用于 Network Connectivity Center spoke 的 Private NAT
借助 Private NAT,您可以创建与 Network Connectivity Center spoke 配合使用的 Private NAT 网关,以执行以下网络之间的网络地址转换 (NAT):
- 虚拟私有云 (VPC) 网络:在此场景中,您要连接的 VPC 网络作为 VPC spoke 连接到 Network Connectivity Center hub。
- VPC 网络和 Google Cloud外部的网络:在此场景中,一个或多个 VPC 网络作为 VPC spoke 连接到 Network Connectivity Center hub,并通过混合 spoke 连接到您的本地网络或其他云服务提供商网络。
规格
除了常规 Private NAT 规范之外,用于 Network Connectivity Center spoke 的 Private NAT 还具有以下规范:
- Private NAT 使用
type=PRIVATE的 NAT 配置,让具有重叠子网 IP 地址范围的网络进行通信。不过,只有非重叠的子网才能相互连接。 - 您需要通过引用 Network Connectivity Center hub 来创建自定义 NAT 规则。NAT 规则指定来自用途为
PRIVATE_NAT的子网的 NAT IP 地址范围,Private NAT 会使用该子网对您已连接网络之间的流量执行 NAT。 - 当您在适用 Private NAT 的子网范围内创建虚拟机实例时,如果目标 spoke 与网关位于同一 Network Connectivity Center hub 中,则网关会对来自此虚拟机实例的所有出站流量进行转换。Private NAT 会将流量转换为与 Private NAT 网关位于同一区域内的目的地辐射网关,以及跨区域的目的地辐射网关。
- Private NAT 网关与单个 VPC 网络中单个区域的子网 IP 地址范围关联。这意味着,在一个 VPC 网络中创建的 Private NAT 网关无法向 Network Connectivity Center hub 的其他 spoke 中的虚拟机提供 NAT 服务,即使这些虚拟机与网关位于同一区域也是如此。
VPC 网络之间的流量
以下额外规范适用于 VPC 网络之间的流量 (Inter-VPC NAT):
- 如需在两个 VPC 网络之间启用 Inter-VPC NAT,必须将每个 VPC 网络配置为 Network Connectivity Center hub 的 VPC spoke。您必须确保 VPC spoke 之间没有重叠的 IP 地址范围。如需了解详情,请参阅创建 VPC spoke。
- 与 Private NAT 网关关联的 Network Connectivity Center hub 必须至少有两个 VPC spoke,其中一个 VPC spoke 是 Private NAT 网关的 VPC 网络。
- Inter-VPC NAT 仅支持 Network Connectivity Center VPC spoke 之间的 NAT,不支持使用 VPC 网络对等互连连接的 VPC 网络之间的 NAT。
VPC 网络与其他网络之间的流量
以下额外规范适用于 VPC 网络与 Google Cloud外部的网络之间的流量:
- 来源 VPC 网络必须配置为 Network Connectivity Center hub 的 VPC spoke。
- 混合 spoke 必须连接到同一 Network Connectivity Center hub,才能在 VPC spoke 与 Google Cloud外部的目标网络之间建立连接。如需了解详情,请参阅在混合 spoke 与 VPC spoke 之间建立连接。
如需了解在同一 Network Connectivity Center hub 中使用 VPC spoke 和混合 spoke 的要求,请参阅与 VPC spoke 进行路由交换。
基本配置和工作流
下图显示了两个 VPC spoke 之间的流量的基本 Private NAT 配置:
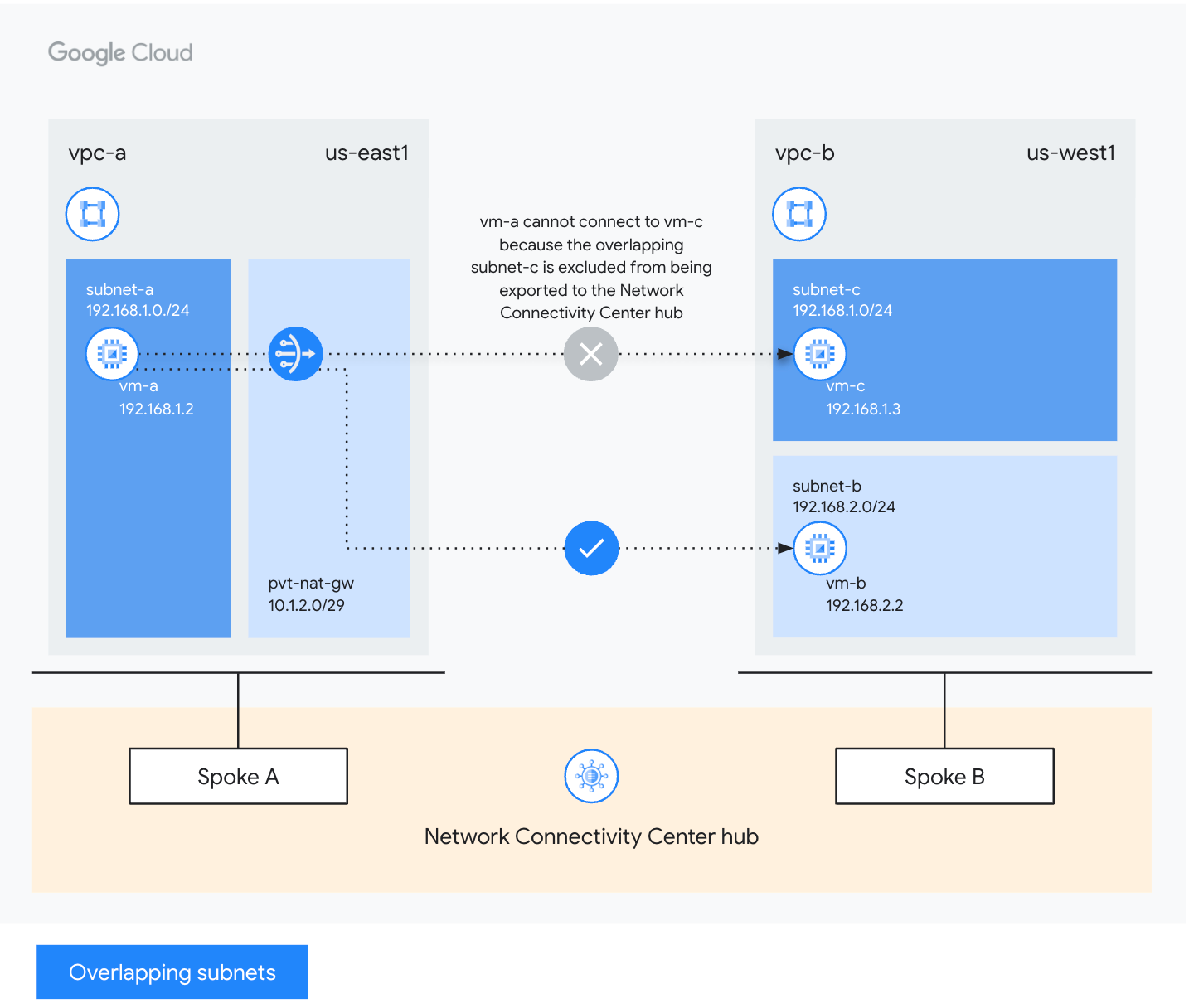
在此示例中,Private NAT 的设置如下:
pvt-nat-gw网关在vpc-a中进行配置,以应用于us-east1区域中subnet-a的所有 IP 地址范围。如果使用pvt-nat-gw的 NAT IP 范围,则vpc-a的subnet-a中的虚拟机 (VM) 实例可以将流量发送到vpc-b的subnet-b中的虚拟机,即使vpc-a的subnet-a与vpc-b的subnet-c重叠。vpc-a和vpc-b都配置为 Network Connectivity Center hub 的 spoke。pvt-nat-gw网关经过配置在配置为同一 Network Connectivity Center hub 中的 VPC spoke 的 VPC 网络之间提供 NAT。
工作流示例
在上图中,vpc-a 的 subnet-a 中具有内部 IP 地址 192.168.1.2 的 vm-a 需要从具有 vpc-b 的 subnet-b 中的 IP 地址 192.168.2.2 的 vm-b 下载更新。这两个 VPC 网络都作为 VPC spoke 连接到同一 Network Connectivity Center hub。假设 vpc-b 包含与 vpc-a 中的子网重叠的另一个子网 192.168.1.0/24。为了使 vpc-a 的 subnet-a 能够与 vpc-b 的 subnet-b 进行通信,您需要在 vpc-a 中配置 Private NAT 网关 pvt-nat-gw,如下所示:
Private NAT 子网:在配置 Private NAT 网关之前,先创建用途为
PRIVATE_NAT的 Private NAT 子网(例如10.1.2.0/29)。确保此子网与连接到同一 Network Connectivity Center hub 的任何 VPC spoke 中的现有子网不重叠。其
nexthop.hub与 Network Connectivity Center hub 网址匹配的 NAT 规则。subnet-a的所有地址范围的 NAT。
下表汇总了上述示例中指定的网络配置:
| 网络名称 | 网络组件 | IP地址/范围 | 区域 |
|---|---|---|---|
| vpc-a | subnet-a | 192.168.1.0/24 | us-east1 |
| vm-a | 192.168.1.2 | ||
| pvt-nat-gw | 10.1.2.0/29 | ||
| vpc-b | subnet-b | 192.168.2.0/24 | us-west1 |
| vm-b | 192.168.2.2 | ||
| subnet-c | 192.168.1.0/24 | ||
| vm-c | 192.168.1.3 |
用于 Network Connectivity Center spoke 的 Private NAT 按照端口预留过程为网络中的每个虚拟机预留以下 NAT 来源 IP 地址和来源端口元组。例如,Private NAT 网关会为 vm-a 预留 64 个源端口:10.1.2.2:34000 到 10.1.2.2:34063。
当虚拟机使用 TCP 协议将数据包发送到目标端口 80 上的更新服务器 192.168.2.2 时,会发生以下情况:
虚拟机发送的请求包具有以下属性:
- 来源 IP 地址:
192.168.1.2,虚拟机的内部 IP 地址 - 来源端口:
24000,虚拟机操作系统选择的临时来源端口 - 目标地址:
192.168.2.2,更新服务器的 IP 地址 - 目标端口:
80,指向更新服务器的 HTTP 流量的目标端口 - 协议:TCP
- 来源 IP 地址:
pvt-nat-gw网关会对出站流量执行来源网络地址转换 (SNAT 或来源 NAT),并重写请求数据包的 NAT 来源 IP 地址和来源端口:- NAT 来源 IP 地址:
10.1.2.2,来自虚拟机预留的 NAT 来源 IP 地址和来源端口元组 - 来源端口:
34022,来自虚拟机预留的来源端口元组之一的未使用的来源端口 - 目标地址:
192.168.2.2,未更改 - 目标端口:
80,未更改 - 协议:TCP,不变
- NAT 来源 IP 地址:
更新服务器发送的响应数据包会到达具有以下属性的
pvt-nat-gw网关:- 来源 IP 地址:
192.168.2.2,更新服务器的内部 IP 地址 - 来源端口:
80,来自更新服务器的 HTTP 响应 - 目标地址:
10.1.2.2,与请求数据包的原始 NAT 来源 IP 地址一致 - 目标端口:
34022,与请求数据包的来源端口一致 - 协议:TCP,不变
- 来源 IP 地址:
pvt-nat-gw网关会对响应数据包执行目标网络地址转换 (DNAT),重写响应数据包的目标地址和目标端口,以便将数据包传送到请求具有以下属性的更新的虚拟机:- 来源 IP 地址:
192.168.2.2,未更改 - 来源端口:
80,未更改 - 目标地址:
192.168.1.2,虚拟机的内部 IP 地址 - 目标端口:
24000,与请求数据包的原始临时来源端口一致 - 协议:TCP,不变
- 来源 IP 地址:
后续步骤
- 设置用于 Network Connectivity Center spoke 的 Private NAT。
- 了解 Cloud NAT 产品交互。
- 了解 Cloud NAT 地址和端口。
- 了解 Cloud NAT 规则。
- 排查常见问题。
