Security Command Center 是 Google Cloud的安全和风险数据库。Security Command Center 包含一个风险信息中心和分析系统,用于在整个组织中发现、了解和补救Google Cloud 安全和数据风险。
Google Cloud Armor 自动与 Security Command Center 集成,并将两个发现结果导出到 Security Command Center 信息中心:允许的流量高峰和拒绝率提高。本指南介绍发现结果及其解释。
如果尚未在 Security Command Center 中启用 Cloud Armor,请参阅配置 Security Command Center。仅在组织层级启用 Security Command Center 的项目中,您才能在 Security Command Center 中看到发现结果。
允许流量高峰发现结果
允许的流量由格式正确的 HTTP(S) 请求组成,这些请求的目标是在强制执行 Cloud Armor 安全政策后到达您的后端服务。
允许的流量高峰发现结果指示每个后端服务允许的流量达到高峰。当与最近历史记录中观察到的正常数量相比,允许的每秒请求数 (RPS) 突然增加时,就会生成一个发现结果。作为发现结果的一部分,提供了构成高峰的 RPS 和最近历史记录的 RPS。
用例:潜在 L7 攻击
当攻击者发送大量请求以使目标服务过载时,就会发生分布式拒绝服务 (DDoS) 攻击。第 7 层 DDoS 攻击流量通常会导致每秒请求数达到高峰。
允许的流量高峰发现结果会确定 RPS 高峰所定向到的后端服务,并提供使 Cloud Armor 将其归类为 RPS 高峰的流量特征。您可以使用此信息来确定以下各项:
- 潜在的第 7 层 DDoS 攻击是否正在进行。
- 要作为目标的服务。
- 您可以用来缓解潜在攻击的措施。
下面是 Security Command Center 信息中心上的允许的流量高峰发现结果示例的屏幕截图。
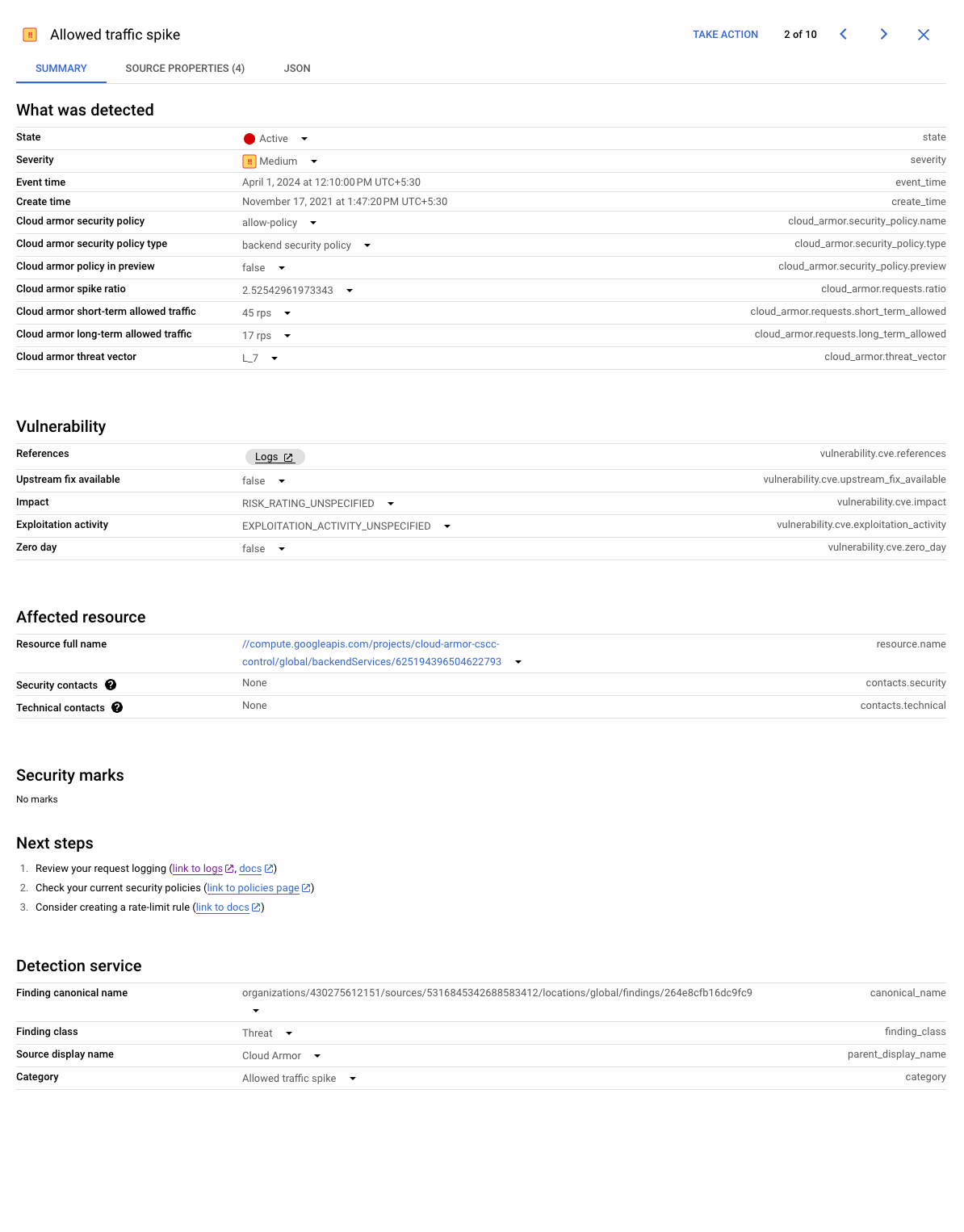
Google Cloud 会根据 Cloud Armor 历史信息计算 Long_Term_Allowed_RPS 和 Short_Term_Allowed_RPS 值。
拒绝率提高发现结果
拒绝率提高发现结果指示由于安全政策中用户配置的规则,Cloud Armor 阻止的流量比率有所增加。尽管拒绝是预期行为,并且不会影响后端服务,但此发现结果有助于提醒您针对应用的有害和潜在恶意流量有所增加。作为发现结果的一部分,提供了拒绝流量和总传入流量的 RPS。
用例:缓解 L7 攻击
拒绝率提高发现结果使您可以了解成功缓解的影响以及恶意客户端行为的显著变化。此发现结果可确定拒绝的流量所定向到的后端,并提供使 Cloud Armor 引发此发现结果的流量特征。使用此信息可评估是否必须详细研究拒绝的流量以进一步加强缓解措施。
下面是 Security Command Center 信息中心上的拒绝率提高发现结果示例的屏幕截图。
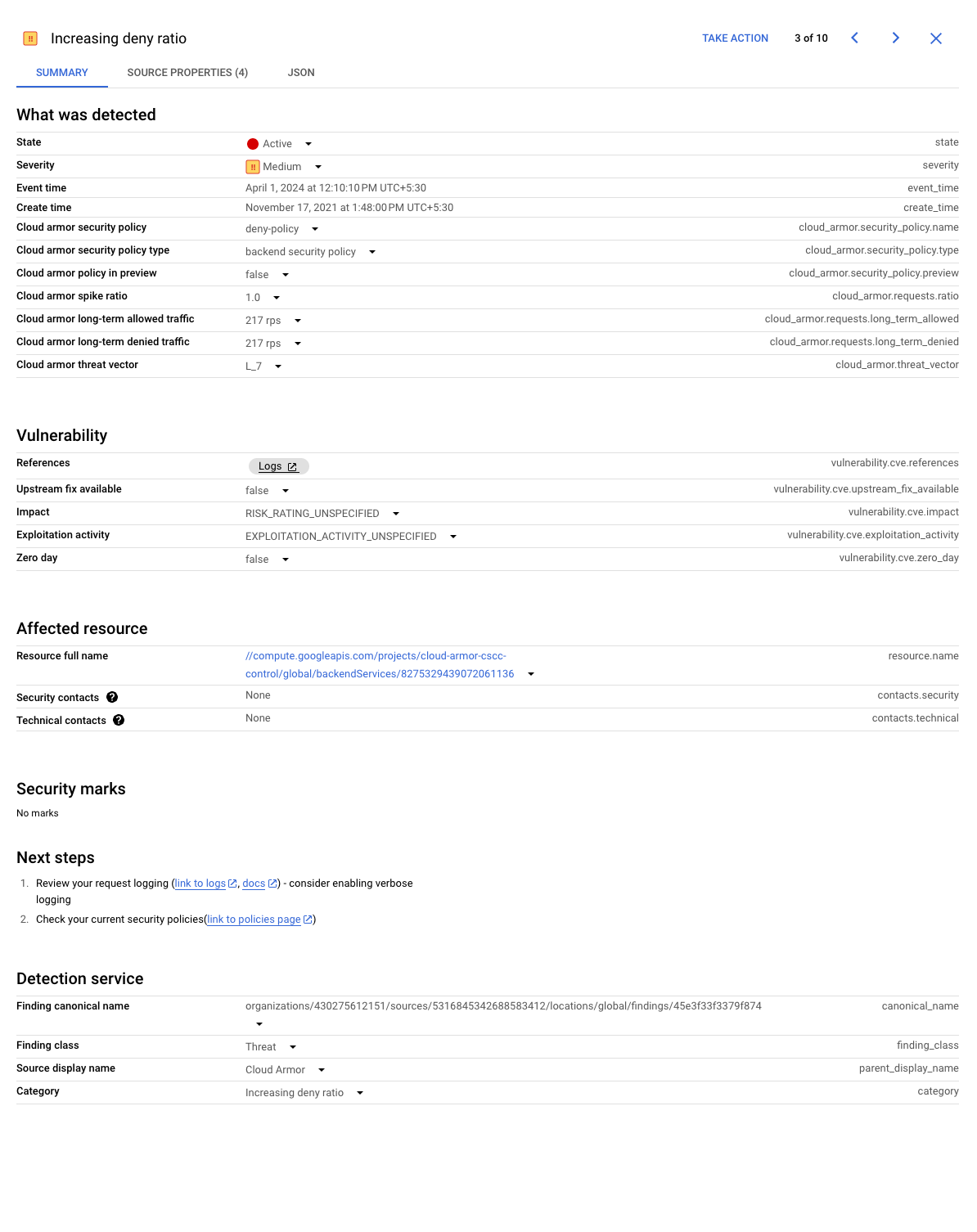
Google Cloud 会根据 Cloud Armor 历史信息计算 Long_Term_Denied_RPS 和 Long_Term_Incoming_RPS 值。
Google Cloud Armor 自动调节式保护
自动调节式保护会将遥测数据发送到 Security Command Center。如需详细了解自动调节式保护发现结果,请参阅自动调节式保护概览中的监控、提醒和日志记录。
高级网络 DDoS 攻击防护
高级网络 DDoS 防护会将遥测数据发送到 Security Command Center。如需详细了解高级网络 DDoS 防护发现结果,请参阅 Security Command Center 发现结果。
流量恢复正常后
Security Command Center 发现结果是在某个时间点观察到特定行为的通知。行为消失后,不会发送任何通知。
如果当前流量特征与现有特征相比大幅增加,则可能会对现有发现结果进行更新。如果没有后续发现结果,则在生成初始发现结果之后,行为消失或流量没有显著增加(允许或拒绝)。
