 工作负载中的漏洞扫描。
按需扫描
- 此服务不是持续性的;您必须运行命令才能手动启动扫描。扫描结果最长可能需要 48 小时才能完成。扫描完成后,漏洞信息不会更新。您可以扫描本地存储的映像,而无需先将其推送到 Artifact Registry 或 GKE 运行时。如需了解详情,请参阅按需扫描。
访问元数据
Artifact Analysis 是一项 Google Cloud 基础架构组件,可让您存储和检索结构化元数据,以用于 Google Cloud资源。在发布流程的各个阶段,可以由相关人员或自动化系统来添加描述活动结果的元数据。例如,您可以为映像添加元数据,以表明该映像已通过集成测试套件或漏洞扫描的测试。
将 Artifact Analysis 集成到 CI/CD 流水线中之后,您可以根据元数据做出决策。例如,您可以使用 Binary Authorization 创建部署政策,以仅允许部署来自受信任注册表的合规映像。
Artifact Analysis 通过备注和发生实例将元数据与映像相关联。如需详细了解这些概念,请参阅元数据管理页面。
如需了解 Artifact Analysis 功能的费用,请参阅 Artifact Analysis 价格。
后续步骤
- 开始使用自动扫描。
- 开始使用 On-Demand Scanning。
- 详细了解扫描概念。
- 详细了解支持的元数据类型。

