密钥版本具有以下状态:
待生成 (
PENDING_GENERATION):(仅适用于非对称密钥。)相应密钥版本仍在生成中。因此无法使用,也无法启用、停用或销毁。只要此版本准备就绪,Cloud Key Management Service 就会自动将其状态更改为 enabled。待导入 (
PENDING_IMPORT):(仅适用于导入的密钥。)此密钥版本仍在导入中。因此无法使用,也无法启用、停用或销毁。只要此版本准备就绪,Cloud Key Management Service 就会自动将其状态更改为 enabled。已启用 (
ENABLED):相应密钥版本已准备就绪,可供使用。已停用 (
DISABLED):相应密钥版本可能无法使用,但密钥材料仍然可用,并且此版本可以重新启用。已安排销毁 (
DESTROY_SCHEDULED):相应密钥版本已安排销毁,并将很快被销毁。当密钥版本处于此状态时,无法用于加密操作,并且使用密钥的请求会失败。您可以在计划的销毁期限内将密钥版本恢复为停用状态。此状态对应于数据删除流水线中的第 2 阶段 - 软删除。已销毁 (
DESTROYED):相应密钥版本已销毁,密钥材料不再存储在 Cloud KMS 中。如果密钥版本用于非对称或对称加密,则使用此版本加密的任何密文都不可恢复。如果密钥版本用于数字签名,则无法创建新签名。此外,对于所有非对称密钥版本,公钥不再可供下载。处于已销毁状态后,密钥版本的状态无法再进行更改,重新导入时除外。此状态对应于数据删除流水线中的第 3 阶段 - 活跃系统的逻辑删除,这意味着密钥材料会从所有活跃的 Cloud KMS 系统中删除。从销毁时间起,关键材料需要 45 天才能从所有 Google 活跃系统和备份系统中删除。如需了解详情,请参阅 Cloud KMS 的删除时间表。导入失败 (
IMPORT_FAILED):无法导入此密钥版本。如需详细了解导致导入失败的条件,请参阅排查失败的导入。
更改密钥版本的状态
下方描述了密钥版本的状态可以如何进行更改:
创建非对称密钥的密钥版本后,它最初的状态为待生成。Cloud KMS 完成生成该密钥版本后,其状态会自动更改为已启用。
创建对称密钥的密钥版本后,它最初的状态为已启用。
使用
UpdateCryptoKeyVersion方法及其接口,密钥版本的状态可以从已启用更改为已停用或从已停用更改为已启用。如需查看示例,请参阅启用和停用密钥版本。使用
DestroyCryptoKeyVersion方法及其接口,处于已启用或已停用状态的密钥版本可以更改为已安排销毁状态。如需查看示例,请参阅安排将密钥版本进行销毁。使用
RestoreCryptoKeyVersion方法及其接口,处于已安排销毁状态的密钥版本可以恢复为已停用状态。如需查看示例,请参阅恢复密钥版本。
下图显示了密钥版本的允许状态。
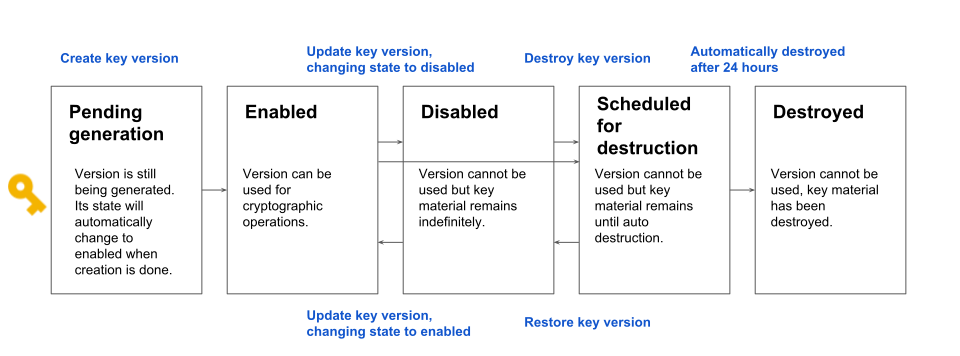
请注意,只有非对称密钥的密钥版本的初始状态为待生成。对称密钥的密钥版本的初始状态为已启用。
密钥版本状态对加密操作的影响
密钥版本状态对加密操作的影响取决于密钥是否用于以下场景:
- 对称加密
- 非对称加密或数字签名
对称加密
每个对称加密密钥都有一个指定的主版本,在该时间点用于加密数据。为了让某个密钥能够用于加密数据,它需要有一个已启用的主密钥版本。
当密钥用于加密明文时,其主密钥版本用于加密该数据。关于哪个密钥版本用于加密数据的信息存储在数据的密文中。在任何给定时间点,只有一个密钥版本可以是主版本。
如果主密钥版本处于已停用状态,则不能使用该密钥版本来加密数据。请注意,已启用的主密钥版本的状态可以更改为已停用、计划销毁或已销毁,而未启用的版本可以设置为主版本。
哪个密钥版本为主版本不会影响解密数据的能力。 只要密钥版本处于已启用状态,就可用于解密数据。
非对称加密或数字签名
每次使用非对称密钥进行加密或数字签名时,都必须指定密钥版本。为了使密钥版本可用于非对称加密或数字签名,必须启用相应密钥版本。 仅当密钥版本处于已启用状态时,才能检索密钥版本的公钥。
已安排销毁状态的可变时长
默认情况下,在从系统中逻辑删除密钥材料之前,Cloud KMS 中的密钥会处于“已安排销毁”(软删除)状态 30 天。您可以配置此时长,但要注意以下事项:
- 时长只能在创建密钥期间配置。
- 密钥时长指定后便无法更改。
- 该时长适用于未来创建的所有密钥版本。
- 所有密钥的最短时长均为 24 小时,但仅限导入的密钥除外,其最短时长为 0。
- 最长时长为 120 天。
该值是使用 CreateCryptoKeyRequest 中 CryptoKey 的 destroy_scheduled_duration 字段配置的。
我们建议您对所有密钥使用 30 天的默认时长,除非有特定的应用要求或监管要求规定使用其他值。

