本页面介绍如何使用边界网桥来允许不同服务边界中的项目和服务进行通信。
准备工作
服务边界网桥
虽然一个项目只能分配到一个服务边界内,但您可能希望您的项目能够与其他边界中的项目进行通信。您可以通过创建边界网桥来跨服务边界实现服务通信并共享数据。
边界网桥可允许不同服务边界内的项目进行通信。边界网桥是双向的,允许每个服务边界内的项目在该网桥的范围内获得同等的访问权限。但是,项目的访问权限级别和服务限制仅由该项目所属的服务边界控制。一个项目可以通过多个网桥连接其他项目。
一个服务边界中的项目不能间接访问其他边界中的项目。例如,假设我们有三个项目:A、B、C。每个项目都属于不同的服务边界。A 和 B 共用一个边界网桥。B 和 C 也共用一个网桥。虽然数据可以在 A 和 B 之间移动,也可以在 B 和 C 之间移动,但 A 和 C 之间不能传递数据,因为这两个项目未通过边界网桥直接连接。
注意事项
在创建边界网桥之前,请考虑以下事项:
项目必须先属于一个服务边界,然后才能使用边界网桥连接到另一个项目。
边界网桥不能包含来自不同组织的项目。通过边界网桥连接的项目必须属于同一组织中的服务边界。
边界网桥不能包含来自不同范围限定的政策的项目。您可以改用入站流量规则或出站流量规则,允许来自不同范围政策的项目之间进行通信。
为项目创建边界网桥后,您无法将该项目中的 VPC 网络添加到边界。
边界网桥的示例
如需查看边界网桥工作原理的宽泛示例,请考虑以下设置:
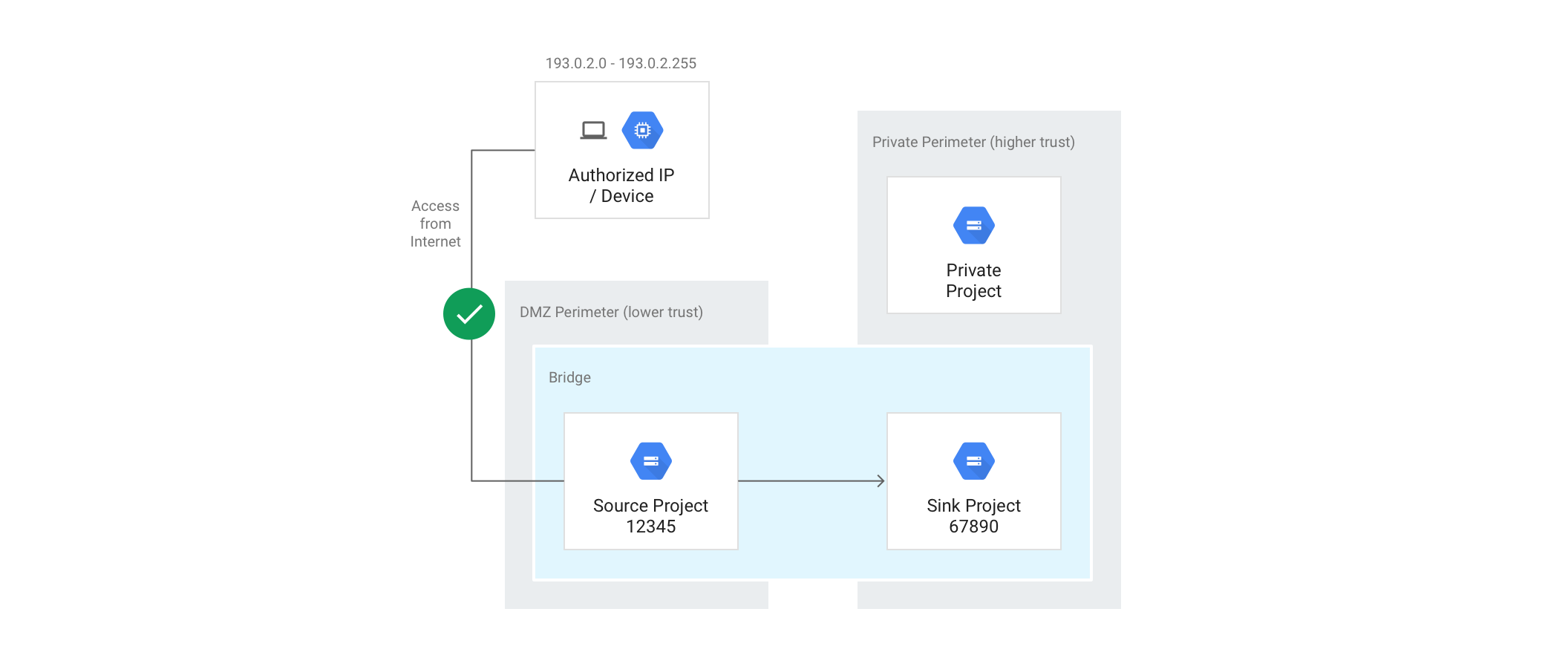
目标是只允许在 DMZ 边界中的 Cloud Storage 存储分区与接收器 (Sink) 项目中的存储分区之间复制数据,而不允许 DMZ 边界中的任何虚拟机访问私有 (Private) 项目中 Storage 存储分区中的数据。
使用以下命令创建边界网桥 (Bridge),指定项目 A 和项目 B 将通过该边界网桥连接。
gcloud access-context-manager perimeters create Bridge \
--title="Perimeter Bridge" --perimeter-type=bridge \
--resources=projects/12345,projects/67890
边界网桥边界是双向的。也就是说,您可以从 DMZ 边界复制到私有 (Private) 边界,也可以从私有 (Private) 边界复制到 DMZ 边界。为了提供方向控制,最好将边界与执行复制操作的服务账号或身份的 IAM 权限配合使用。
